This blog post is about a pre-release feature, which means that it’s included in the product for early testing in a production environment, but should not be considered production ready.
This week a blog post about the Conditional access for managed PCs feature that is introduced in ConfigMgr 1602. This feature is introduced as a pre-release feature. The requirements for using Conditional access for managed PCs are similar to the requirements of the blog series that I did a few months ago about Conditional access for PCs. Make sure that those requirements are in-place before starting with the configurations described in this post.
Introduction
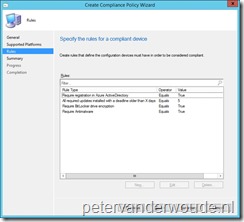
Conditional access for managed PCs is basically an additional level of restricting access to Exchange Online and SharePoint Online. Before the only level of restricting access was that device had to be enrolled via Microsoft Intune, or that the device had to be domain joined. Now it’s also possible to create additional compliance policies for managed PCs. Managed PCs by ConfigMgr. Those compliance policies can contain the following rules:
- Require registration in Azure Active Directory: This rule checks if the end-user device is workplace joined to Azure AD. If not, the device is automatically registered in Azure AD. Automatic registration is currently only supported on Windows 8.1.
- All required updates installed with a deadline older than a certain number of days: This rule checks to see if the end-user device has all required updates within the configured deadline and grace period. If not, any pending required updates are automatically installed.
- Require BitLocker drive encryption: This is a check to see if the primary drive on the device is BitLocker encrypted. If not, access to Exchange Online and SharePoint Online is blocked.
-
Require Antimalware: This is a check to see if the antimalware software is enabled and running. If not, access to Exchange Online and SharePoint Online is blocked. At this moment only supported for System Center Endpoint Protection and Windows Defender.
Configuration
Now lets have a look at the configuration. I will briefly mention the conditional access policy, because I’ve written a lot about those in my previous blog series about Conditional access for PCs. After that I’ll go through all the required steps for creating the compliance policy and I’ll end this configuration section with the effect on the client.
Pre-release feature
As Conditional access for managed PCs is a pre-release feature, it must be specifically turned on. This can be achieved by simply performing the following 2 steps.
| 1 | In the Configuration Manager administration console, navigate to Administration > Overview > Cloud Services > Updates and Servicing > Features; |
| 2 | Right-click Pre-release – Conditional access for managed PCs and select Turn on. |
Conditional access policy
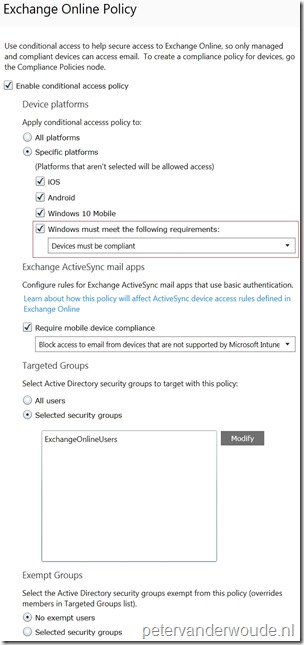
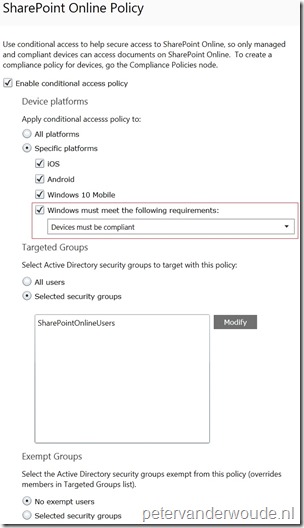
The reason why I do have to mention the conditional access policy, is one specific configuration setting. That specific setting is that the setting Windows must meet the following requirements is selected and configured to Devices must be compliant. This is very important, as any other configuration would make a domain join enough to be compliant, while in this configuration I want to create an additional compliance policy. That setting can be configured as shown below for Exchange Online and SharePoint Online.
| Exchange Online Policy | SharePoint Online Policy |
 |
 |
Compliance policy
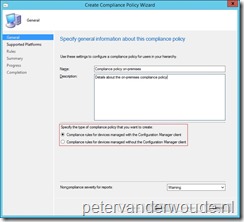
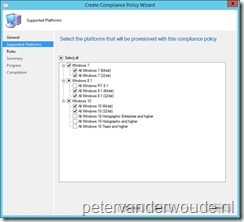
More interesting is the new compliance policy. Within the compliance policy it’s now possible to create a compliance policy specifically for devices managed with the ConfigMgr client. The following 9 steps will go through the creation of the compliance policy. After the creation of the compliancy policy, it can be deployed, like any other policy, to users.
Policy effect
A good place to look at the effect of the compliance policy, is to look at the reports. More specifically, the reports Compliance Access Compliance for Users and Compliance Access Compliance Report. However, I still like to think that the log files are the best place to look at the effect of the compliance policy. More specifically, the DcmWmiProvider.log. That log file provides detailed information about the compliance checks that are performed. Below is a log snippet about a successful compliance check.
CreateInstanceEnumAsync called for the provider
Class name CCM_SoftwareUpdateCompliance
Days 5
CCMSoftwareUpdateCompliance 20160313160716
CCMSoftwareUpdateCompliance Select * from CCM_UpdateCIAssignment
Determined 0 as not compliant with deadline exceeded by 5 days
CCMEncryptionCompliance: Get instance of CCM_EncryptionCompliance
Detected virtual machine: Drive encryption not applicable. Setting compliance to true
Setting Encryption Compliance to: 1
CheckWPJCert – Checking Machine\ cert store
Found WorkplaceJoin cert
Status: 2
Error: 0
CCMAntimalwareCompliance: Get instance of CCM_AntimalwareCompliance
Retrieved RealTimeProtectionEnabled property = 1
Retrieved AntivirusEnabled property = 1
Setting Antimalware Compliance to: 1
This log snippet provides clear information about the 4 rules, of the compliance policy, that are being checked. It clearly shows the software update check, the BitLocker encryption check, the workplace join check and the antimalware check. The log snippet even provides some details about how those checks are performed. For example, it shows that my test device was a virtual machine and that, because of that, the encryption check was skipped and that the compliance, for that check, was automatically set to true.
End-user experience
Now it’s time to look at the end-user experience. At this moment the end-user experience is as shown below. When a non-compliant managed PC tries to access Exchange Online, or SharePoint Online, it will get a message as shown below. A compliant managed PC will be able to simply access Exchange Online and SharePoint Online. To get the detailed information about the compliance of the managed PC, the end-user can use the Device compliance section in Software Center, as shown below.
| Non compliant | Compliant |
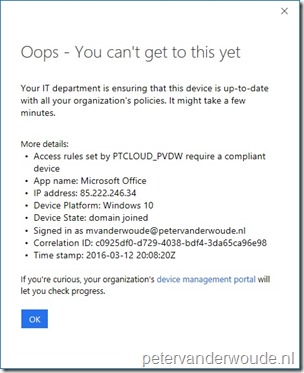 |
Not applicable. A compliant managed PC will automatically have access. Meaning there is no special screen that the en-user will get. |
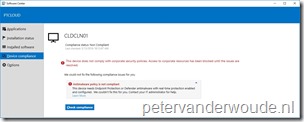 |
 |
More information
For more information about conditional access for PCs that are managed by ConfigMgr, please refer to this article about Manage access to O365 services for PCs managed by System Center Configuration Manager.

When I first read “conditional access” I just about flipped out thinking they were adding temporary access control mechanisms into the machines as in request/audit/approve temporary admin access. What a wonderful way to give helpdesk temporary elevated rights and keep it trackable…. but then that’s not traditionally a SCCM area of focus so I’m not sure why I read that much into it …
This is pretty cool too, but with NAS/NPS support pulled it seems like maybe that engine is getting written in native now … so hey maybe not so far off afterall…
True, this is really cool! It allows you to create policies to restrict access to Exchange Online and SharePoint Online. Really cool!
Hi Peter, whenever Microsoft refer to “domain joined” for compliance, does this mean joined to the on-prem domain, or does it mean the device is registered in Azure AD? Thanks.
Hi Nick,
That means joined to the on-premises domain.
Peter