This week a little bit about role-based administration control (RBAC) in combination with devices, in Microsoft Intune. I specifically want to look at that combination, as the RBAC-model in Microsoft Intune differs in that area from how the RBAC-model works in Configuration Manager. Within Configuration Manager a delegated administrator would be a combination between a security role (that defines the permissions and a security scope (that defines the objects). In that case the security scope is a combination between tagged objects and users and devices in specified collections. Specifically that last section, regarding the collections, is were the RBAC-model differentiates from Microsoft Intune. In this post I want to provide a short introduction to the different pieces of RBAC in Microsoft Intune, followed by how those pieces together impact the devices within Microsoft Intune.
Introduction
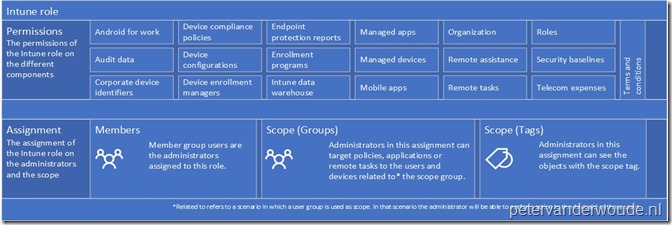
Now let’s start by having a look at RBAC in Microsoft Intune. RBAC helps administrators to control who can perform various Intune tasks within the organization, and who those tasks apply to. Administrators can either use the built-in roles that cover some common Intune scenarios, or create their own roles. Below is an overview of the different components of an Intune role. The permissions and the assignment.
A summary of the overview would be that an Intune role is defined by:
- Permissions: The permissions of the Intune role;
- Assignments: The assignment of the Intune role is the combination of the members, the scope and the scope tags. Those components are used for the following:
- Members: The user groups that are granted the permissions of the Intune role;
- Scope: The user or device groups that the members can manage;
- Scope tag:
The objects that the members can see.
Bringing the pieces together
Previously an often heard comment was that an administrator could delegate permissions to a delegated administrator, but the delegated administrator would still see all the device objects. That has changed with the introduction (and recent modifications) of Scope tags! This is also the point were the RBAC-model differs from that of Configuration Manager. Main reason, within Microsoft Intune it’s required to specifically tag the objects that the delegated administrators can see. Including the devices. That means, using a Scope to determine which users and/or devices the delegated administrator can manage and using Scope tags to determine which devices the delegated administrator can see.
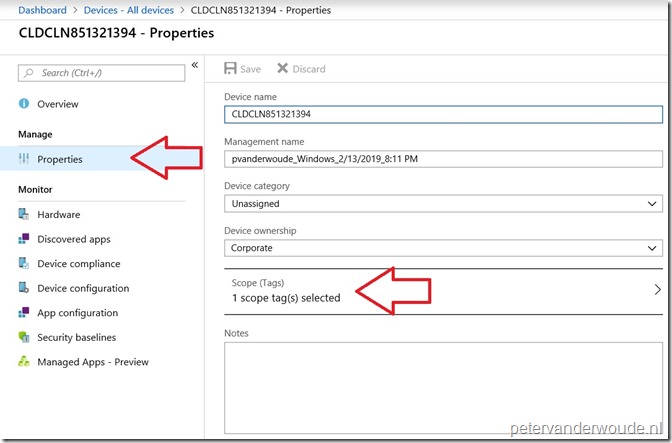
The Scope tag configuration is a little bit hidden and unknown on devices. The configuration can be found by going to the Properties of a device, as shown below.
As the configuration of a Scope tag is currently done per device, it might be smart to look at automating that process. To help with that automation, Microsoft recently provided a PowerShell example for assigning a Scope tag to a device.
More information
For more information regarding to RBAC in Microsoft Intune, please refer to the following articles:
- Role-based administration control (RBAC) with Microsoft Intune: https://docs.microsoft.com/en-us/intune/role-based-access-control
- Use scope tags to filter policies: https://docs.microsoft.com/en-us/intune/scope-tags
Thanks for shining lights on RBAC cause RBAC is often forgotten imo. Nice to have this little break-down.
Thanks, Rkast!
Hi, I just tested it, but it doesn’t work for me, I created an scope tag and assigned it to some user devices and to a Role, but the delegated admin can still see all the devices I have in Intune. Should I wait some time for kind of configurations to take effect.
Regards,
Hi Jean,
The delegated administrator should really only see the tagged devices. It should be applicable almost instant.
Regards, Peter
Hi Peter,
I have been testing this configuration but my delegated administrator can see all the devices that I have in Intune (but they can not manage all of them). I consulted with Anoop C Nair, who has a similar post, https://www.anoopcnair.com/intune-scope-tags-guide/ and he told me that it does’n work for him neither. Should I create a support ticket with Microsoft?
Hi Jean,
I’ve just tested it again and it works fine with me. Just keep in mind that the delegated admin will see all the specifically tagged devices + all devices without a tag.
Regards, Peter
Hi Peter,
You’re right! that was the problem! the delegated admin was seeing all the specifically tagged devices + all devices without a tag.
Thank you very very much!
YMMD
Regards,
Jean Chavez
Great news, Jean!
Hi Peter,
In the MSIntune-RBAC infographic from above you mentioned that a user group can be used as scope. With that the admin can perform action to the devices of those users. I’m currently working on a case, where I’m trying to select all Android devices from a specific country. This can’t be achieved through a dynamic device group, as there are no searchable patterns for these mobiles. The only way to get these devices is a manual match via the device’s primary user setting.
Do I understand you article right, that we can assign a scope (tag) to the country user group and this should also set this scope to the devices with the corresponding primary user? Currently this is not working for us.
Thanks a lot for any reply!
Hi Klaus,
No. You can either assign the scope tag manually (or via script) to each device object, or assign the scope tag to a group that contains the devices.
Regards, Peter