Let’s start this new year with a short blog post about the Cloud Management Gateway (CMG). More specifically, about replacing an (expired) server authentication certificate on the CMG. The server authentication certificate is a required certificate for the CMG. That certificate is used to build the secure channel that is used with the created HTTPS service. The HTTPS service is were the internet-based clients connect. This certificate should come from a public provider, or from a public key infrastructure (PKI). In this post I’ll have a quick look at how to prevent the expiration of the server authentication certificate and how to replace the server authentication certificate.
Certificate expiration
The most important thing to note is – like with everything else – that prevention is better than cure. In this case: make sure that the certificate is replaced before it expires. Of course it still happens that – for whatever reason – the certificate is forgotten. In that case the Configuration Manager site will keep on working, but the clients that are managed over the Internet via the CMG, will loose their connection with the Configuration Manager site. The clients will show behavior in the CcmMessaging log that includes the messages shown below.

CcmMessaging log snippet
It includes the messages WINHTTP_CALLBACK_STATUS_SECURE_FAILURE and WINHTTP_CALLBACK_STATUS_FLAG_CERT_DATE_INVALID, which both imply that something is wrong with the server certificate (see also the docs for some more details).
As mentioned, prevention is better than cure. At this moment Configuration Manager will not provide any alerts about the expiration of the CMG server authentication certificate. That doesn’t mean that there are no methods available for verifying the expiration of the certificate. When working with a solid third-party certificate provider, warnings will arrive months, weeks and days ahead of the expiration date. Ignoring those messages is nearly impossible (unless managed by a different team). When not willing to rely on a third-party, looking in the Azure portal is a very good alternative. Navigate to the cloud service of the CMG and select Certificates. That section will provide an overview of the certificates that belong to the cloud service. An example is shown below.
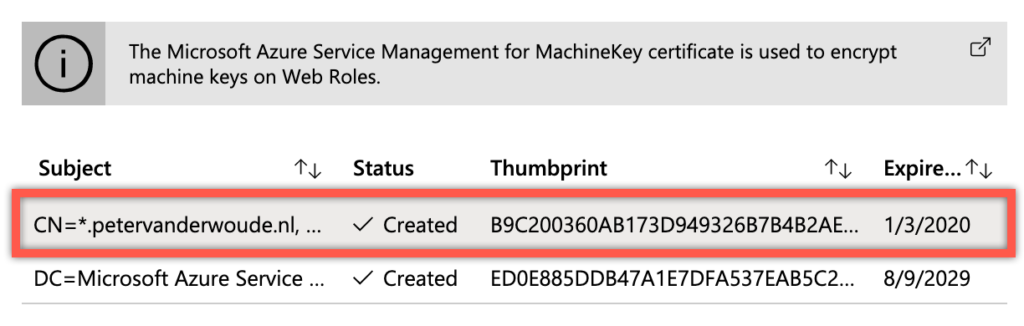
Cloud service certificates
Of course this can also be automated by looking at PowerShell and/or the Azure Management API. That API contains the certificate URI for a resource group, which can be used for automation purposes.
Replace the certificate
The actual replacement of the (expired) CMG server authentication certificate should be pretty straight forward and can be achieved by following the next three steps.
- Open the Microsoft Endpoint Configuration Manager administration console and navigate to Administration > Overview > Cloud Services > Cloud Management Gateway
- Select {YourCMG} and click Properties in the Home tab to open the {YourCMG} Properties dialog box
- In the {YourCMG} Properties dialog box, navigate to the Settings tab, browse to (and select) the new certificate and click OK
Note: In my case I noticed that it wasn’t as straight forward as I thought. The deployment in Azure would fail with the message that the certificate with the new thumbprint was not found. I could address this challenge by manually uploading the certificate with the cloud service in Azure and again performing the mentioned steps. Performing those steps again will make sure that the correct actions are performed with the new certificate.
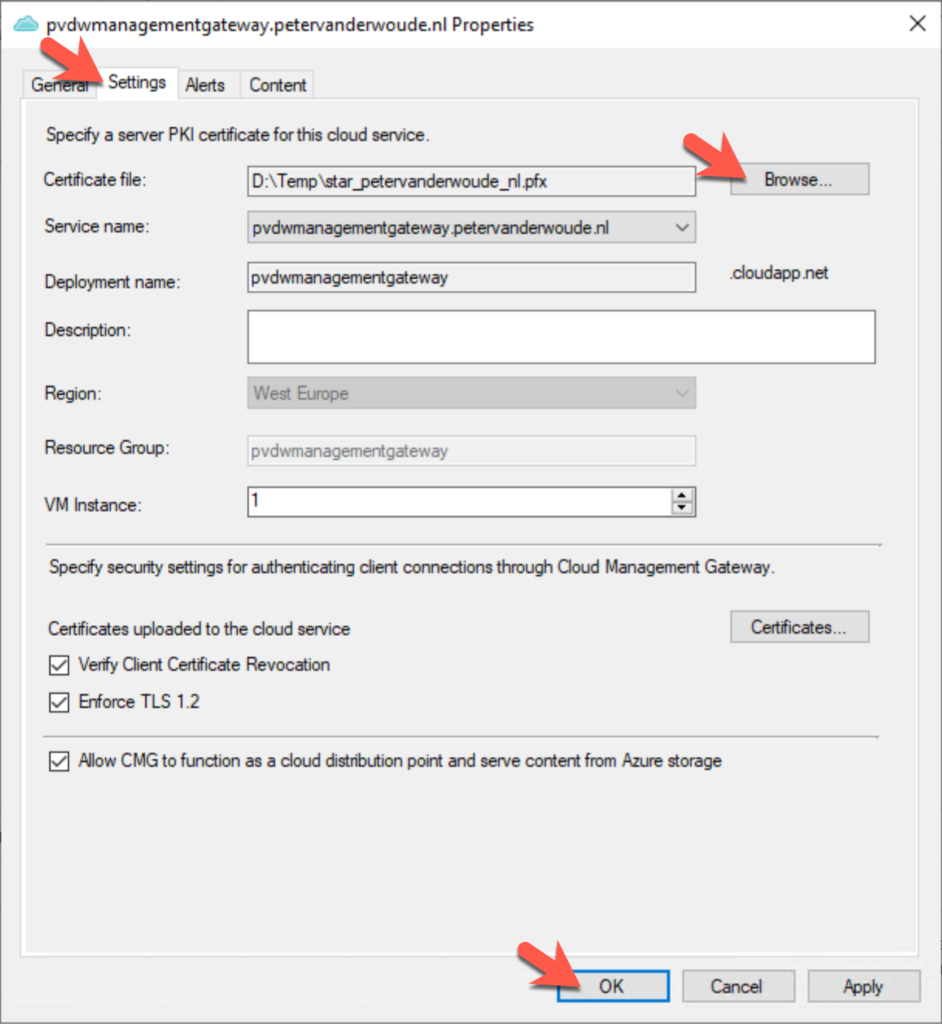
Cloud management gateway properties
After a successful deployment of the cloud service the, earlier mentioned, Certificates section of the cloud services will show the new certificate and, in my case, show the old and expired certificate.
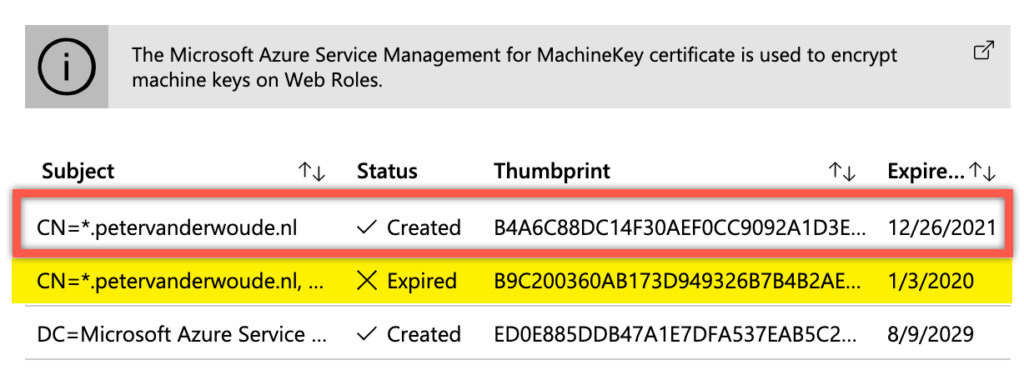
Cloud service certificates (new and old)
Also, it’s good to know that when the CMG server authentication certificate was actually expired, the clients will automatically start communicating again once the certificate is replaced.
More information
For more information about the certificates for the CMG, please refer to the documentation Certificates for the cloud management gateway.
Hi Peter, total different question are you going to do a write up about switching from co-mgmt (old style) certificate based to the (new style) azure ad device auth ? Or do you have any info on this ?
Hi Rkast,
Are you referring to the authentication via CMG, or something else?
Regards, Peter
Hi Peter,
Yes I mean azure ad client auth and enhanced http that was introduced in 1806. So a transition from pki to enhanced http.
Hi Rkast,
What are the problems that you’re running into?
Regards, Peter
Hi Peter,
Not really a problem But just curious how to switch to cmg auth. Is it just enabling enhanced http for example and maybe a new configmgr client?
Regards,
Hi RKast,
You should see – on an Azure AD joined device – a log ADALOperationProvider that already provides information about the token.
Regards, Peter
So I uploaded the new cert to Azure with no issues. But when I try and add the cert in Config Manager CMG > Settings > Certificate File
It keeps telling me the password is incorrect, when I know it is correct. I literally just put the password on it, and Azure accepted it with no issues. Any thoughts?
Hi Matthew,
Is that also the error that you’re seeing in the logs?
Regards, Peter
Do you have a method for monitoring when the certs/secret expires so you proactively can fix it?
Hi Mathias,
I don’t have anything myself, but I can imagine that it shouldn’t be to difficult to create a script that verifies the date.
Regards, Peter
Great post Peter, thanks! Here’s a simple trick I use to get alerts on my cert expiration. CM does have alerting on the expiration of Secret Keys for Azure Cloud services. I’m not sure when this feature was added in CM, but my SK for the CMG server service recently approached it’s expiration from our initial CMG deployment two years ago triggering an alert in my CM console. The trick is to simply make sure that your certificate and Secret Key expiration dates line up. Then the SK alert also acts as an alert for your certificate.
Thank you for the tip Al.
Regards, Peter
Hello,
I have the certificates expired in Test and Production:
VITSCCMCB
The Service certificate was invalid for cloud service CMGO365QA. Please check CloudMgr.log for further details.
ERROR: Management certificate for service CMGO365QA is in expired state. Expiry date-time(UTC):11/13/2022 09:19:43 SMS_CLOUD_SERVICES_MANAGER 6/30/2023 10:42:06 AM 9020 (0x233C)
ERROR: Service Certificate is expired for Service CMGO365QA. SMS_CLOUD_SERVICES_MANAGER 6/30/2023 10:42:06 AM 9020 (0x233C)
VRPSCCMPR01
The Service certificate was invalid for cloud service CMGO365PROD. Please check CloudMgr.log for further details.
ERROR: Management certificate for service CMGO365PROD is in expired state. Expiry date-time(UTC):06/11/2023 13:55:47 SMS_CLOUD_SERVICES_MANAGER 6/30/2023 10:52:04 AM 8824 (0x2278)
ERROR: Service Certificate is expired for Service CMGO365PROD. SMS_CLOUD_SERVICES_MANAGER 6/30/2023 10:52:04 AM 8824 (0x2278)
But apparently no complain from anybody… what should be the behavior when the certificate is expired?
Also I noticed in Test I have 1 certificate
CN = CMGO365QA.Cloudapp.net
but in Production I have two:
CN = CMGO365PROD.Cloudapp.net
and
CN = cmgo365prod.westus.cloudapp.azure.com
Why this difference?
Thanks,
Dom
Hi Dom,
The cert is used for the HTTPS service to which Internet clients connect (see: https://learn.microsoft.com/en-us/mem/configmgr/core/clients/manage/cmg/server-auth-cert). The CN is what you configured as the service name(s).
Regards, Peter
Hey Peter, Do you have any instructions for uploading the certificate to the azure service like you mention in your note? I think this was the issue i had last year and Microsoft ended up suggesting rebuilding my entire CMG from scratch. I am replacing the cert again today and would like to avoid that if this issue occurs again..
Hi Sean,
In my case I could manually upload the certificate.
Regards, Peter