This week I want to devote a post to something new in ConfigMgr 2012 R2, which is still in a preview state, called Certificate Profiles. These profiles integrate directly with Active Directory Certificate Services (ADCS), and the Network Device Enrollment Service (NDES) role, to provision managed devices with authentication certificates. This means that another Group Policy setting is coming to ConfigMgr AND, maybe even bigger, this creates a possibility to automatically deploy certificates to non-domain devices.
Prerequisites
Even though this sounds, to me, really promising for the future of ConfigMgr, there is a small catch. That small catch is the third bullet of the prerequisites, following now:
- Configuration Manager 2012 Service Pack 1 R2
- Install and configure the Certificate Registration Point (which requires the NDES for ADCS). For a great installation guide see: http://technet.microsoft.com/en-us/library/dn270539.aspx
- Note: The Certificate Registration Point doesn’t have to be installed on the NDES server.
- Windows (RT) 8.1, iOS or Android clients
Part 1 – Root Certificate
When all the prerequisites are met, let’s start with configuring. The deployment of Certificate Profiles always consist out of two parts, deploying a root certificate followed by deploying a client certificate. So lets start with the first part, the configuration and deployment of a Certificate Profile for the root certificate:
 In the Configuration Manager Console navigate to Assets and Compliance > Overview > Compliance Settings > Company Resource Access > Certificate Profiles.
In the Configuration Manager Console navigate to Assets and Compliance > Overview > Compliance Settings > Company Resource Access > Certificate Profiles.
- On the Home tab, in the Create group, click Create Certificate Profile and the Create Certificate Profile Wizard will popup.
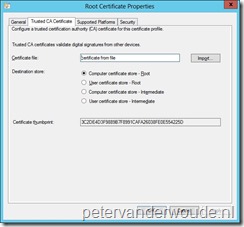
- On the General page, fill in with Name <aCPName>, select Trusted CA certificate and click Next.
- On the Trusted CA Certificate page, browse (by clicking on Import) to the exported root certificate, select Computer certificate store – Root and click Next.
- On the Supported Platforms page, select Windows 8.1 Preview and click Next.
- Note: All the other supported platforms are iPhone/ iPod/ iPad 5 and 6 and all Android devices.
- On the Summary page click Next.
- On the Completion page click Close.
Now the configuration is created it’s time for the deployment. An important step of this deployment is the remediation. So to deploy and remediate the Certificate Profile follow the next steps:
- In the Configuration Manager Console navigate to Assets and Compliance > Overview > Compliance Settings > Company Resource Access > Certificate Profiles.
- Select the new item <aCPName> and on the Home tab, in the Deployment group, click Deploy and the Deploy Trusted CA Certificate Profile popup will show.
- On the Deploy Trusted CA Certificate Profile popup, browse to a device collection, select Remediate noncompliant rules when supported and click Ok.
Part 2 – Client Certificate
After the Certificate Profile for the root certificate is deployed, it’s time to start with the configuration and deployment of a Certificate Profile for the client certificate. It’s important to note that a root certificate has to be deployed to enable a successful client certificate deployment. Also a Certificate Profile for the deployment of the root certificate is a prerequisite for a Certificate Profile for the deployment of a client certificate:
 In the Configuration Manager Console navigate to Assets and Compliance > Overview > Compliance Settings > Company Resource Access > Certificate Profiles.
In the Configuration Manager Console navigate to Assets and Compliance > Overview > Compliance Settings > Company Resource Access > Certificate Profiles.
- On the Home tab, in the Create group, click Create Certificate Profile and the Create Certificate Profile Wizard will popup.
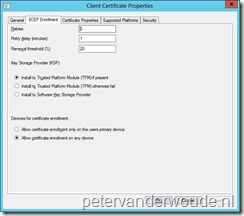
- On the General page, fill in with Name <aCPName>, select Simple Certificate Enrollment Protocol (SCEP) settings and click Next.
- On the SCEP Enrollment page, select Install to Trusted Platform (TPM) if present, then select Allow certificate enrollment on any device and click Next.
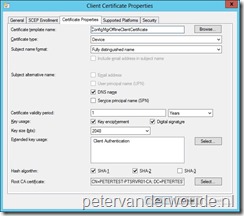 On the Certificate Properties page select with Certificate template name <aCertificateTemplate>, select with Root CA certificate the previously created Certificate Profile and click Next.
On the Certificate Properties page select with Certificate template name <aCertificateTemplate>, select with Root CA certificate the previously created Certificate Profile and click Next.
- Note: All the other settings will be filled automatically, but are customizable, based on the selected template, but Read rights on the selected template are necessary for the user. Also the selected template has to be configured on the Network Device Enrollment Service server, in the following key: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\MSCEP.
- On the Supported Platforms page, select Windows 8.1 Preview and click Next.
- Note: All the other supported platforms are iPhone/ iPod/ iPad 5 and 6 and all Android devices.
- On the Summary page click Next.
- On the Completion page click Close.
Now the configuration is created it’s again time for the deployment. And again an important step of this deployment is the remediation. So to deploy and remediate the Certificate Profile follow the next steps:
- In the Configuration Manager Console navigate to Assets and Compliance > Overview > Compliance Settings > Company Resource Access > Certificate Profiles.
- Select the new item <aCPName> and on the Home tab, in the Deployment group, click Deploy and the Deploy Trusted CA Certificate Profile popup will show.
- On the Deploy Trusted CA Certificate Profile popup, browse to a device collection, select Remediate noncompliant rules when supported and click Ok.
Result
These Certificate Profiles are handled via the Compliance Settings (see the standard compliancy log files). As soon as a device is non-compliant, AND Remediate noncompliant rules when supported is configured, the CCM Certificate Enrollment Agent will kick in. The Enrollment Agent will then communicate directly with NDES to do a certificate request via the Simple Certificate Enrollment Protocol (SCEP). The success and/ or failures of this process can be followed in a new log file named CertEnrollAgent.log. This log file will show information like this snippet of a successful enrolment on my workgroup device: 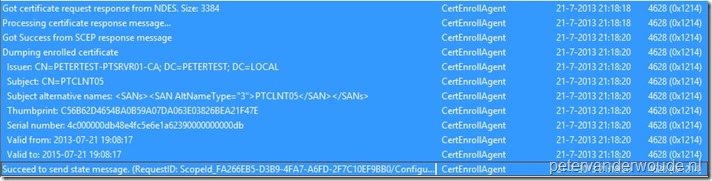
Another good place to look is a MMC with the Certificates snap-in, on the enrolled device. This will immediately show whether, or not the the Certificate Profile provided a successful enrollment of the a certificate: 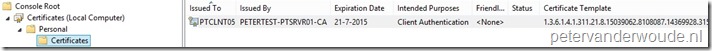
The last good place to check, that I want to show, is the Certification Authority. A successful request should be visible with the Issued Certificates. This request will show as requester the service account of NDES:
Could you use this for a Mac client cert? We do not, and problematically cannot (security reasons), have a CA in our enviroment. This basically illuminates our ability to manage Macs, which we want to do.
Hi,
It does work with iOS, BUT for this solution you still need a CA for the certificate requests.
Peter
Hi Peter,
Great article first of all, very informative!
I am currently working on the combination of SCCM 2012 R2 and Intune.
Do you know if SCEP certificate requesting is supported for that as well? And if so, if the SCEP- or SCCM-server (or both) should be published to the internet?
Thanks!
It’s definitely supported! For the devices that are enrolled by Windows Intune, this requires the Network Device Enrollment Service to be accessible from the Internet. See for more information: http://technet.microsoft.com/en-us/library/dn248971.aspx
Hi Peter thanks for this article. Quick question when deploying the CP to devices should this be an available or required deployment? Or does it matter?
Thanks
Hi Rasheedah,
A Certificate Profile is similar to a configuration baseline. That means there is no required or available type of deployment. You specify how often it should be checked (and remediated).
Peter
Hi Peter!
I have a question, how deploy JUST app approve from app store for apple devices?. The bussines approve some app not all. I apply policies and can close access to App Store but some app required conect the site.
Please Help!
Hi Erick,
At this moment you can only have compliant and non-compliant apps on iOS. For a lot more information see: https://technet.microsoft.com/en-US/library/dn818906.aspx?f=255&MSPPError=-2147217396
Peter
hi, on my SCEP options (SCCM v1606) the certificate template name is blank with no options at all HELP!
Make sure that you have at least read permissions to the template.
Hi Peter
I read your post and its really good.
I have a question. DO YOU how to delete Blocked CA from Sccm config manager. I could not find any information.
Please help me.
Rume.
Hi Rume,
Which CA cert are you referring to?
Regards, Peter