Configuring Windows Hello for Business cloud Kerberos trust
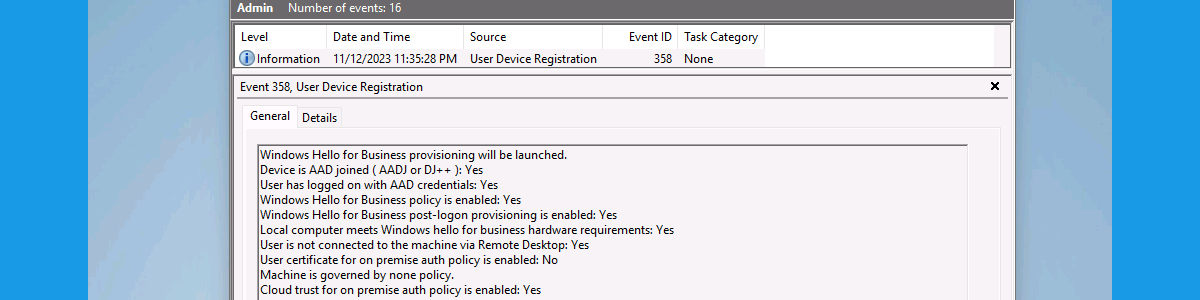
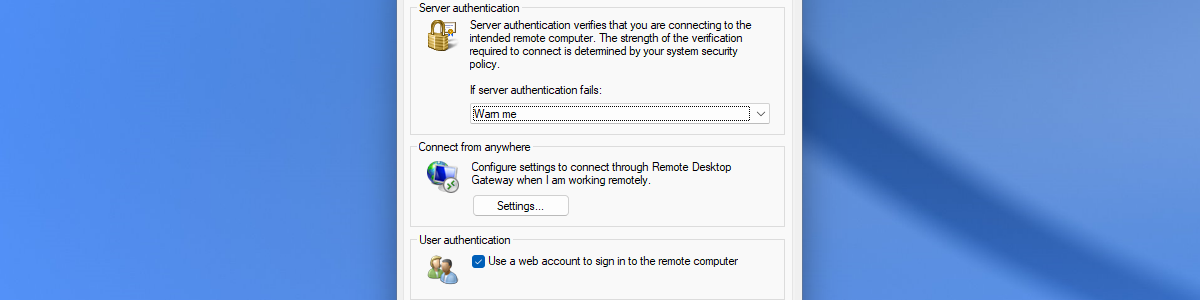
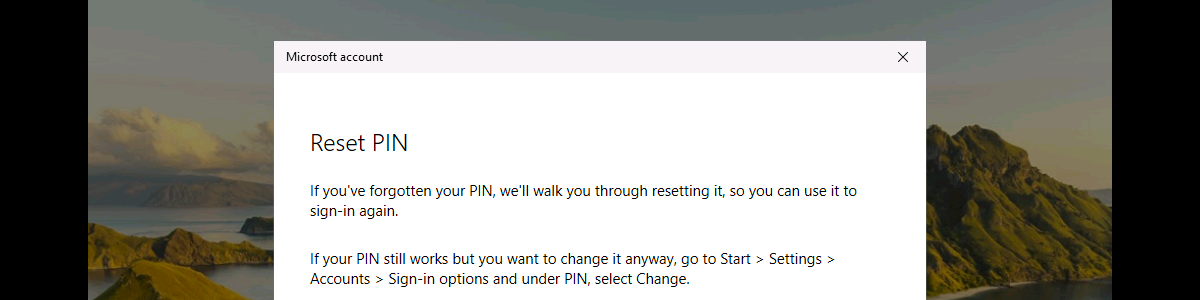
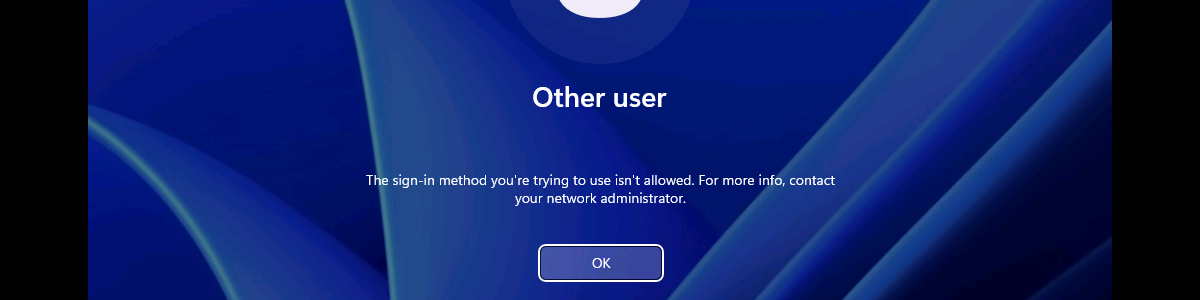
This week is all about Windows Hello for Business. More specifically, about Windows Hello for Business cloud Kerberos trust. Not something really new, but definitely something that should be part of the default toolset. Hopefully familiar nowadays, Windows Hello for Business can be used to replace password sign-in with strong authentication on Windows. On top of that, Windows Hello for Business cloud Kerberos trust brings a simplified deployment experience for hybrid authentication with Windows Hello for Business. To provide that functionality, it relies on Microsoft Entra Kerberos for requesting Kerberos ticket-granting-tickets (TGTs). And those TGTs can then be used for on-premises authentication. A bing difference with other deployment models is the simplicity. No dependency on a public key infrastructure (PKI) and no need to synchronize …