 This blog post will be about the other magical store world of Windows Phone 8.1 and that’s the world of the Windows Phone Store. By now, I think many are already aware of the different possibilities for the Windows Phone Store, but I thought it would be time for a complete overview like I did for Windows Phone 8.1 and the Microsoft Intune Company Portal app.
This blog post will be about the other magical store world of Windows Phone 8.1 and that’s the world of the Windows Phone Store. By now, I think many are already aware of the different possibilities for the Windows Phone Store, but I thought it would be time for a complete overview like I did for Windows Phone 8.1 and the Microsoft Intune Company Portal app.
This post will contain the different scenarios for providing (limited) access to the Windows Phone Store. These scenarios will be explained for Microsoft Intune standalone and Microsoft Intune hybrid.
Scenarios
Now lets start with summarizing the different scenarios that are possible for providing (limiting) access to the Windows Phone Store. I found the following three scenarios and I’ll go through them in detail after listing them:
- Scenario 1: Completely block the Windows Phone Store;
- This scenario will be about completely blocking the access to the Windows Phone Store;
- Scenario 2: Block the Windows Phone Store except…;
- This scenario will be about blocking the access to all the apps from the Windows Phone Store except for specifically configured exceptions;
- Scenario 3: Allow the Windows Phone Store except…;
- This scenario will be about allowing the access to all the apps from the Windows Phone Store except for specifically configured exceptions.
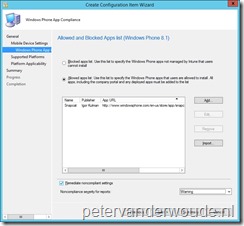
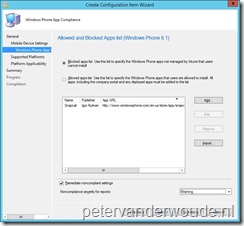
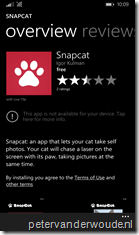
For the second and third scenarios I’ve used the wonderful app Snapcat, which is basically a selfie app for cats, as an example. The App URL for this app is the following: http://www.windowsphone.com/en-us/store/app/snapcat/7a1a6000-4956-4030-8862-831d3633d8b9.
Scenario 1: Completely block the Windows Phone Store
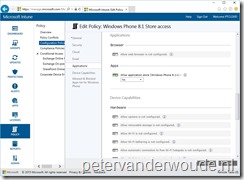
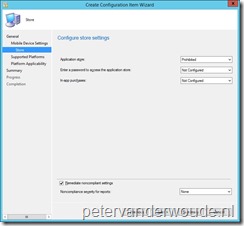
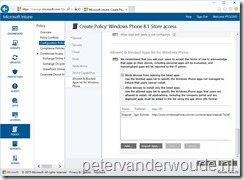
The first scenario is also the most restricting scenario. This scenario will completely block the access to the Windows Phone Store. On a high-level, this can be configured by performing the configurations mentioned below. These configurations are based on the current versions of ConfigMgr and Microsoft Intune.
Note: In both cases this is also still possible via a custom OMA-URI. The value should be set to 0 and the location would be the following ./Vendor/MSFT/PolicyManager/My/ApplicationManagement/AllowStore.
Scenario 2: Block the Windows Phone Store except…
The second scenario provides a bit more room for movement within the Windows Phone Store. In this scenario the Windows Phone Store will be accessible, but only for specifically specified applications. Every application that’s not specified will be disabled when it was already installed, or will not be available when the installation is tried via the Windows Phone Store. On a high-level, this can be configured by performing the configurations mentioned below. These configurations are based on the current versions of ConfigMgr and Microsoft Intune.
Note: In both cases this is also still possible via a custom OMA-URI. Via OMA-URI there is also a bit more flexibility, as it also provides the ability to allow a specific publisher. The location of the OMA-URI would be the following ./Vendor/MSFT/PolicyManager/My/ApplicationManagement/ApplicationRestrictions.
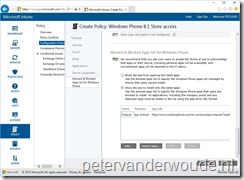
Scenario 3: Allow the Windows Phone store except…
The third scenario provides the most room for movement within the Windows Phone Store. In this scenario the Windows Phone Store will be accessible, except for specifically specified applications. Every application that’s specified will be disabled when it was already installed, or will not be available when the installation is tried via the Windows Phone Store. This could even be used to block certain line-of-business applications. On a high-level, this can be configured by performing the configurations mentioned below. These configurations are based on the current versions of ConfigMgr and Microsoft Intune.
Note: In both cases this is also still possible via a custom OMA-URI. Via OMA-URI there is also a bit more flexibility, as it also provides the ability to block a specific publisher. The location of the OMA-URI would be the following ./Vendor/MSFT/PolicyManager/My/ApplicationManagement/ApplicationRestrictions.
Results
Now that I’ve gone through the different scenarios it’s time to look at the results of those configurations. Below are screenshots available per scenario. For the first and second scenario I choose to go for a screenshot of the App list, as it provides the best visible result. For a similar reason I choose to go for a screenshot of the specific app, in the Windows Phone Store, for the third scenario.
More information
For more information about Microsoft Intune standalone, or Microsoft Intune hybrid, in combination with the Windows Phone Store, please refer to the following links:
- Use Windows Phone configuration policies to manage device settings in Microsoft Intune: https://technet.microsoft.com/en-us/library/mt147408.aspx
- App Compliance for Mobile Devices in Configuration Manager: https://technet.microsoft.com/en-us/library/mt131416.aspx
- Restrict Windows Phone 8.1 apps via XML and custom OMA-URI: https://technet.microsoft.com/en-us/windows/dn771706.aspx


Hi
Out of interest have you tried this on a Windows 10 Mobile as I am configuring a setup using scenario 2 with Intune standalone, however on a Windows 10 mobile it blocks pretty much everything including the settings, Outlook, and calendar app. The store App is also blocked even though in my policy I have set it up to be allowed and it is not greyed out like the others.
Is this expected
For Windows 10 Mobile I would look at assigned access. This should get you started: https://msdn.microsoft.com/library/windows/hardware/mt157024(v=vs.85).aspx
Peter
Thanks for your comment and much appreciated, however if I am managing a high number of Windows 10 mobile devices this solution is difficult to implement as you have to manually install the provisioning package as Intune doesn’t support deployment of this. So to me the easier way would be to publish the list of apps URL’s in the store so you can add them to the allowed list.
Hi Adam,
No, you don’t have to create provisioning packages. You can create and XML and use that as the value for the required OMA-URI.
Regards,
Peter