This week a short blog post about configuring Bluetooth on Windows 10 devices that are managed via Microsoft Intune. More specifically, about configuring the Bluetooth encryption strength that is required for pairing Bluetooth devices. Last year there was a vulnerability regarding the Bluetooth encryption key negotiation that was addressed with an update to Windows and a specific configuration that should be performed to required a specific encryption strength. By default Windows allows all Bluetooth traffic, but with this vulnerability in mind some organizations might want to enforce a minimal encryption key size to be required for Bluetooth traffic. Even if that means that some Bluetooth devices won’t work, or stop working. In this post I’ll start with showing how to configure the Bluetooth encryption key size and I’ll end by showing the applied configuration.
Overview of the Bluetooth configuration options
Let’s start with an overview of the Bluetooth configuration options. Windows 10 already provides multiple configurations options regarding Bluetooth, via the Bluetooth policies in the Policy CSP. Most of these policies are already available via a Device restriction policy in the Cellular and connectivity section. That section contains nearly all available policies, with the exception of the latest policy, the ability to configure the encryption key size. That policy is recently introduced with Windows 10, version 2004, and will probably eventually also end-up in the UI.
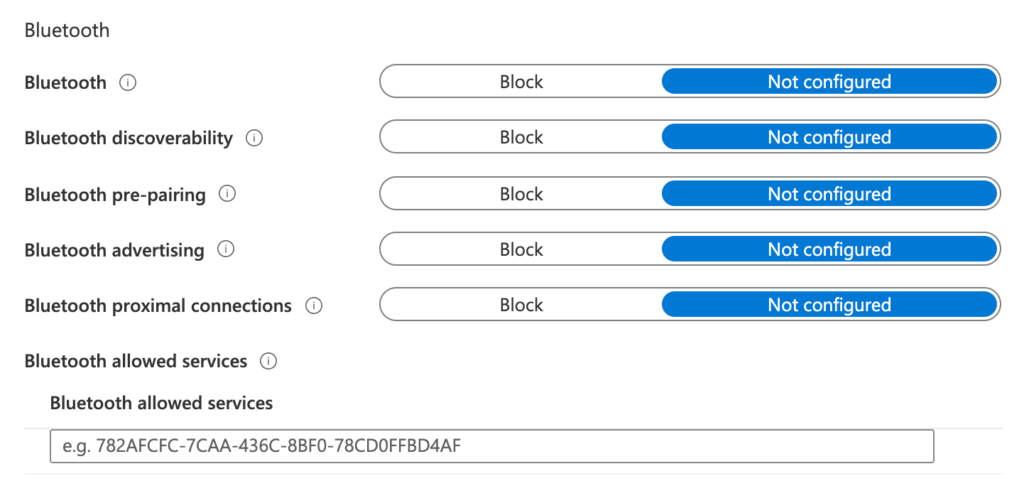
Figure 1: Current Bluetooth configuration options
That doesn’t mean that we can’t configure the Bluetooth encryption key size at this moment. Like with any available setting within the Policy CSP, it’s always possible to configure it by using a custom configuration profile. The only required information is the policy node and the available configuration values. Below is an overview of the required policy node within the Bluetooth section of the Policy CSP and the available configuration values.
| Policy | Description |
|---|---|
| SetMinimumEncryptionKeySize | This policy setting helps with preventing weaker devices cryptographically being used in high security environments, as there are multiple levels of encryption strength when pairing Bluetooth devices. The default configuration is 0 and allows all Bluetooth traffic. Number 1 can be used to always enforce Bluetooth encryption and ignoring the precise encryption key size. Any number from 2 through 16 can be used to always enforce Bluetooth encryption and in that case that number also represents the bytes used in the encryption process. |
Configuration of the Bluetooth encryption key size
After being familiar with the available policy settings and the possible values, it’s time to take a look at the steps for configuring the Bluetooth encryption key size policy setting. The nine steps below walk through the configuration of a new custom device configuration profile that includes the required OMA-URI and its value. The wizard style of configuring makes sure that the device configuration profile will be assigned to the selected users and/or devices.
- Open the Microsoft Endpoint Manager admin center portal navigate to Devices > Windows > Configuration profiles to open the Windows | Configuration profiles blade
- On the Windows | Configuration profiles blade, click Create profile to open the Create a profile page
- On the Create a profile page, provide the following information and click Create to open the Custom wizard
- Platform: Windows 10 and later
- Profile type: Custom
- On the Basics page, provide the following information and click Next
- Name: Provide a valid name for the custom device configuration profile
- Description: (Optional) Provide a valid description for the custom device configuration profile
- On the Configuration settings page, click Add to open the Add Row page. On the Add Row page, provide the following information and click Add (and click Next back on the Configuration settings page)
- Name: Provide a valid name for the OMA-URI setting
- Description: (Optional) Provide a valid description for the OMA-URI setting

Figure 2: Add custom configuration
- OMA-URI: ./Vendor/MSFT/Policy/Config/Bluetooth/SetMinimumEncryptionKeySize
- Data type: Select Integer
- Value: 7
- On the Scope tags page, configure the applicable scopes and click Next
- On the Assignments page, configure the assignment and click Next
- On the Applicability rules page, configure the applicability rules (think about the existence of this setting for only the Business, Enterprise and Education edition and the existence of this setting for only the 2004 version and later) and click Next
- On the Review + create page, verify the configuration and click Create
Result of the Bluetooth encryption configuration
Let’s end this post by showing the result of the Bluetooth encryption configuration. This time I’ll do that by simply looking at the Event Viewer and the MDM Diagnostic Report and relating the information seen at both locations. In both overviews the following corresponding information is seen of the successfully applied configuration.
- Policy setting: SetMinimumEncryptionKeySize
- Policy area: Bluetooth
- Policy value: 7
- Policy scope: Device
- Policy ID: 5C71E17A-2715-47C6-B338-4EE-07C445339
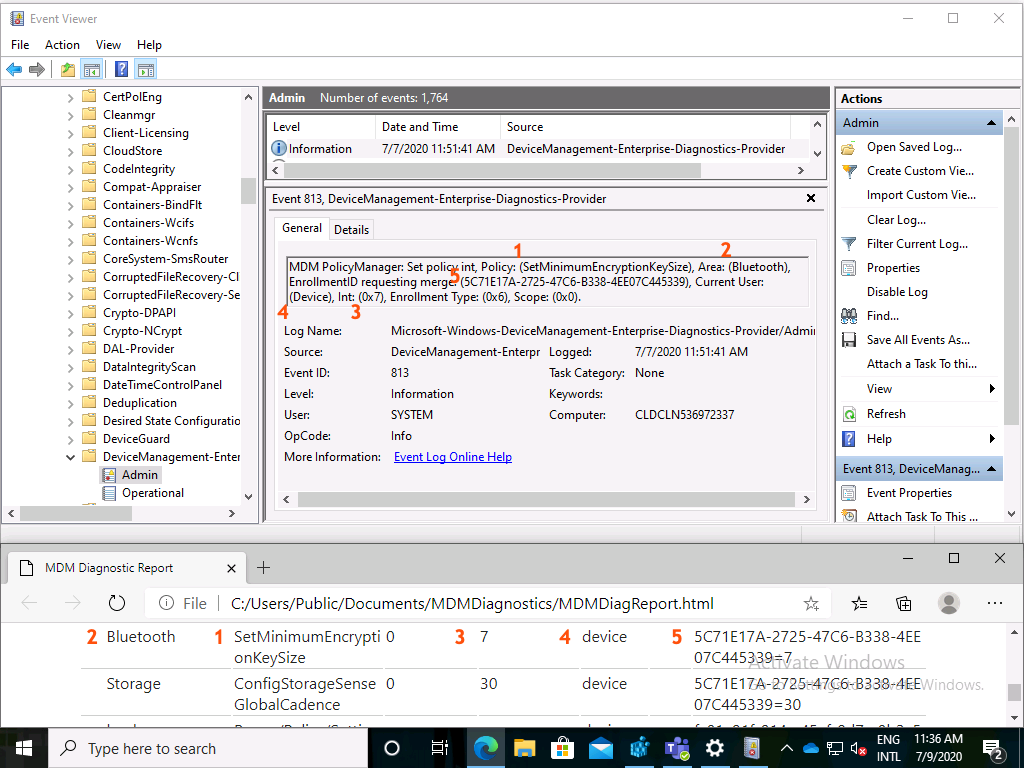
Figure 3: Result of the Bluetooth encryption configuration
More information
For more information about the different configuration options for Bluetooth, refer to the Bluetooth policies in the Policy CSP documentation.
How do you verify if the key is working?
Hi Jeppe,
The best way would be by using a device that doesn’t support the new configuration.
Regards, Peter
Thanks Peter!
We first tried this with 8 (min. 64 bit keysize) and 1 (any encryption).
Pairing is still possible, but devices won’t connect.
We tried this with different types of devices from bluetooth 2.1 to 5.1 like headsets, android phones and other notebooks.
When trying to connect we get an error saying
“Windows rejected a connection from your Bluetooth device ((MAC-Address)) because the resulting encryption key size was smaller than the system required minimum.”
Hi Michael,
Does that mean that basically all bluetooth headsets are rejected?
Regards, Peter
Yes, exactly. Every bluetooth device is rejected.
Did you verify the Bluetooth Core Specification v5.1 to verify the best encryption to use?
Regards, Peter
Yes we did. I think we figured out how to solve this:
I don’t know why (and I am still waiting for the MS-Support to verify this to me) but in addition to deploying this OMA-URI setting, we need to create and set this registry key
HKLM\System\CurrentControlSet\Policies\Hardware\Bluetooth
“EnableMinimumEncryptionKeySize”=dword value to 00000001
We found it by accident and wonder why those Microsoft articles are not linked to each other. (and why it’s even nescessary to set this config at two different locations)
Best regards
Michael
Forgot to share this link:
https://support.microsoft.com/en-us/topic/windows-guidance-for-bluetooth-key-length-enforcement-1b80c5b9-ddc1-31c7-1c3e-78e07c4fe877
Thank you for the update Michael. That indeed sounds a bit disturbing when that’s really required.
Regards, Peter
Hey Peter,
last comment:
The Microsoft Support confirmed that the fix that we have “deployed via intune to push the registry is the way to go and is a correct solution and still valid now”
Besteht regards
Thank you for the information Michael!
Definitely not what I expected..
Regards, Peter
Hello, where can I check the different bluetooth standards and how long enryption key length they support?
Hi Nish,
Not sure what you mean. Are you looking for an overview of the bluetooth specification: https://www.bluetooth.com/bluetooth-resources/bluetooth-core-specification-v5-1-feature-overview/?
Regards, Peter
In your example you have set your value to 7. That means it will use 7 bytes in the encryption process. Can we “map” this value to a specific standard? For example if we set value to 7 then only devices using bluetooth standard X.X and above will be able to connect? 🙂
Hi Nish,
That value was related to the value documented in the Windows guidance for Bluetooth key length enforcement.
Regards, Peter