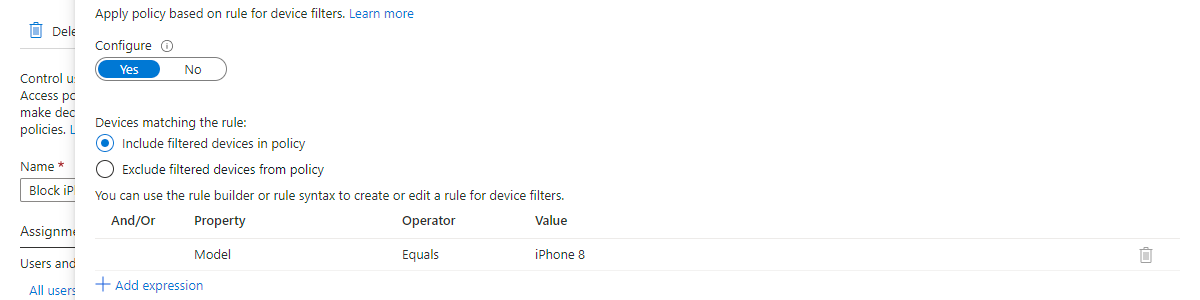
Using filters for devices as condition in Conditional Access policies
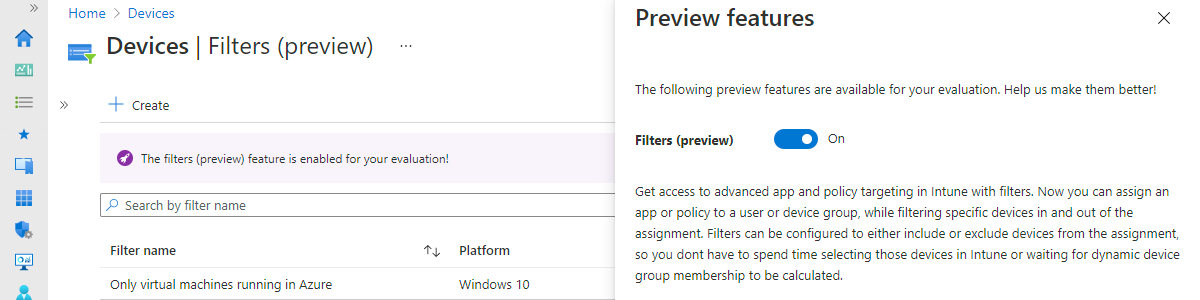
This week is also all about filters. Last week was about filters for assigning apps, policies and profiles to specific devices in Microsoft Intune and this week is about filters for devices as a condition in Conditional Access policies. Filters for devices are a nice addition to Conditional Access policies to only target specific devices. A great option for addressing specific scenarios. This post starts with a short introduction about filters for devices, followed with the steps for configuring a filter within a Conditional Access policy. This post ends with the administrator experience. Important: At the moment of writing, filters for devices are still public preview. For Azure AD features that means that the feature is provided without a service level agreement, and that the …