This week is all about providing users with a method to deliberately opt-in for running Windows Insider Preview Builds. That option to opt-in is created by using an access package. That makes this post basically a combination between an earlier post about allowing users to opt-in for Windows 11 and an earlier post about managing Windows Insider Preview Builds. By default, many organizations prevent users from simply enabling and using Windows Insider Preview Builds. Often the main reason is to prevent unpredicted and unwanted issues from happening on the devices of users. Using an access package makes sure that the user consciously chooses to use Windows Insider Preview Builds, possibly in combination with the approval of a manager and in combination with sharing information in a specifically to Windows Insider devoted Teams-environment. This post walks through the steps for creating the required access package, followed with the steps for creating the required update ring. This post will end by showing the user experience with and after using the access package.
Important: This concept relies on the availability of Azure AD Premium 2 licenses.
Create a static Azure AD security group for assigning memberships
The first action is to create an Azure AD security group with an assigned membership type for the update ring assigment. This action is that straight forward that the steps to actually create that group are not described in further detail.
Create an access package for opt-in to Windows Insider Preview Builds
The second action is to create an access package that will be used to provide the user with an automated flow to opt-in for using Windows Insider Preview Builds. In reality that flow will just add the user to the just created Azure AD security group that will be used for the assignment of the Windows Insider Preview Build update ring. The following nine steps walk through the creation of that access package.
- Open the Azure portal and navigate to Azure Active Directory > Identity Governance > Access packages
- On the Identity Governance | Access packages page, click New access package
- On the Basics page, provide the following information and click Next: Resource roles
- Name: Provide a valid name for the access package to distinguish it from other similar access packages
- Description: Provide a description for the access package to provide more information about the access package
- Catalog: Select the catalog that should contain the access package
Note: When no catalog is available, make sure to create a catalog. That catalog is a container of resources and access packages and is used to group related resources and access packages.
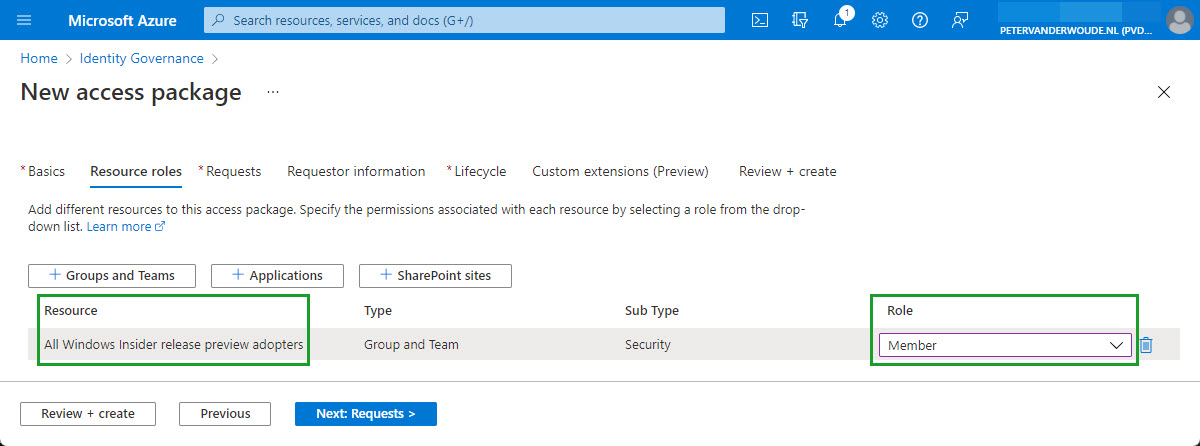
- On the Resource roles page, click Groups and Teams to add the Azure AD security group, set the Role to Member to make sure that the user opting-in for Windows Insider Preview Builds will be added as a member to the group, and click Next: Requests
Note: This section can also be used to add a Teams environment for sharing information with users, and between users, about Windows Insider Preview Builds and how it works with business apps.
- On the Requests page, provide the following information and click Next: Requestor Information
- Users who can request access: Select For users in your directory > All members (excluding guests) to allow all users to request access to the opt-in for Windows Insider Preview Builds
- Require approval: Select No to make it the responsibility of the user to opt-in for Windows Insider Preview Builds
- Enable new requests: Select No to prevent new requests
Note: This section can be used to add an approval flow that will be triggered after requesting access. That approval flow can be used to make sure that a manager has to approve the access to Windows Insider Preview Builds.
- On the Requestor information page, (optional) specify information and attributes from requestor to collect and click Next: Lifecycle
- On the Lifecycle page, provide the following information and click Next: Rules
- Access package assignments expire: Select Never to not expire the access package assignments
- Require access reviews: Select No to not review the access to the access package assignments
Note: This section can be used to add access reviews to the access package that will be automatically scheduled. Those reviews can be used to make sure that, once in while, the current access of users is reviewed.
- On the Custom extensions page, (optional) specify rules that trigger custom flows and click Next
- On the Review + Create page, verify the configuration and click Next
Create an update ring for Windows Insider Preview Builds
The third action is to create an update ring for Windows 10 and later that is used for controlling the Windows Insider Preview Builds that are enabled on the applicable devices in the organization. The following seven steps walk through the configuration of an update ring that is focused on the required configuration options for Windows Insider Preview Builds.
- Open the Microsoft Endpoint Manager admin center portal and navigate to Devices > Update rings for Windows 10 and later
- On the Windows | Update rings for Windows 10 and later blade, click Create profile
- On the Basics page, provide a valid Name and an (optional) Description and click Next
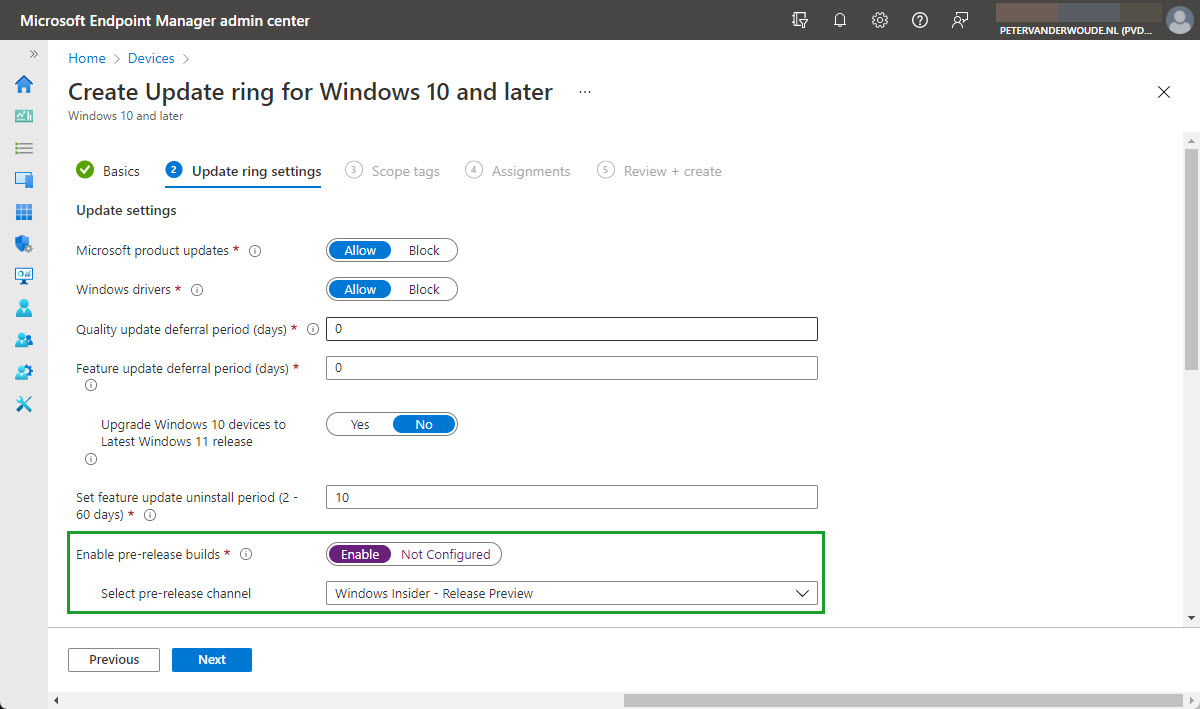
- On the Update ring settings page, provide at least the following configuration and click Next
- Update settings – This section is used for configuring the available update settings
- Microsoft product updates: Select Allow to also allow Microsoft product updates
- Windows drivers: Select Allow to also allow Windows drivers
- Quality update deferral period (days): Specify 0 to prevent the deferral of quality updates
- Feature update deferral period (days): Specify 0 to prevent the deferral feature updates
- Upgrade Windows 10 devices to Latest Windows 11 release
- Set feature update uninstall period (2 – 60 days): Specify 10 to enable the uninstall period
- Enable pre-release builds: Select Enable to enable the devices to run pre-release builds
- Select pre-release channel: Select Windows Insider – Release Preview, Beta channel, or Dev channel as the servicing channel to enable the devices to run a Windows Insider Preview Builds
Note: This section can also be used to configure the user experience. That can be used to configure the restart and deadline behavior. Those settings are not relevant to the purpose of this post.
- On the Scope tags page, configure the required scope tags and click Next
- On the Assignments page, add the just created Azure AD security group as included group and click Next
- On the Review + create page, review the configuration and click Create
Note: Keep in mind that enabling pre-release builds will require devices to reboot. There should, however, no longer be an additional reboot during Windows Autopilot (as the ManagePreviewBuilds setting is no longer changed).
Exclude Windows Insider Preview Build users from existing update rings
The fourth action is to exclude the just created and just included Azure AD security group, from the assignments of other existing update rings. That will make sure that only a single update ring is applicable. This action is that straight forward that the steps to actually exclude the group are not described in further detail.
User experience after opt-in for Windows Insider Preview Build
Once the access package is available and the update ring is configured, the user can actually request access to Windows Insider Preview Builds. The My Access portal can be used to achieve that. When the user navigates to that portal, an overview is shown of all the access packages that are available for that user. The user can select the just created access package to get an overview of the resources that belong to that package and to actually request access by clicking on Request access. That brings the user to the dialog that should be used to actually submit the request (as shown below in Figure 3).
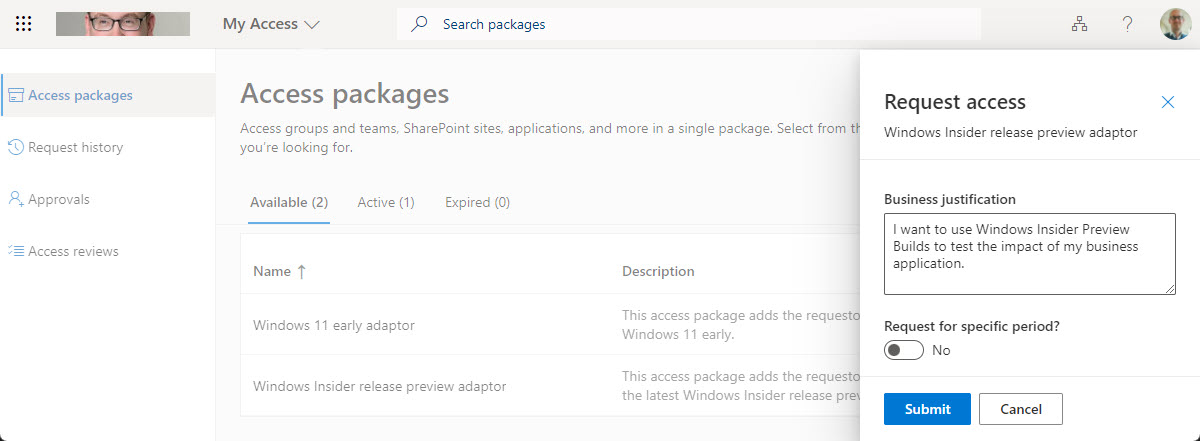
Immediately after the user requested access, the flow is triggered to add the user to the earlier created Azure AD security group. Once the user is added to that group, Microsoft Intune will make sure that only the earlier created update ring is applied and that the Windows Insider Program will be automatically configured. For this configuration the work account is used (as shown below in Figure 4).

Note: For this registration to the Windows Insider Program to work, it’s important that the requirements are in place and that the organization is registered with the Windows Insider Preview for Business program.
More information
For more information about update rings, entitlement management and the Windows Insider Program, refer to the following.
- What is entitlement management? – Azure AD | Microsoft Docs
- Request an access package – Azure AD entitlement management | Microsoft Docs
- Getting started with the Windows Insider Program
- Managing preview builds across your organization – Windows Insider Program | Microsoft Docs
- Configure Update rings for Windows 10 and later policy in Intune | Microsoft Docs

But this would add the user to the group which will then apply to all of his Windows devices. Is there a solution for specific test devices?
Also, insider requires you to activate the telemetry. If you have this disabled, you wont be able to join the insider program.
Correct, Peter. This is base on the user. For the device, you need to get creative to get the device of the user. That will probably also require you to look at something else than access packages.
Regards, Peter