This week another blog post about new MDM capabilities that are introduced in Windows 10, version 1703. This post is focused on enabling the setting to allow users to connect remotely to this computer via Remote Desktop. To enable that specific setting, Windows 10, version 1703, introduced ADMX-backed policy via the Policy CSP. In this post I’ll provide a short introduction about ADMX-backed policies, which is actually a short summary of the Microsoft docs, and I’ll show a configuration example. I’ll end this post by showing the end-user experience.
Introduction
Starting with Windows 10, version 1703, the Policy CSP can now also handle ADMX-backed policies. In an ADMX-backed policy, an administrative template contains the metadata of a GPO. Each administrative template specifies the registry keys, and their values, that are associated with a GPO and defines the policy settings that can be managed. Each setting in an administrative template corresponds to a specific registry value. Windows maps the name and category path of a GPO to a MDM policy area, and policy name, by parsing the associated ADMX-file, finding the specified GPO, and storing the metadata in the Policy CSP. When the MDM policy is referenced, this metadata is referenced and determines which registry keys are set or removed.
Configuration
Now let’s have look at the configuration for enabling the setting to allow users to connect remotely to this computer. I’ll do that by first going through the available settings, related to Remote Desktop, and getting the required values. After that I’ll put those two together in a configuration example.
Available settings
As Windows 10, version 1703, introduced a few new settings to manage Remote Desktop, I thought it would be good to briefly go through these new settings. The root node for the Remote Desktop related settings is, in the Policy CSP, ./Vendor/MSFT/Policy. The Remote Desktop related settings are grouped below ./Vendor/MSFT/Policy/Config/RemoteDesktopServices and contains the following settings.
| Setting | Description |
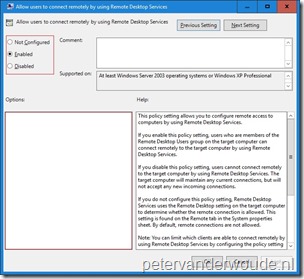
| AllowUsersToConnectRemotely | This setting allows the administrator to configure remote access to computers by using Remote Desktop Services. |
| ClientConnectionEncryptionLevel | This setting allows the administrator to specify whether to require the use of a specific encryption level. |
| DoNotAllowDriveRedirection | This setting allows the administrator to specify whether to prevent the mapping of client drives in a Remote Desktop Services session (drive redirection). |
| DoNotAllowPasswordSaving | This setting allows the administrator to control whether passwords can be saved on this computer from Remote Desktop Connection. |
| PromptForPasswordUponConnection | This setting allows the administrator to specify whether Remote Desktop Services always prompts the client for a password upon connection. |
| RequireSecureRPCCommunication | This setting allows the administrator to specify whether a Remote Desktop Session Host server requires secure RPC communication with all clients. |
Available values
Now that I’ve been through the available settings related to Remote Desktop, let’s have closer look at the setting that enables the administrator to allow users to connect remotely to this computer. That’s the setting AllowUsersToConnectRemotely.
Note: When a setting contains more configuration options, like the ClientConnectionEncryptionLevel setting, which relates to the Set client connection encryption level setting, then it’s required to dive into the ADMX-file that contains the GPO setting. The ADMX-file contains the available elements that are required when the setting is enabled. In this case the TerminalServer.admx. Minor detail, this ADMX-file doesn’t contain readable information related to the required setting. To find the related setting in that AMDX-file, my advise is to first find the setting in the related AMDL-file. In this case the TerminalServer.adml. That file contains readable information and shows the name of the setting in the ADMX-file. In this case the setting is TS_ENCRYPTION_POLICY. The additional element for that setting is TS_ENCRYPTION_LEVEL and the available values for that element are 1, 2 and 3. Every element must show as data in the ADMX-backed policy. Related to ADMX-backed policies, this could translate to a value of <enabled /><data id=”TS_ENCRYPTION_LEVEL” value=”1″/>.
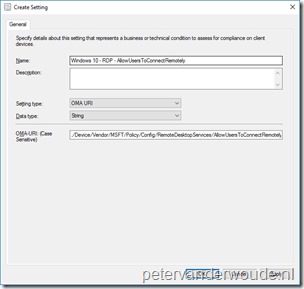
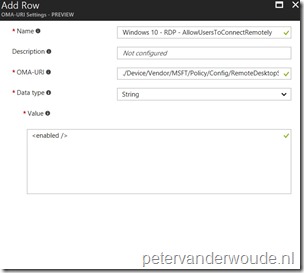
Together this means that to enable the setting to allow users to connect remotely to this computer, the following OMA-URI configuration can be used:
- OMA-URI: ./Device/Vendor/MSFT/Policy/Config/RemoteDesktopServices/AllowUsersToConnectRemotely
- Date type: String
- Value: <enabled />
Configure settings and values
Let’s put the setting and values together. Together this information can be used in Microsoft Intune hybrid and Microsoft Intune standalone, by using the configuration guidelines shown below.
End-user experience
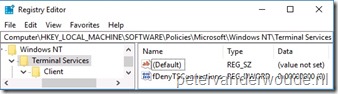
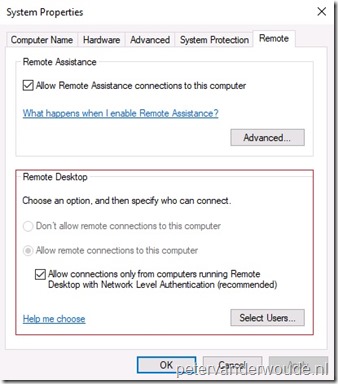
Let’s end this post with the end-user experience. This time I’ll do that by showing the configuration in the user interface and in the registry. Like with configuring the setting to allow users to connect remotely to the computer, via GPO, the Allow remote connections to the computer setting is enabled and grayed-out, as shown below on the right. This also corresponds to the registry setting fDenyTSConnections at HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT\Terminal Services, as shown below on the right. As these are ADMX-backed policies, the settings are configured in the registry.
 |
 |
More information
For more information about ADMX-backed policy and the Policy CSP, please refer to:
- Understanding ADMX-backed policies: https://msdn.microsoft.com/en-us/windows/hardware/commercialize/customize/mdm/understanding-admx-backed-policies
- Policy CSP – ADMX-backed policies: https://msdn.microsoft.com/en-us/windows/hardware/commercialize/customize/mdm/policy-admx-backed
Hi Peter.
Thank you very much for this article, very interesting.
Could you please cover more complex ADMX templates in the future posts like InternetExplorer/AllowTrustedSitesZoneTemplate?
Thank you.
Hi Jack,
Have a look at this post by Arjan Vroege: http://www.vroege.biz/?p=3139#more-3139
Also, tomorrow I’ll have a post online explaining how to configure more advanced settings. In a step-by-step format.
Regards,
Peter
Hi Peter,
First thing. Brilliant Blog it has been a life saver for a firstie Intune implementation!
This is not directly related to the above but wondered if you had any other examples of using ADMX configs? primarily im trying to use the Onedrive one
many thanks
Jon
I’ve got a few more examples on my blog. However, keep in mind that at this moment not all the GPO-settings are available via MDM. Only the documented settings.
Hi Peter,
The policy is being applied effectively (I checked via the GUI and the fDenyTSConnections regkey), but I notice that the firewall is not adapted accordingly. Do I need to apply an extra policy of some kind? I’m running Win10 1803.
Kind regards,
Manu
Hi Manu,
If I’m not mistaken, that policy only does the specific setting and still requires you to configure the firewall separately.
Regards, Peter
Hi Peter, like Manu, I’m halfway there. I was able to set RDP on, but this doesn’t create the firewall exception. I think a lot of folks want to do this – it would be super helpful to know how to manage the firewall rules using the Firewall CSP like this example from the Config CSP.
I tried an OMA-URI of:
./Device/Vendor/MSFT/Firewall/MdmStore/FirewallRules/RemoteDesktop-UserMode(TCP-In)/Enabled
and string data
but no joy. Please help!
Hi Andrew,
From what I’ve heard recently, creating firewall rules via custom URI is currently not supported.
Regards, Peter
ok – thanks. Will investigate using PowerShell…