After a couple of weeks with distractions, this week I’m stepping away from conditional access. This week is all about Win32 app management capabilities. More specifically, about Win32 app dependencies. About half a year ago, when Win32 app management capabilities were introduced, I did my first post about those capabilities. That post is still being read really good, so I thought this would be a good time for a nice addition to that post. In this post I’ll start with a shorting introduction about Win32 app dependencies, followed by the configuration steps for Win32 apps and specifically for Win32 app dependencies. I’ll end this post by showing the experience for the end-user and the administrator.
Introduction
Let’s start with a short introduction about reason for using Win32 apps and more specifically about using the Win32 app dependencies. Slowly there are coming more and more reason to look at Win32 apps as a serious alternative to using single-file MSI via MDM. An important reason for that is that Windows 10, version 1709 and later, will download Win32 app content by using delivery optimization. Other reasons are the Win32 app configuration options for requirements and detection rules. That will make the Win32 app really flexible. To make the Win32 app even more flexible, and even more comparable to the ConfigMgr app model, it’s now also possible to configure dependencies between Win32 apps.
Scenario
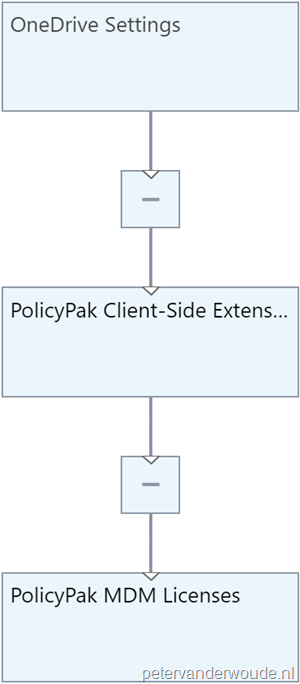
Before looking at the actual configuration steps, let’s first describe the example scenario that I’ll use to show the Win32 app dependencies feature. As an example scenario, I’m using PolicyPak. I won’t go into details about the functionalities of PolicyPak, that information can be found here. The reason that I’m using it as an example scenario, is simply because the installation contains three steps: install the license file, install the client-side extension and install any setting file. All of these are available as MSI and the mentioned order (see also the picture below) provides the best result. In other words, ideal for showing the Win32 app dependencies feature.
Note: In my testing, PolicyPak will work just perfectly fine if you don’t take into account dependencies, but this is an ideal scenario to ensure that all policies delivered from PolicyPak always get applied the first time
Configuration
Now let’s start with the configuration steps. I’ll do that by first quickly showing the steps to wrap a Win32 app and the steps to configure a Win32 app. For more details about that, please refer to my previous post about Win32 apps. After that, I’ll show the detailed steps for configuring Win32 app dependencies.
Prepare Win32 app
The first step is to quickly go through the steps to prepare the Win32 apps by using the Microsoft Intune Win32 App Packaging Tool. Wrap the Win32 apps. The packaging tool wraps the application installation files into the .intunewin format. Also, the packaging tool detects the parameters required by Intune to determine the application installation state. The following five steps walk through wrapping the different PolicyPak MSIs.
| 1 | Download the Microsoft Intune Win32 App Packaging Tool. In my example to C:\Temp; |
| 2 | Create a folder per PolicyPak MSI. In my example C:\Temp\[PolicyPakMSI]; |
| 3 | Open a Command Prompt as Administrator and navigate to the location of IntuneWinAppUtil.exe. In my example that means cd \Temp; |
| 4 | Run IntuneWinAppUtil.exe and provide the following information, when requested
|
| 5 | Once the wrapping is done. The message Done!!! will be shown. In my example a file named [PolicyPakMSI].intunewin will be created in C:\Temp. |
Note: The mentioned steps should be performed per PolicyPak MSI.
Configure Win32 app
The next step is to quickly look at the configuration steps, within Microsoft Intune, to configure the Win32 apps. The following 17 steps walk through all the steps to configure the Win32 apps, by using the .intunewin files.
| 1 | Open the Azure portal and navigate to Intune > Client apps > Apps to open the Client apps – Apps blade; |
| 2 | On the Client apps – Apps blade, click Add to open the Add app blade; |
| 3 | On the Add app blade, select Windows app (Win32) – preview to show the configuration options and select App package file to open the App package file blade. |
| 4 | On the App package file blade, select the created [PolicyPakMSI].intunewin as App package file and click OK to return to the Add app blade; |
| 5 | Back on the Add app blade, select App information to open the App information blade; |
| 6 | On the App information blade, provide at least the following information and click OK to return to the Add app blade;
Note: The remaining information regarding the Information URL, the Privacy URL, the Developer, the Owner, the Notes and the Logo is optional. |
| 7 | Back on the Add app blade, select Program to open the Program blade; |
| 8 | On the Program blade, verify the Install command and the Uninstall command and click OK to return to the Add app blade; |
| 9 | Back on the Add app blade, select Requirements to open the Requirements blade; |
| 10 | On the Requirements blade, provide at least the following information and click OK to return to the Add app blade;
|
| 11 | Back on the Add app blade, select Detection rules to open the Detection rules blade; |
| 12 | On the Detection rules blade, select Manually configure detection rules and click Add to open the Detection rule blade. |
| 13 | On the Detection rule blade, select MSI as Rule type, verify the pre-provisioned MSI product code and click OK to return to the Detection rules blade; |
| 14 | Back on the Detection rules blade, click OK to return to the Add app blade; |
| 15 | Back on the Add app blade, select Return codes to open the Return codes blade; |
| 16 | On the Return codes blade, verify the preconfigured return codes and click OK to return to the Add app blade; |
| 17 | Back on the Add app blade, click Add to actually add app. |
Note: The mentioned steps should be performed per PolicyPak .intunewin file.
Configure Win32 app dependency
Now the main configuration of this post, the configuration of the dependency between Win32 apps. The created Win32 apps need to be installed in the order as described (and shown) during the explanation of the scenario. The following six steps walk through the Win32 app dependency configuration. In my scenario, these steps need to be performed for he PolicyPak settings MSI, to create a dependency between the PolicyPak settings MSI and the PolicyPak client-side extensions MSI, and for the PolicyPak client-side extensions MSI, to create a dependency between the PolicyPak client-side extensions MSI and the PolicyPak license MSI. After configuring the Win32 app dependencues, make sure to assign the PolicyPak settings MSI to a user group.
| 1 | Open the Azure portal and navigate to Intune > Client apps > Apps to open the Client apps – Apps blade; |
| 2 | On the Client apps – Apps blade, select the just created [PolicyPakMSI] app to open the [PolicyPakMSI] app blade; |
| 3 | On the [PolicyPakMSI] app blade, select Dependencies to open the [PolicyPakMSI] app – Dependencies blade; |
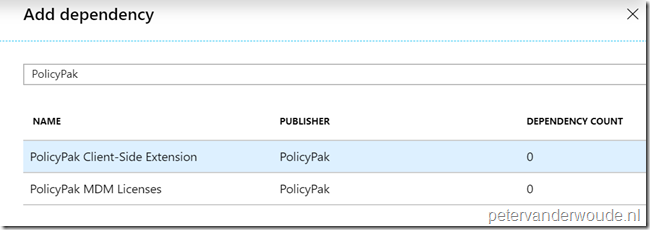
| 4 | On the [PolicyPakMSI] app – Dependencies blade, click Add to open the Add dependency blade; |
| 5 | On the Add dependency blade, select the [PolicyPakMSI] app and click Select to return to the [PolicyPakMSI] app – Dependencies blade; |
| — |  |
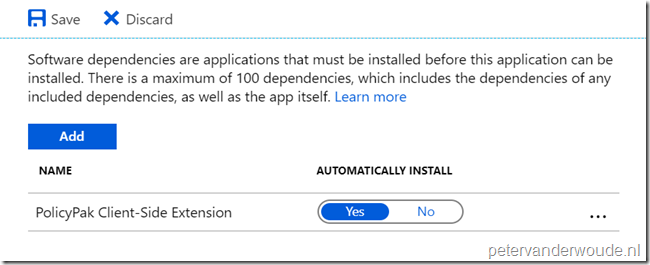
| 6 | Back on the [PolicyPakMSI] app – Dependencies blade, select Yes with AUTOMATICALLY INSTALL and click Save. |
| — |  |
Note: Keep in mind that these steps need to be performed for both dependencies.
Experience
Now let’s end this post by looking at the end-user experience and the administrator experience.
End-user experience
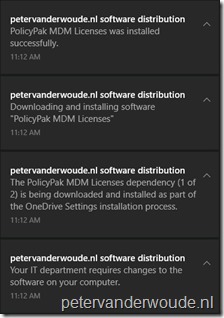
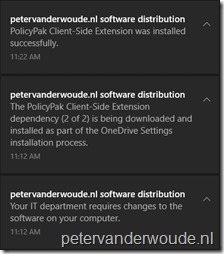
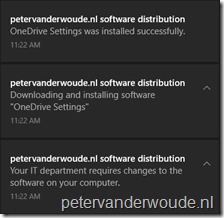
The first experience to look at is the end-user experience. Below, from left to right, is the end-user experience. As I configured the dependencies to automatically install, the dependencies will install before the actual assigned PolicyPak settings MSI. First the end-user will receive the message that PolicyPak license MSI will install as a part of the PolicyPak settings MSI installation. After a successful installation, the end-user will receive the message that the PolicyPak client-side extensions MSI will install as part of the PolicyPak settings MSI installation. And once that installation is successful, the PolicyPak settings MSI will install.
 |
 |
 |
Administrator experience
More information
For more information regarding Win32 apps and Win32 app dependencies, please refer to the following article:
- Intune Standalone – Win32 app management – App dependencies: https://docs.microsoft.com/en-us/intune/apps-win32-app-management#app-dependencies

Peter,
OK, I think you’re right – that’s how dependencies work for now.
But does it make sense?
1. Instead of just ordering the components I need to create a dependency chain.
That is not only non-intuitive in many cases it’s also not exactly flexible: any component but the last in the chain cannot be installed without its dependencies. Splitting components into different app packages and combining them by dependency relations only makes sense if the combinations are flexible and components may be used by different apps.
2. What about uninstallation?
The dependencies will not be uninstalled when uninstalling the “main” component, right?
What if I want to uninstall my app together with all of it’s components?
I think currently it is better to avoid dependencies and put all components into 1 app, installing and uninstalling them in my preferred order using a script.
Not exactly what I really want but works reliably.
I hope Microsoft will add the necessary functionality soon to make dependencies a really valuable feature.
– allow ordered installation of same level dependencies (and apps)
– allow the configuration of uninstallation options (always, never, if not needed by other app)
What do you think?
Cheers
Klaus
Hi Klaus,
You do have some fair points. However, do keep in mind that using separate apps make the troubleshooting a lot easier and it enables you to use the same app as a dependency for multiple apps.
Regards, Peter
Hi Peter,
Yes, using the same app in combination with other apps, that’s what I want!
But how would I do that?
Let’s have a look on you example scenario:
I want to combine just one of the components “PolicyPak settings MSI” with another app, let’s say an updated version of the main app.
I can’t because it would install its direct and indirect dependencies, too.
And what if I wanted to uninstall the PolicyPak client-side extension?
Using some runtimes as dependencies might work because they are used by multiple other apps and we usually leave them installed when uninstalling the main applications.
I can hardly think of any other scenario where the current dependencies would make sense but would certainly be very interested to learn how people actually use dependencies.
I think Microsoft will come up with an enhanced version of the dependencies and I hope they will deliver it in the not too far future.
Cheers
Klaus
BTW, I suggested to support defined ordering of same level dependencies on Uservoice – that would at least make dependency chains redundant if we want nothing else but a certain order of our dependencies.
Click it if you want it: https://microsoftintune.uservoice.com/forums/291681-ideas/suggestions/37589611-ordered-win32-app-dependencies
Hi Klaus,
Yes, you’re correct. Currently, the Win32 app dependency functionality does not fulfill all scenario’s. At this moment I’m creating a dependency chain to order the installations. That’s not possible yet. And no, that’s not always the most efficient way.. This is the initial version of this functionality, so probably updates will follow.
Regards, Peter
Nice post.
Do you know if there is any plan for Line of Business Apps be added as dependencies??
I have some legacy apps which need some components which are MSIs and currently i cant say they are a dependency because only other win32apps can be used.
Thanks
Hi Jose,
I’m not aware of those plans.
Regards, Peter
Hi Peter,
thanks for this great articel. I run into the issue, that I need to delte an application that has an dependency but I didn’t find a way yet to find out the dpendend apps. The dependency viewer just shows me the dependencies but not the apps that depend on this package. Do you have any ideas on that point?
Regards, Oliver
Hi Oliver,
I haven’t looked at that specifically yet, but I can imagine that it’s scriptable. Have you looked at PowerShell/Graph?
Regards, Peter
Hi Peter, this post is a couple of years old now but I’m looking for some additional info that doesn’t seem to be anywhere in MS’ own documentation.
If a dependency was created, how do I actually edit it after the fact? Do I have to remove the app completely?
Hi Adrian,
You can just edit the dependency section of the app, to make adjustments.
Regards, Peter
Where does this 100 dependencies limit come into play? Is that per chain or per your entire Intune instance?
Hi Edwin,
The total limit of all dependencies of all apps in the chain.
Regards, Peter
Hi Peter,
Can we deploy a dependency for an already deployed win32 app?
I know its weird and unexpected, but it worked for me.
Not sure if I completely understand what you’re asking..
Regards, Peter
Hi Peter, thanks for the article, very useful.
I have a large (12GB) Autodesk application that i’m making available through the Company Portal. This application has 3 dependencies which are basically 7zip split parts that are combined during the install.
Now when a users opens the Company Portal and so much as browses to the install page, the dependencies are already installing. Is this by design? It’s not what i want, I want them to install after the user clicks the install button…
Regards,
Mark
Hi Mark,
Are you saying that the dependencies start installing automatically? Even without triggering the installation?
Regards, Peter
Hi Peter,
Do you know if there is an easy way to see what Apps depend on a certain package. Let’s say, Visual C++, can I get an overview of the apps that are depending in this?
It would be nice if they appeared in the Dependency Viewer for Visual C++, but that’s obviously not the case.
//Jasper
Hi Jasper,
Not sure if it’s really easy, but PowerShell should give you your answers.
Regards, Peter
Thank you for your reply, Peter.
I’ll try some powershell.
Strange that Microsoft didn’t implement this into the dependency viewer. This should be relatively easy for them to do.
Best regards,
Jasper
What if you have a dependency you need to deploy to the virtual All Users groups (because it fails if installed to the All Devices Group), but the dependent app needs to be installed via All Devices group? I was experimenting with this recently. It seems that this isn’t possible because, and I’m just guessing here, during the ESP process Device Settings are applied first, and then User Settings are applied. It appears that Intune does not like it if you have an app that’s set to install to a User group that also happens to be a dependency for an app that’s assigned to a Device group since Device settings are applied first (I know there some exception here…). Have you seen this behavior? Does MS document this anywhere?
Hi Andrew,
Is the dependency configured to install automatically? If so, quote: “By automatically installing a dependent app, even if the dependent app is not targeted to the user or device, Intune will install the app on the device to satisfy the dependency before installing your Win32 app””
Regards, Peter