This week is all about registering and joining devices to Azure Active Directory (Azure AD). More specifically, about requiring multi-factor authentication (MFA) when registering or joining devices to Azure AD. Starting with March 2021, Azure AD contains a new feature in Conditional Access (CA) that provides more flexibility for requiring MFA when registering or joining devices to Azure AD. That new feature is the Register or join devices user action. This post will start with a short introduction about that new user action, followed with the steps to configure that user action. This post will end with a look at sign-in logs.
Important: The Register or join devices user action is also the new recommended method for enforcing MFA when registering or joining a device Azure AD.
Introduction to the user action for registering or joining devices
It’s important to start with mentioning that it’s not new that it’s now possible to require MFA when registering or joining devices to Azure AD. That was already possible. Azure AD already contains a setting that can be used to required MFA when registering or joining devices to Azure AD. That setting, however, is a tenant-wide setting and allows no flexibility. It’s either on, or off, for all devices. That could cause some challenges with specific scenarios, which – in the worst case – would require that setting to be turned off for all devices. That changes now.
The Register or join devices user action can be used to address those challenges. By bringing that user action to CA, the flexibility of a CA policy can be used to create a fine-grained policy that fits the needs and requirements of any organization when requiring MFA for registering or joining devices to Azure AD. That flexibility can be used to exclude specific users from the assignment (not advised) and can also be used to add additional conditions to the assignment. Basically every condition that is not dependent on a device registration, can be used as a condition in the assignment. That includes the user risk level, the sign-in risk of the user, the device platform of the device that the user is signing in from and the location that the user is signing in from. Besides the flexibility in the assignment, there is no flexibility in the access control. That makes perfect sense, as using other access controls would create a continuous loop in the device registration.
When using this new user action, it’s important to keep in mind that it will be triggered when the user hits the Device Registration Service resource in Azure AD. That’s not always the first sign-in during the device enrollment process. The used application differs per platform.
Configuration of requiring MFA when registering or joining devices
The configuration of CA policy, to require MFA when registering or joining devices to Azure AD, is pretty straight forward. However, it’s important to first make sure that the tenant-wide device setting in Azure AD is not enabled. That’s required to correct enforce the CA policy. The following two steps walk through verifying that device setting.
- Open the Azure portal and navigate to Azure Active Directory > Devices > Device settings
- On the Devices | Device settings page, as shown in Figure 1, make sure that Devices to be Azure AD joined or Azure AD registered require Multi-Factor Authentication is set to No
Note: The message below the slider will change when the MFA configuration with Conditional Access is in place.
Once the configuration of the device setting in Azure AD is verified, it’s time to have a look at the configuration of the actual CA policy. The following four steps walk through the process of creating and assigning that CA policy. The focus of those steps is on the important required configuration of the user action and the grant control.
- Open the Microsoft Endpoint Manager admin center portal navigate to Endpoint security > Conditional Access – or open the Azure portal and navigate to Azure Active Directory > Security > Conditional Access – to go to the Conditional Access policies section in Azure Active Directory
- On the Conditional Access | Policies blade, click New policy to start the creation of a new Conditional Access policy
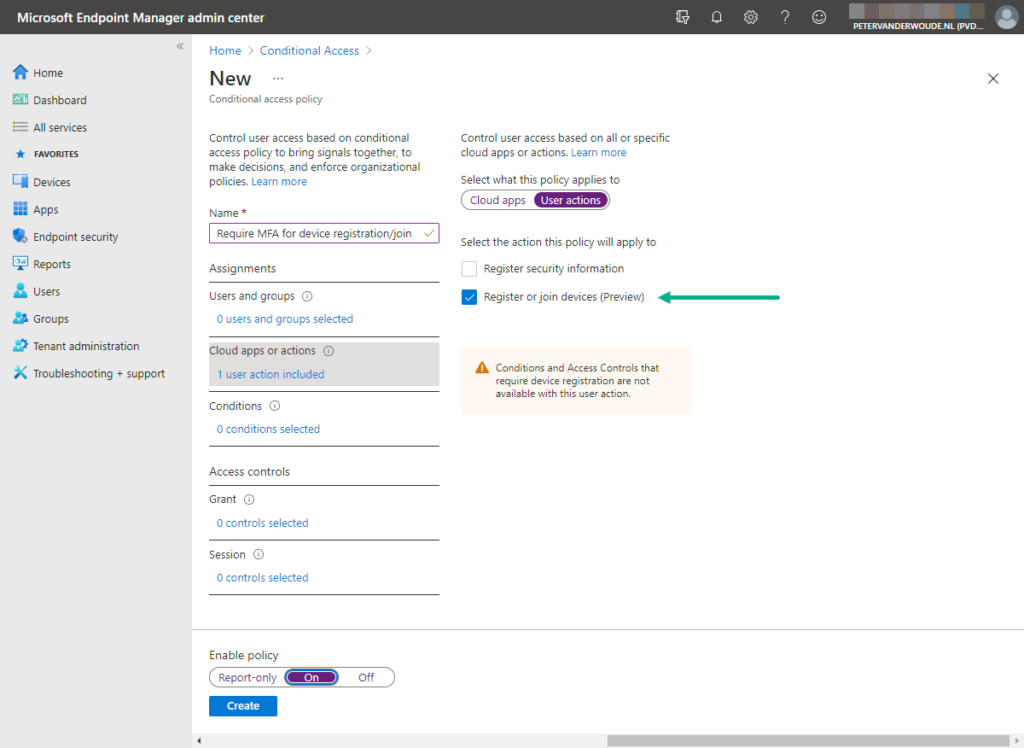
- On the Assignments section, as shown below in Figure 2, configure the following for the different assignments
- Users and groups: Select the users that should be assigned with this policy
- Cloud apps or actions: Select User actions > Register or join devices to configure the action that this policy applies to
- Conditions: If needed, configure User risk, Sign-in risk, Device platforms or Locations as additional conditions to more specifically assign this policy to a specific scenario
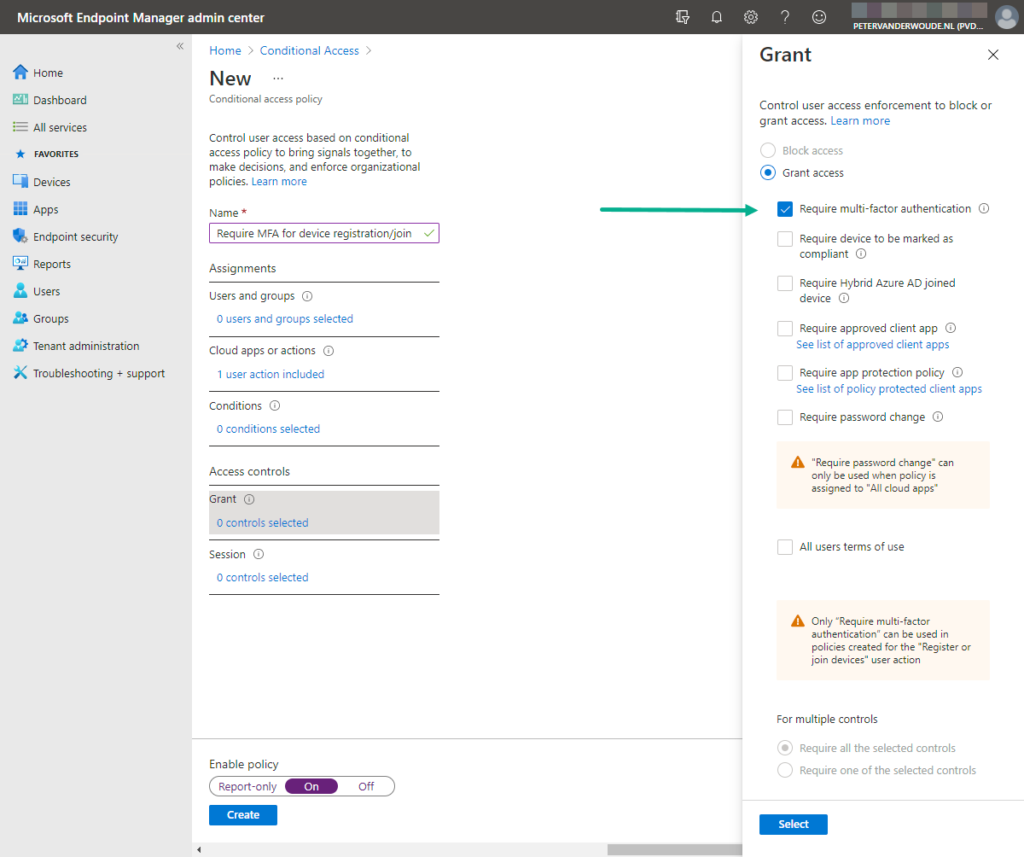
- On the Access controls section, as shown in below Figure 3, configure the following for the grant control
- Grant: Select Grant > Require multi-factor authentication to require MFA for the user action
- Session: Not applicable to the user action
Note: This is also the only available configuration with the specified user action. Every other configuration option is greyed out (as shown above in Figure 3).
Sign-in information with requiring MFA when registering or joining devices
For this subject, the user experience is probably not the most interesting. The user experience is just a MFA prompt. Nothing special. The only thing about the user experience, that might be worth looking at, is the moment that the device will prompt for MFA. That moment differs per platform and per enrollment type. Especially on devices that are running Android and iOS, the behavior is interesting to look at. Mainly because MFA is then often triggered after the second username-password prompt. Especially with company-owned device scenarios (enrollment during the out-of-the-box experience). That being said, the behavior is completely logic, as it requires MFA when hitting the device registration service.
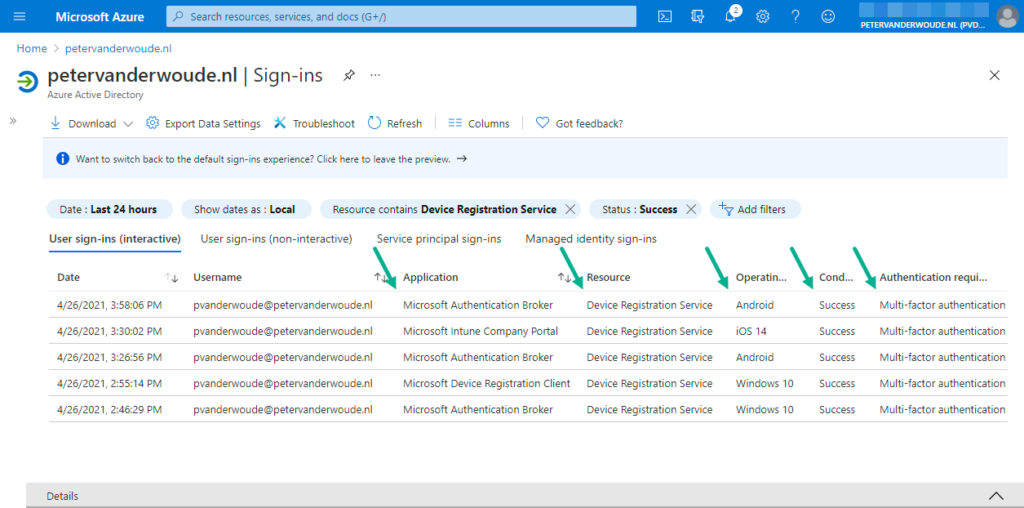
The most interesting location to look at is in Azure portal at Azure Active Directory > Monitoring > Sign-ins. That contains an overview of the different applications that are used when accessing the device registration service, with the CA status and the authentication requirement. Below in figure 4 is the information shown for the following different enrollment types:
- Android Enterprise corporate-owned fully managed device
- Android Enterprise corporate-owned device with work profile
- Apple Automated Device Enrollment with user affinity
- Windows Autopilot user-driven deployment
Note: With the shown Android and iOS enrollments, the MFA prompt was with the second username-password prompt. With the shown Windows Autopilot enrollment, the MFA prompt was with the initial username-password prompt.
More information
For more information about user actions in Conditional Access, refer to the documentation about Cloud apps or actions in Conditional Access policy – Azure Active Directory | Microsoft Docs


Hi Peter – Thanks for the detailed information. So can we use these CA policy during our Autopilot Hybrid Azure AD join process in the initial OOBE process?
Hi Vinod,
I haven’t tried that myself, but according to the docs it’s only for register or join of devices (https://docs.microsoft.com/en-us/azure/active-directory/conditional-access/concept-conditional-access-cloud-apps#user-actions).
Regards, Peter