Getting started with Windows Backup for Organizations
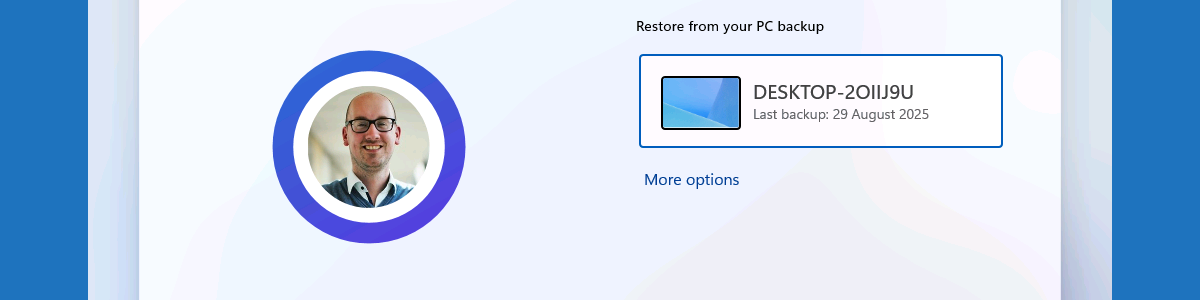
This week is all about the new Windows Backup for Organizations feature that has become available. The Windows Backup for Organizations feature is initially aimed at making it easier to transition from Windows 10 to Windows 11. Besides that, it also makes it easier to switch towards new Windows 11 devices and versions. At this point in time Windows Backup for Organizations can be used to preserve user settings and Microsoft Store app configurations. Especially the first part seems to have a lot of similarities with the already existing Enterprise State Roaming functionality. One might consider Windows Backup for Organizations as the on steroids version of Enterprise State Roaming. Where Enterprise State Roaming is really focused on the basics of the user experience, Windows Backup …