This week is all about Windows 10 enrollment methods. The different methods to enroll Windows 10 devices into Microsoft Intune. There are many different methods to enroll Windows 10 devices, which makes it easy to get lost. In this post I’ll provide an overview of these different enrollment methods, including the use case of the enrollment method and how to perform the enrollment. This post is definitely not a complete guide through the different enrollment methods. Its main purpose is to create awareness for the different enrollment methods and to describe the main characteristics of the enrollment methods.
The different enrollment methods
Now let’s discuss the different enrollment methods and their use cases. Before starting, it’s good to mention that I’m aware of the existence of the MDM only enrollment method. However, I don’t consider that as a valid option to enroll a device into Microsoft Intune, as that method doesn’t register the device in Azure AD. And that provides many challenges, for example with conditional access. When discussing the different enrollment methods, I’ll try to group those methods were possible and I’ll try to mention the differences.
Bring Your Own Device (BYOD)
Description: The Bring Your Own Device (BYOD) method enables the user to enroll a personal device into Microsoft Intune by using the Settings panel and adding a Work and School account. That action will trigger the flow to register the device in Azure AD and that will also automatically enroll the device into Microsoft Intune.
Important requirements: This requires that auto-enrollment is configured (as shown in Figure 1). Keep in mind that within the auto-enrollment configuration, the administrator can also configure MAM enrollment. When the MDM and MAM enrollment is configured for a user, the MAM enrollment takes precedence for personal devices.
Example scenario: This can be useful for Bring Your Own Device (BYOD) scenarios. The device will be enrolled as a personal device.
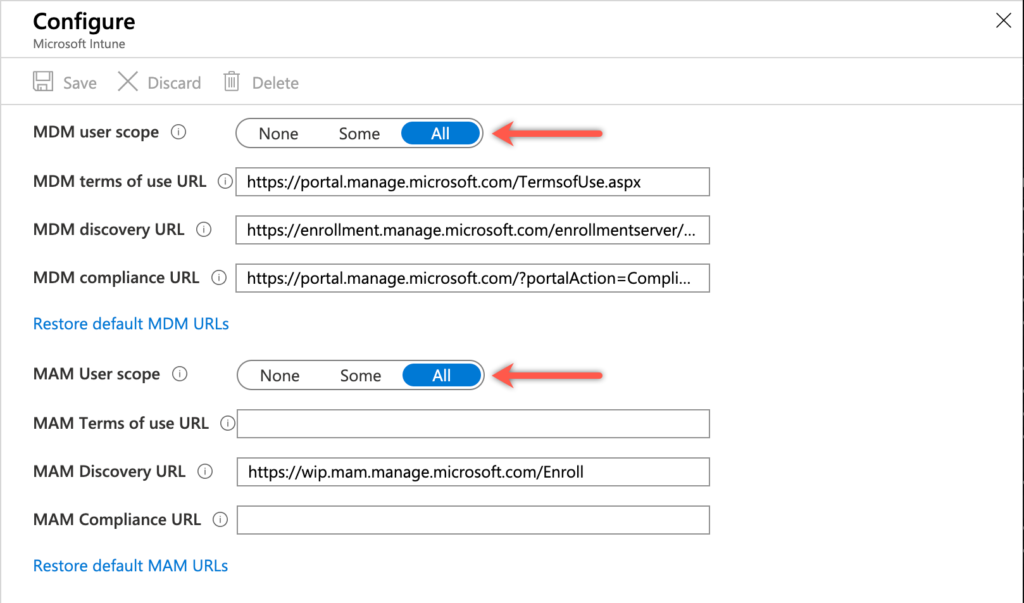
Figure 1: Configure auto-enrollment
Azure AD join (with auto enrollment)
Description: The Azure AD join method enables the user to enroll a corporate-owned device into Microsoft Intune, similar to enrolling a personal device – by using the Settings panel and adding a Work and School account – the user can also choose to join the device to Azure AD. That option will become available during the same configuration flow. The user has to specifically choose to join Azure AD during that flow (as shown in Figure 2). This same behavior can also be triggered during the Out-Of-the-Box-Experience (OOBE). That can be achieved by setting the device up for an organization. That will trigger the flow to Azure AD join the device.
Important requirements: This requires that auto-enrollment is configured (as shown in Figure 1).
Example scenario: This can be useful for Choose Your Own Device (CYOD) scenarios. The device will be enrolled as a corporate-owned device.
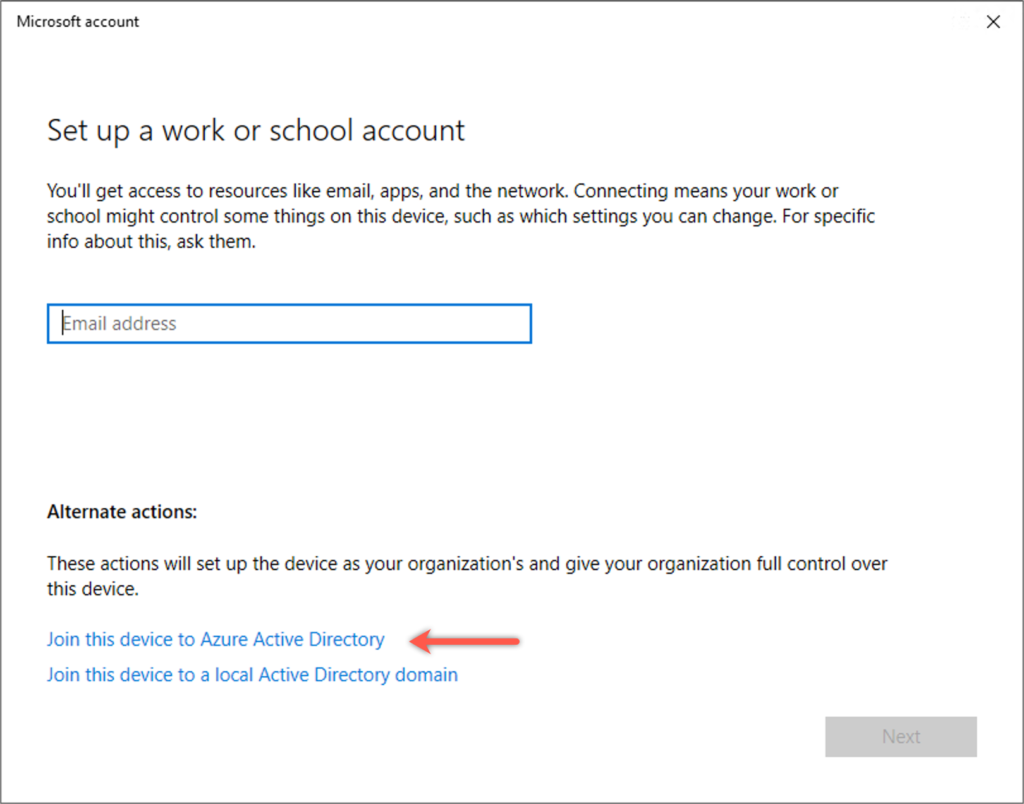
Figure 2: Manual device enrollment
Windows Autopilot
Description: The Windows Autopilot method enables users to easily enroll corporate-owned devices. Windows Autopilot can be used to automate the Azure AD Join and directly enroll corporate-owned devices into Microsoft Intune. This method simplifies the OOBE – as mentioned with the Azure AD join method – as it will automatically add the device to AD or Azure AD and directly enroll the device into Microsoft Intune.
Important requirements: This requires that the device should be added in Microsoft Intune as Windows Autopilot devices (as shown in Figure 5) and specific Windows Autopilot profiles should be created to control the behavior and the OOBE.
Example scenario: This is useful in scenarios when handing out devices to users without the need to build, maintain, and apply custom operating system images to the devices. The device will be enrolled as a corporate-owned device.
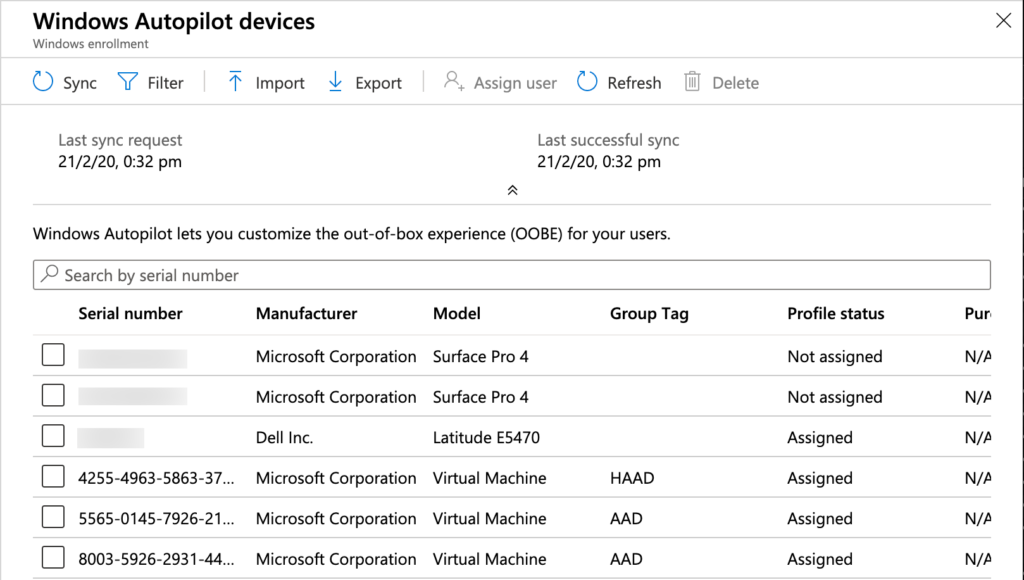
Figure 3: Windows Autopilot enrollment
Device Enrollment Manager (DEM)
Description: The Device Enrollment Manager (DEM) method enables the administrator to enroll multiple corporate-owned devices. The DEM account is a special account with permissions to enroll and manage multiple (up to 1000) corporate-owned devices. That enables a bulk enrollment method for non-personal corporate-owned devices. The enrollment can be achieved by following any of the flows to configure an Azure AD join.
Important requirements: This requires that auto-enrollment is configured (as shown in Figure 1). Besides that the Device Enrollment Manager (DEM) should be configured (as shown in Figure 3) and make sure to keep the maximum number of devices that the user account can add to Azure AD matches.
Example scenario: This can be useful in scenarios where the device is enrolled and prepared before handing it out to the user of the device. The device will be enrolled as a corporate-owned device.
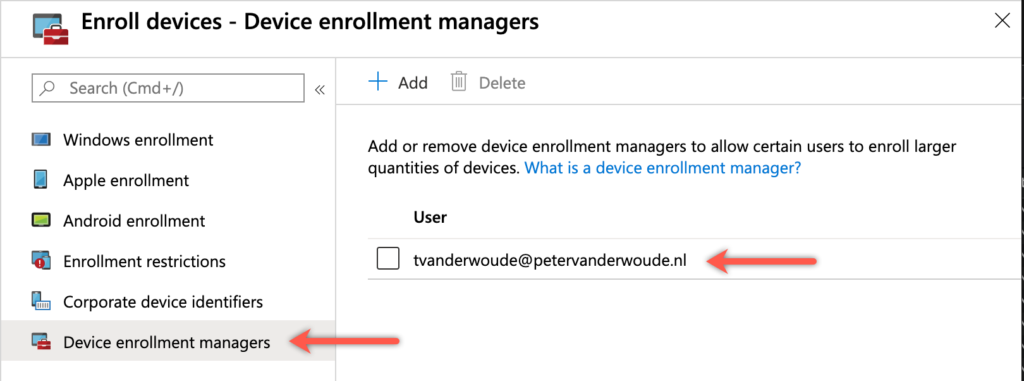
Figure 4: Configure device enrollment managers
Provisioning package
Description: The provisioning package method enables the administrator to bulk enroll corporate-owned devices. A provision package can be used to add devices in bulk to Azure AD and automatically enroll those devices into Microsoft Intune. That provisioning package can be created by using the Windows Configuration Designer (as shown in Figure 4) and can be applied to corporate-owned devices. Once the package is applied, it’s ready for Azure AD users to sign in.
Important requirements: This requires that auto-enrollment is configured (as shown in Figure 1). Besides that make sure to keep the maximum number of devices that a user can add to Azure AD matches with the usage of the package.
Example scenario: This can be useful in scenarios where an authorized user joins large numbers of corporate-owned devices. The device will be enrolled as a corporate-owned device.
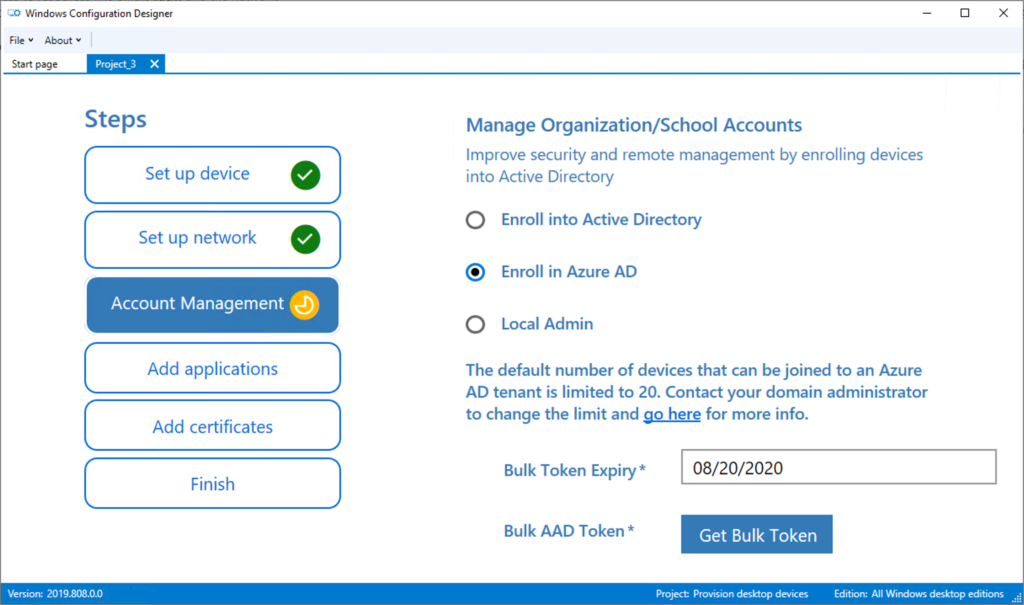
Figure 5: Configuration package
Co-management
Description: The co-management method enables administrators to automatically enroll corporate-owned devices. Co-management enables organizations to automatically enroll devices into Microsoft Intune. This requires the device to be managed with Configuration Manager and the enablement of co-management. Within the co-management configuration, the automatic enrollment in Microsoft Intune can be configured (as shown in Figure 6).
Important requirements: This requires that auto-enrollment is configured (as shown in Figure 1) and that the device is registered or joined to Azure AD (can be achieved via Client Settings).
Example scenario: This is useful in scenarios when the flexibility is still required to use the technology solution that works best for the organization. The device will be enrolled as a corporate-owned device.
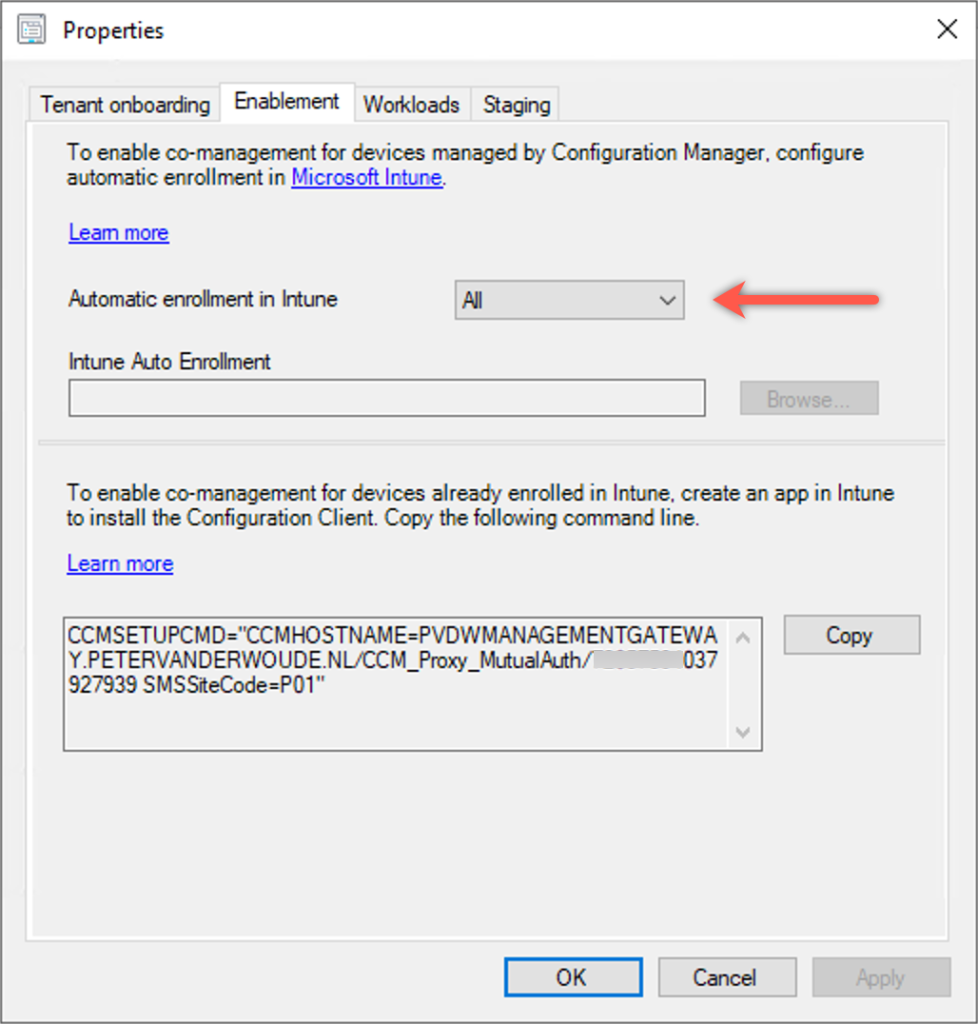
Figure 6: Co-management configuration
Group Policy
Description: The Group Policy method enables administrators to automatically enroll corporate-owned devices. Group Policy enables organizations to automatically enroll devices into Microsoft Intune. The automatic enrollment is triggered by the Group Policy (as shown in Figure 7). That means that the device is always hybrid Azure AD joined.
Important requirements: This requires the device to registered in Azure AD.
Example scenario: This is useful in scenarios when mass-enrolling domain-joined devices.The device will be enrolled as a corporate-owned device.
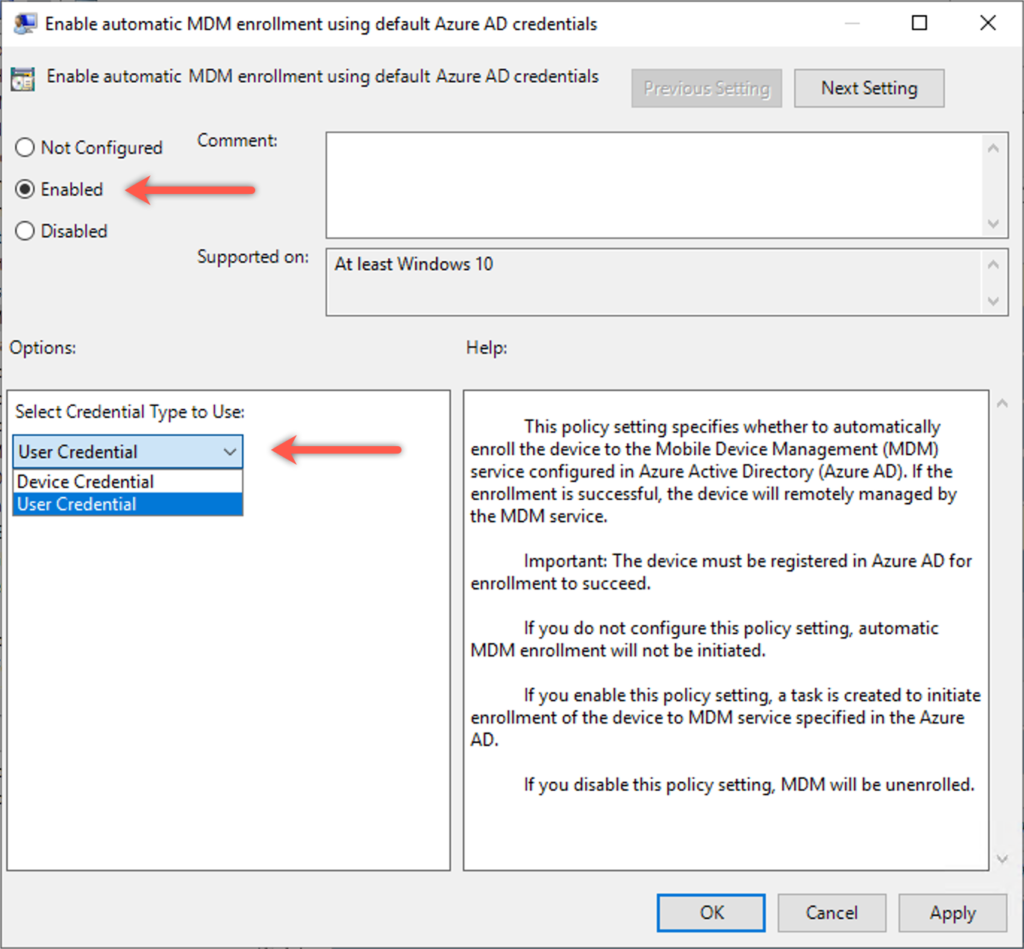
Figure 7: Group Policy configuration
An overview of the enrollment methods
Let’s end this post by providing short overview of the different enrollment methods and their most important characteristics that are mentioned in throughout this post. Those characteristics are the ownership registration of the device, the user affinity with the device and the user interaction with the device during the enrollment.
| Enrollment method | Ownership | User affinity | User interaction |
| Bring Your Own Device | Personal | Yes | Yes |
| Azure AD join | Corporate | Yes | Yes |
| Windows Autopilot | Corporate | Yes | Yes |
| Device Enrollment Manager | Corporate | No | No |
| Provisioning package | Corporate | No | No |
| Co-management | Corporate | Yes | No |
| Group Policy | Corporate | Yes | No |
A couple of remarks with this table are that 1) Windows Autopilot contains multiple scenarios, including scenarios without user interaction and that 2) methods without user affinity provide challenges with conditional access.
More information
For more information about configuring Windows 10 enrollment methods, refer to the following docs:
- What is device enrollment? – https://docs.microsoft.com/en-us/intune/enrollment/device-enrollment
- Intune enrollment methods for Windows devices – https://docs.microsoft.com/en-us/intune/enrollment/windows-enrollment-methods
- Enroll devices in Intune by using a device enrollment manager account – https://docs.microsoft.com/en-us/intune/enrollment/device-enrollment-manager-enroll
- Bulk enrollment for Windows devices – https://docs.microsoft.com/en-us/intune/enrollment/windows-bulk-enroll
- Enroll Windows devices in Intune by using the Windows Autopilot – https://docs.microsoft.com/en-us/intune/enrollment/enrollment-autopilot
- What is co-management? – https://docs.microsoft.com/en-us/configmgr/comanage/overview
- Enroll a Windows 10 device automatically using Group Policy – https://docs.microsoft.com/en-us/windows/client-management/mdm/enroll-a-windows-10-device-automatically-using-group-policy
Hi Peter, I always love you content and the way you layout the facts.
Any chance you can do an article on Windows AutoPilot Azure AD joined vs. Windows AutoPilot Hybrid Azure AD joined devices?
Thank you, Matt!
What is it that you want to know about the different Azure AD join scenarios? Just the pro’s and cons for both scenarios?
Regards, Peter
Hi Peter,
Thanks for a good overview, i have one question about the device enrollment manager secnario, can it be used to provision devices with autopilot, and will the device then have the DEM account as primary user?
Regards,
Nicklas
Hi Nicklas,
I’m not sure why you would want that. Autopilot has many options itself to prepare devices, like Whiteglove and Self-deploying mode.
Regards, Peter
Peter, thanks very much for the article.
May I ask, how do you enrol users of BYOD who are already registered in AAD (i.e. they already connected to the organisation via a Work/School connections – they did this prior to our use of Intune)? Do they have to unlink their accounts and relink?
Thanks a lot
Cheers
Tim
Hi Tim,
You should be able to add the MDM enrollment.
Regards, Peter
Hi Peter,
Always appreciate your work.
Following up on Tim’s comment above, how do you add the MDM enrollment? We have devices that are already joined in azure AD via Azure AD Connect from on prem. I have put some users of azure ad devices into a group that I specified to be in the MDM user scope, yet they do not get enrolled. Open to any thoughts.
Thanks in advance,
Brian
Hi Brian,
The MDM user scope will only help with automatic enrollment during the Azure AD join. Not afterwards. Are your devices hybrid Azure AD joined? If so, you could use a GPO.
Regards, Peter
Question; The Device Enrollment Manager can register up 1000 device. Any member of DEM-role will not have the device registration limit (e.g. 5 or 10) applied. But is the DEM user only bound by the number of registrations (ANY DEVICE) or does the DEM still need to listen to the Device Allowed platforms ? For some reason i assumed DEM would be allowed to register 1000 devices of any type. Maybe i misunderstood ?
Hi Toni,
I’m not sure what restricted number per platform you’re referring to. The device enrollment manager can enroll up to 1000 device. Not bound to a specific platform.
Regards, Peter
Hello Peter, thx for the reply. That is indeed what we have been testing…if a DEM can register ANY type of device, even if the device type restriction just says e.g. Android only. We have a test user in DEM role, and overall device number restrictions set to 1 (test lab) and android only. A normal user could just register his Android, but not a second android. Another user could not do iOS. but also the DEM was not able to register IOS. maybe we missed something…
Ah, now I understand your question Toni. To my knowledge the device type restrictions also apply to the device enrollment manager. The number is only for the allowed platforms.
Regards, Peter
In response to Brian’s question, we have exactly the same scenario. Would you recommend MDM enrolment of GPO?
Hi Paul,
Without knowing all the details, using a GPO could very well be a good method for triggering the enrollment.
Regards, Peter
Hi Peter,
thanks for your post!
We want to auto enroll a few devices during OOBE with a provisioning profile (PPKG file). But this will only work if the “MDM user scope” is set to “ALL”. If set to “ALL” both Azure AD Join and Enrollment to Intune will work. But we want to restrict the “MDM user scope” to “SOME”. If option “Some” is selected, we defined an Azure AD group (e.g. Inunte_MDM_AutoEnrollment) with the users which can do the enrollment. This won’t work as with the provisioning profile not the user will do the enrollment but the generated user “package_….”. But even if we add this user (package_…) to the Azure AD Users group (Intune_MDM_AutoEnrollment).
We need to restrict the AutoEnrollment to “some” users. Do you have an idea how this could work?
Thanks in advance for your help!
Regards, Phil
Hi Phil,
Why do you want to use a provision package?
Regards, Peter
Hello Peter,
Thank you for your excellent articles !
Quick question : are there been any change to enrollment mode lately ?
In my company, a few month ago I uses to enroll some device using bulk enrollment and auto-enrollment : deploying a provisioning package to join existing windows 10 enterprise device into AAD, then when licensed users sign-in, the device enroll into intune.
Now, in the same company but with another groups of users (that is allowed in MDM scope), I can’t get it to work. provisioning package is applied correctly and device become AAD joined, but auto-enrollment never trigger (scheduled task is not created) and they don’t get enrolled into intune.
I can trigger it by setting the local policy on device to enroll into MDM, which confirm there is no enrollment restriction or CA causing issue, but I never had to do this before and I can’t understand what is going on, neither finding any windows log about this.
Any idea about this ?
Are there no differences with your earlier configuration?
Regards, Peter
No change that I can think of. I reproduced the configuration step by step on another, blank tenant : works fine. On our prod tenant : still no auto enroll. Tried it with different users, default tenant upn to be sure. I’ve opened a ticket, at this point I believe it might be a backend problem.
Curious what the result of your ticket will be.
Regards, Peter
Hello Peter,
hope you are doing well!
I have a question, The devices are getting deleted automatically after enrolling a new device with DEM account. There is no device cleanup rule present ,No CA policy is applied. when they add one device then it deletes another. End goal is to enroll close to 1000 shared devices using this DEM account. we have tested with another newly created DEM account and the same behavior occurs. It gets deleted from Intune and AAD as well. Any help on this please
Hi Ravi,
I can’t reproduce that behavior. I would suggest to create a support ticket with Microsoft.
Regards, Peter