This week is all about device compliance. More specifically, this week is all about the just introduced capability to block access to company resources if certain apps are installed. This enables organizations to truly blacklist specific apps that are not allowed when using devices to access company resources. In this case it’s not about the apps used for accessing the company resources, but it’s really about the apps installed on the device. In this post I’ll provide the configuration steps, by using OWA for iPad as an example, followed by the end-user experience.
Configuration
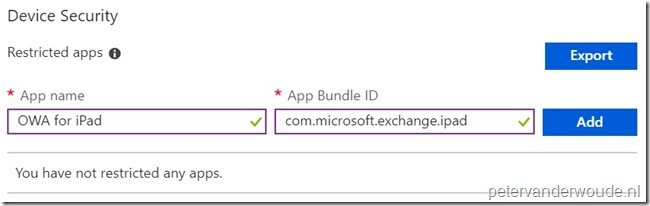
Before starting with the actual configuration, it’s important to get the bundle ID of the iOS app that cannot be installed. These steps are very clearly documented here. I will use OWA for iPad as an example, which has the following bundle ID: com.microsoft.exchange.ipad.
Now let’s continue by having a look at the configuration steps. The following five steps walk through the creation of a device compliance policy with at least the configuration of OWA for iPad as a restricted app. Within a device compliance policy a restricted app is what was earlier described, in this post, as blacklisted apps. After the creation of the device compliance policy, simply assign it to the applicable user group.
| 1 | Open the Azure portal and navigate to Intune > Device compliance > Policies; |
| 2 | On the Device compliance – Policies blade, click Create Policy to open the Create Policy blade; |
| 3 |
On the Create Policy blade, provide a Name, select iOS with Platform and select Settings to open the iOS compliance policy blade; Note: This is currently an iOS only configuration. Android is expected a bit later. |
| 4 | On the iOS compliance policy blade, select System Security to open the System Security blade; |
| 5 |
On the System Security blade, navigate to the Device Security section, provide the App name, the App Bundle ID and click Add, followed by and clicking OK, OK and Create. Note: The provided App name will be mentioned in the potential non-compliance message to the end-user and the App Bundle ID is in this example the id of the OWA for iPad app. |
| — |  |
Note: To complete this configuration, it must be used in combination with a conditional access policy that requires the device to be marked as compliant.
End-user experience
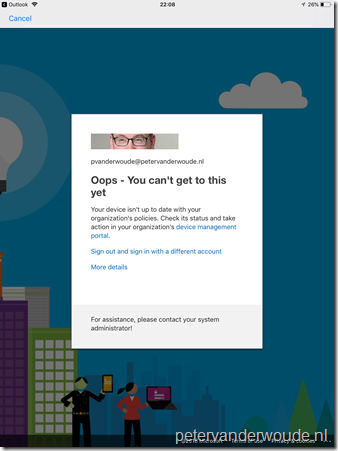
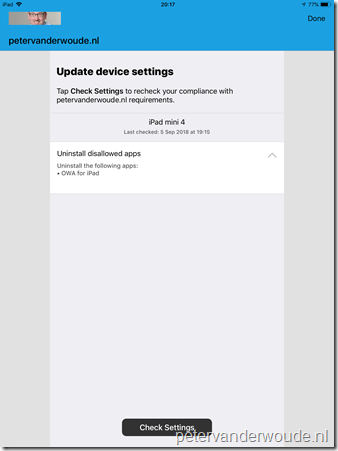
Now let’s end this post with the end-user experience. Let’s do that by looking at the end-user experience on an iOS device with OWA for iPad installed. On the left is the default message that is displayed to the end-user when trying to access company data on a non-compliant device. On the right is the message that the end-user will receive in the Company Portal app related to the compliance state of the device. In this case it will provide the end-user with a list of disallowed apps that should be uninstalled. The list shows the name of the app, as provided in the compliance policy.
 |
 |
More information
For more information about blocking access if certain apps are installed, refer to the documentation about adding a device compliance policy for iOS devices in Intune.
hi
Is the MD devices only
thanks
Hi Simon,
This is currently iOS only.
Regards, Peter
Peter,
Does it mean the app cannot be used to connect to corp data, or is only the precense of the app enough to get blocked? Will Windows 10 also be supported, for example block flash or Adobe 🙂 ?
Hi Rkast,
It means that the presence of the app is enough to get blocked. Currently this is iOS only and Android should follow. Haven’t seen anything about Windows 10 yet.
Regards, Peter