This week is another follow-up on the posts of the last weeks about customizing Windows 11 devices. This week, however, is focused on customizing the default app accosiations on Windows 11 devices. Customizing the default app associations enables organizations to associate specific apps with file and link types, for their users. Besides that, this post is also an updated version of this post of over four years ago. Even though not a lot has changed, the configuration did become easier. This post goes through the creation of the required app assocations file, folowed with applying that file on Windows 11 devices. This post ends with showing the user experience with the customized app assoications.
Important: My personal opinion is that – as with every other customization – the default app associations should be left untouched, when possible. In most cases the user and their apps will create their own app associations, when needed.
Creating the custom app associations in Windows 11
When looking at the configuration options for the default app associations on Windows 11, all the configurations are already available on Windows 10. The biggest change, however, is that in the meantime the configuration options via Microsoft Intune got slightly better. At least no need for using the ApplicationDefaults/DefaultAssociationsConfiguration policy in a custom configuration profile. That ADMX-backed policy setting is now available in the Settings Catalog and can be used to apply an XML-file with the required configuration. The following four steps go through the actions to configure the required app associations, to export the required XML-file and to encode that XML-file to Base64 format.
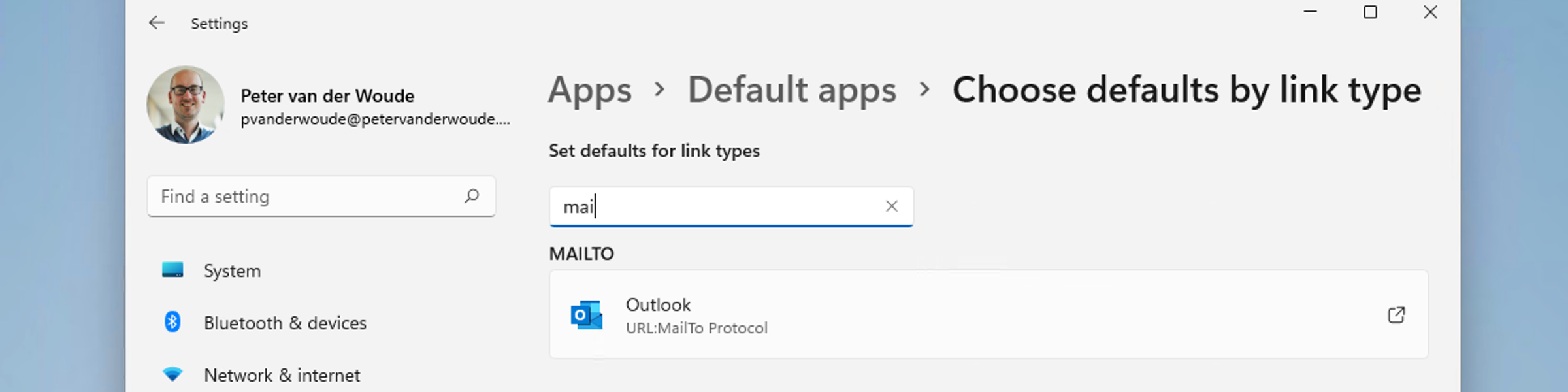
- On a Windows 11 device, open Settings > Apps > Default apps and configure the required app associations
- Open Windows Terminal and run
dism /online /export-defaultappassociations:defappass.xmlto export the XML-file with the configured app associations - Take out the required app assocation that should be configured on the Windows 11 devices
<DefaultAssociations>
<Association Identifier="mailto" ProgId="Outlook.URL.mailto.15" ApplicationName="Outlook"/>
</DefaultAssociations>- Open a Base64 encoder, like Base64 Encode and Decode – Online, and encode the content of the exported XML-file with the XML-file with the configured app associations to Base64 format
PERlZmF1bHRBc3NvY2lhdGlvbnM+Cgk8QXNzb2NpYXRpb24gSWRlbnRpZmllcj0ibWFpbHRvIiBQcm9nSWQ9Ik91dGxvb2suVVJMLm1haWx0by4xNSIgQXBwbGljYXRpb25OYW1lPSJPdXRsb29rIi8+CjwvRGVmYXVsdEFzc29jaWF0aW9ucz4=Important: Different configuration rules apply for organizations that are still into OS deployments. In that case taking out a part of the exported XML-file might cause An app default was reset messages on first boot (see for more information the docs here).
Configuring the custom app associations in Windows 11
When looking at actually applying custom app associations on Windows 11, the ApplicationDefaults/DefaultAssociationsConfiguration policy can be used. That ADMX-backed policy can be used to set the default file type and protocol associations. When set, the default associations are applied during the sign-in on Windows 11. The configuration of that policy can be achieved by using the Settings Catalog. The following eight steps walk through the creation of the Settings Catalog profile, with the required settings.
- Open the Microsoft Endpoint Manager admin center portal and navigate to Devices > Windows > Configuration profiles
- On the Windows | Configuration profiles blade, click Create profile
- On the Create a profile blade, provide the following information and click Create
- Platform: Select Windows 10 and later to create a profile for Windows 10 devices
- Profile: Select Settings catalog to select the required setting from the catalog
- On the Basics page, provide the following information and click Next
- Name: Provide a name for the profile to distinguish it from other similar profiles
- Description: (Optional) Provide a description for the profile to further differentiate profiles
- Platform: (Greyed out) Windows 10 and later
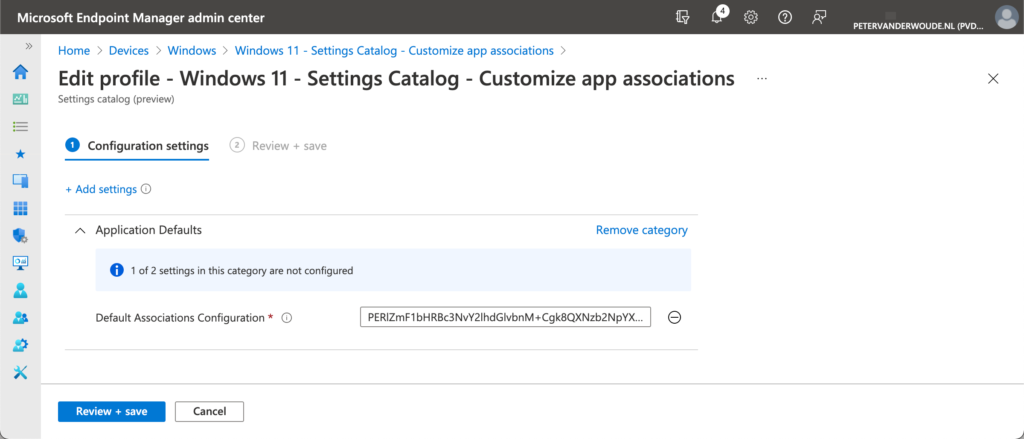
- On the Configuration settings page, as shown below in Figure 1, perform the following actions and click Next
- Click Add settings and perform the following in Settings picker
- Select Application Defaults as category
- Select Default Associations Configuration as setting
- Configure the selected settings with the following values
- Provide the created value with Default Associations Configuration
- On the Scope tags page, configure the required scope tags and click Next
- On the Assignments page, configure the assignment and click Next
- On the Review + create page, verify the configuration and click Create
Important: When customizing the default app associations, the existing associations of the user for the customized app associations will be overwritten.
User experience with the custom app associations in Windows 11
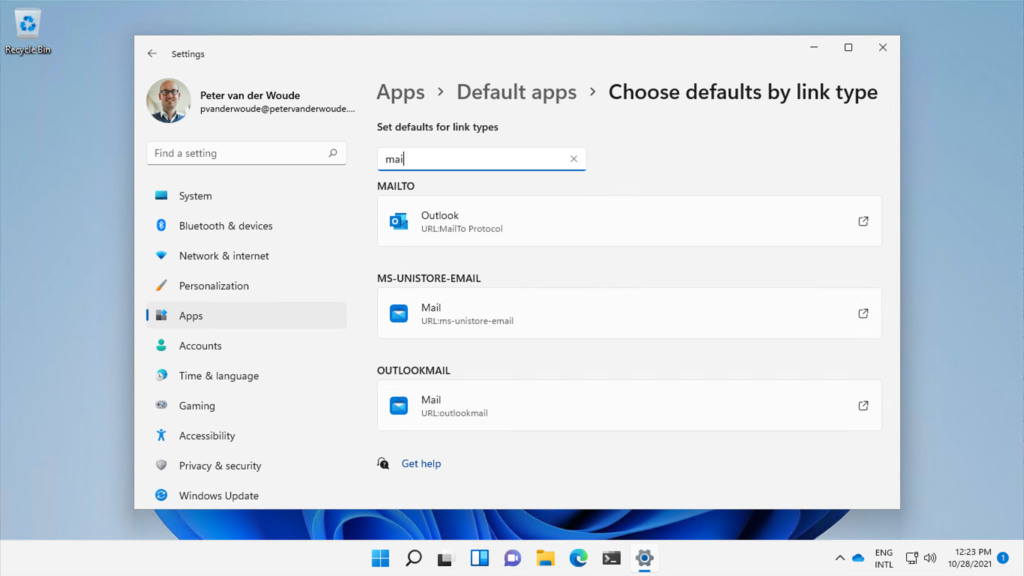
The best place to look at the configuration is by looking at the user experience. Figure 2 provides an overview of the customized app associations on Windows 11. It provides an overview that shows the example configuration that changes the mailto-link to Outlook. Besides that, it seems to imply that there is nothing preventing the user from making adjustments. That is, however, not true. Yes, the user can adjust the configured app association, but with the next sign-in the applied configuration will be back.
Important: After customizing app associations, the user won’t be able to adjust the customized app associations.
More information
For more information about customizing the default app associations on Windows 11, refer to the following docs.
In my Intune environment if I deployed multiple app associations it threw a conflict error on policy application, which was a bit of a bummer. Not sure if that’s your experience as well but in my case I was not able to layer multiple policies, which seems like a common use case. If you have app X then set these associations. If you have app Y then set these associations type of thing.
Hi Dan,
I haven’t used it recently, but it does sound familiar.
Regards, Peter
Hello Peter
I am attempting to do this via an Intune “settings catalog” policy, under the “application defaults” category.
It asks to do all the steps above, but rather than paste the Base64 into a CSP, it ask you to add the Base64 to SyncML. Then, I suppose, paste the entire SyncML into the little text box in the policy?
Have you tried this method?
Cheers
Hi CS,
Isn’t that the same settings as shown in this post?
Regards, Peter
Hey Peter
THanks for the reply.
Well it is, but I am wondering if you don’t have to paste the SyncML into that box rather than just the Base64.
Based on this from the tooltip of the “Default Associations Configuration”:
—
This policy allows an administrator to set default file type and protocol associations. When set, default associations will be applied on sign-in to the PC. The association file can be created using the DISM tool (dism /online /export-defaultappassociations:appassoc. xml), and then needs to be base64 encoded before being added to SyncML.
—
And also this part of the documentation on it,
https://docs.microsoft.com/en-us/windows/client-management/mdm/policy-csp-ApplicationDefaults?WT.mc_id=Portal-Microsoft_Intune_Workflows#applicationdefaults-defaultassociationsconfiguration
which shows a SyncML example. My impression was that the Base64 needed to be pasted into the SyncML template (the example given in the documentation linked above) step 4 here:
—
To create the SyncML, follow these steps:
1. Install a few apps and change your defaults.
2. From an elevated prompt, run “dism /online /export-defaultappassociations:appassoc.xml”
3. Take the XML output and put it through your favorite base64 encoder app.
4. Paste the base64 encoded XML into the SyncML
—
Or am I looking too deeply into this and should just paste the Base64 right into the box?
Hi CS,
The SyncML is what’s eventually being pushed by Intune.
Regards, Peter
Thank you for clearing that up!
Greetings,
If I export this default apps to an XML using DISM, do I still have to encode it to Base64 if I’m using standard Group Policy to deploy it? I’m not using InTune or EndPoint Manager or any other type of MDM setup. Just a local AD domain with group policy.
On our Windows 10 systems – I just used the regular XML file (no encoding) and copied it to the System32 folder before capturing the image. Windows 11 seems have changed a LOT of things under the hood.
Thanks!
Hi Dave,
This setting is based on a GPO-setting (Set a default associations configuration file) and hasn’t changed between Windows 10 and Windows 11. I just haven’t specifically tested it as a GPO-setting.
Regards, Peter
Hi Peter,
I have this settings active on windwos 11 22h2 and it seems to be broken… Intune just says the config is applied but no luck on the app association.
Hi Dennis,
I haven’t specifically tested that yet. When you can reproduce that behavior, my suggestion would be to create a case with Microsoft.
Regards, Peter
Correct, I can confirm the same behaviour, worked fine before but doesn’t work at this moment in Win11 22H2