This week is all about app protection policies for managed iOS devices. More specifically, about some default behavior that might be a little bit confusing when not known. When creating app protection policies, those policies can be configured for managed devices or managed apps. That sounds simple. By default, however, when creating and assigning separate policies for managed devices and managed apps, every iOS device will apply app protection policies that are assigned to managed apps. That behavior is caused by the fact that the device will only be identified as a managed device when a specific configuration is in place. That configuration is the user UPN setting. Even better, the user UPN setting opens even more use cases for managed devices. This post will go through that setting, the different use cases and the required app configuration.
Note: A big thank you to Nico Bakker for the trigger for this blog post about app protection policies.
Introducing the user UPN setting for managed devices
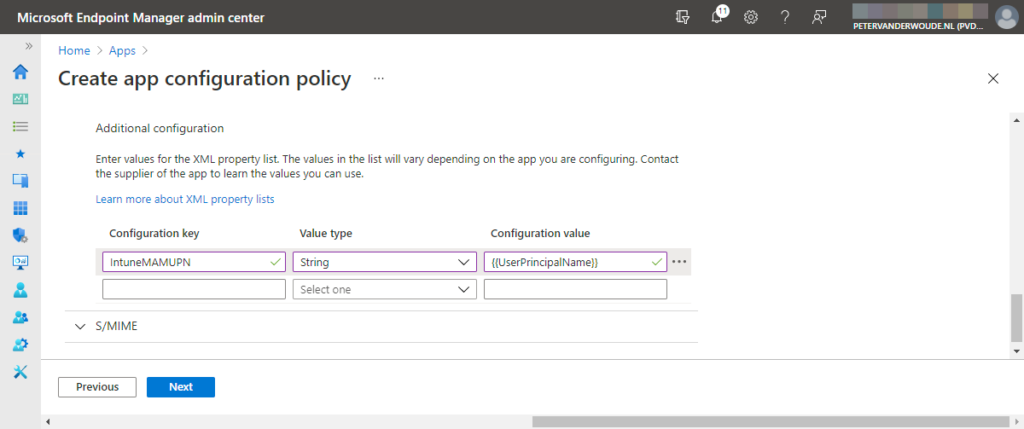
The user UPN setting is required for managed devices to identify the enrolled user account. That can be achieved by using the IntuneMAMUPN configuration key with the value type and configuration value as described in the table below.
| Configuration key | Value type | Configuration value |
|---|---|---|
| IntuneMAMUPN | String | {{UserPrincipalName}} |
The user UPN setting is used to make sure that the management type of the app is recognized as a managed device. Recognizing the correct management type is important to make sure that the protected apps are associated with the correct app protection policy and to make sure that the protected apps can work together with iOS managed apps. An iOS managed app can be basically any app that’s been distributed by using Microsoft Intune. Either pushed as required, or manually installed via the Company Portal app. That enables the IT administrator to use the Send org data to other apps property in an app protection policy with the value of Policy managed apps with OS sharing, to enable the user to send data from protected apps to iOS managed apps. That provides more flexibility for users to use their favorite apps for work activities and more flexibility for the IT administrator to use non-protected apps on a managed device.
Configuring the user UPN setting on managed devices
The configuration of the user UPN setting can be achieved by using an app configuration policy. That policy should be targeted to devices with the enrollment type of managed device, to make sure that it’s applied to the correct scenario and to make sure that the correct behavior is applied. That also brings a challenge, as that kind of app configuration policy should be configured per app. So, every app that should be protected with the correct app protection policy for managed devices and that should be able to send data to iOS managed apps, should have their own app configuration policy. The following seven steps walk through an example of such a policy for the Microsoft Outlook app. Other apps will be similar.
Important: This policy must be configured for every protected app on a managed device that should have the correct app protection policy applied and that should be able to send data to iOS managed apps.
- Open the Microsoft Endpoint Manager admin center portal navigate to Apps > App configuration profiles
- On the Apps | App configuration policies blade, click Add > Managed devices to open the Create app configuration policy wizard
- On the Basics page, provide the following information and click Next
- Name: Provide a name for the profile to distinguish it from other similar app configuration policies
- Description: (Optional) Provide a description for the profile to further differentiate app configuration policies
- Device enrollment type: (Grayed out) Managed devices
- Platform: Select iOS/iPadOS as value to apply this policy only to managed iOS/iPadOS devices
- Targeted app: Select Microsoft Outlook as value to apply this policy to the Microsoft Outlook app
Note: When configuring this app configuration policy for a different app, select that app as targeted app.
- On the Settings page, select Use configuration designer and provide at least the following configuration key in the Additional configuration section (as shown below in Figure 1) and click Next
- Configuration key: Specify IntuneMAMUPN as value for the configuration key
- Value type: Specify String as value for the value type
- Configuration value: Specify {{UserPrincipalName}} as value for the configuration value
- On the Scope tags page, configure the required scope tags click Next
- On the Assignments page, configure the required assignment and click Next
- On the Review + create page, verify the configuration and click Create
Note: When configuring an app configuration policy for managed iOS devices and enabling Allow only work or school accounts, the configuration key IntuneMAMUPN and its value is configured automatically.
Verifying behavior of configuring user UPN setting on managed devices
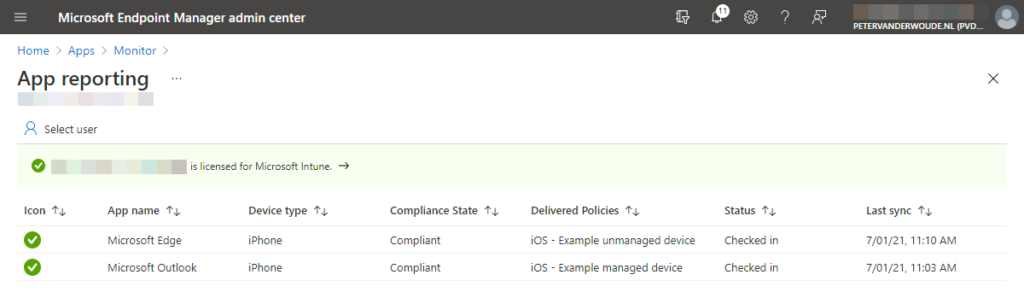
There are multiple methods to verify the configuration of the user UPN setting on managed devices. That could be verified by looking at the actual behavior of protected apps, with or without iOS managed apps. It is, however, maybe even better to look at the reporting about the protected apps, by looking at the applied app protection policies. When using different policies for unmanaged devices (i.e. managed apps) and for managed devices, the difference becomes clear. After applying the user UPN setting, the app protection policy for managed devices will be applied. Below in Figure 2 is an overview of a single device with two protected apps and two different delivered policies. The difference between the two protected apps is the applied user UPN setting. The Microsoft Edge app doesn’t have the user UPN setting applied and receives the policy for unmanaged devices (i.e. managed apps), while the Microsoft Outlook app has the user UPN setting applied and receives the policy for managed devices.
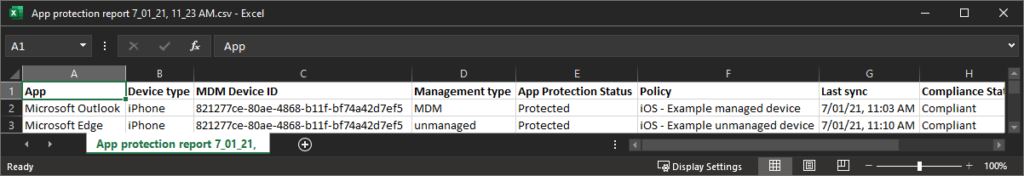
Below in Figure 3 are more details about that single device and the two protected apps. That shows more details to proof that it’s really the same device and to show that actually the management type has change for the app protection service.
Note: To simply verify that the app configuration policy is applied, open the Microsoft Edge app and browse to about:intunehelp. On the Intune Diagnostics page, navigate to Get Started > Share Logs to get the IntuneMAMDiagnosticsFiles.txt that contains all the applied app protections and app configuration settings.
More information
For more information about using app protection policies for iOS devices and Microsoft Intune, refer to the following docs.
Excellent write-up. Works as described for enrolled personal devices. FWIW, this doesn’t appear to apply to User-Enrolled iOS devices (“Policy Not applicable”) .
Thank you Brant.
Hi Peter,
Great post and really helpful. Can the app protection policies be extended to guest users in azure as well?
Hi Testing Uem,
No it doesn’t. For secure guest access, have a look at this: https://docs.microsoft.com/en-us/microsoft-365/solutions/create-secure-guest-sharing-environment?view=o365-worldwide
Regards, Peter
Hi Peter, many thanks for the article, really interesting.
Something not clear to me is that if Managed App policies apply by default, then if I create a managed device policy for the same app, which one will have preference?
Thanks,
Hi CB,
That’s why you need the IntuneMAMUPN key on managed devices. That will make sure that it’s recognized as a managed devices and that will make sure that the correct MAM policy is applied.
Regards, Peter
This has been an absolute saviour for me Peter. Thanks a lot Peter! 🙂
Just a quick question though, does it apply for the DEP/ABM devices as well?!
Hi Mrin,
Yes. That’s required to make it recognize the useraccount on a managed device.
Regards, Peter
Hi Peter,
I found your article because we are currently battling app protection policies 🙂
We have another MDM (Blackberry UEM) and we would like Intune to see them as “managed” and therefore bypass the app protection policy (which is targeted at “unmanaged” ios devices).
Is this possible? Or does the managed / unmanaged context only apply to Intune managed devices?
Thanks
Brian
Hi Brian,
I haven’t tested that, but pure theoretical it might work. As long as you can configure the UPN.
Regards, Peter
This is somewhat still confusing to me. We only have non-intune enrolled BYOD iOS devices and have a MAM policy defined to protect company data. The company would also like to use Whatsapp now to share company data. In this case is it enough to create a new App Configuration policy and define WhatsApp as a “Managed apps” policy without adding any Configuration Key?
Hi brokia,
When you’re only using it for unmanaged devices this is not needed at all. By default a device is seen as unmanaged.
Regards, Peter
Hi Peter ,
Big Fan! Wonderful write-up. I have started testing this policy. I am hoping that by applying this to just one app “Outlook” for an ADE iOS device, I am able to get that device to appear as managed and thus use the new Managed Apps filter to filter out the managed apps. Thus I can use this filter to exclude the managed devices from the APP that I use for MAM WE devices.
Would that sound sensible, or is there another approach? The reason being, I can see the enrolled Android devices using the managed app filter but for iOS, all my managed devices do not appear when applying that filter.
Regards,
Thomas T
Hi Thomas,
Not really. This configuration is really an iOS-thing to identify that the device is managed and use that information for applying the correct app protection policy. So, when the configuration is applied, the app will automatically pick the correct configuration.
Regards, Peter
Hi Peter,
Yes, found this the hard way. So I would ideally have to create one policy for each MAM app if i want it to be identifier right by the MDM iOS device.
Regards,
Thomas
That is correct, Thomas!
Regards, Peter
Hi Peter,
Im currently looking to deploy MAM in our environment for both iOS and Android. Can i just create one APP policy for iOS and one for Android and assign to same users group?
Also can use one policy to target both unmanaged and managed device, if yes how? I have created the policy and applied, everything works fine apart from encrypting data. if i forward an email with attachment from managed outlook to my personal email then am able to open the attached from my person email.
Hi Ram,
MAM only protects the data within the managed app that belongs to your corporate account. When that information is forwarded to a personal account that protection is not applicable anymore. In that case you might want to protect the data on a data-level.
Regards, Peter