Configuring the default credential provider
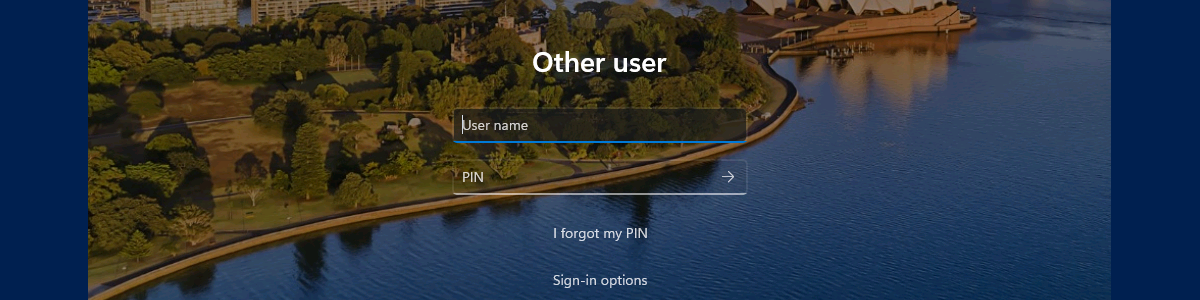
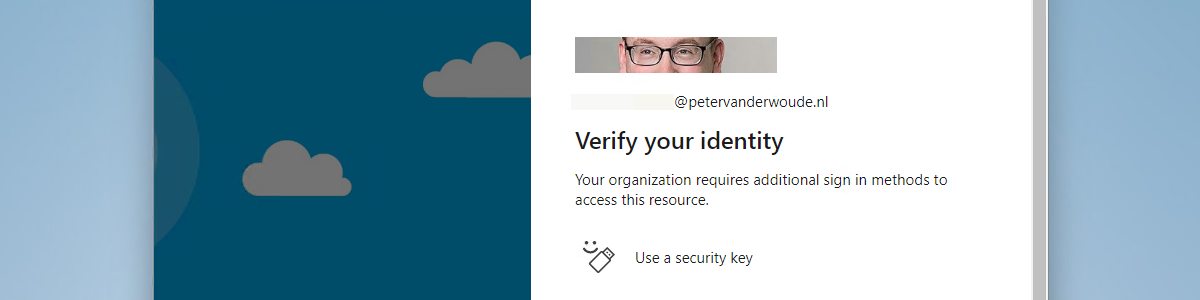
This week is a short post about configuring the default credential provider and this is basically a small addition to the blog posts of about two years ago around configuring credential providers. That time the focus was around actually making it impossible to use specific credential providers. This time the focus is around configuring the default credential provider. That can be a powerful combination, but that can also be a step in the direction of guiding users away from using username-password. So, guiding users instead of forcing users. From a technical perspective that could make it a bit easier, as it doesn’t involve removing functionalities. In this case, it simply provides the configured credential provider as the default credential provider. That default credential provider will …