Getting started with compliance for Linux devices
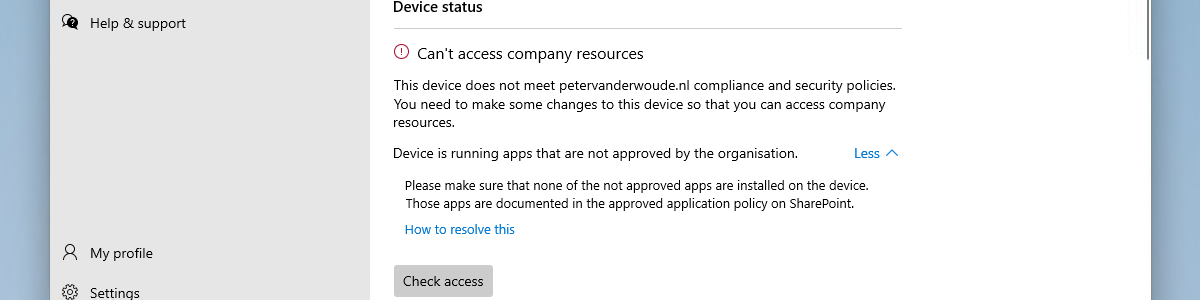
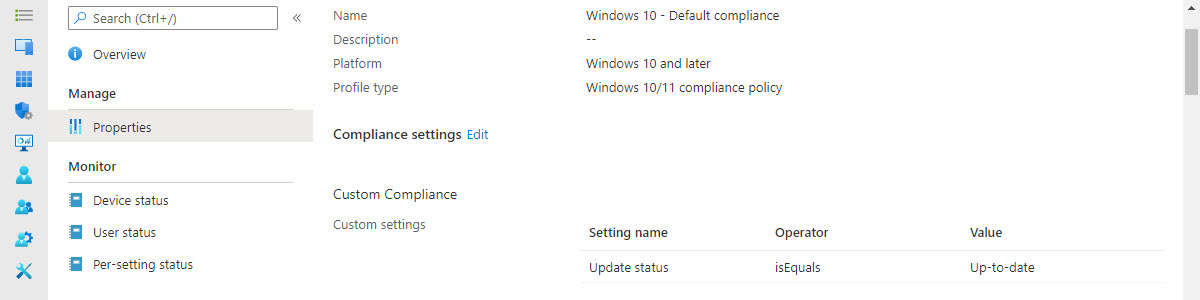
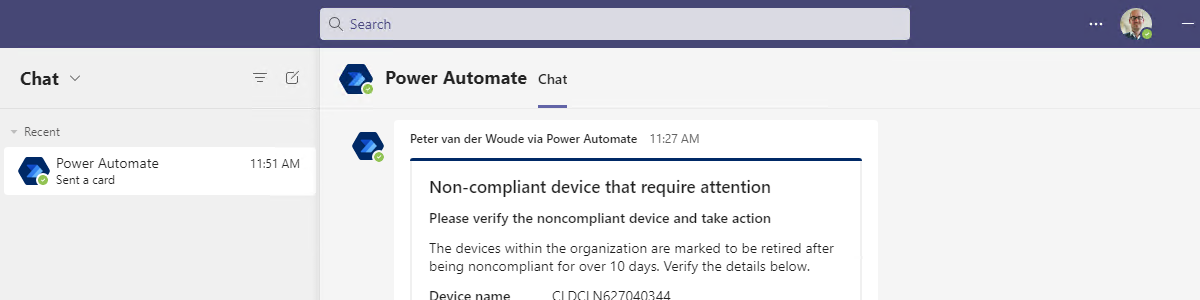
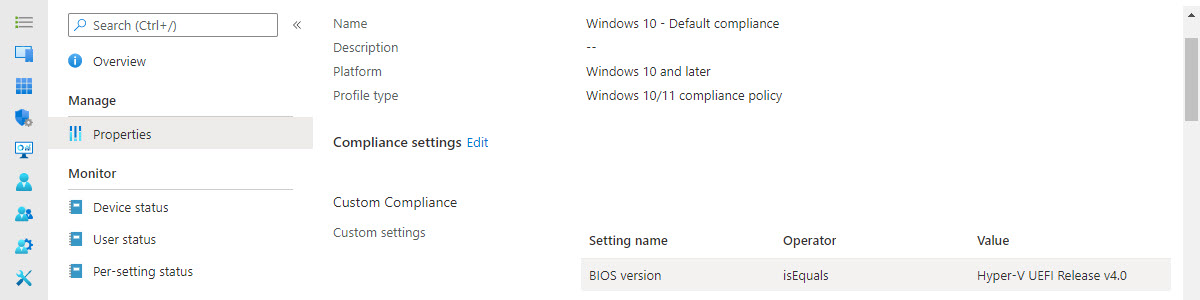
This week is about a totally different platform as the last few months. This week is all about Linux devices. A few years ago, I wrote this post about supporting the unsupported platforms. This post will describe a solution that will address the biggest part of that challenge, as it will enable the compliance of Linux devices. All powered by the enrollment in Microsoft Intune. That enables organizations to require Linux devices to be compliant and enable users to be productive. Even on Linux devices. Besides that, it’s good to keep in mind that, at this point in time, it’s really only about device compliance. Configuring Linux devices is not part of the currently available functionalities. This post will describe the minor details about the …