This post is an updated version of a blog post that I did one-and-a-half year ago about managing Windows Defender, of Windows 10, via OMA-DM. As I still get questions about that post and the OMA-URI settings that are used in that post, I thought it would be good to mention that easier methods are available nowadays. Starting with Configuration Manager 1610 and the Microsoft Intune standalone update around March/ April 2016, it’s simply configurable through the console. No need anymore to configure all those OMA-URI settings manually.
Within this post I’ll provide a quick overview of the configuration options, followed by an overview of the end result. That end result will show how the configured settings simply translate to the known OMA-URI settings.
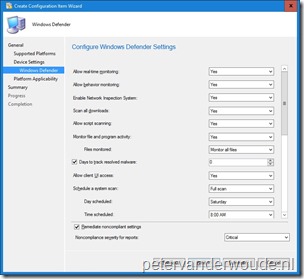
Configuration
Now let’s have a quick look at the required configurations for Microsoft Intune hybrid and Microsoft Intune standalone. I won’t provide a step-by-step guidance, but I will show were to find the settings and what to do with them.
Note: That these configuration options are available nowadays, doesn’t mean that it’s not possible anymore to create custom OMA-URI settings. That is still a valid method to configure these type of settings and changes to these types of settings will always be the first available via custom OMA-URI settings.
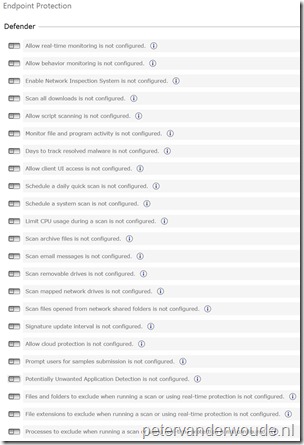
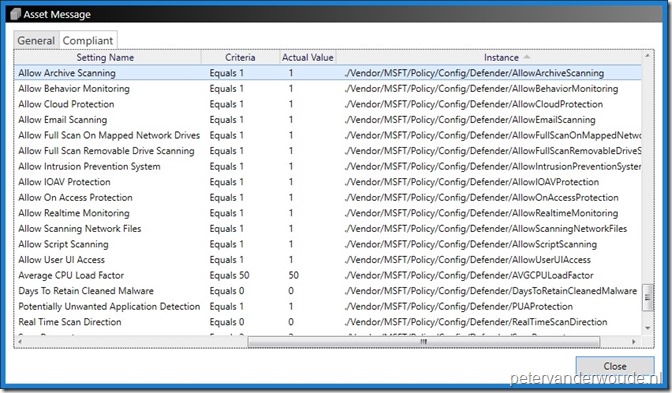
End result
Let’s finish this post by looking at the end result. I could do this by showing the Windows Defender section in the Settings panel on a Windows 10 device, but that will only show grayed out settings and the message Some settings are managed by your organization. I think it’s more interesting to link the created settings to the OMA-URI settings. A great place to look at that is the Deployments node in the Configuration Manager administration console. When I’m looking at the compliance state of the deployment, it will show the Setting Name and the related Instance (in this case the OMA-URI setting), as shown below.
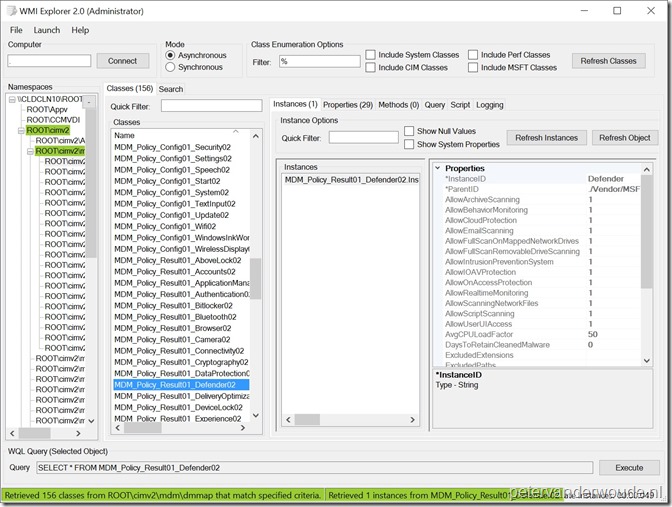
Like last week, I can use a combination of PSEXEC and my favorite WMI Explorer, to locate the created instance with the results of the created policies. As should be familiar by now, the Policy/Result node groups the evaluated policies from all available providers that can be configured. That’s the reason why the example below shows the MDM_Policy_Result01_Defender02 class instead of the MDM_Policy_Config01_Defender02 class. The first class relates to the Policy/Result node and the second class relates to the Policy/Config node.
More information
Fore more information about the managing Windows Defender and the Policy CSP, please refer to:
- Create configuration items for Windows 8.1 and Windows 10 devices managed without the System Center Configuration Manager client: https://docs.microsoft.com/en-us/sccm/compliance/deploy-use/create-configuration-items-for-windows-8.1-and-windows-10-devices-managed-without-the-client
- Intune policy settings for Windows 10 devices in Microsoft Intune: https://docs.microsoft.com/en-us/intune/deploy-use/windows-10-policy-settings-in-microsoft-intune
- Policy CSP: https://msdn.microsoft.com/en-us/windows/hardware/commercialize/customize/mdm/policy-configuration-service-provider
Thanks for pointing out that we can now manage these settings more easily. We’re battling with choosing between the full fat Intune Client to manage updates and endpoint security vs the newer MDM client for a windows 10 deployment.
Is there a way of monitoring/reporting on the status of updates and endpoint security or is it configuration only in the standalone Intune portal at present?
At this moment not via Intune. You could use OMS for that additional piece of information.