This week is all about filters. Filters are basically a super-set of the functionalities of applicability rules – already available for a while for Windows 10 – and are a great new addition to assigning apps policies and profiles to specific devices. Those specific devices are only the devices that meet the specific properties that are configured in the filters. A great method for specifically targeting apps, policies and profiles. This post starts with a short introduction about filters, followed with information about creating and using filters (including the steps for using and creating filters). This post ends with the administrator experience with filters.
Introducing filters
For device configuration profiles for Windows 10 devices it was already possible to use applicability rules. Applicability rules would enable the IT administrator to assign or not assign the profile based on the version or the edition of Windows 10. Filters could be seen as the enhanced platform independent version of those applicability rules. The main enhancements are that filters can be used for all the different platforms, filters can be used for apps, policies and profiles, and filters can be used with many different Intune device properties. Besides that, filters can be used in combination with any Azure AD group assignment and even in combination with the default All users or All devices groups. In that case the targeted devices of the assignment will be dynamically filtered based on the configured device properties.
One of the best characteristics of filters is the reusability. Unlike applicability rules – that are created per profile – filters are created once and can be reused for different objects of apps, policies and profiles. That enables the IT administrator to create a filter – with an expression that for example filters personal devices – for usage across different assignments. During the check-in of the device, the filter evaluation engine will determine the applicability of the assignment. The expression in a filter can be created by using different Intune device properties. Those properties are available for all the managed devices in Intune. There is – however – a slight difference in availability of the different properties for devices of different platforms. The table below provides a quick overview of the available properties, the shape of the value and the supported platforms.
| Device property | Property | Value | Supported platforms |
|---|---|---|---|
| Device name | deviceName | String | Android device administrator, Android Enterprise, iOS/iPadOS, macOS, Windows 10 |
| Device manufacturer | manufacturer | String | Android device administrator, Android Enterprise, iOS/iPadOS, macOS, Windows 10 |
| Device model | model | String | Android device administrator, Android Enterprise, iOS/iPadOS, macOS, Windows 10 |
| Device category | deviceCategory | String | Android device administrator, Android Enterprise, iOS/iPadOS, macOS, Windows 10 |
| Platform version | osVersion | String | Android device administrator, Android Enterprise, iOS/iPadOS, macOS, Windows 10 |
| Rooted/ jailbroken | isRooted | Selection | Android device administrator, Android Enterprise (work profile only), iOS/iPadOS |
| Device ownership | deviceOwnership | Selection | Android device administrator, Android Enterprise, iOS/iPadOS, macOS, Windows 10 |
| Enrollment profile name | enrollmentProfileName | String | iOS/iPadOS, Windows 10 |
| Operating system SKU | operatingSystemSKU | String | Windows 10 |
Note: For the correct string values, of the different device properties, simply verify the different columns in the devices overview of the Microsoft Endpoint Manager admin center.
Creating filters
Filters are reusable. That is an important starting point for creating filters, as filters are not related to a specific assignment. That means that filters can be created as separate configurations. The following six steps walk through the required steps for creating a filter with multiple expressions.
Note: The steps below show the creation of a filter for the Windows 10 virtual machines in Azure. In this example, those devices can be filtered by using a combination of the Device name and Model.
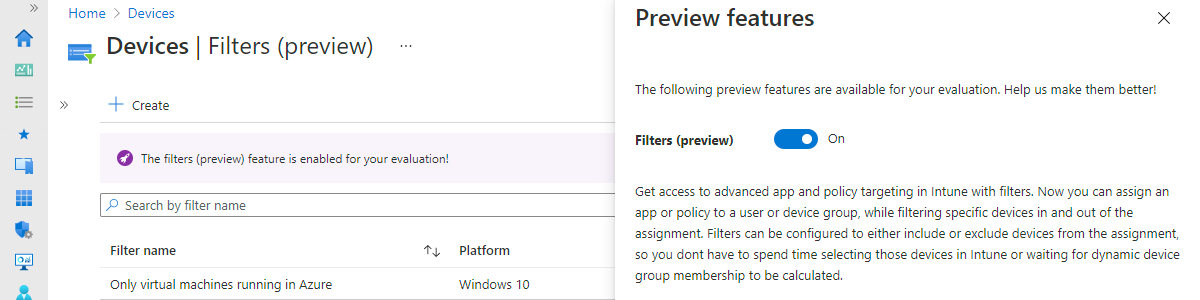
Important: At the moment of writing filters are still in preview. That requires the IT administrator to specifically enable filters for evaluation. That can be achieved by clicking at the purple bar on top of the page at step 2 below an switching the slider with Filters (preview) to On.
- Open the Microsoft Endpoint Manager admin center portal and navigate Devices > Filters (alternative roads to the same configuration are Apps > Filters or Tenant admin > Filters)
- On the Devices | Overview page, click Create to open the Create Filter wizard
- On the Basics page, provide the following information and click Next
- Filter name: Specify a unique name to distinguish the filter from other filters
- Description: (Optional) Specify a description to further explain the usage of the filter
- Platform: Select Windows 10 as the platform
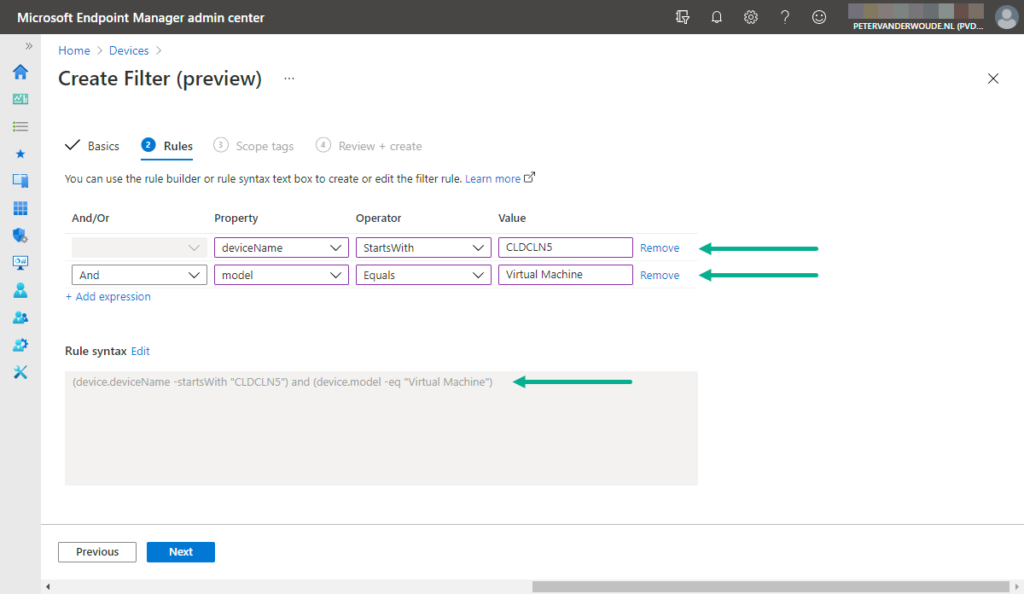
- On the Rules page, as shown below in Figure 1, create the following configuration and click Next
- Expression 1 – This expressions is used to filter devices based on how the name starts
- And/Or: Not applicable
- Property: Select deviceName as value
- Operator: Select StartsWith as value
- Value: Specify the required string as value
- Expression 2 – This expression is used to also require devices to have a specific model
- And/Or: Select And as value
- Property: Select model as value
- Operator: Select Equals as value
- Value: Specify Virtual Machine as value
- On the Scope tags page, configure the required scope tags and click Next
- On the Review + create page, verify the configuration and click Create
Using filters
Filters are used on top of the normal group assignments. That means that an IT administrator still configures the group assignment and combines that with the created filter, to filter the applicable devices. Also, filters can only be used on top of the included groups of an assignment and not on top of the excluded groups of an assignment. That actually makes perfect sense, as a filter already makes sure that only the specifically filtered devices will eventually receive the assignment. Besides that, using filters also provides more flexibility, as it enables mixing user groups with device properties. Excluding groups can, however, still be useful for filtering users from a user group assignment.
So, in general, the include and exclude groups are still the starting point of an assignment. Using filters on top of that enables the IT administrator to only target the required devices. An example of using filters in an assignment is described in the following six steps.
Note: The steps below show the usage of a filter for an existing app assignment. The idea and steps are similar when configuring a filter with a new app app assignment or any policy or profile assignment.
- Open the Microsoft Endpoint Manager admin center portal and navigate Apps > Windows > Select the app that should be assigned to only specific Windows 10 devices > Properties
- In the properties of the select app, click Edit with Assignments
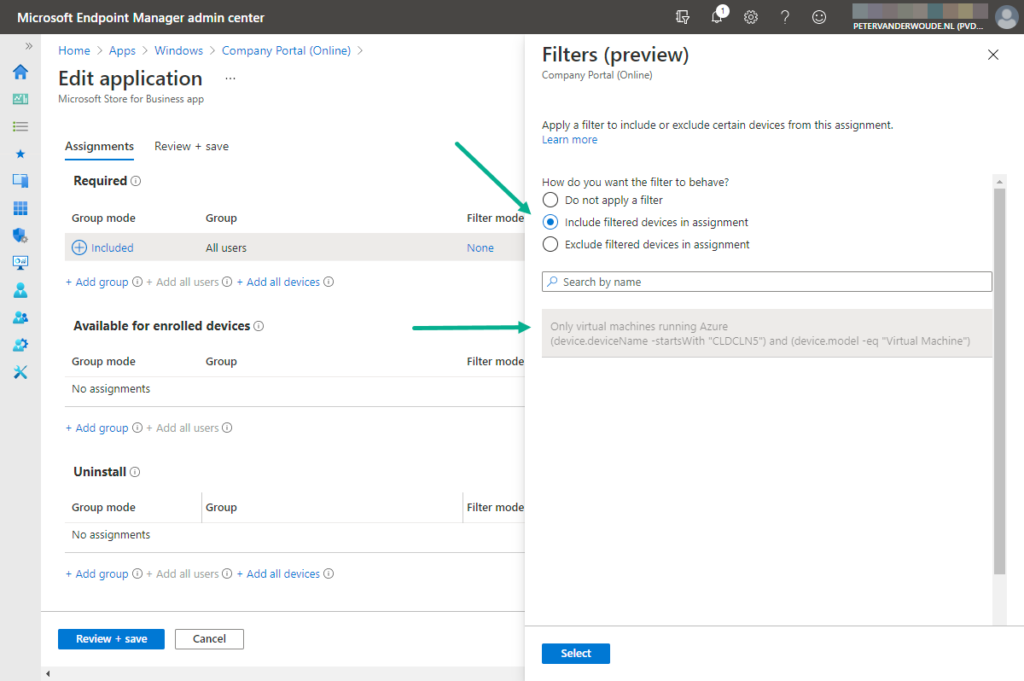
- On the Edit application page, as shown below in Figure 2, create the following configuration and click Review + save
- Group mode: Select Included as value
- Group: Select the required group of users or devices as value
- Filter mode: Select Include filtered devices in assignment as value
- Filter: Select the just created filters as value
Note: The Filters page is shown when clicking on either None with Filter mode or None with Filter. In both cases the IT administrator must configure both settings at the same time.
Experiencing filters
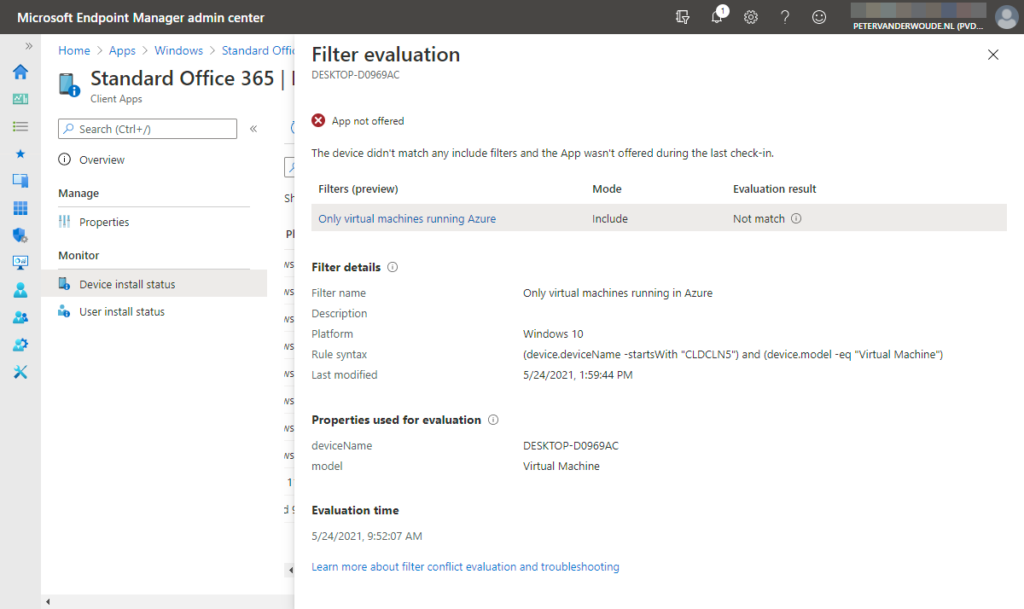
The best place to look at the results of filters is not the device of the user, but the Microsoft Endpoint Manager admin center. That provides the IT administrator with two different views (or reports) with information about the evaluation of filters. The first view is available as the Filter evaluation monitor in the overview of a specific device. The second view is available by clicking on Filters evaluated in the Device install status monitor. That provides the Filter evaluation blade that is shown below in Figure 3. That blade provides an overview about the evaluated filter, the status of the evaluation and the details that are used for that evaluation. On top of the blade is the actual result of the filter on the assignment. In the example below, the app is not offered as the evaluation is not a match.
More information
For more information about using filters in Microsoft Intune, refer to the following docs.
- Use Microsoft Endpoint Manager filters to target apps and policies to specific devices
- Filters Public Preview – Overview and Known Issues
- Use filters (preview) when assigning your apps, policies, and profiles in Microsoft Endpoint Manager
- Device properties, operators, and rule editing when creating filters in Microsoft Endpoint Manager
- List of platforms, policies, and app types supported by filters in Microsoft Endpoint Manager
- Filter reports and troubleshooting in Microsoft Endpoint Manager
It seems that filters is not available for Win32-apps? Until there is support for Win32-apps, this feature is pretty useless at the moment. at least for us. Too bad.
Hi Pär,
Filters are already available for the assignments of Win32 apps.
Regards, Peter
Hm, interesting. I could’ve sworn it wasn’t there when I looked. But now it is. ? Maybe it just took a little longer, or I needed to log out of Endpoint Managemt to activate it.
Sorry, and thanks!
No problem Pär! Enjoy the possibilities!
Hi Peter,
I have one query on feature “Enable Filters Public Preview”, Basically I would like to know if we can see from admin logs or any other source that who has enable this feature from Intune console tenant ?
Or do we have to depend only on Microsoft ?
Hi Yogesh,
I haven’t looked at that specific message, but I would expect it to be in the Audit logs.
Regards, Peter
Hi. Is it possible to apply two filters in a compliance policy? So I want to have a filter that rules all Mac OS devices and one filter that includes that includes all windows devices azure ad joined.
Then to create a compliance policy set to a group of users and exclude both filters above, so the policy is applied to only windows users as well as to not personal devices not Azure AD joined. Can I include two filters? Thank you
Hi Dorjana,
In that case you need to combine those filter to a single filter.
Regards, Peter
Is it possible to apply a device filter to an application protection policy? I am only seeing where it allows me to apply a managed apps filter but I want to use a managed device filter. Can you even work with devices in an application protection policy or can that only be applied to users/group?
No, that’s not possible. It’s a different service that contains different properties. See for more information also: https://learn.microsoft.com/en-us/mem/intune/fundamentals/filters
Regards, Peter