This week is all about device compliance policies. Well, actually it’s all about what actions can be triggered for non-compliant devices. Since recently it’s possible to configure actions for non-compliance. Previously the action for non-compliant devices was that the device would be marked as non-compliant. That action is still configured by default, but it’s now also possible to configure additional end-user notifications. In this blog post I’ll provide a short introduction to the actions for non-compliant devices, followed by the required configurations. I’ll end this post with the end-user experience.
Introduction
Let’s start with a short introduction. Device compliance policies now contains configuration properties for the configuration of Actions for noncompliance. The Actions for noncompliance allows administrators to configure a time-ordered sequence of actions that are applied to devices that don’t meet the device compliance policy criteria. By default, when a device does not meet the device compliance policy, Intune immediately marks it as non-compliant. The Actions for noncompliance gives administrators more flexibility to decide what to do when a device is non-compliant. There are two types of actions:
- Send email to end user: Administrators can customize an email notification that can be sent to the end-users. Intune provides customization of the subject, message body, company logo, company name and contact information. A schedule can be defined to determine how many days after non-compliance the e-mail notification should be sent;
- Mark device noncompliant: Administrators can define a schedule to determine how many days after non-compliance the device should actually be marked as non-compliant.
This combination enables the IT organization to decide not to block the device immediately. Instead, immediately sent the end-user a notification via e-mail and give the end-user a grace period to become compliant. A good use case for that configuration would be to force end-users to upgrade to the latest version of the platform.
Configuration
Now let’s continue by looking at the configuration. The configuration contains two required steps. The first step is to configure the actual notification and the second step is to configure the device compliance policy to actually use the created notification.
Step 1: Configure notification
The first step is to create the device compliance notification. That notification will contain the message that will be sent to the end-users. To create the notification, follow the next three steps.
| 1 | Open the Azure portal and navigate to Intune > Device compliance > Notifications; |
| 2 | On the Device compliance – Notifications blade, click Create notification to open the Create Notification blade; |
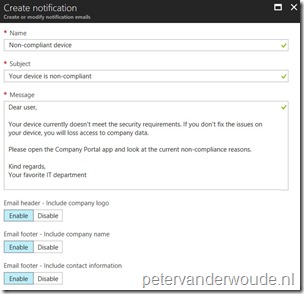
| 3 |
Note: The last three settings use the information as configured with Intune > Mobile apps > Company Portal branding. |
Step 2: Configure device compliance policy
The second step is to configure the actual Actions for noncompliance for a device compliance policy. Let’s do that by looking at an existing device compliance policy. To configure a notification for non-compliant devices, in an existing device compliance policy, follow the next 5 steps.
| 1 | Open the Azure portal and navigate to Intune > Device compliance > Policies; |
| 2 | On the Device compliance – Policies blade, select an existing device compliance policy and click Properties to open the {PolicyName} – Properties blade; |
| 3 | On the {PolicyName} – Properties blade, click Actions for noncompliance to open the Actions blade; |
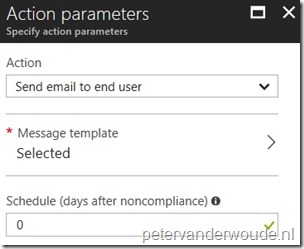
| 4 |
On the Actions blade, click Add to open the Action parameters blade; Note: By default this blade also shows the standard action named Mark device noncompliant. This action can not be deleted, but the schedule when it’s triggered can be configured (in days). |
| 5 |
Note: Make sure that the notification message matches with the configured schedule for marking the device as noncompliant. |
End-user experience
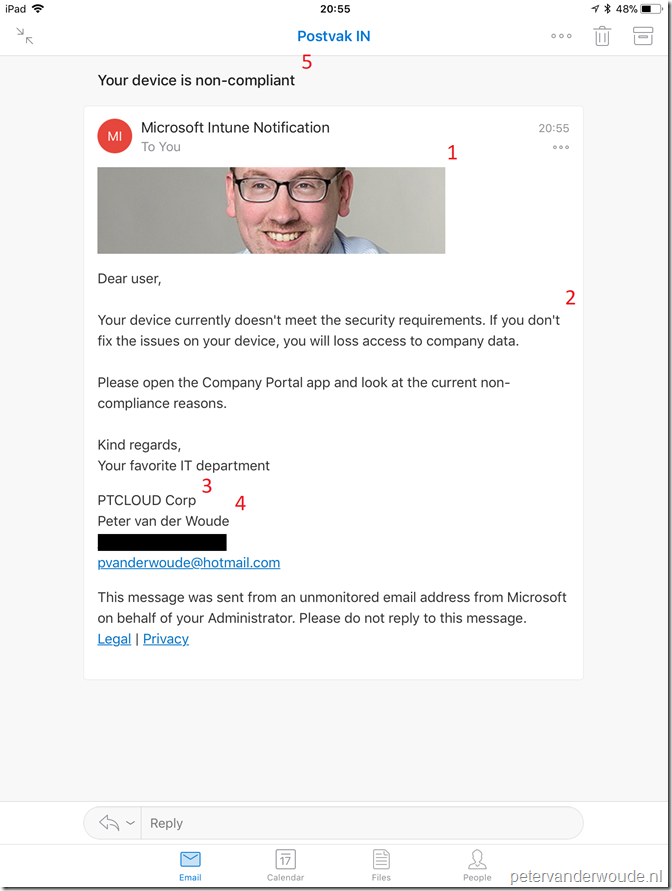
Now let’s end this post by looking at the end-user experience. Below is an example of an non-compliant iOS device and the notification e-mail that was received. The different section of the notification e-mail can be matched with the configuration (step 1.3), by looking at the numbers below.
- Email header – Include company logo;
- Message;
- Email footer – Include company name;
- Email footer – Include contact information;
- Subject.
More information
For more information about notifying end-users about non-compliant devices, please refer to this article Automate actions for noncompliance.
Note: While I was writing this blog post, my colleague Arjan Vroege posted his version about this same subject. For his version, please have a look at this blog post.
Is there also an option for an Admin to send a custom notification to the end user/device?
At this moment you can only sent these custom notification by email.
Hi Peter,
Does a compliance policy only check if a configuration is set, or does it also set the configuration? I mean if we configure a compliance policy with 28 character password does it also set this or do we also need a configuration policy for setting a 28 character password?
Hi Arjan,
It’s a compliance policy, it doesn’t force a user to make adjustments. It does provide users with information about non-compliance, as non-compliance can prevent access to company data.
Peter
Hi Peter,
Under “Step 2: Configure device compliance policy”, you say Note: Make sure that the notification message matches with the configured schedule for marking the device as noncompliant.”
By this you mean, when your device is marked as noncomplaint after 1 day, the mail option also has to be set at 1 day? (so you have 2 compliance rules?)
Best regards,
Leon
Hi Leon,
No. I mean that you’ve got one compliance rule with multiple actions. For example when the device is not compliant the user will immediately recieve an email and the device will be marked noncompliant after a few days.
Regards, Peter
Hi Peter,
Would you know if there are placeholders available like %devicename%, for users which work on multiple devices?
I am currently testing these notifications for corporate owned personal devices and corporate shared devices.
The latter might be confusing as a user will not know which devices were used during the day.
Regards,
Micha
Hi Micha,
Not to my knowledge. See also: https://docs.microsoft.com/en-us/mem/intune/protect/actions-for-noncompliance#create-a-notification-message-template
Regards, Peter
Hello Peter-
Noticed that the compliance notification template is very restrictive and one can’t use specific fonts and can’t remove Microsoft privacy statement either in the footer section. We tried to customize , but our business groups doesn’t approve sending to end users yet as they might think non-complaint message is not coming from legit source. Do you know if one can customize the notification message template, with different fonts/fonts size, customize sender, using 3rd party tool/app or Azure logic app , probably integrate with endpoint manager and send to end users. Let me know if you are aware of other options to send non-compliant device messages to iOS/Android device users
IJ
Hi IJ,
I can imagine that you would use a Logic app that would send a Teams notification.
Regards, Peter
hi
is there anyway to not send the non compliance email to end users but to rather send to a group of users on the service desk ?
Hi Mike,
You at least need to send it to the user and can also add additional recipients.
Regards, Peter
Hello,
how often will user receive the email notification?
Maybe every couple days, for example?
Does it depend on how long computer is online?
Thanks
Hi Djordje,
Every time the device becomes non-compliant.
Regards, Peter
Thanks for the article. I created a device compliance policy and set actions for non-compliance as below:
Mark device noncompliant = 1 days
Send e-mail to end user = 0 days ( immediately)
The device compliance policy shows the policy compliance status for my device as non compliant. However, the device is in grace period since “Mark device noncompliant = 1 days”.
I was expecting an e-mail since it`s supposed to send an e-mail immediately but i haven`t got any mail yet about it. Any thoughts!
Hi Rahul,
Is the device also showing as non-compliant in the devices overview?
Regards, Peter