This week back in conditional access. More specifically, the recently introduced feature to assign a conditional access policy to All guest users, which is currently still in preview. At the same time also the ability to assign to Directory roles was introduced. The idea for both is the same. The first is to specifically assign to guest users and the second is to assign to specific roles in the directory. This post will focus on the first scenario. I’ll show the very simply and straight forward configuration, followed by the end-user experience.
Configuration
Microsoft Teams is getting really hot for collaboration. This also creates a very low bar for inviting external parties (B2B) to collaborate with. Working together. Of course this should be facilitated to enable the productivity of the end-user. However, that doesn’t mean that there shouldn’t be additional security in-place. Even if it’s just to ensure the identity of the guest user. For example, enable multi-factor authentication for guest users. The following steps walk through the simple configuration to enable multi-factor authentication for guest users on Microsoft Teams.
| 1 | Open the Azure portal and navigate to Intune > Conditional access > Policies or to Azure Active Directory > Conditional access > Policies; |
| 2 | On the Policies blade, click New policy to open the New blade; |
| 3 | 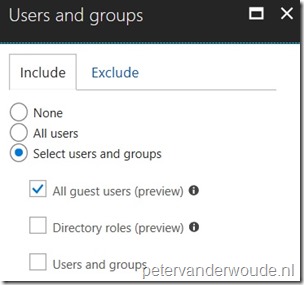 On the New blade, select the Users and groups assignment to open the Users and groups blade. On the Users and groups blade, select Select users and groups > All guest users (preview) and click Done; On the New blade, select the Users and groups assignment to open the Users and groups blade. On the Users and groups blade, select Select users and groups > All guest users (preview) and click Done; |
| 4 | 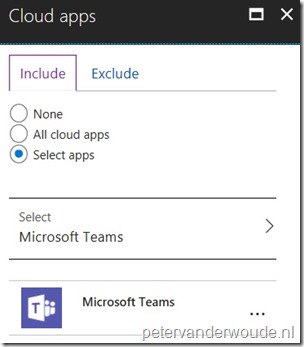 On the New blade, select the Cloud apps assignment to open the Cloud apps blade. On the Cloud apps blade, select Select apps > Microsoft Teams and click Done; On the New blade, select the Cloud apps assignment to open the Cloud apps blade. On the Cloud apps blade, select Select apps > Microsoft Teams and click Done; |
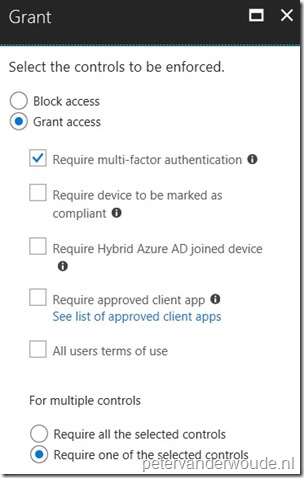
| 5 |
|
| 6 | Open the New blade, select On with Enable policy and click Create; |
Note: Guest user matches any user account with the userType attribute set to guest.
End-user experience
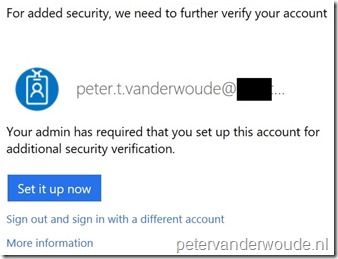
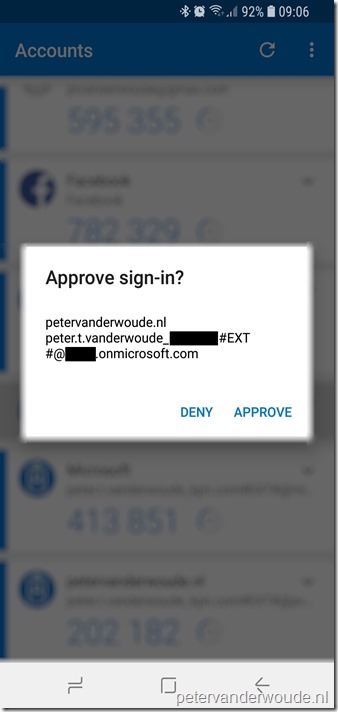
Now let’s end this post by looking at the end-user experience. Once the (external) user is invited for using Microsoft Teams, it will first have to configure MFA (see screenshot on the left). After that the user will be able to access Microsoft Teams by using its favorite MFA option. In my example I picked the Microsoft Authenticator app, as it will clearly show that an external account was used (see screenshot on the right). It clearly shows #EXT and onmicrosoft.com.
 |
 |
More information
For more information about conditional access and assignments, please refer to this article about Conditions in Azure Active Directory conditional access | Users and groups.
Hi Peter,
Thanks for a great post, i have one question: Do we need to assign a Azure Multi-Factor Authentication liceses for all our guests users in order for this to work?
BR,
Nicklas
Hi Nicklas,
No. The licensing is automatically calculated and reported, based on a 5:1 ratio. For every user (license) an organization can invite 5 guest users.
For a lot more information, see: https://docs.microsoft.com/en-us/azure/active-directory/active-directory-b2b-licensing
Regards, Peter
I did not know that, thanks a lot!
BR,
Nicklas
We have this setup, one thing to have in mind. If you using AIP for e-mails, external users might have problem. Add AIP in the excluded list of apps so it does not being blocked by this policy for external reciptens.
You’re absolutely correct, Dan! When using AIP, you should add that exclusion to make it work..
Regards, Peter