In this blog post I would like to write a little about, what I like to call, the three layers of protection with conditional access for Exchange email. No, I don’t mean that a device has to be 1) enrolled in Microsoft Intune, 2) workplace joined and 3) compliant with any Microsoft Intune compliance policies. What I do mean is related to company data, in this case company email, and the protection of it on mobile devices. That means three different layers of protection for Exchange email on mobile devices. From basic protection to almost complete protection.
The first layer of protection
 The first, basic, layer of protection is simply using an Exchange Online Policy, or an Exchange On-premises Policy. These policies make it possible to protect Exchange email by blocking the access, via ActiveSync, to Exchange. It, of course, doesn’t block connections via OWA.
The first, basic, layer of protection is simply using an Exchange Online Policy, or an Exchange On-premises Policy. These policies make it possible to protect Exchange email by blocking the access, via ActiveSync, to Exchange. It, of course, doesn’t block connections via OWA.
By enabling these policies, a mobile device, of an user that’s in a Targeted Group and not in an Exempted Group, will be blocked from ActiveSync when it’s not enrolled in Microsoft Intune, and/or not compliant with any targeted Microsoft Intune compliance policies. When no compliance policy is targeted, the device will automatically be evaluated as compliant. Also, not supported and exempted platforms can be blocked access through these policies.
I like to call this the first layer of protection, as it provides very basic protection, to the Exchange email, on the mobile device, by simply making sure that the mobile device is enrolled in Microsoft Intune. That enrollment makes sure that the connected mobile devices are known by the IT organization.
The second layer of protection
 The second layer of protection is adding a few requirements, by using a Conditional Access Policy. A Conditional Access Policy can be used to add additional requirements to the mobile devices that want to connect to Exchange email, via ActiveSync.
The second layer of protection is adding a few requirements, by using a Conditional Access Policy. A Conditional Access Policy can be used to add additional requirements to the mobile devices that want to connect to Exchange email, via ActiveSync.
These policies can be used to specify additional requirements to the password and encryption of the mobile device. Besides that it’s possible to, in case of iOS, block jailbroken mobile devices and, in case of Android, rooted mobile devices.
I like to call this the second layer of protection, as it already adds another form of protection, to the Exchange email, on the mobile device, by requiring additional configurations to mobile devices.
The third layer of protection
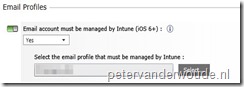 The third layer of protection is adding another, very important, requirement, by using a Conditional Access Policy in combination with an Email Profile.
The third layer of protection is adding another, very important, requirement, by using a Conditional Access Policy in combination with an Email Profile.
This is basically nothing more than an additional configuration in the Conditional Access Policy, but it adds a lot more. It requires that the mobile device (currently only iOS) can only connect to Exchange email, via ActiveSync, when it’s using a specific Email Profile that’s configured via Microsoft Intune.
I like to call this the third layer of protection, as it adds almost complete protection to the company email that’s available on the mobile device. As the mobile device can only connect via an Email Profile, configured via Microsoft Intune, the company email will also be removed when the device is removed from Microsoft Intune.
Conclusion
These three layers of protection together make a very powerful combination for protecting company email. Especially by adding the third layer, it ensures that the available company email will also be removed again.
A good thing to know is that the (managed) Microsoft Outlook app can also still connect to Exchange email, via ActiveSync, as long as the mobile device is enrolled and compliant. More about this in my next blog post.
Note: Even though this post only shows Microsoft Intune standalone screenshots, the same is applicable to Microsoft Intune hybrid.
More information
For a lot more information about conditional access and compliance policies, please refer to the following links.
- Manage email access with Microsoft Intune: https://technet.microsoft.com/en-us/dn705841
- Manage device compliance policies for Microsoft Intune:
- https://technet.microsoft.com/en-us/dn705843
- Conditional Access for Exchange Email in Configuration Manager: https://technet.microsoft.com/en-us/library/mt131421.aspx
- Compliance Policies in Configuration Manager: https://technet.microsoft.com/en-us/library/mt131417.aspx
1 thought on “The three layers of protection with conditional access for Exchange email”