This week is all about a recently introduced feature that will help organizations with their move away from Android device administrator managed devices to Android Enterprise work profile management. That is a very welcome feature as Google is decreasing device administrator support in new Android releases, which makes difficult for Microsoft Intune (and any other MDM-solution) to adequately manage Android device administrator managed devices starting with Android 10. The feature in Microsoft Intune that will help with moving away from Android device administrator managed devices is a compliance setting that will enable organizations to block devices in a structured manner and to provide a direct migration path to Android Enterprise work profile management.
In this post I’ll show how to create and configure a device compliancy policy that will slowly trigger end-users to start the migration to Android Enterprise work profile management, followed by the steps to block the enrollment of Android device administrator managed devices. Together that should help organizations to fully move away from Android device administrator managed devices. I’ll end this post by having a look at the end-user experience.
Configuring the device compliance policy
The first step is preparing a good migration experience, from Android device administrator managed devices to Android Enterprise work profile management, for the end-users. That can be achieved by creating a device compliance policy that eventually will block Android device administrator managed devices. To make sure that the end-user is not immediately being blocked from accessing company resources, I advise to use at least two levels of noncompliance. The first level would be that the end-user receives an email message with the advise to start the migration and the second level would be to actually block access to company resources. That can be after a longer period of noncompliance. The following seven steps walk through the steps for configuring a device compliance policy and provide some guidance for the different configurations. After the creation of the device compliance policy, assign the policy like any other policy.
- Open the Microsoft Endpoint Manager admin center portal and navigate to Devices > Android > Compliance policies to open the Android | Compliance policies blade
- On the Android | Compliance policies blade, click Create Policy to open the Create Policy blade
- On the Create Policy blade, provide the following information and click Create
- Name: Provide a valid name for the device compliance policy
- Description: (Optional) Provide a description for the device compliance policy
- Platform: Select Android device administrator
- Settings: See step 4 and 5
- Locations: Leave default (for this post)
- Actions for noncompliance: See step 6
- Scope (Tags): Leave default (for this post)
- On the Android compliance policy blade, select Device Health to open the Device Health blade
- On the Device Health blade, select Block with Devices managed with device administrator and click OK to return to the Android compliance policy blade and click OK to return to the Create Policy blade
- On the Create Policy blade, select Actions for noncompliance to open the Actions blade
- On the Actions blade, add an action to first notify the user via email and make sure to adjust the default action to not mark a device as noncompliant immediately. That will provide the end-user with time to perform the migration before completely being blocked.
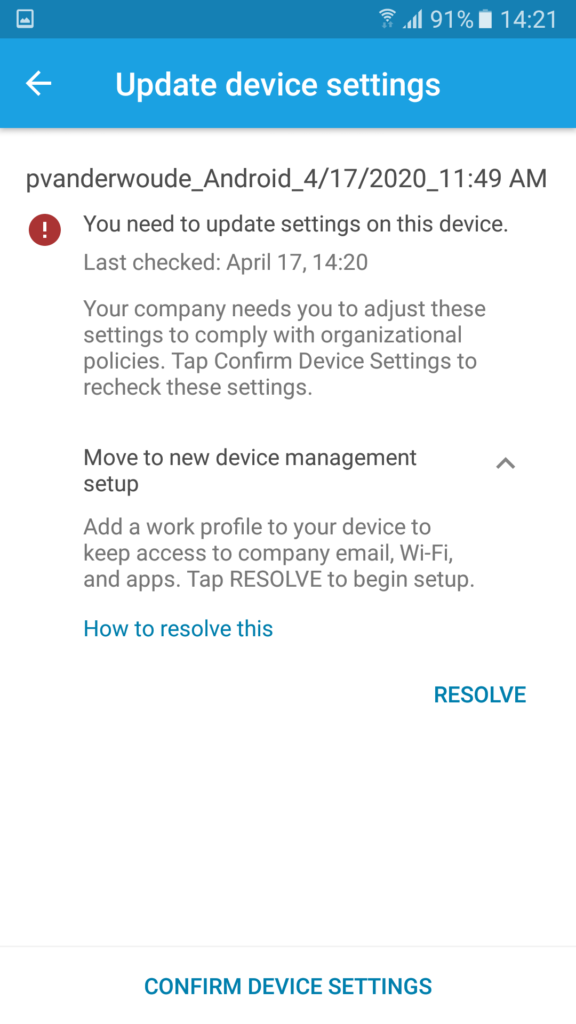
Note: The url https://portal.manage.microsoft.com/UpdateSettings.aspx can be used in the email message to launch the Company Portal app directly in the Update device settings page.
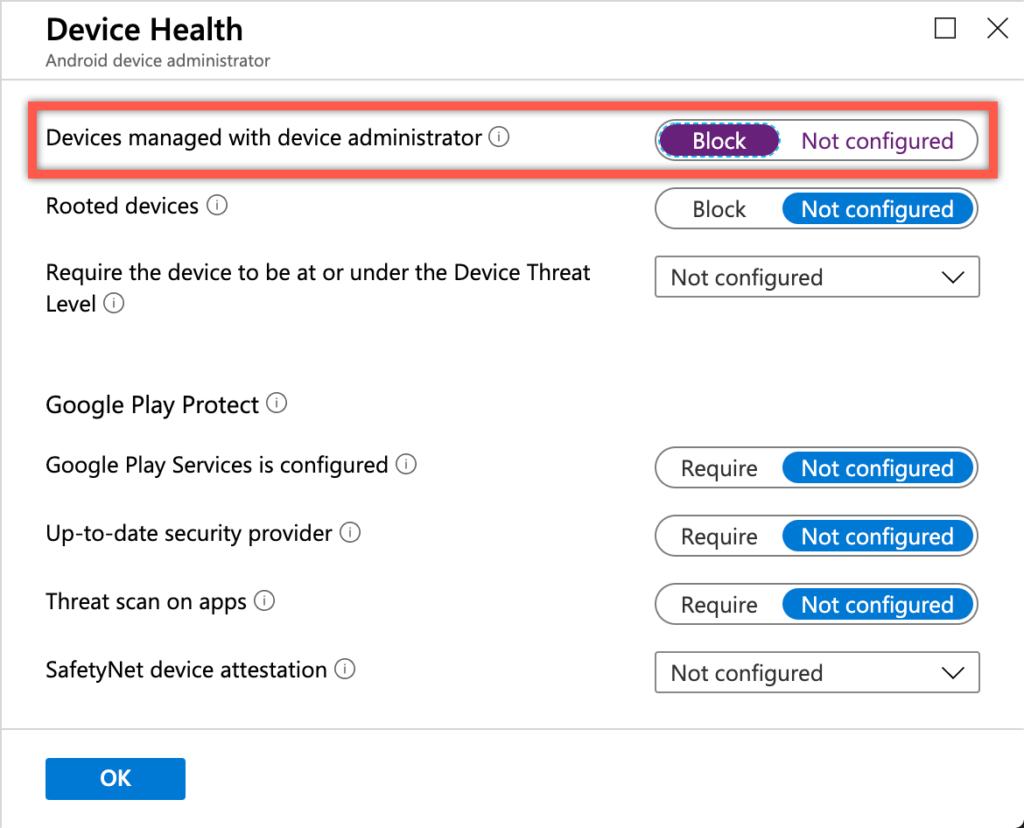
Figure 1: Device compliance
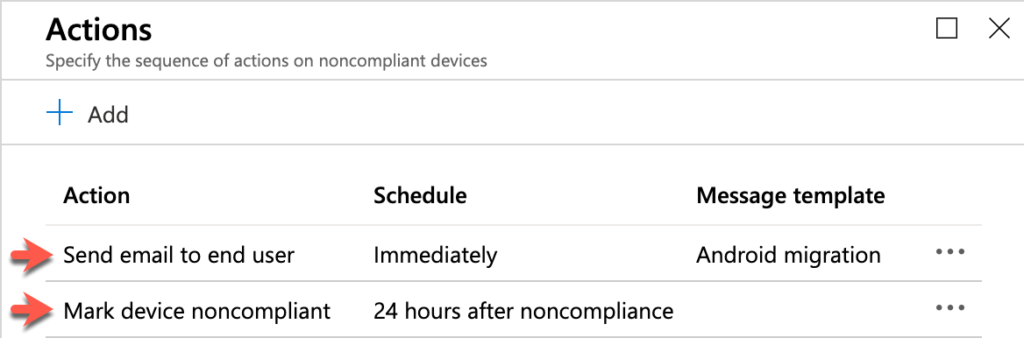
Figure 2: Device compliance actions
For automation purposes, automating the device compliance policy configuration can be achieved by using the deviceCompliancePolicies object in the Graph API.
https://graph.microsoft.com/beta/deviceManagement/deviceCompliancePoliciesConfiguring the device enrollment restrictions
The second step is making sure that new Android device administrator managed devices can no longer be enrolled into Microsoft Intune. That can be achieved by using device enrollment restrictions. The device enrollment restrictions can be used for blocking the enrollment of Android device administrator devices. The following five steps walk through the adjustment of the default enrollment restrictions. Something similar, and often more flexible, can be achieved by using custom enrollment restrictions.
- Open the Microsoft Endpoint Manager admin center portal and navigate to Devices > Enroll devices > Enrollment restrictions to open the Enroll devices | Enrollment restrictions blade
- On the Enroll devices | Enrollment restrictions blade, select the Default device type restriction and navigate to Properties to open the All Users | Properties blade
- On the All Users | Properties blade, navigate to the Platform settings section and click Edit to open the Platform settings page on the Edit restriction blade
- On the Platform settings page, select Block with Android device administrator (see example below) and click Review + save to continue to the Review + save page
- On the Review + save page, click Save
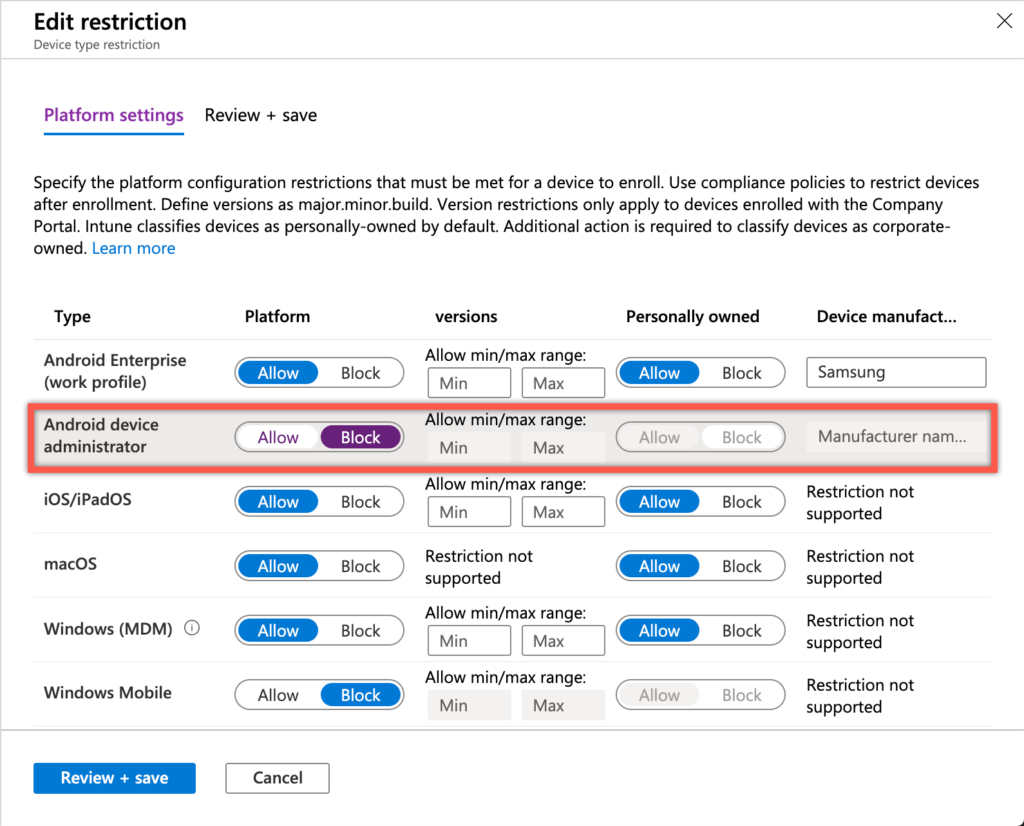
Figure 3: Device enrollment restrictions
For automation purposes, automating the device type restriction configuration can be achieved by using the deviceEnrollmentConfigurations object in the Graph API.
https://graph.microsoft.com/beta/deviceManagement/deviceEnrollmentConfigurationsEnd-user experience
Now let’s end this post by having a look at the end-user experience, which is the most important part of everything in this post. The end-user experience determines whether this migration process will be adopted by the end-user and whether this migration process is intuitive enough to walk the end-user through this migration process. My personal experience, after performing multiple of these migrations, is very positive. It catches problems and brings the end-user back to the progress in the Company Portal app. Even on an older device, which wasn’t encrypted, I eventually ended up in the Company Portal app.
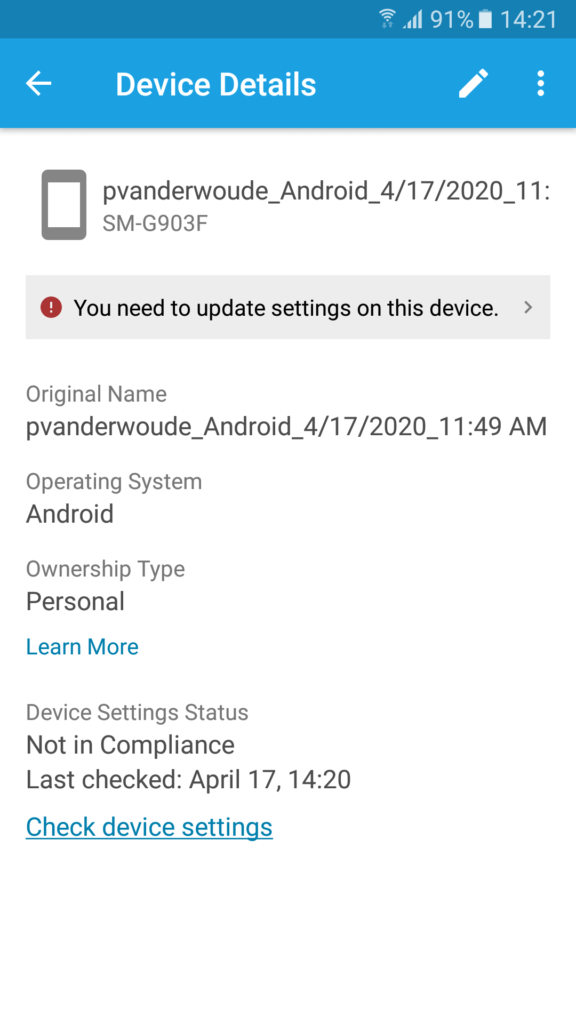
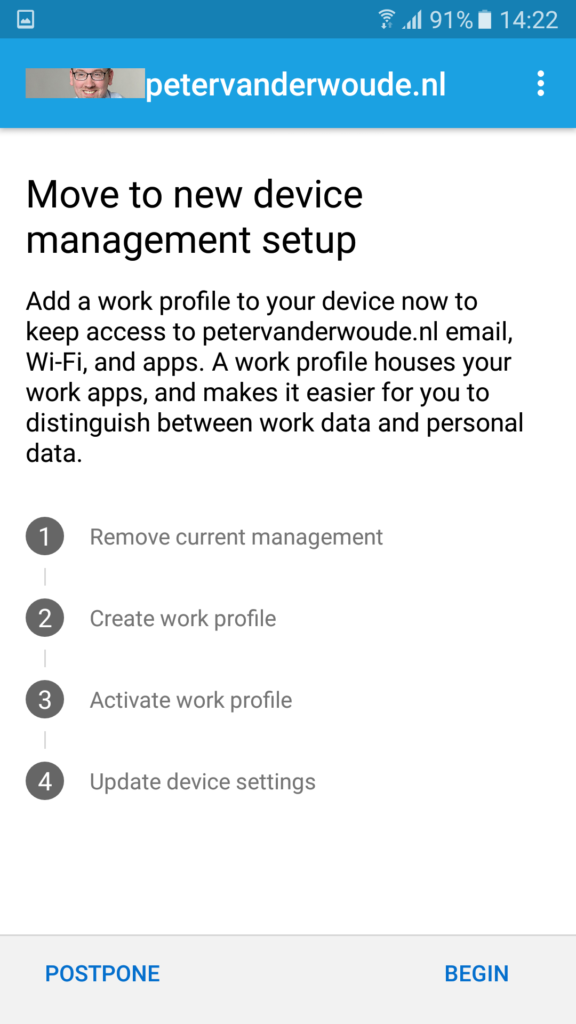
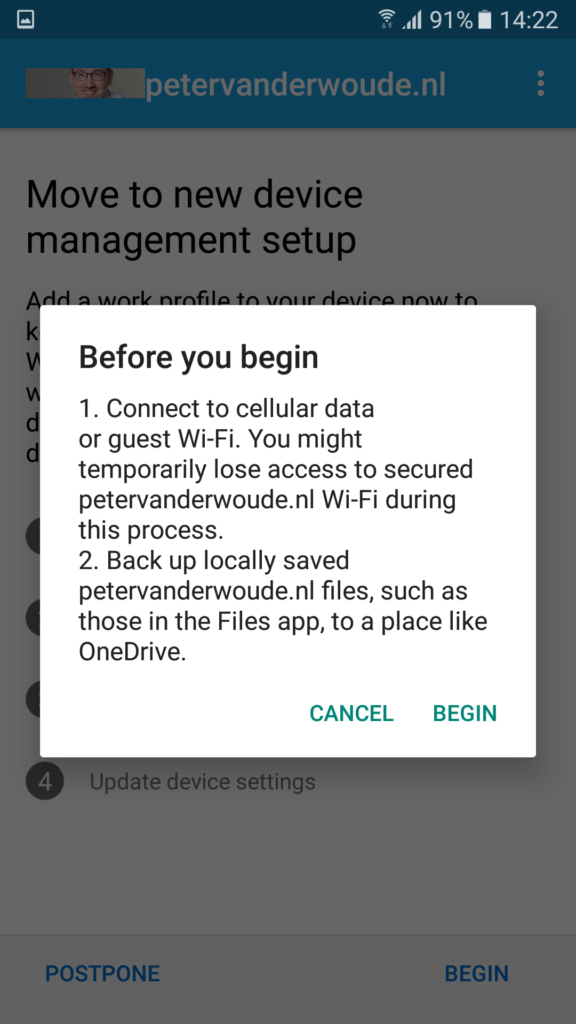
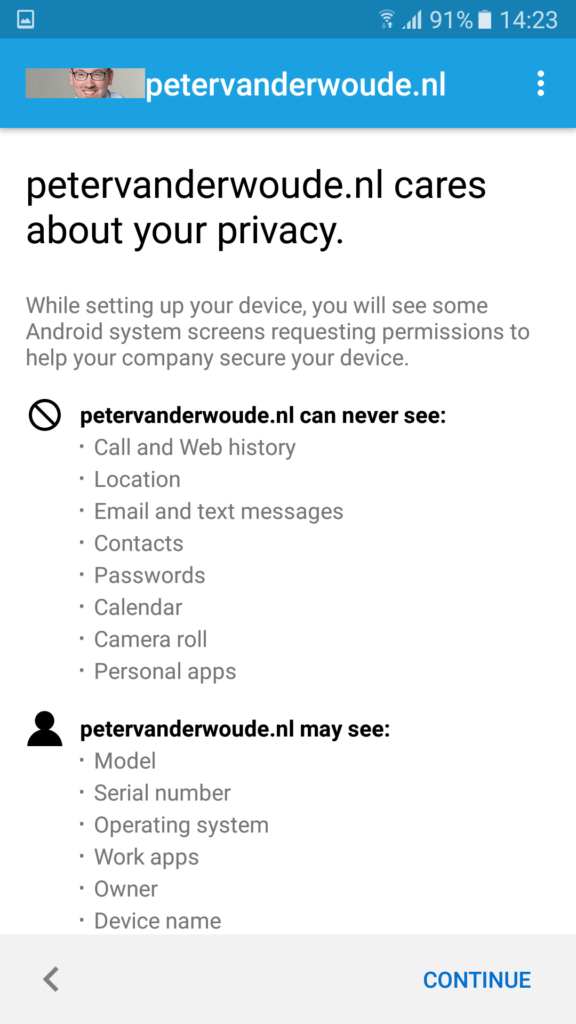
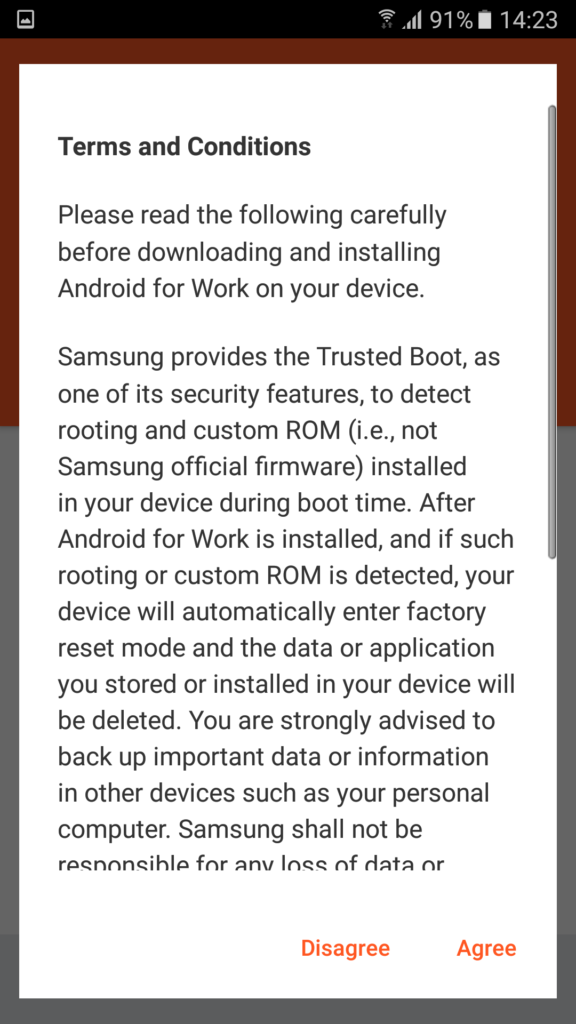
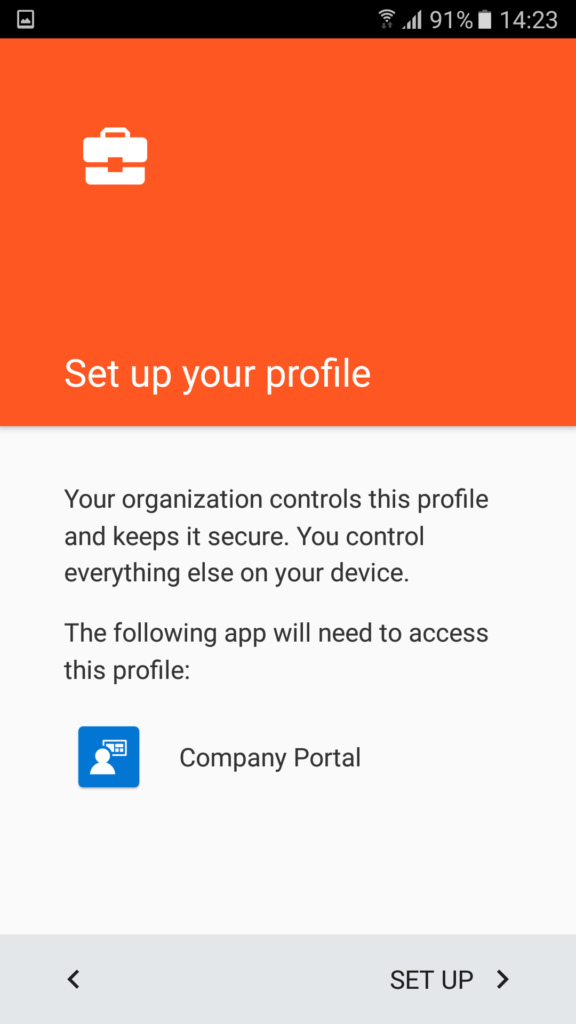
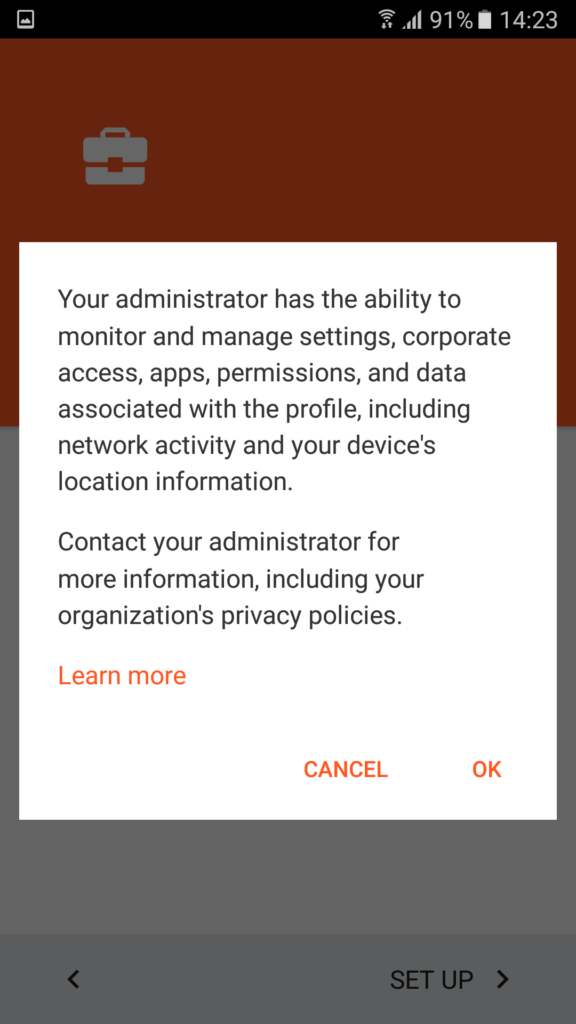
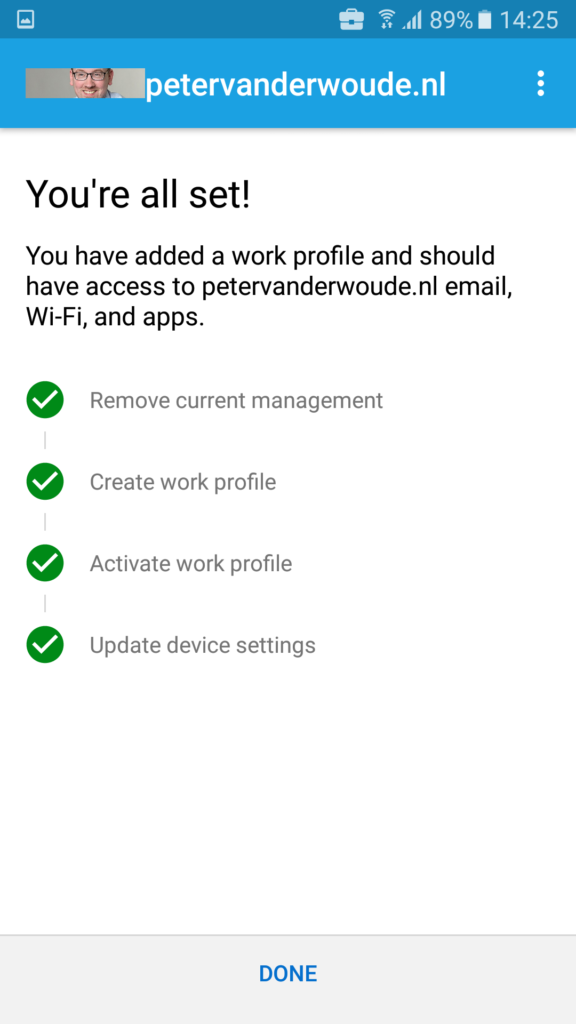
Figure 4 to Figure 14 below, walk through the migration steps for the end-user when starting with an Android device administrator managed device and moving to Android Enterprise work profile management. Figure 5 is also the starting point when the end-user would click on the provided link in an email and Figure 15 provides an overview of the end result.
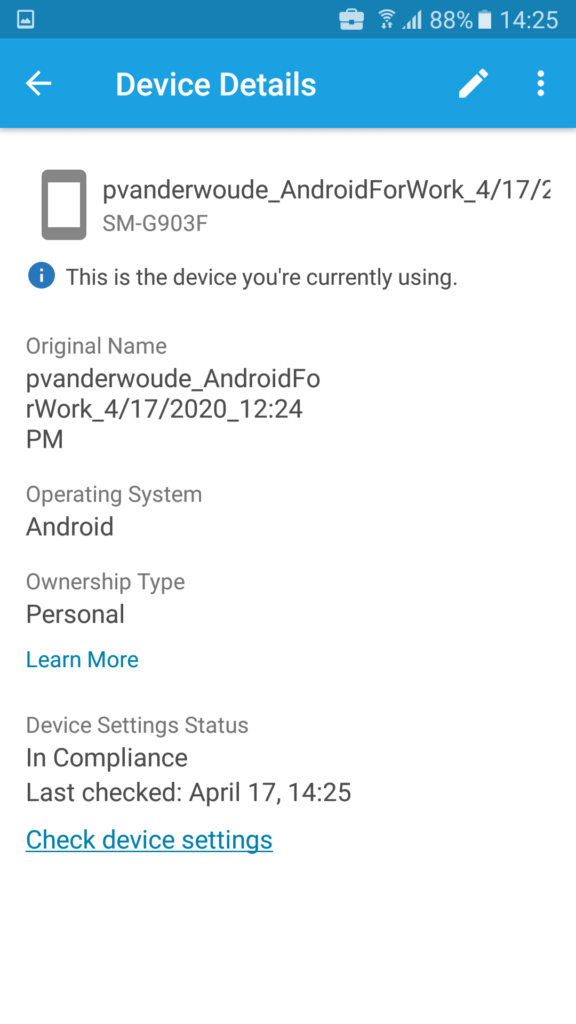
Figure 15: End result of the device migrated to Android Enterprise work profile
Note: In Figure 4 it already shows that the device status is “Not in Compliance“, while in fact the device can still be “In grace period“. Also, in Figure 5 the end-user will receive the message “Unable to resolve” when the enrollment of Android Enterprise (work profile) devices is restricted for the specific end-user.
More information
For more information about moving to Android Enterprise work profile management and enrollment restrictions, refer to the following docs:
- Move Android devices from device administrator to work profile management – https://docs.microsoft.com/en-us/mem/intune/enrollment/android-move-device-admin-work-profile
- Set enrollment restrictions – https://docs.microsoft.com/en-us/mem/intune/enrollment/enrollment-restrictions-set


Open the Microsoft Endpoint Manager admin center portal and navigate to Devices > Windows > Compliance policies to open the Windows | Compliance policies blade
On the Windows | Compliance policies blade, click Create Policy to open the Create Policy blade
On the Create Policy blade, provide the following information and click Create
Do i have to select Windows compliance blade for Android devices moving from device admin to work profile?
Apologies, Jagan! That should of course be Android instead of Windows. I’ve directly updated it.
Thank you!
Regards, Peter
Thank you Peter!!?.
Also actions for Non compliance. I see by default. Mark device non complaint. option as to select number of days.
Not getting options the way that’s showing as per your image
Hi Jagan,
That’s correct. In text is a guidance for what you can create and the picture provides an example configuration.
Regards, Peter
Dear Peter,
Thanks for you doc, but for example, outlook contacts sync , access to native pictures, need to reinstall pdf viewer apps to open attachment in outlook work profile is a no go for most of the users here… I can understand the work profile is a secure container but this is too big constraints for common use
Hi Julien,
I can imagine that Android Enterprise Enterprise work profile is not the solution for every organization. That being said, this is the only existing migration path. A path to a different Android Enterprise deployment model is not a simple migration, but often requires a reset of the device.
Regards, Peter
Hi Peter,
Thanks for this very explanatory article. The device restriction on Android device administrator resolved a major issue I was experiencing during my testing, which was not allowing me to migrate over to a Work Account, even though the compliance policy was set up correctly.
Regards,
Marios
Good to hear that, Marios!
Hi Peter,
Thank you for the article.
Before the users are migrated to Android Enterprise by the compliance policy as described, there should be configuration profiles (such as Email and Wi-fi) and a (default) compliance policy created for Android Enterprise in place correct?
Regards,
Menno
Hi Menno,
Yes, that’s correct. It can be done at a later moment also, but your devices will be missing that configuration in the time between.
Regards, Peter