This week is all about the just, during Microsoft Ignite 2020, released Microsoft Tunnel Gateway (often referred to as Microsoft Tunnel or Tunnel). Microsoft Tunnel Gateway is a new solution that can provide iOS and Android devices with access to on-premises resources. In other words, Microsoft Tunnel Gateway is a VPN solution. The best part of Microsoft Tunnel Gateway is that it fully integrates with a Microsoft 365 solution and that it’s included in the existing Microsoft Intune license. That integration is also one of the strongest points of Microsoft Tunnel Gateway, as it also provides single sign-on capabilities and even conditional access. All of that with a relatively simple deployment. Also, to work with Microsoft Tunnel Gateway, Microsoft released the Microsoft Tunnel app for iOS and Android. That app can be deployed to users and can be used to provide access via Microsoft Tunnel Gateway. That provides a truly great experience for the user. In this post I want to walk through the prerequisites for Microsoft Tunnel Gateway, followed with the different configurations to configure Microsoft Tunnel Gateway. I’ll end this post by distributing the app and configurations to the user and by looking at the user experience.
Important: At this moment, Microsoft Tunnel Gateway is a solution for iOS and Android only.
Prerequisites for Microsoft Tunnel Gateway
For this post it’s important to start with a list of prerequisites for Microsoft Tunnel Gateway. The main reason for that is that I’ll leave a few subjects out-of-scope for this post, but those subjects are important for getting started with Microsoft Tunnel Gateway. Make sure that the following is in place, before starting with Microsoft Tunnel Gateway.
- a server with a supported Linux distribution that will be used for hosting Microsoft Tunnel Gateway
- Docker is installed on the server to support containers on the Microsoft Tunnel Gateway server
- a (preferably publicly) trusted TSL certificate, that contains the public FQDN of the Microsoft Tunnel Gateway server, is available for securing the connection between the devices and the Microsoft Tunnel Gateway server
- inbound port 443 (UDP and TCP) is available on the server for a functioning Microsoft Tunnel Gateway
- outbound port 80 (TCP) and 443 (TCP) is available on the server for interaction with Microsoft Intune
- add Microsoft Tunnel Gateway as a cloud app to Azure AD to enable the use of Conditional Access
My setup
Also, I thought it would be a good idea for this post to provide some information about the starting point that I’ll use for the configurations that are provided throughout this post. That starting point is described below.
- a virtual server that is running Ubuntu 20.04
- Docker is installed on that virtual Ubuntu 20.04 server by using these configuration steps
- a publicly trusted certificate for *.petervanderwoude.nl is available
- an A-record is configured for vpn.petervanderwoude.nl
- a gateway router is used to forward port 443 to the virtual Ubuntu 20.04 server
Create the server configuration
The first Microsoft Intune related configuration is the Server configuration. The Server configuration is used to create a configuration that can be applied to one or multiple Microsoft Tunnel Gateway servers. That contains the configuration that will be used for configuring the Microsoft Tunnel Gateway server. That contains information like the IP address range that is used for devices connecting to Microsoft Tunnel Gateway and the port that the Microsoft Tunnel Gateway server is listening to. This information can also be adjusted when Microsoft Tunnel Gateway is up-and-running, but that would require a restart of the server to apply the new configuration. The following five steps walk through creating the Server configuration.
- Open the Microsoft Endpoint Manager admin center portal navigate to Tenant administration > Microsoft Tunnel Gateway (Preview) to open the Tenant admin | Microsoft Tunnel Gateway (Preview) blade
- On the Tenant admin | Microsoft Tunnel Gateway (Preview) blade, navigate to Server configurations and click Create new to open the Create server configuration wizard
- On the Basics page, provide the following information and click Next
- Name: Provide a valid name for the server configuration
- Description: (Optional) Provide a valid description for the server configuration
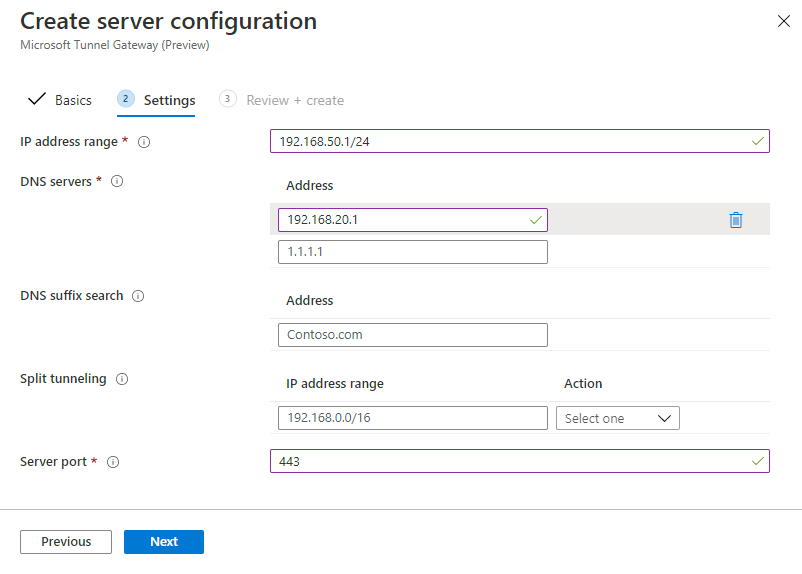
- On the Settings page, provide the following information and click Next
- IP address range: Provide an IP address range that is leased to devices that connect to Microsoft Tunnel Gateway
- DNS servers: Provide DNS server addresses that are used for DNS request from devices that are connected to Microsoft Tunnel Gateway
- DNS suffix search: (Optional) Provide a DNS suffix that is used as default domain for devices that are connected to Microsoft Tunnel Gateway
- Split tunneling: (Optional) Provide addresses that are included or excluded from Microsoft Tunnel Gateway
- Server port: Provide the port that Microsoft Tunnel Gateway listens to
- On the Review + create page, verify the information and click Create
Important: The server port will also be used for the configuration of the Microsoft Tunnel app.
Create the site
The second Microsoft Intune related configuration is creating a Site. A Site is used to create a logical group of servers that host Microsoft Tunnel Gateway. A Site contains two important configurations that are applied to all the Microsoft Tunnel Gateway servers in the site and that’s the public address and the Server configuration that should be applied. Make sure that the Site is configured correctly, as it can’t be adjusted afterwards. The following three steps walk through the creation of a Site.
- Open the Microsoft Endpoint Manager admin center portal navigate to Tenant administration > Microsoft Tunnel Gateway (Preview) to open the Tenant admin | Microsoft Tunnel Gateway (Preview) blade
- On the Tenant admin | Microsoft Tunnel Gateway (Preview) blade, navigate to Sites and servers and click Create > New site to open the Create a site page
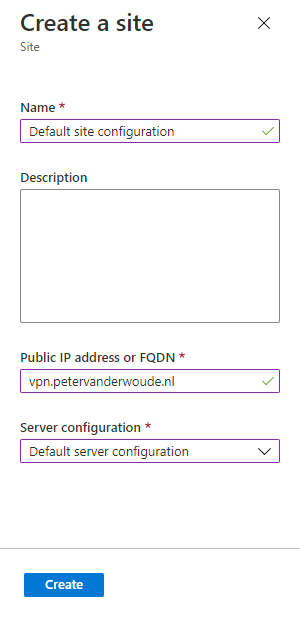
- On the Create a site page, provide the following information and click Create
- Name: Provide a valid name for this site
- Description: (Optional) Provide a valid description for this site
- Public IP address or FQDN: Provide a public IP address or FQDN that is used by the devices as the connection point to to Microsoft Tunnel Gateway
- Server configuration: Select the just created server configuration
Note: The IP address or FQDN can point to an individual server or to a load-balancing server. When there is a firewall in between, make sure to create the necessary network adjustments.
Important: The IP address must be publicly routable and the FQDN must be publicly resolvable.
Install Microsoft Tunnel Gateway
After creating the Site and the Server configuration that can be applied to a Microsoft Tunnel Gateway server, it’s time to start with the actual installation of Microsoft Tunnel Gateway on the created Linux server with Docker. The installation is performed by downloading and running the Microsoft Tunnel Gateway installation script on the Linux server with Docker installed. The Microsoft Tunnel Gateway installation script will walk through the different required actions that should be performed to get the Microsoft Tunnel Gateway server up-and-running and interacting with Microsoft Intune. The following seven steps walk through that process.
- Connect to the Linux server with Docker and logon
- Download the Microsoft Tunnel Gateway installation script by using a command like this
wget https://aka.ms/microsofttunneldownload -O mstunnel-setup- Start the Microsoft Tunnel Gateway installation script by using a command like this
sudo bash mstunnel-setup- When prompted by the Microsoft Tunnel Gateway installation script, accept the license agreement (EULA)
- When prompted by the Microsoft Tunnel Gateway installation script, copy the TLS certificate to the specified location
Important: The name of the certificate file(s) is mandatory for the Microsoft Tunnel Gateway installation script to detect the existence of the required certificate file(s).
- When prompted by the Microsoft Tunnel Gateway installation script, register Microsoft Tunnel Gateway with Microsoft Intune by opening a browser, navigating to https://microsoft.com/devicelogin and entering the code that was provided by the Microsoft Tunnel Gateway installation script
Tip: The browser action can be performed on a different device.
Note: The Microsoft Tunnel Gateway script will prompt to enter a GUID of the site that this Microsoft Tunnel Gateway server should join, when multiple sites are configuration in Microsoft Intune.
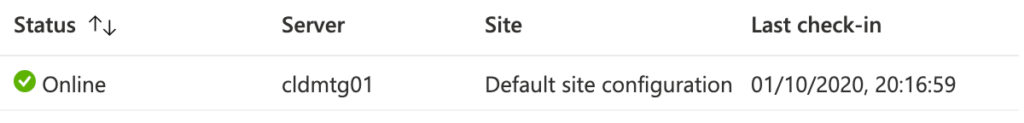
- After the Microsoft Tunnel Gateway installation script is finished, the server will show in the Microsoft Endpoint Manager admin center portal when navigating to Tenant administration > Microsoft Tunnel Gateway (Preview) > Health status as shown below in Figure 3.
Tip: When the Microsoft Tunnel Gateway installation script is stopped, it can be restarted again by using the same installation command. The installation will continue were it was stopped.
Deploy Microsoft Tunnel app
Once Microsoft Tunnel Gateway is up-and-running and online, it’s time to look at the device configurations. The first thing of those configurations is distributing the Microsoft Tunnel app. The Microsoft Tunnel app is required for accessing resources via Microsoft Tunnel Gateway on a mobile device. As the steps differ per platform, the most common options for deploying the Microsoft Tunnel app are described below per platform.
Deploy Microsoft Tunnel app for Android
The following seven steps walk through the process of distributing the Microsoft Tunnel app to the different Android Enterprise managed devices. As this is focused on Android Enterprise, the focus is on the Managed Google Play store.
- Open the Microsoft Endpoint Manager admin center portal navigate to Apps > All apps > Android to open the Android | Android apps blade
- On the Android | Android apps blade, click Add to open the Select app type blade
- On the Select app type blade, select Managed Google Play app as App type and click Select to open the Managed Google Play page
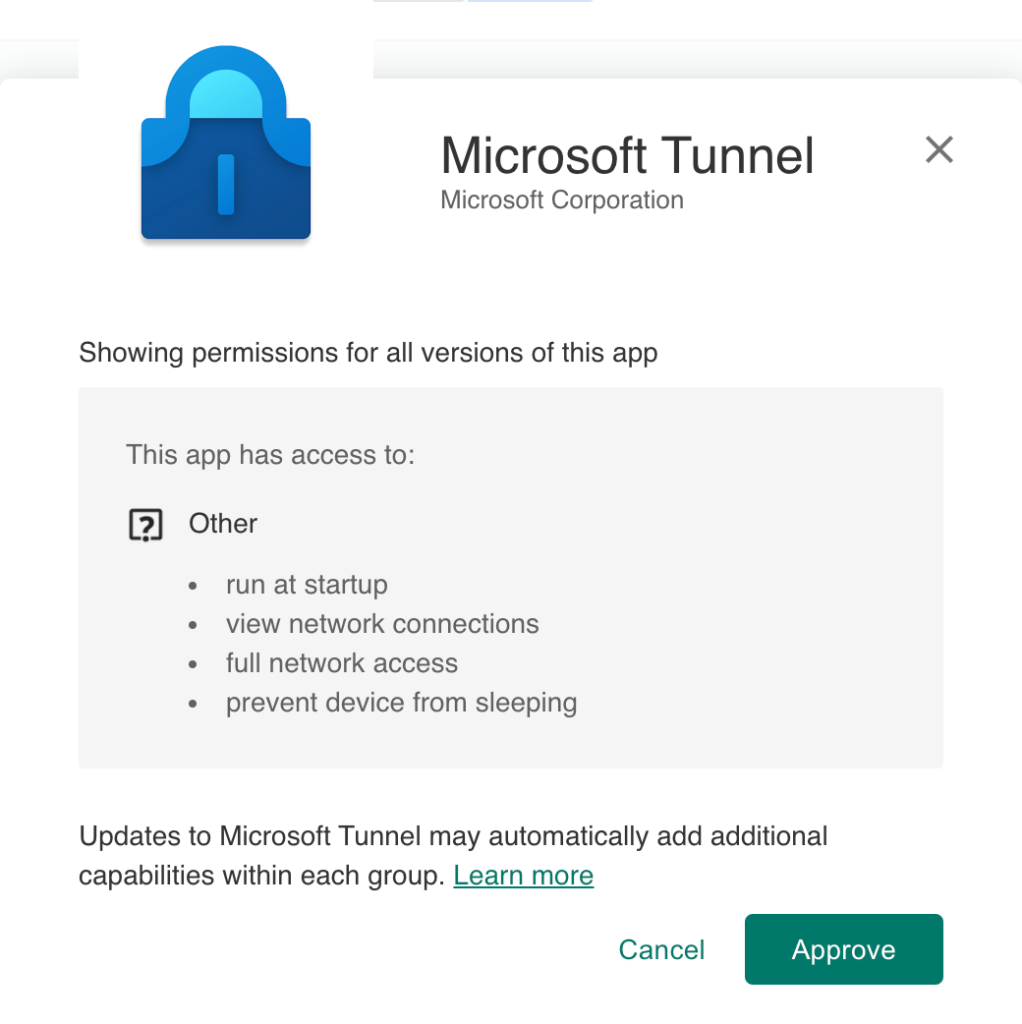
- On the Managed Google Play page, search for the Microsoft Tunnel app, select the app (as shown in Figure 4) and click Approve
- On the Approval settings dialog, select Keep approved when app requests new permissions click Done
- Click Sync to synchronize the approval to Microsoft Intune
- Assign the Microsoft Tunnel app to the required users and/or devices
Deploy Microsoft Tunnel app for iOS/iPadOS
The following seven steps walk through the process of distributing the Microsoft Tunnel app to iOS/iPadOS devices. As my lab doesn’t contain Apple Business Manager (ABM), the focus is on the normal App Store.
- Open the Microsoft Endpoint Manager admin center portal navigate to Apps > All apps > iOS/iPadOS to open the iOS/iPadOS | iOS/iPadOS apps blade
- On the iOS/iPadOS | iOS/iPadOS apps blade, click Add to open the Select app type blade
- On the Select app type blade, select iOS store app as App type and click Select to open the Add app wizard
- On the App information page, click Search the App Store, select the Microsoft Tunnel app (as shown in Figure 5) and click Select and click Next
- On the Scope tags page, click Next
- On the Assignments page, configure the assignment to the required users and/or devices and click Next
- On the Review + create page, verify the configuration and click Create
Deploy VPN profile
Once Microsoft Tunnel Gateway is up-and-running and online and the Microsoft Tunnel app is deployed to the mobile devices, it’s time to configure and deploy the VPN profile. The VPN profile is used to apply the correct configuration to the Microsoft Tunnel app and to make sure that the device can connect via Microsoft Tunnel Gateway.
Deploy VPN profile on Android
The following eight steps walk through the process of creating a VPN profile for the different Android Enterprise managed devices. Even thought the corporate-owned device and personal device deployment scenarios require a separate VPN profile, the steps below are applicable for both deployment scenarios.
- Open the Microsoft Endpoint Manager admin center portal navigate to Devices > Android > Configuration profiles to open the Android | Configuration profiles blade
- On the Android | Configuration profiles blade, select Create profile to open the Create a profile page
- On the Create a profile page, provide the following information and click Create
- Platform: Android Enteprise
- Profile: Select Fully Managed, Dedicated, and Corporate-Owned Work Profile > VPN or select Work Profile > VPN, depending on the Android Enterprise deployment scenario to open the VPN wizard
- On the Basics page, provide the following information and click Next
- Name: Provide a valid name for the VPN profile
- Description: (Optional) Provide a valid description for the VPN profile
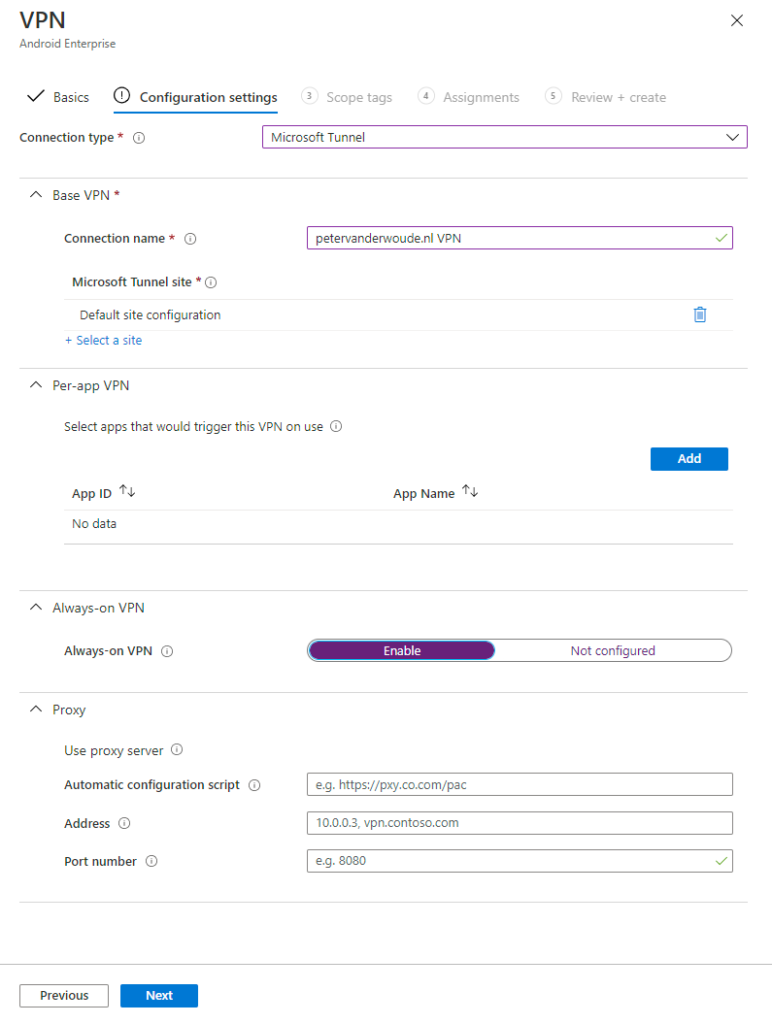
- On the Configuration settings page, provide the following information and click Next
- Connection type: Select Microsoft Tunnel
- Connection name: Provide a valid name for the VPN profile that will be shown to the user in the Microsoft Tunnel app
- Microsoft Tunnel site: Select the Site that will be used by this VPN profile
Note: When selecting the Site, the configuration also shows the complete public address that will be used for the Microsoft Tunnel app configuration.
- Select apps that would trigger this VPN on use: (Optional) Add apps that should use this VPN profile to send app traffic to the tunnel
Note: When adding apps to this VPN profile, this VPN profile will only be used as a per-app VPN.
- Always-on VPN: (Optional) Select Enable to make sure that the VPN will automatically connect and reconnect
- Automatic configuration script: (Optional) Configure the location of the automatic configuration script, when a proxy should be used
- Address: (Optional) Configure the address of the proxy server, when a proxy should be used
- Port number: (Optional) Configure the port number of the proxy server, when a proxy should be used
- On the Scope tags page, click Next
- On the Assignments page, configure the assignment to the required users and/or devices and click Next
- On the Review + create page, verify the configuration and click Create
Deploy VPN profile on iOS/iPadOS
The following eight steps walk through the process of creating a VPN profile for iOS and iPadOS devices. These steps are nearly identical to the steps for creating a VPN profile for Android Enterprise device, but only the available configurations for per-app VPN, in step 5, are slightly different.
- Open the Microsoft Endpoint Manager admin center portal navigate to Devices > iOS/iPadOS > Configuration profiles to open the iOS/iPadOS | Configuration profiles blade
- On the iOS/iPadOS | Configuration profiles blade, select Create profile to open the Create a profile page
- On the Create a profile page, provide the following information and click Create
- Platform: iOS/iPadOS
- Profile: Select VPN to open the VPN wizard
- On the Basics page, provide the following information and click Next
- Name: Provide a valid name for the VPN profile
- Description: (Optional) Provide a valid description for the VPN profile
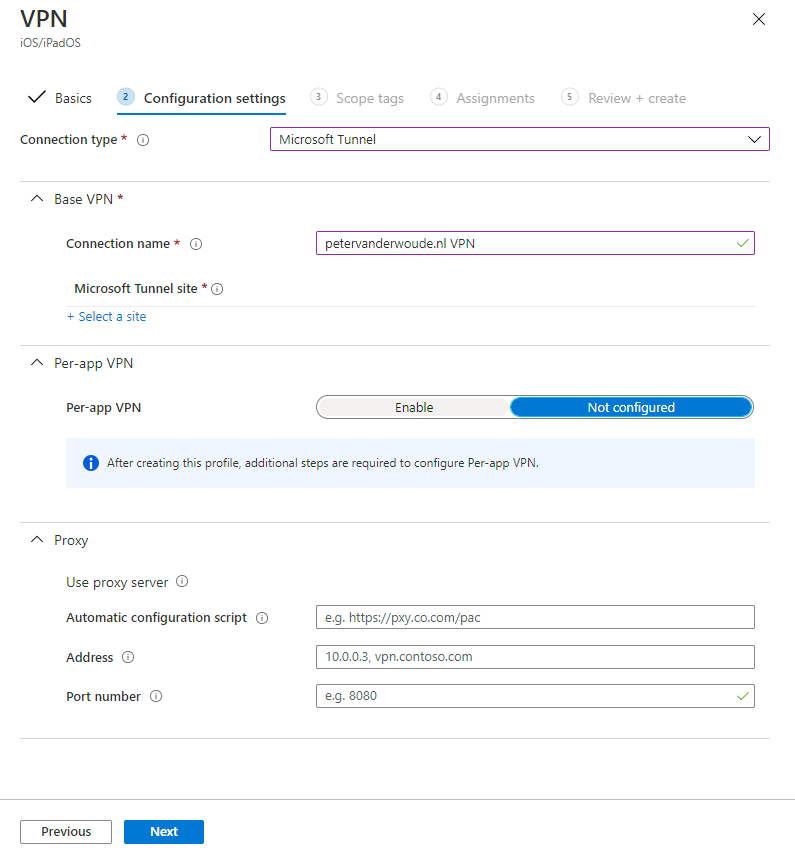
- On the Configuration settings page, provide the following information and click Next
- Connection type: Select Microsoft Tunnel
- Connection name: Provide a valid name for the VPN profile that will be shown to the user in the Microsoft Tunnel app
- Microsoft Tunnel site: Select the Site that will be used by this VPN profile
Note: When selecting the Site, the configuration also shows the complete public address that will be used for the Microsoft Tunnel app configuration.
- Per-app VPN: (Optional) Select Enable when this profile should be used for per-app VPN
Note: When enabling per-app VPN, an app should be specifically associated with the VPN profile.
- Automatic configuration script: (Optional) Configure the location of the automatic configuration script, when a proxy should be used
- Address: (Optional) Configure the address of the proxy server, when a proxy should be used
- Port number: (Optional) Configure the port number of the proxy server, when a proxy should be used
- On the Scope tags page, click Next
- On the Assignments page, configure the assignment to the required users and/or devices and click Next
- On the Review + create page, verify the configuration and click Create
Conditional access reflections
As mentioned in the prerequisites, to facilitate a working Microsoft Tunnel Gateway in combination with Conditional Access, a Microsoft Tunnel Gateway cloud app should be registered in Azure AD. That cloud app can be used in the different Conditional Access rules within an organization. Without adding that cloud app to Azure AD, and assigning Conditional Access rules to all cloud apps, those Conditional Access rules will also be applicable to Microsoft Tunnel Gateway. Of course, that doesn’t have to be a bad thing. However, one scenario to keep in mind is with requiring an approved client app or a requiring an app protection policy. The problem is that the Microsoft Tunnel app is not yet on the list of approved client apps or on the list of app protection policy apps. That means that the Microsoft Tunnel app will be blocked when either one of those settings is applicable to Microsoft Tunnel Gateway. Requiring a compliant device is not a problem.
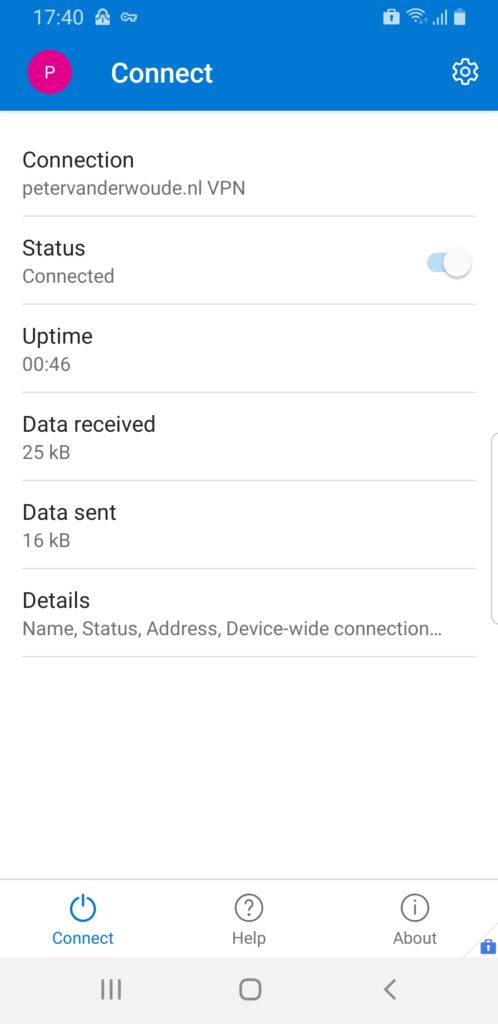
End-user experience
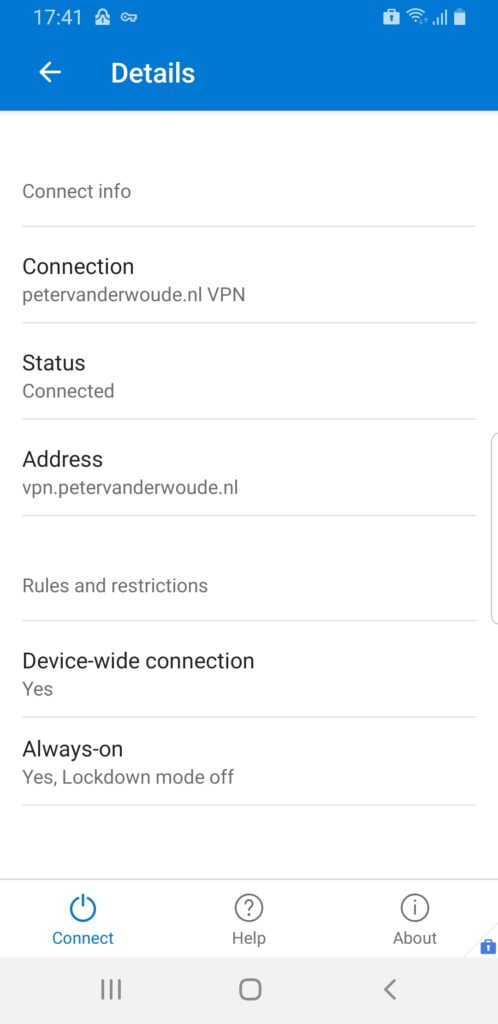
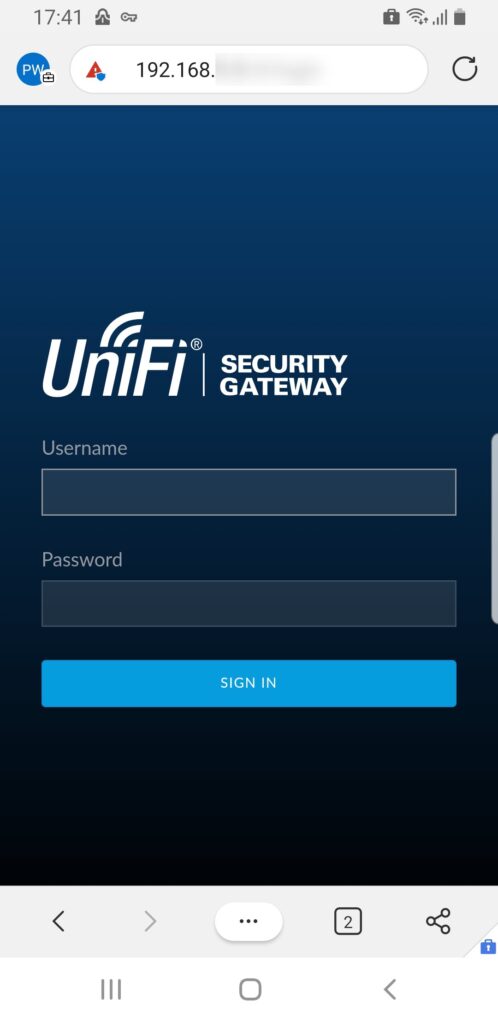
The best way to end this long post is by looking at the end-user experience. More specifically, a successful end-user experience. Below are three screenshots that are showing a working connection with Microsoft Tunnel Gateway. Figure 8 provides an example of the basic connection information. That contains information about the status. uptime, data sent and received and the name of the connection. The latter can be related to the name in the VPN profile. Figure 9 provides an example about the details of the connection. That contains information about the type of VPN (per-app versus device-wide), if always-on is enabled and also the name and status. All of that information can be related to the configured VPN profile. Figure 10 provides an example of a connection to an internal resource (with internal IP) within my environment. The icons on the top left of the screen show the successful VPN connection that is still on.
Note: An administrator can look at more details about the status of Microsoft Tunnel Gateway, by using the mst-cli command line tool on the Microsoft Tunnel Gateway server. That tool can be used to look at details, like the status, statistics, connected users and much more.
More information
For more information about Microsoft Tunnel Gateway, refer to the following docs
Thanks for your instructions, but I run into issues when trying to run the tunnel gateway behind a nginx reverse proxy. (As you know public ipv4 addresses are rare) Do you have gained any experiences with this construct?
Best regards,
Tom
Hi Tom,
I’m sorry, but I don’t have any experience with that specific reverse proxy. What is the challenge that you’re running in to?
Regards, Peter
Nice guide, helped me a ton.
However trying to get this working on Android Enterprise fully managed (the only i’ve tried so far) seems far from trivial.
after the configuration profile is applied the tunnel application still reports no connection profiles, i’ve removed assignments and reapplied the profile many times.
have you seen this problem at your end?
Andoid 10
tunnel installed
fully managed dedicated device
all profiles deployed to device group in AAD
Hi Temilit,
No, I haven’t seen that behavior yet. Only the other way around, in a way that the profile was applied but not reported in the portal. If you consistently see that behavior, I would advise you to log a support ticket with Microsoft.
Regards, Peter
Hi,
great article, we still got one problem. per app vpn is working for acutally deployed iphone’s. but when we deploy a complete new iphone the vpn tunnel it will not work. any idea ?
Hi Daniel,
I haven’t seen that specific behavior yet. If you can reproduce that behavior constantly, I would advise to register a support case with Microsoft.
Regards, Peter
We have implemented the Tunnel service for a customer. We have the issue that we have connected Microsoft Edge with the per app vpn configuration but edge is tunneling the whole traffic through the tunnel now indepentent if intranet access is required. Is it possible to define a split tunneling here so that the vpn is only used for specific endpoints/domains?
Hi Marcel,
You can configure split tunnel rules in the server configuration.
Regards, Peter
Is a public ip address required on the nic of the linux VM, or can we placce the linux vm behind a firewall and NAT 443 to the linux vm and thus giving the linux vm a private IP ?
Hi Rkast,
As mentioned in one of the notes, the IP address or FQDN can point to an individual server or to a load-balancing server. When there is a firewall in between, make sure to create the necessary network adjustments. So, yes you can place it behind a firewall.
Regards, Peter
Hi Peter, thanks! Yes I did read it but on the docs it’s a bit cryptic if you take the text litterally. “NIC 1 – This NIC handles traffic from your managed devices and should be on a public network with public IP address. ”
I meant the not in my post. The VM doesn’t need a public IP itself.
Regards, Peter
So just to clarify a little more in regards to this. The Linux VM should be in the trusted network not the DMZ? I’ve asked a few MSPs and none have been able to verify this…actually one has told me that we need to put it in the DMZ…but that doesn’t sound like the case.
Hi Luke,
The Linux VM can be basically anywhere were your security and/or networking team requires it to be. As long as the networkpaths are available to the Internet and to the internal resources.
Regards, Peter
Hi Peter,
We have MS Tunnel servers setup and configured with thresholds. Sometimes when they are unhealthy due to memory or CPU, I can open the link under “Name” and see the parameters. However for one of the server in unhealthy state, I could not open the server under Name.
Status Name Site last check in
When I open it I get the error – Server if offline. Please check network connectivity and firewall is configured properly
The server is however up and running with the CPU and memory also fine. What could the reason for this error in the Intune Portal ?
Regards
NG
Hi NG,
I’ve only had that with a test-server that was often off for a while. In that case after turning on the server, it would function correctly but the portal wouldn’t update the status. To fix the status in the portal I think you should reach out to Intune Support.
Regards, Peter
Hi Peter, I tried to configure split tunneling for Android to optimize traffic for my device. PerApp is disabled for the moment. I have a strange behaviour when i define IP range though the tunnel. Seems that only these IP included are working from Chrome browser. The other traffic seems blocked. The Linux server have one NIC i know that MS recommended 2 NIC but i see nothing related that split tunneling is not support on 1 NIC. Do you have an idea or already see that behaviour? Thank you for this article.
Hi Xavier,
I’m trying to understand this: are you saying that when you configure split tunneling, only the specified IPs are allowed and the rest is blocked?
Regards, Peter