Easier configuring additional LSA protection
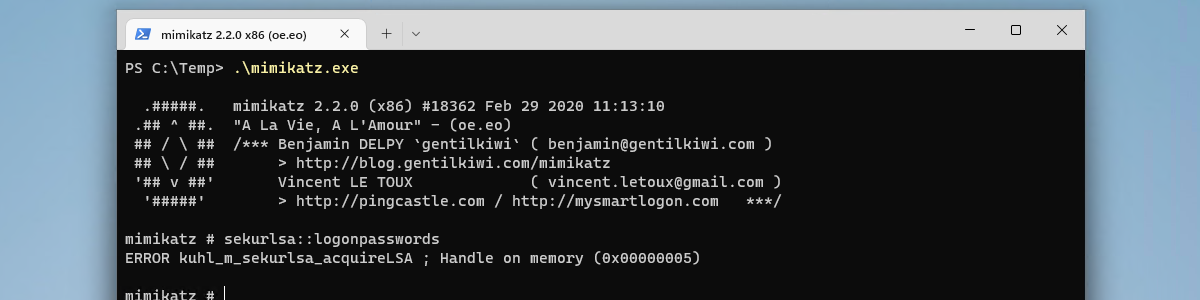
This week another short blog post about another nice configuration addition to Windows. This time it’s about configuring additional Local Security Authority (LSA) protection for credentials. LSA, which includes the Local Security Authority Server Service (LSASS) process, validates users for local and remote sign-ins and enforces local security policies. Starting with Windows 8.1 and later, additional protection is provided for the LSA, to prevent reading memory and code injection by non-protected processes. That provides added security for the credentials that LSA stores and manages. Not really something new, but it’s good to know that something has changed from a configuration perspective. The protected process setting for LSA can also be configured in Windows 8.1 and later. That would, however, always require the manual creation of a …