 This week a short blog post about my tweet of a bit more than a week ago. In that tweet I mentioned a new easy method to automagically convert Intune managed devices to AutoPilot. That method makes some scenarios a whole lot easier. Like for example what I did in this post to get the AutoPilot device information of Intune managed devices. That type of custom scripting is not needed anymore!
This week a short blog post about my tweet of a bit more than a week ago. In that tweet I mentioned a new easy method to automagically convert Intune managed devices to AutoPilot. That method makes some scenarios a whole lot easier. Like for example what I did in this post to get the AutoPilot device information of Intune managed devices. That type of custom scripting is not needed anymore!
As I got many reactions to that tweet, mainly related to the location of that configuration, I thought it would be good to make a short post describing the configuration option and the expected behavior. In this post I’ll provide the steps to make this configuration and I’ll describe the expected behavior. There is no real end-user or administrator experience to show for this configuration. So, no section related to that. I’ll do explain the the expected behavior in the introduction.
Introduction
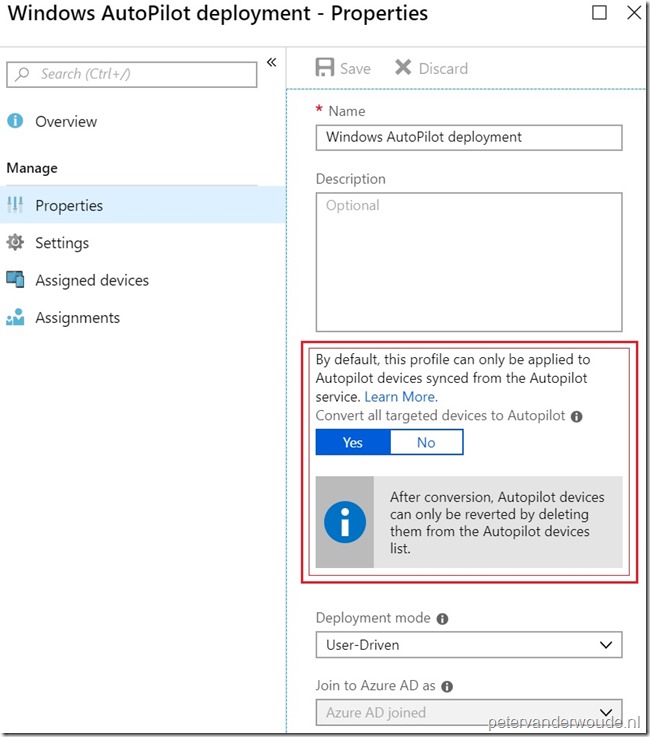
Let’s start with a short introduction about the mentioned configuration option. That configuration option is the Convert all targeted devices to AutoPilot setting. By default an AutoPilot deployment profile is only applied to already existing AutoPilot devices and doesn’t apply to non-AutoPilot devices. Configuring the Convert all targeted devices to AutoPilot setting to Yes will automagically convert all devices in the assigned group to AutoPilot. This is a one-time conversion that also works for co-managed devices. That also means that removing the AutoPilot profile will not remove the converted devices from AutoPilot. After conversion the devices can only be removed by using the Windows AutoPilot devices view. Keep in mind that it can take up to 48 hours for the conversion to be completed.
Configuration
Now let’s continue by having a look at the actual configuration. And in this case only the specific Convert all targeted devices to AutoPilot setting. The following four steps walk through the steps to get to the specific setting and are not meant to create a complete the Windows AutoPilot deployment profiles.
| 1 | Open the Azure portal and navigate to Microsoft Intune > Device enrollment > Windows enrollment to open the Device enrollment – Windows enrollment blade; |
| 2 | On the Device enrollment – Windows enrollment blade, select Deployment Profiles in the Windows AutoPilot Deployment Program section to open the Windows AutoPilot deployment profiles blade; |
| 3 | On Windows AutoPilot deployment profiles blade, either select Create profile or select [existing deployment profile] > Properties to open the Create profile blade or the [existing deployment profile] – Properties blade; |
| 4 | On the Create profile blade or the [existing deployment profile] – Properties blade, the setting Convert all targeted devices to AutoPilot must be switched to Yes (below is an example of the the [existing deployment profile] – Properties blade, the Create profile blade looks similar) ; |
| — |  |
Note: There’s not a real easy method to see which devices are converted to AutoPilot. Those devices will show as any other imported device, without enrollment state. However, as the configuration is done via an AutoPilot deployment profile, the device is immediately assigned to a profile. Again, without creating any fancy configurations, like query based dynamic device groups.
More information
For more information about enrolling Windows devices by using Windows AutoPilot, please refer to the documentation named Enroll Windows devices by using the Windows Autopilot.
Hi Peter,
Technically this means that Intune has the Device Serial Number, Windows Product ID and Hardware Hash if a device is enrolled normally by a user ? So it will do a harvest for Autopilot of the devices targeted by the convert option ?
Let’s say if we bulk enroll 200 devices with a DEM account and we assign the Autopilot profile with convert targeted devices, will it do an Autopilot Reset, Fresh Start or an Wipe and will the DEM account association be removed ?
Hi Rkast,
This configuration doesn’t do anything to existing devices directly. It only makes sure that the devices are added to AutoPilot and on the next reset of the device the AutoPilot deployment profile will be applied.
Regards, Peter
Very cool. Keep up the awesome content 🙂
Thank you, Ewan!
Hi Peter,
Ok good to know. Thank you very much for your answer!
What kind of reset does the device need if we initiate one from intune (Fresh Start, full wipe) or does it need factory reset ?
Hi RKast,
The device needs to go to a state in which it can do an AutoPilot deployment. From a remote action perspective, the Wipe would do that trick.
Regards, Peter
Thank you Peter!
Is it possible to Automatically convert legacy Intune managed devices(Intune Client Installed Device) to AutoPilot.
Hi Rahul,
To my knowledge the device must be Intune MDM managed.
Regards, Peter
Hi Peter,
In the opening statement you write “In that tweet I mentioned a new easy method to automagically convert Intune managed devices to AutoPilot.
Must the device be Intune manage? I’ve looked on docs, and can’t find any information that points to that the device needs to be Intune managed, neither doesn’t say what kind ‘koin type’ that is needed.
I’ve asked MS about this, but still haven’t gotten any answers.
Do you know if this should work with hybrid joined,azure ad joined and/or azure d registered devices?
Regards,
Hi Niklas,
To my knowledge those devices must be Intune managed to harvest that information.
Regards, Peter
Hi,
I’m working on W10 Intune MDM last month for my Company and followed lot of your post …among other interesting blog 😉
First challenge was to achieve AADj with MFA with Intune Enrolement (conformity/config/…). It’s now called mode 4 OOBE –> https://msdnshared.blob.core.windows.net/media/2018/08/EnrolmentScenario5.png
Second challenge was to remove user local admin rights manually (with power shell send by Intune). I did it but find Autopilot mode to have this automatically !
But that means to have autopilot informations from hardware provider (CSV or AAD Tenant connection)…or to retrieve it manually on each computer…very painful for foreign BU without local IT :-/
In the next week , I’m challenged to deploy the concept on Australian BU… and I still do not know if I will have autopilot informations (with new computer order or if have to re-use existing computer).
So I think to find a trick which is a mix of my old OOBE mode (with admin removed) and this new magially option.
I create a dynamic groupe that include all Intune Managed (identify by name prefix part of the generated hostname durecing enrolement&configuration process) but without [ZTDId].
(device.displayName -startsWith “commonprefix”) -and -not (device.devicePhysicalIDs -any _ -contains “[ZTDId]”)
After that I can apply a new autopilot profile with conversion option to this group
If My distant user do a OOBE AADj/Intune (without autopilot), after 48h, device will be Converted and should have ZTDId flag. that will automatically transfer device to my standard Production Autopilot group and profile 😉
And after next reset this should work as an Autopilot-native W10.
Time for tests now…
Hi Julien,
If the devices are already Azure AD joined and Intune managed and running Windows 10, you should be fine.
Regards, Peter
Hi Peter,
I have follow microsoft documentation regarding autopilot – carrying out a standard AAD Join – the devices get the profile the user can log in, bitlocker and windows hello profile gets deployed to the device but:-
1. I don’t see the device under the devices under All Devices in InTune? But if I find the user that logged on to the device, I can see the device listed under the user device with bitlocker info. So I can’t do a wipe/reset?
2. None of the apps that I deployed to the device works? even office?
Any ideas? please?
Hi Tee,
That sounds like the device is not MDM enrolled, which is often caused by configuring auto MDM enrollment.
Regards, Peter
Hello Peter,
We experience that existing Intune devices, with the function “convert all targeted devices to autopilot”, are not visible in AutoPilot.
The devices are registered manually in Intune, with the addition of a Work / School account and are also visible on Intune devices.
Do you have any advice?
Regards, Wouter
Hi Wouter,
Is that only for those type of devices?
Regards, Peter
Hi Peter,
I am Running Windows Autopliot and it get completed in 30 min or little longer. After when device get ready, I manually Restart the Device and try to Login with the same User Id through which I ran Windows Autopilot, but strangely I cant login on the Device and its giving your Username or Password is wrong… 3 or 4 times I have Build the Device and every time same result I am getting. I am Running Windows Autopilot for AAD join.
Please help me in this…
Hi Yasphal,
I’ve seen situations like that many times, when ADFS is used. Often it’s related to a misconfiguration in ADFS.
Regards, Peter
I have an enrollment profile that used to do its job perfectly (converting enrolled devices to autopilot), I will give you an example of what is happening now:
Computer-1 enrolled to Intune
Computer-1 assigned to a dynamic group Group-1
Enrollment profile assigned to Group-1 ( set to convert target devices to autopilot)
Now when I open the list of autopilot devices, I find the serial number of Computer-1
I click this serial to see to which device it is assigned to and I find that it is assigned to a different device that Computer-1
and that device has the name as the serial number of Computer-1, if I check this device in Azure active directory I find this device as diabled!!!
Does anuone has a similar experience?
Thanks
Hi Philip,
Are you saying that you have multiple device objects with the same serial?
Regards, Peter
Hello Peter,
Thank you for your reply,
It seems that when converting an enrolled device to AutoPilot device, another device is created in Azure Active Directory and assigned to the AutoPilot device instead of the correct device,
This newly created device has a name as the serial number of the enrolled device and it is disabled.
below link is a discussion I startted earlier, go to the last comment by me, it may give a better idea:
https://docs.microsoft.com/en-us/answers/questions/487592/dynamic-group-showing-serial-number-instead-of-dev.html#answer-494972
Regards
Hi Philip,
I can’t really reproduce the behavior, as I don’t have GPO enrolled devices in my lab environment. I can only say that I’m not seeing that behavior with my Intune managed devices that are enrolled via different methods. Are you also saying that you don’t get both devices objects in the dynamic groups?
Regards, Peter
Hello Peter,
Many thanks for your reply, I think the problem is from Microsoft end, I have opened a ticket directly with them and they are working on it now, Will keep you posted of the updates.
I will try a manual enrollment process on one computer and see if the same problem will happen.
My problem is that if I enrolled “Computer-01” to Intune, the enrollment process is done successfuly but the conversion to Autopilot process is not assigning Computer-01 to the created Autopilot device , it is creating a new device and assigning it to this autopilot device. so when I assign a group tag to the autopilot device the newly created device is now a member of the dynamic group and Computer-01 is not.
Hi Philip,
Apologies for the late reply, as I was enjoying my vacation. I’m curious, did you still got an answer on your ticket with Microsoft?
Regards, Peter
Hi Peter,
I am working with one of my clients to get their existing Windows 10 estate co-managed and converted to Autopilot devices. I have managed to get the test workstations enrolled and co-managed into Intune (great!). I am also now targeting the Autopilot Deployment Profile with the convert to Autopilot devices setting enabled. However it currently isn’t working. My only thought is that we currently still have all the co-management workloads in ConfigMgr. Do you know which specific workload we would require to switch over to allow Intune to deploy the deployment profile please?
Thanks
Shimal
Hi Shimal,
Apologies for the late reply, as I was enjoying my vacation. I’m not sure actually. Are you seeing that behavior with all devices? If so, also devices that are not co-managed?
Regards, Peter
Hi Peter,
Great blog, thanks for all your hard work!
I too am getting the same issues as a few people above, co-management is enabled for all my workstations, they are all hybrid or Azure AD joined and I’ve migrated a couple workloads over with no issues. However, when I attempt to use the convert all target devices to autopilot setting on a dynamic device group that contains my W10 workstations, it simply does not seem to work properly. out of the 8000+ machines, only 900 or so have an autopilot profile applied, the rest are unassigned although they do show up under autopilot devices. I left the configuration in place for a couple months thinking it could just take some time to complete but after almost 2 months, it seems to have stopped at 900.
Any ideas on what could be causing this?
Hi Matt,
In that case you might want to contact support to see what’s happening in the back.
Regards, Peter
Peter,
Actually I found a clever way to upload the hash.csv file to a storage blob using AzCopy and a SAS Token, need to clean it up a bit but is working, any suggestions are welcome, I will be deploying this via Win32 app deployment with Endpoint Manager:
Set-ExecutionPolicy Bypass -Force
$ThisComputer = $env:ComputerName
New-Item -Path “C:\” -Name $ThisComputer -ItemType Directory
Set-Location C:\$ThisComputer
Install-Script -Name Get-WindowsAutoPilotInfo -RequiredVersion 3.5 -Force
Get-WindowsAutoPilotInfo.ps1 -OutputFile C:\$ThisComputer\$ThisComputer.csv
$AzCopyLocation = “C:\AzCopy”
Set-Location $AzCopyLocation
.\azcopy copy “C:\$ThisComputer\$ThisComputer.csv” “https://YourOwnTenantStorageAccount.blob.core.windows.net/hashes/?sv=2020-08-04&ss=bfqt&srt=sco&sp=rwdlacupitfx&se=2022-03-10T04:46:52Z&st=2022-03-09T20:46:52Z&spr=https&sig=QPQ%2BeDVse53v98CvlvG6x0Mg%2Fpe9%2BomyVYeU%2XXXXXXXXXX” –recursive=true
You need to go here, and download the proper version of AzCopy for your OS:
https://docs.microsoft.com/en-us/azure/storage/common/storage-use-azcopy-v10
In my case (still cleaning it) I created the “C:\AzCopy” folder and dropped the AzCopy executable I downloaded and run AzCopy.exe from there, keep in mind that you MUST use the “.\” element otherwise it wont work
Happy testing!
Thank you for sharing Ed!
Regards, Peter
PS: Keep in mind that nowadays, you can automatically convert devices that are already available within Intune.
Oh I am aware of that, my issue has been dealing with migrating from one tenant to another due to an acquisition, removing them from the old tenant and making them autopilot in the new one… we still need the hash for this regardless. I devised a different way by deploying pre-sets of PowerShell scripts after I wrote this not.
Thanks
Ed
Ah, great! Thanks for sharing Ed!
Regards, Peter
Hi Peter,
Does this work with azure ad registered devices and managed by mdm? I connected a device to azure and the device appears in azure portal as azure registered and managed by intune (my mdm user scope is set to all). i moved the device to a security group which is included in the autopilot profile (converted option is set to yes). I have waiting more than 24hrs now and none of the devices has got the autopilot profile assigned yet.
so does this work with azure registered with intune mdm or the device has to be azure joined?
Hi kev,
I can’t be an hybrid Azure AD joined device. See also: https://docs.microsoft.com/en-us/mem/autopilot/automatic-registration
Regards, Peter
Hi Peter, excellent blog !
After converting all devices, can we simply click Autopilot reset and it should work after 48hrs ? Or do we have to wipe ?
Thanks.
Hi Scott,
I have to say that I never tried that. But according to the docs it should be possible as long as the device is MDM managed and joined to Azure AD: https://learn.microsoft.com/en-us/mem/autopilot/windows-autopilot-reset#reset-devices-with-remote-windows-autopilot-reset
Regards, Peter