This blog post uses the TaskManager node of the Policy CSP, to prevent the end task functionality on Windows 10 devices. This node is added in Windows 10, version 1809, which is currently still in preview.
This week a short blog post about a newly introduced setting in Windows 10, version 1809, which is currently still in preview. That’s the setting to prevent non-administrator users from ending tasks via Task Manager. That can be a useful addition to a Windows AutoPilot deployed device on which the users are configured as standard users. Simply preventing users from performing activities that an administrator might not like them to do. In this post I’ll show the available settings, followed by the configuration and the end-user experience.
Settings
Let’s start by having a look at the available settings. The TaskManager area is a new node within the Policy CSP. That area currently contains only one policy setting, which is AllowEndTask. That policy setting can be configured to an Integer value of 0, which means that the end task functionality is blocked in Task Manager, or to an Integer value of 1, which means that the end task functionality is available in Task Manager. By default, the end task functionality is available. Also, keep in mind that this configuration is only applicable to non-administrator users.
Configuration
Now let’s continue by having a look at the configuration to prevent non-administrator users from ending tasks via Task Manager. In other words, create a device configuration profile with the previously mentioned custom policy setting. The following three steps walk through the creation of that device configuration profile. After that simply assign the created profile to a user or device group.
| 1 | Open the Azure portal and navigate to Intune > Device configuration > Profiles; |
| 2 | On the Devices configuration – Profiles blade, click Create profile to open the Create profile blade; |
| 3a |
On the Create profile blade, provide the following information and click Create;
|
| 3b |
|
Note: At some point in time this configuration will probably become available in the Azure portal without the requirement of creating a custom OMA-URI.
End-user experience
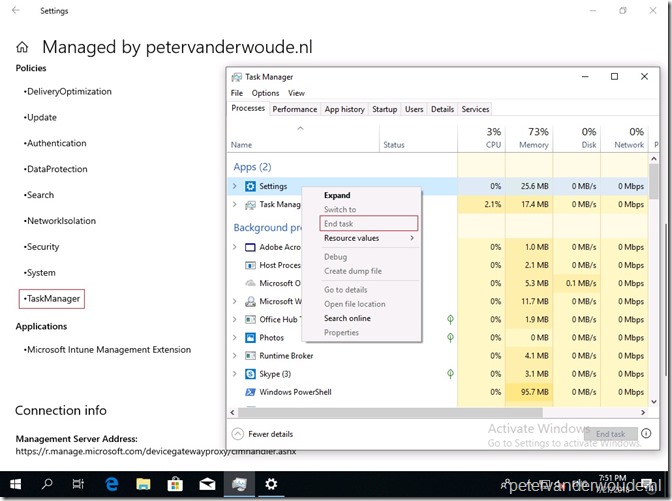
Let’s end this post by looking at the end-user experience. Below is an example of a Windows 10 device running the latest available Windows Insider Preview build and deployed via Windows AutoPilot. In that example it’s visible on the left that the TaskManager policy is configured and it’s visible on the right that the end task option is actually grayed out for the user. In other words, the user is unable to end a task via Task Manager.
More information
For more information about the available Task Manager settings in the Policy CSP, please refer to the documentation about Policy CSP – TaskManager.

Does this disable the menu item or the functionality in total? In other words; does this prohibit tools such as processExplorer (and possibly even remote code exec) from disabling processes?
And what’s the effect on non-current user processes? I.e. SBC environments.
Hi Jeroen,
Based on the description of the policy (this setting determines whether non-administrators can use Task Manager to end tasks) I would say that it only prevents the functionality via Task Manager. As it’s a MDM policy, it’s not meant for SBC configurations.
Regards, Peter