 Last week I started this series with a blog post on How to configure multi-factor authentication in Microsoft Intune – Part 1: The easiest method, this week I’m going to take it up one level and also include single sign-on in the configuration. I will describe the multi-factor authentication configuration, for Microsoft Intune, when using single sign-on. The nice thing is that the multi-factor authentication page, in Microsoft Intune, already describes the configuration. In this post I will walk through that configuration and also show the results of that configuration, as that was a little bit surprising to me.
Last week I started this series with a blog post on How to configure multi-factor authentication in Microsoft Intune – Part 1: The easiest method, this week I’m going to take it up one level and also include single sign-on in the configuration. I will describe the multi-factor authentication configuration, for Microsoft Intune, when using single sign-on. The nice thing is that the multi-factor authentication page, in Microsoft Intune, already describes the configuration. In this post I will walk through that configuration and also show the results of that configuration, as that was a little bit surprising to me.
Scenario
Like last week it’s important to mention a couple of lines about the scenario before I’ll start with this configuration for multi-factor authentication. This specific multi-factor authentication configuration is only possible when the following situations are applicable:
- The Mobile Device Management Authority is set to Microsoft Intune;
- The devices to enroll are all Windows 8.1 (and newer) or Windows Phone 8.1;
- Multi-factor authentication is only required during the device enrollment;
- Single sign-on is used. For a basic single sign-on configuration have a look at the first three parts of this blog series. Keep in mind that Microsoft Intune should not be integrated with ConfigMgr 2012.
Configuration
Now let’s start with the configuration. The configuration is pretty straight forward and divided in two steps. The first step will describe the configuration of an additional authentication method in the on-premises Active Directory Federation Services (AD FS) and the second step will describe, like last week, the configuration in Microsoft Intune. After going through the following two steps multi-factor authentication will be enabled, in a single sign-on configuration, for device enrollment of Windows 8.1 (and newer) and Windows Phone 8.1.
Step 1
 The first step is to select an additional authentication method in the on-premises AD FS. I will do this by using the default certificate authentication option. To configure certificate authentication as an additional authentication method follow the next steps:
The first step is to select an additional authentication method in the on-premises AD FS. I will do this by using the default certificate authentication option. To configure certificate authentication as an additional authentication method follow the next steps:
- Logon to the on-premises federation server and open the AD FS management console;
- Right-click Authentication Policies and select Edit Global Multi-factor Authentication;
- In the Edit Global Authentication Policy window, select Certificate Authentication with Select additional authentication methods and click OK.
Note: It’s important to not configure any additional multi-factor authentication settings. Not in the global authentication policy and not in the Microsoft Office 365 Identity Platform authentication policy. Configuring these settings will cause multi-factor authentication to be triggered for more then just the device enrollment in Microsoft Intune.
Step 2
The second step is to enable multi-factor authentication in Microsoft Intune. To configure multi-factor authentication in Microsoft Intune follow the next steps:
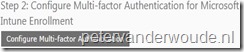 Logon on to the Microsoft Intune administration console;
Logon on to the Microsoft Intune administration console;
- Navigate to Administration > Mobile Device Management > Multi-factor Authentication;
 Select Configure Multi-factor Authentication;
Select Configure Multi-factor Authentication;
- In the Configure Multi-factor Authentication dialog box select Enable Multi-factor Authentication and click OK.
Result
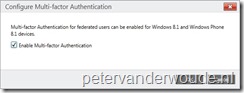
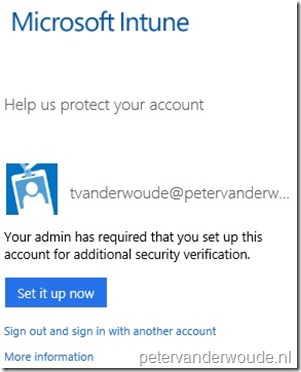
The result of this configuration is as expected, in a way that multi-factor authentication is only required with the enrollment of Windows 8.1 (and newer) and Windows Phone 8.1. The one thing I noticed, and I didn’t really expect, is that multi-factor authentication will be triggered in the on-premises AD FS and in Microsoft Intune. To the end-user the behavior will be as shown in the screenshots below. During the first enrollment the end-user has to select a certificate, for the on-premises multi-factor authentication, and configure multi-factor authentication, for the Microsoft Intune service. During the next enrollments the end-user has to select a certificate, for the on-premises multi-factor authentication, and the configured multi-factor authentication method, for the Microsoft Intune service, will be used automatically.
| First enrollment | Next enrollments |
 |
 |
 |
 |
Further reading
The first three parts of this blog series about how to integrate Microsoft Intune and ConfigMgr with single sign-on can be useful for a initial set up of AD FS. Also, this walkthrough guide about managing risks with additional multi-factor authentication for sensitive applications can be useful for configuring multi-factor authentication. That guide describes, step-by-step, the configuration of the additional authentication methods of certificate authentication and Windows Azure multi-factor authentication.