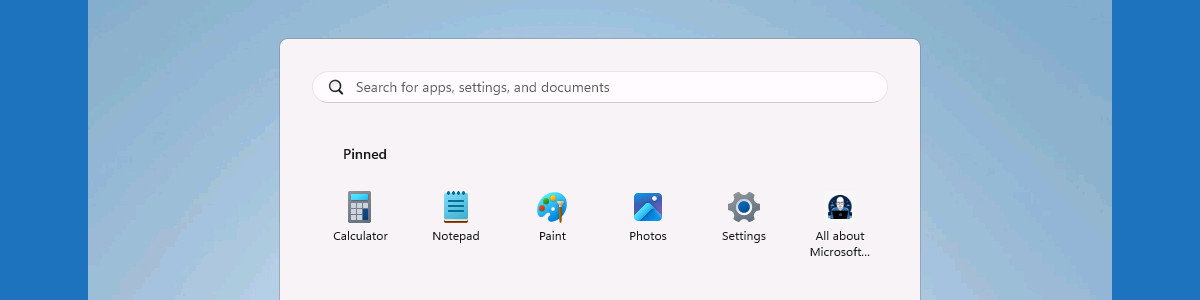
Hiding the recommended section from the Start layout and multi-app kiosk mode
This week is all about another relatively small, but essential, configuration to further enhance the Start layout experience. Especially when using multi-app kiosk mode. That configuration is to hide the recommended section from the Start layout. Hiding that section is especially relevant when using a multi-app kiosk mode, as that includes a link to the Settings app when there are no recommendations. Even though that might sound pretty small, it does take away another item that a user could potentially click on and hitting an unnecessary blockage. In those cases lesser is better. That means that there are definitely scenarios in which it can be really useful to prevent the Start layout from displaying recommended applications and files. This post will provide a closer look …