This week is all about providing an overview of the best and easiest option for doing some initial testing of conditional access policies. The conditional access What If tool. The What If tool will help with easily understanding what to expect from the configured conditional access policies. It provides an overview of how the different conditional access policies will impact the user(s) under various sign-in conditions. In this post I’ll provide an overview of the What If tool, followed by the available evaluation settings and the evaluation results.
Important: At this moment the What If tool is still in public preview.
Introduction
Let’s start with a short introduction about the What If tool. The What If tool allows administrators to understand the impact of the conditional access policies in the environment. Instead of testing the conditional access policies by performing multiple sign-ins manually, the What If tool enables administrators to evaluate a simulated sign-in of a user. The simulation estimates the impact that a sign-in has on the conditional access policies and generates an evaluation report. That report lists the conditional access policies that apply (and not apply) to the simulated sign-in and it shows the classic conditional access policies, if they exist.
Available settings
Overview
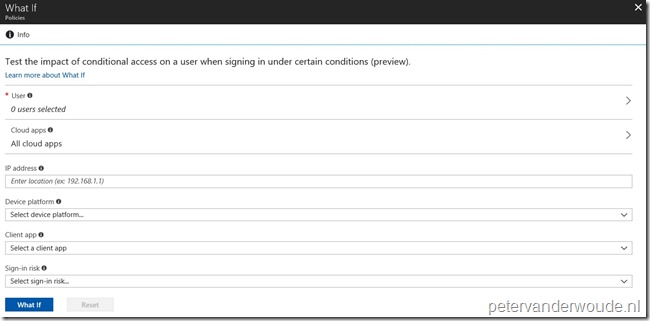
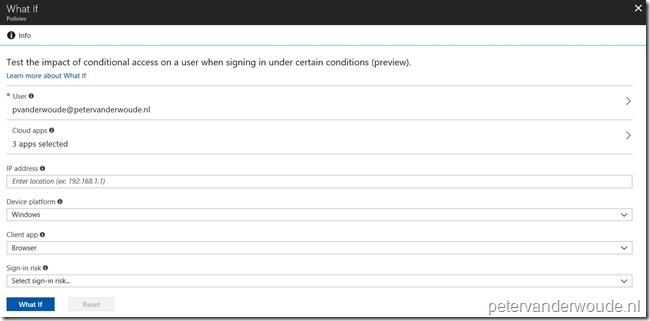
Now let’s continue with an overview of the What If tool. The What If tool is available in the conditional access section of the Azure portal. The following two steps walk through navigating to the What If tool, followed by an overview of the available settings.
| 1 | Open the Azure portal and navigate to Intune > Conditional access or to Azure Active Directory > Conditional access to open the Conditional access – Policies blade; |
| 2 | On the Conditional access – Policies blade, click What If to open the What If blade; |
| — |
Settings
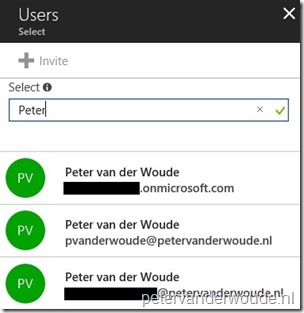
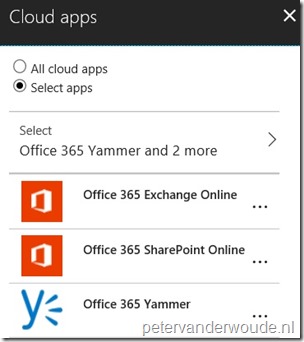
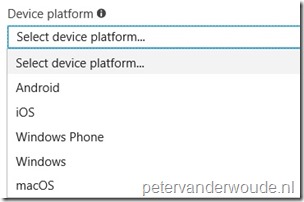
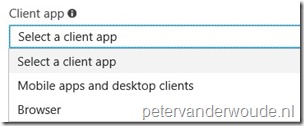
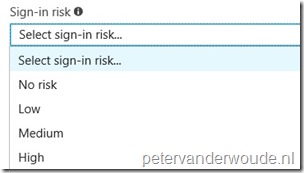
After looking at an overview of the What If tool, it’s time to look at the available evaluation settings. Within the What If tool the following six sections are available for testing conditional access policies.
Evaluation results
Let’s end this post by looking at the evaluation results of the What If tool. After making the selections, as shown above, to the settings to evaluate, and clicking the What If button, the tool What If tool generates a report of the affected conditional access policies. That report is divided into two tabs.
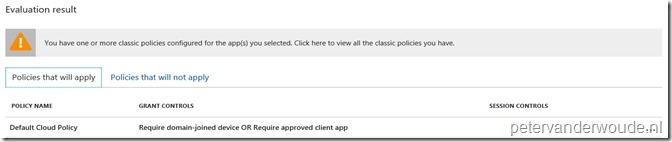
The first tab, which is shown below, contains the conditional access policies that apply to the selected user(s), in combination with the selected conditions. It also provides an overview of the grant controls that the user must satisfy to get access to the selected cloud apps.
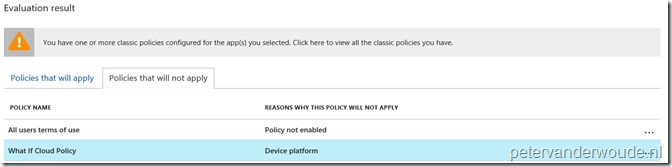
The second tab, which is shown below, contains the conditional access policies that will not apply to the selected user(s), in combination with the selected conditions. It also provides an overview of the reasons why the conditional access policy doesn’t apply. Good to know, when there are multiple reasons for a conditional access policy to not apply, it only shows the first reason.
Note: When classic conditional access policies still exist in the environment, the orange exclamation mark is shown above the evaluation results. Even when these conditional access policies are already disabled.
More information
For more information about the What If tool, refer to this article about the Azure Active Directory conditional access what if tool – preview.
Very nice feature.
Not directly related to conditional access, but it might be very helpful to have this kind of preview also when you create a scoping filter for the provisioning of users to an application. Just to be sure that the conditions of the scoping filter will target the right people
Hi Olivier,
At this moment, the closest to that is the troubleshoot section. If that’s not enough, you can always add the idea to UserVoice.
Regards, Peter