This week is all about Policy sets in Microsoft Intune. Policy sets are introduced a few months ago and enable administrators to group management objects that need to be identified and assigned as a single object. That can help with simplifying the administration of the environment. A Policy sets can be a group of almost all different object that are available within Microsoft Intune. That includes objects for different platforms within the same Policy sets. This enables an administrator to use Policy sets for a lot of different use case, from creating a standard for a specific user type to creating a standard set of apps for all users. In this post I’ll walk through the configuration steps and through the different steps I’ll describe the available options and challenges. I’ll end this post with some notes about the assignment of a Policy set.
Creating policy sets
Now let’s have a closer looking at Policy sets by walking through the configuration. The following 9 steps walk through the creation of a Policy set and the different options.
- Open the Microsoft Endpoint Manager admin center portal and navigate to Devices > Policy sets to open the Policy sets blade
- On the Policy sets blade, select Policy sets and click Create to open the Create a policy set wizard
- On the Basics page, provide the following information (see Figure 1) and click Next: Application management
- Policy set name: Provide a valid name for the Policy set
- Description: (Optional) Provide a description of the Policy set
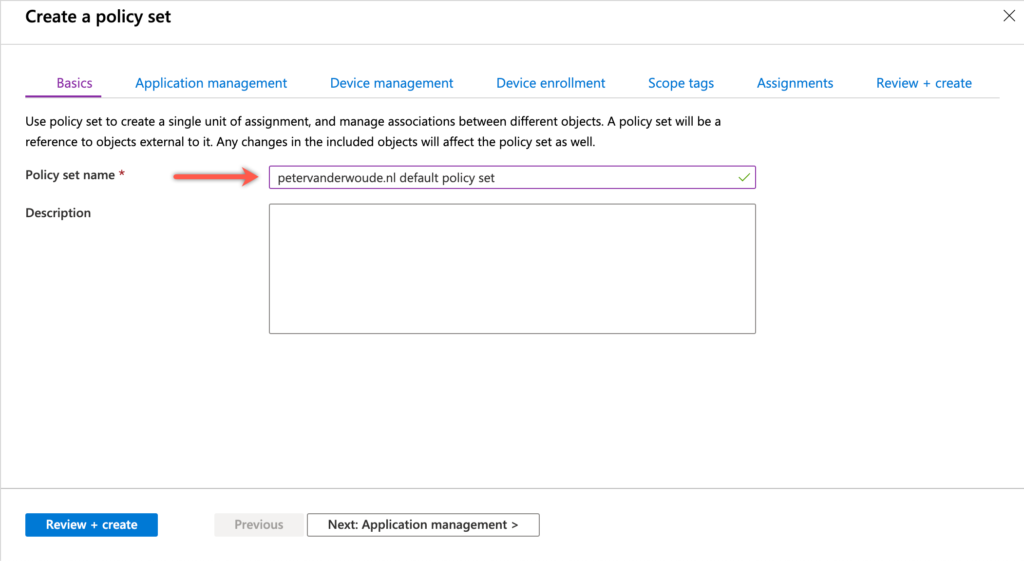
Figure 1: Basics page
- On the Application management page, provide the following information (see Figure 2) and click Next: Device management
- Apps: Click Select apps to add apps to the Policy set. That can be an iOS/iPadOS store app, an iOS/iPadOS line-of-business app, a Managed iOS/iPadOS line-of-business app, an Android store app, an Android line-of-business app, a Managed Android line-of-business app, an Office 365 ProPlus Suite (Windows 10), a Web link, a Built-in iOS/iPadOS app, or a Built-in Android app. That also means that a Windows app (Win32) is currently not supported. After adding an app to the Policy set, the assignment type can also be configured.
- App configuration policies: Click Select app configuration policies to add app configuration policies to the Policy set.
- App protection policies: Click Select app protection policies to add app protection policies to the Policy set. That can be an APP targeted at managed Windows devices, an APP targeted at managed iOS/iPadOSOS devices, an APP targeted at managed Android devices, an APP targeted at unmanaged iOS/iPadOSOS devices, or an APP targeted at unmanaged Android devices. That also means that APP targeted at unmanaged Windows devices are not supported.
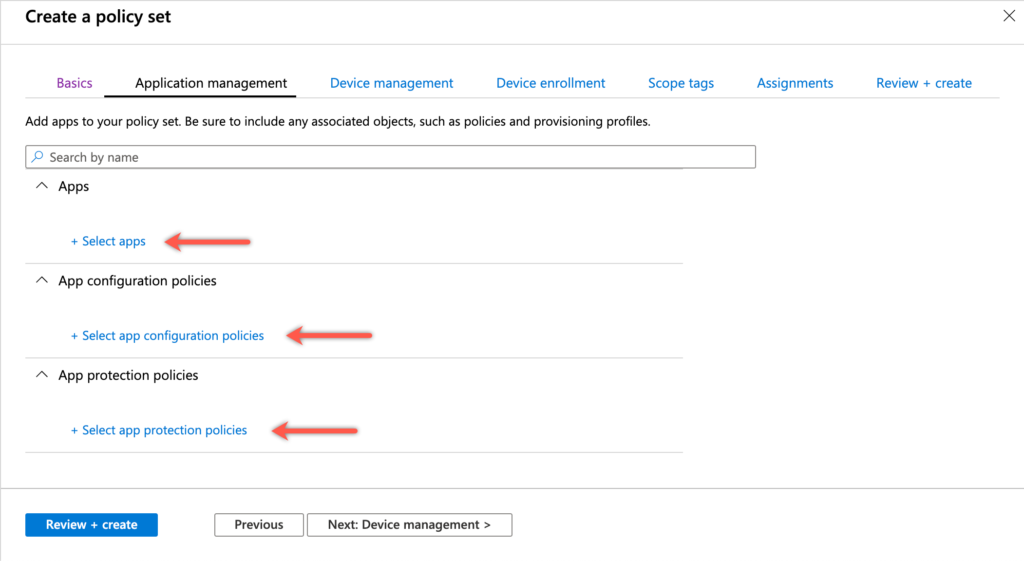
Figure 2: Application management page
- On the Device management page, provide the following information (see Figure 3) and click Next: Device enrollment
- Device configuration policies: Click Select device configuration policies to add device configuration policies to the Policy set.
- Device compliance policies: Click Select device compliance policies to add device compliance policies to the Policy set. Only the Android Enterprise device owner type policies are not available.
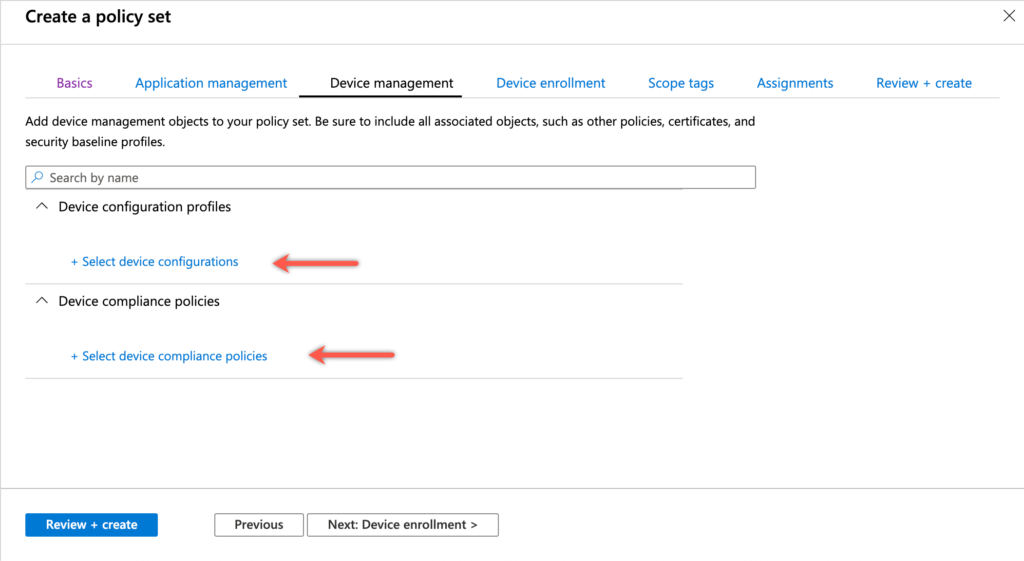
Figure 3: Device management page
- On the Device enrollment page, provide the following information (see Figure 4) and click Next: Scope tags
- Device type restrictions: Click Select device type restrictions to add custom device type restrictions to the Policy set.
- Windows autopilot deployment profiles: Click Select Windows autopilot deployment profiles to add Windows autopilot deployment profiles to the Policy set.
- Enrollment status pages: Click Select enrollment status page profiles to add custom enrollment status page profiles to the Policy set.
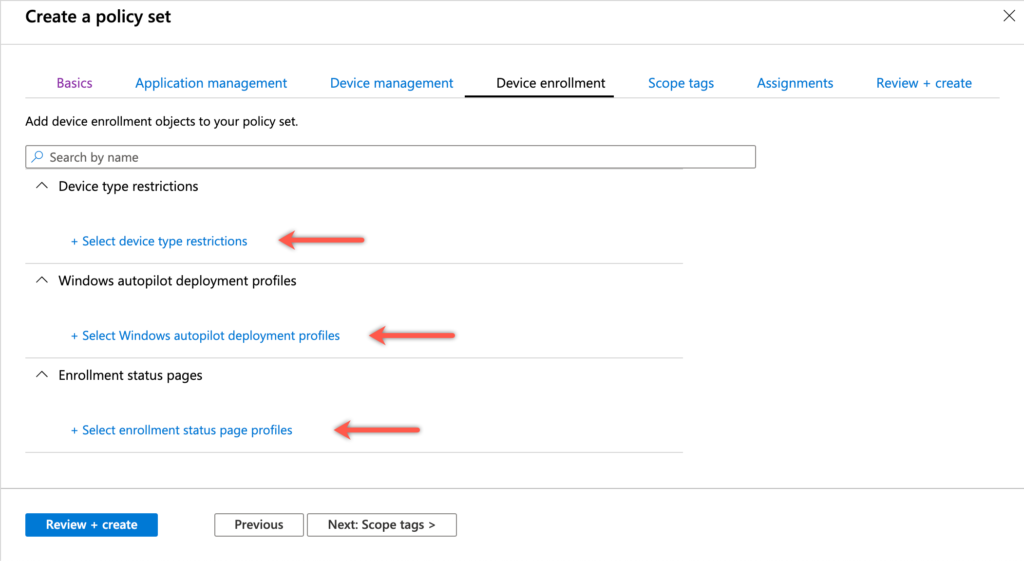
Figure 4: Device enrollment page
- On the Scope tags page, provide the following information (see Figure 5) and click Next: Assignments
- Scope tags: Click Select scope tags to add custom scope tags to the Policy set.
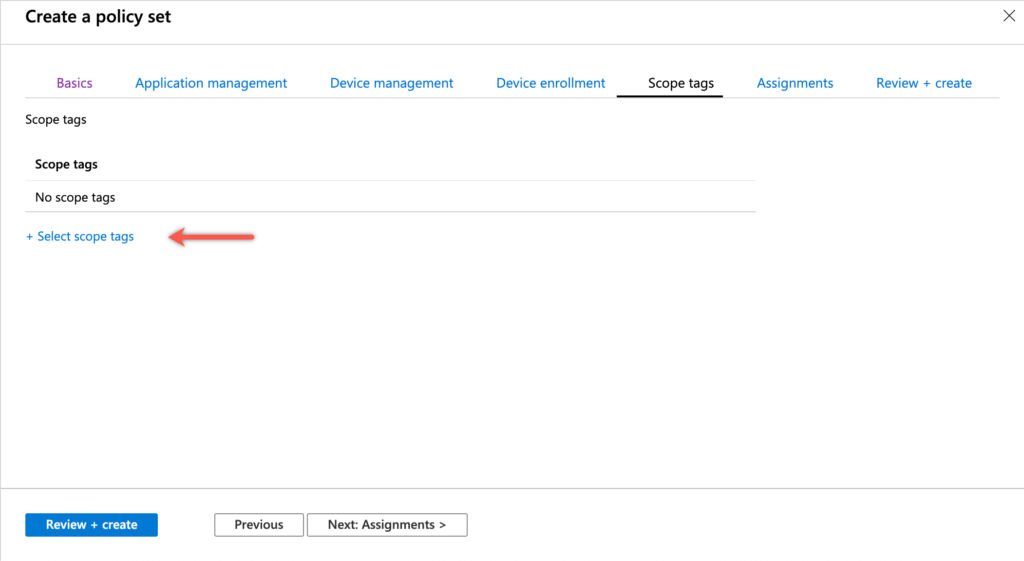
Figure 5: Scope tags page
- On the Assignments page, provide the following information (see Figure 6) and click Next: Review + create
- Included groups: Click Select groups to include to include groups to the assignment of the Policy set.
- Excluded groups: Click Select groups to exclude to exclude groups from the assignment of the Policy set
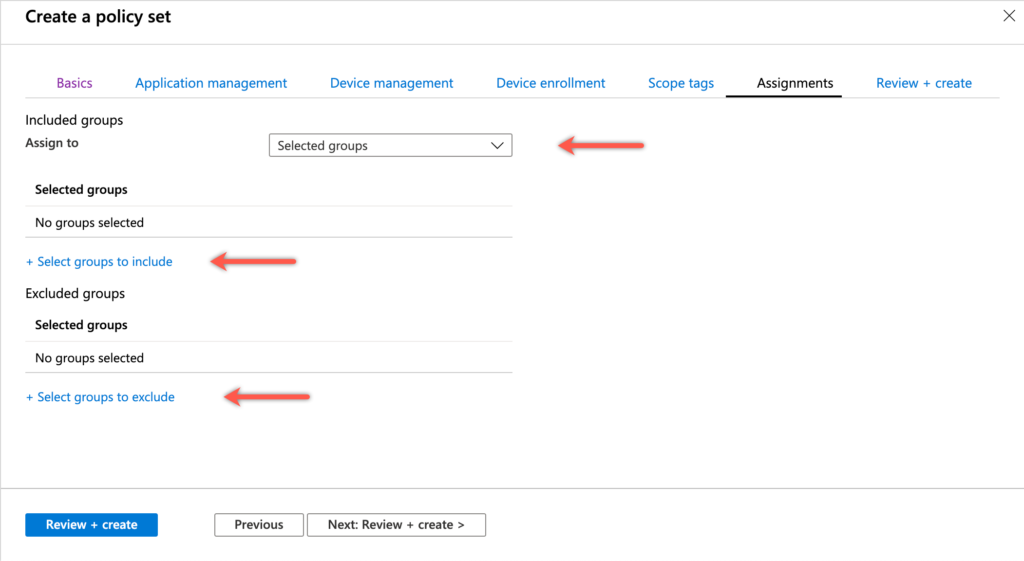
Figure 6: Assignments page
- On the Review + create page, verify the following information and click Create
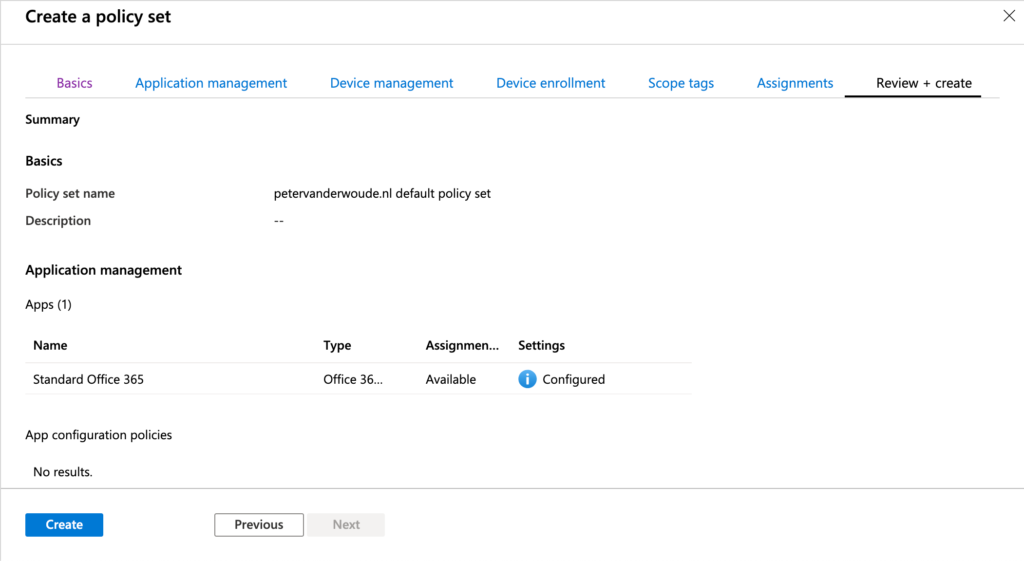
Figure 7: Review + create page
After going through the configuration of a Policy set it’s good to note that security baselines are not part of a Policy set configuration. The guided scenario Try out a cloud-managed PC also creates a policy set to group the different objects that are created during the guided scenario and that are supported as being a part of the guided scenario. That scenario also creates a security baseline assignment that is not part of the created Policy set. Guided scenarios are available on the Home page of the Microsoft Endpoint Manager admin center.
For automation purposes, it might be better to know how to automate the device type restriction configuration. That can be achieved by using the policySet object in the Graph API.
https://graph.microsoft.com/beta/deviceAppManagement/policySetsAssignment notes
Let’s end this post with some notes about the assignment of a Policy set. The following should be kept in mind when creating the assignment for the Policy set.
- The different non-Windows app protection policies (APP) do not support an assignment via a Policy set. In that case the group will be added as a direct assignment. Those assignments will not be deleted when the assignment of the Policy set is removed.
- The different APPs do not support an assignment to All users or All devices
- A Windows autopilot deployment profile does not support an assignment to All users
- An Enrollment status page profile does not support the assignment of virtual groups (All users, All devices or All user & All devices)
- An Device type restriction profile does not support the assignment of virtual groups (All users, All devices or All user & All devices)
When the assignment of the Policy set is created it will show as a specific assignment with the different objects that are part of the Policy set (as shown in Figure 8).
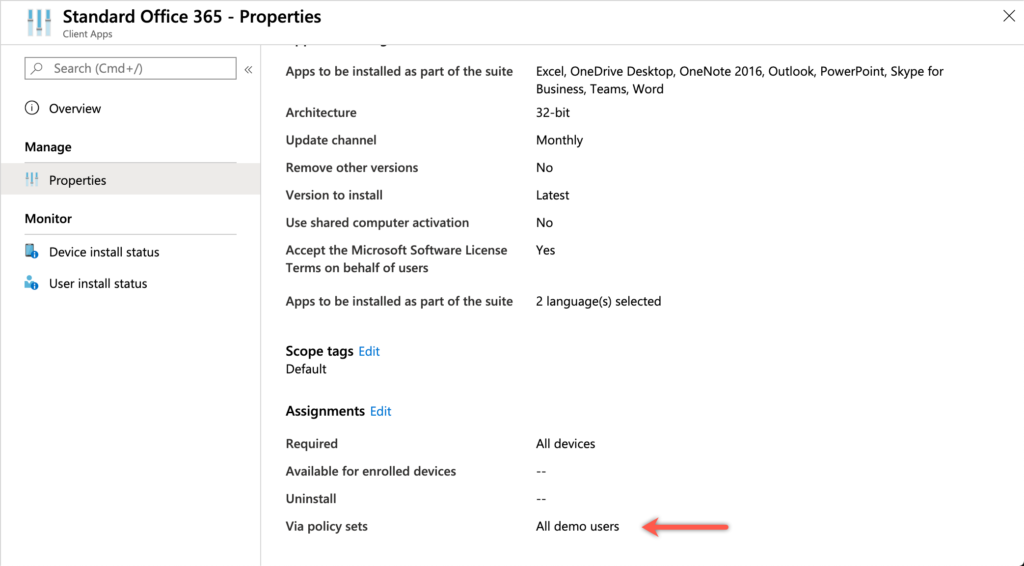
Figure 8: Policy set assignment
More information
For more information about using policy sets for managing groups of objects in Microsoft Intune, refer to the documentation about Use policy sets to group collections of management objects.
This is definitely interesting, but needs support for both Win32 applications and powershell scripts to be really useful. Hopefully it’s in the pipeline.
Agree, Pär!
Can you control the order in which policy sets are applied.
Hi Clive,
Not to my knowledge.
Regards, Peter
Have you come across the issue of Android config policies not showing up when you try to add them to the policy set? When you select to bring up the config policy search box, it only lists windows policies but won’t show any android config policies to select.
Hi Damian,
I have to admit that I haven’t looked at policy sets recently, but I just did and I do see the same. You might want to report that with Microsoft.
Regards, Peter