Working with the automatic enablement of Windows hotpatch security updates
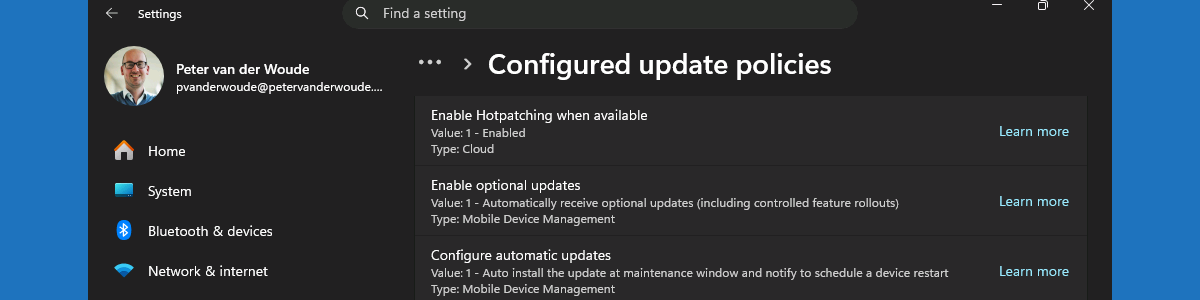
This week is all about the recently introduced configuration that will enable Windows hotpatch security updates by default. The configuration to enable the usage of hotpatch security updates has been available since the introduction of Windows 11 version 24H2, and can be configured relatively as shown in this post. Starting with the Windows security update of May 2026, Windows Autopatch will enable hotpatch security updates by default. That should help organizations with easier getting more secure. The configuration is achieved via a tenant-wide configuration via Windows Autopatch that is only applied when no quality update policies are applied to the device. That configuration is available in Microsoft Intune and will be enabled by default. This post will provide a closer look at that new tenant-wide …