Similar like last week, this week is also still about conditional access. This week is about the recently introduced user action of Register security information (Preview). A lot has been posted about that recently and I had my post ready, but I wanted to wait for an official blog post before publishing my version. Just to make sure that I’m using the right reasons for using this feature. Also, it simply fits the line of my recent post. This user action can be used to add conditional action to Azure AD security services that require information of the end-user. In this post I’ll start with a short introduction about this new user action and the behavior that the user action controls. After that I’ll show the configuration steps, followed by the end-user experience.
Introduction
Let’s start with a short introduction about the Register security information (Preview) user action. This user action can be used to add conditional access to Azure AD security service that require information of the end-user. That enables the administrator to require the end-user to be in a trusted location to register for multi-factor authentication (MFA) or self-service password reset (SSPR). At this moment this user action responds to the following:
- https://aka.ms/setupsecurityinfo – The new, still in preview, combined security information registration page for MFA and SSRP;
- https://aka.ms/mfasetup – The MFA security information registration page. With preview features enables for end-user, this will redirect to the new combined page;
- https://aka.ms/ssprsetup – The SSRP security information registration page. With preview features enables for end-user, this will redirect to the new combined page;
Configuration
Let’s continue by having a look at the configuration options. Let’s do that by looking at a simple scenario that is focused on the Register security information user action. That scenario is to only allow users to register their security information, when connecting from a trusted location. The following seven steps walk through that scenario.
| 1 | Open the Azure portal and navigate to Microsoft Intune > Conditional access > Policies or navigate to Azure Active Directory > Conditional access > Policies to open the Conditional Access – Policies blade; |
| 2 | On the Conditional Access – Policies blade, click New policy to open the New blade; |
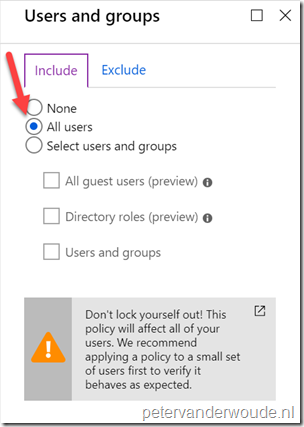
| 3a |
Explanation: This configuration will make sure that this conditional access policy is applicable to all users. |
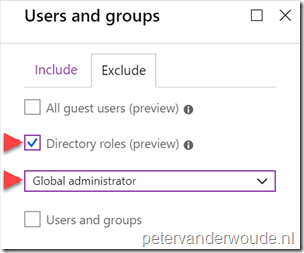
| 3b |
Explanation: This configuration will make sure that this conditional access policy will exclude global administrators. As global administrators should not be treated as normal users (to prevent a potential lock out) and usually have a separate conditional access policy applied. |
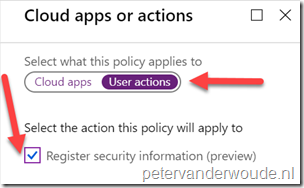
| 4 |
Explanation: This configuration will make sure that this conditional access policy is only applicable to user actions to register security information. |
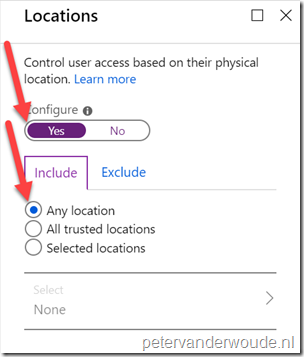
| 5a |
Explanation: This configuration will make sure that this conditional access policy is applicable to any location. . |
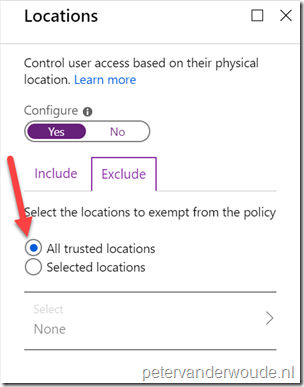
| 5b |
Explanation: This configuration will make sure that this conditional access policy will exclude trusted locations. As this conditional access policy should only be applied to untrusted locations. |
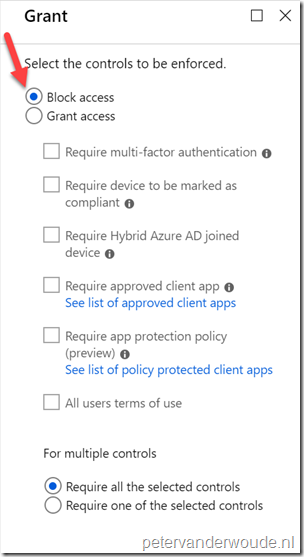
| 6 |
Explanation: This configuration will make sure that this conditional access policy will block access for any location that is not trusted by the IT organization. . |
| 7 | Open the New blade, select On with Enable policy and click Create; |
Note: Keep in mind that the Register security information user action is still in preview.
End-user experience
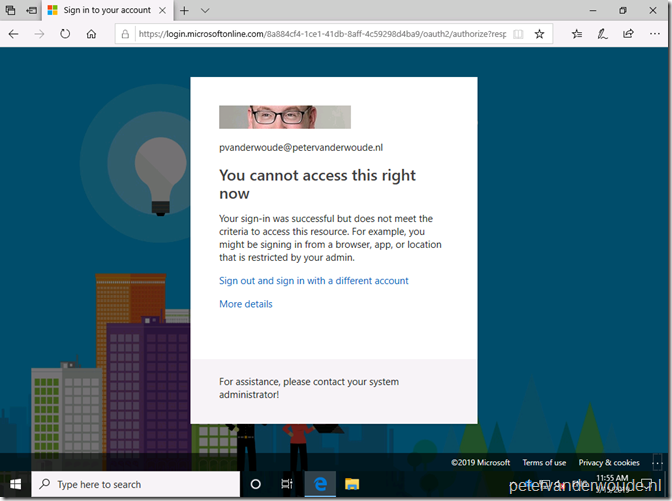
Now let’s end this post by having a look at the end-user experience. When the end-user is connecting from a non-trusted location, the end-user will be blocked from accessing any of the earlier mentioned URLs. In that case the end-user will receive the message “You cannot access this right now” as shown below.
I did notice a few hick-ups when using this feature in it’s early preview state:
- When using the new combined security information registration page for MFA and SSRP, the URL will re-direct via the Microsoft App Access Panel. That can trigger other conditional access rules that are configured for cloud apps;
- Often I could initially sign-in shortly before getting tossed out by conditional access;
More information
For more information regarding conditional access and sign-in frequency, please refer to the following article:
- Conditional access for the Azure AD combined MFA and password reset registration experience: https://techcommunity.microsoft.com/t5/Azure-Active-Directory-Identity/Conditional-access-for-the-Azure-AD-combined-MFA-and-password/ba-p/566348
Great post.
I have got a question surrounding this.
I work in an org where we do not allow unmanaged devices access to any of our Azure/M365 services. We use both conditional access and tenant restrictions and other methods to secure our environment.
However we are in the process of enabling Azure virtual desktop and we DO want to users to be able to use this from an unmanaged device.
We find that since enabling combined registration one of CA policies is blocking access for a user to register their security information either from the legacy workflows or using the combined registration experience.
Using the user actions – register security information to allow from all locations also doesn’t seem to work.
We cannot make any exceptions or remove the conditional access policy, which BTW prevents unmanaged devices to access. We do have another CA policy which does allow AVD from an unmanaged device but mandates MFA. That works great until we force the user to register SSPR security information.
Are you aware of any other options that could help in this scenario?
Thanks
Hi isotonic_uk,
If I remember correctly that redirects to Microsoft App Access Panel and that is blocked by CA. Right?
Regards, Peter
That is correct