A couple of weeks ago I did a blog post about the different management options for Windows 8.1. In that specific post I already mentioned OMA-DM as a very valid method to manage Windows 8.1 and Windows 10 devices. To refresh the memories, OMA Device Management (OMA-DM) is an open management standard designed for mobile devices. The nice thing is that OMA-DM is also fully utilized in Windows 10, even the desktop version. That means that OMA-DM can be used to fully manage specific parts of a Windows 10 device.
In this post I’ll show how OMA-DM can be used to fully manage Windows Defender in Windows 10. For Windows 10 it’s possible to manage all the settings available for Windows Defender. This includes everything, from managing exclusions until blocking the access to the user interface. Managing Windows Defender can be very useful for Windows 10 devices connecting to the work resources. Also, this level of management can be useful for both personal and company owned devices.
Disclaimer: This blog post is based on a technical preview build of Windows 10 (build 10122). The configurations described in this post might change in future releases. I’ll update this post, if needed, with the next release.
Configuration
Now let’s have a look at the configuration. Actually it doesn’t differ a lot from the configurations required for managing settings on Windows Phone 8.1, but I’ll go through the required configurations anyway. I’ll go through the required configurations for both, Microsoft Intune standalone and Microsoft Intune hybrid.
Microsoft Intune standalone
The first configuration steps are for Microsoft Intune standalone. I’ll go through the high-level steps for creating the required policies and the required deployment. It shows the creation of a single OMA-URI setting, which can be used to (not) allow real-time monitoring. The creation of the other OMA-URI settings is similar and can be created by repeating step 2. A complete list of available settings can be found later in this post.
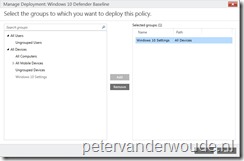
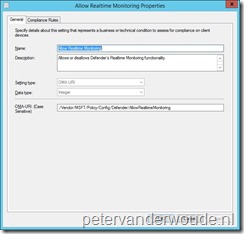
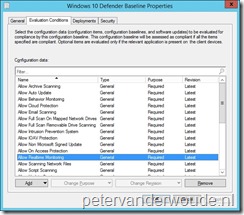
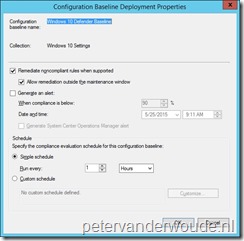
Microsoft Intune hybrid
The last configuration steps are for Microsoft Intune hybrid. I’ll go through the high-level steps for creating the required configuration items, the required configuration baseline and the required deployment. It shows the creation of a single configuration item, that’s used for a single OMA-URI setting, which can be used to (not) allow real-time monitoring. The creation of the other configuration items is similar and can be created be repeating step 1 and 2. A complete list of available settings can be found later in this post.
Result
There is nothing better than looking at the results, especially with something relatively new. Below are two screenshots of the settings of Windows Defender. The first screenshot is before applying the OMA-URI settings and the second screenshot is after applying the configured OMA-URI settings. It shows that every configured setting can also not be changed anymore (besides the configuration of the exceptions). The best thing is that once the Windows 10 device is un-enrolled, the before-state will be applicable again.
| Before | After |
 |
 |
Windows Defender Settings
There are more than 30(!) settings available that can be configured via OMA-URI and are specifically targeted on Windows Defender. All of these settings are configurable via the path of ./Vendor/MSFT/Policy/Config/Defender/<PolicyName>. The following table shows the available policies including the supported and valid values. Many of these values are also available in the documentation, but I’ve noticed that many of the Allowed/ Not allowed values are switched.
| PolicyName | Values |
| AllowCloudProtection To best protect your PC, Windows Defender will send information to Microsoft about any problems it finds. |
Supported values (Integer):
|
| AVGCPULoadFactor Represents the average CPU load factor for the scan (in percent). |
Valid values (Integer): 0–100. |
| DaysToRetainCleanedMalware Time period (in days) that quarantine items will be stored on the system. |
Valid values (Integer): 0–90. |
| AllowArchiveScanning Allows or disallows scanning of archives. |
Supported values (Integer):
|
| AllowBehaviorMonitoring Allows or disallows Defender’s Behavior Monitoring functionality. |
Supported values (Integer):
|
| AllowEmailScanning Allows or disallows scanning of email. |
Supported values (Integer):
|
| AllowFullScanOnMappedNetworkDrives Allows or disallows a full scan of mapped network drives. |
Supported values (Integer):
|
| AllowFullScanRemovableDriveScanning Allows or disallows a full scan of removable drives. |
Supported values (Integer):
|
| AllowIntrusionPreventionSystem Allows or disallows Defender’s Intrusion Prevention functionality. |
Supported values (Integer):
|
| AllowIOAVProtection Allows or disallows Defender’s IOAVP Protection functionality. |
Supported values (Integer):
|
| AllowOnAccessProtection Allows or disallows Defender’s On Access Protection functionality. |
Supported values (Integer):
|
| AllowRealtimeMonitoring Allows or disallows Defender’s Realtime Monitoring functionality. |
Supported values (Integer):
|
| AllowScanningNetworkFiles Allows or disallows a scanning of network files. |
Supported values (Integer):
|
| AllowScriptScanning Allows or disallows Defender’s Script Scanning functionality. |
Supported values (Integer):
|
| AllowUserUIAccess Allows or disallows user access to the Defender UI. If disallowed, all Defender notifications will also be suppressed. |
Supported values (Integer):
|
| ExcludedExtensions Allows an administrator to specify a list of file type extensions to ignore during a scan. |
Each file type in the list must be separated by | (String). For example, zip|exe. |
| ExcludedPaths Allows an administrator to specify a list of directory paths to ignore during a scan. |
Each path in the list must be separated by | (String). For example, C:\Data|C:\Temp. |
| ExcludedProcesses Allows an administrator to specify a list of files opened by processes to ignore during a scan. |
Each file type must be separated by a | (String). For example, C:\Program Files\7-Zip\7zG.exe|C:\Program Files (x86)\Foxit Software\Foxit Reader\FoxitReader.exe. |
| RealTimeScanDirection Controls which sets of files should be monitored. |
Supported values (Integer):
|
| ScanParameter Selects whether to perform a quick scan or full scan. |
Supported values (Integer):
|
| ScheduleQuickScanTime Selects the time of day (in minutes) that the Defender quick scan should run. |
Valid values (Integer): 0–1380 |
| ScheduleScanDay Selects the day that the Defender scan should run. |
Supported values (Integer):
|
| ScheduleScanTime Selects the time of day (in minutes) that the Defender scan should run. |
Valid values: 0–1380 (Integer). |
| SignatureUpdateInterval Specifies the interval (in hours) that will be used to check for signatures. |
Valid values: 0–24 (Integer). |
| SubmitSamplesConsent Checks for the user consent level in Defender to send data. If the required consent has already been granted, Defender submits them. |
Supported values (Integer):
|
More information
For more information about all the possible configuration policies in Windows 10, see the Policy Configuration Service Provider documentation: https://msdn.microsoft.com/en-us/library/windows/hardware/dn904962%28v=vs.85%29.aspx



Hi,
thank you for this guide.
Is Microsoft Intune Endpoint Protection going to be replaced by Windows Defender in the Windows 10 Final Edition?
Based on the (ConfigMgr) documentation, I would say yes. See the What’s new in ConfigMgr 2012 SP2 note here: https://technet.microsoft.com/en-us/library/hh508781.aspx