This week a relatively short blog post about the recently introduced feature to require a minimum platform version, app version and Intune app protection policy SDK version, when using MAM-WE. This enables organizations to require end-users to update their personal devices when using apps to connect to company resources. That can be very useful when specific platform and/or app updates introduce important new features, or fix important bugs. In other words, a great feature! In this post I’ll go through the available settings, the configuration options and the end-user experience.
Configuration
Let’s start by having a look at the configuration. I’ll do that by first going through the available settings, followed by going through how to configure those settings in an app protection policy.
Available settings
Since May 2017 it’s possible to set additional requirements for MAM-WE that enforces the following policies before connecting to company data:
- Minimum app version;
- Minimum platform version;
- Minimum Intune app protection policy SDK version (iOS only).
Most of these settings are available for both Android and iOS. Microsoft Intune supports minimum version enforcement for platform versions, app versions, and Intune app protection policy SDK. Setting a minimum version enforcement for the Intune app protection SDK, is currently only available for iOS. The configuration is also available when configuring an app protection policy for Android, but in that case the configuration will not work and will not save (at this moment).
Configure app protection policy
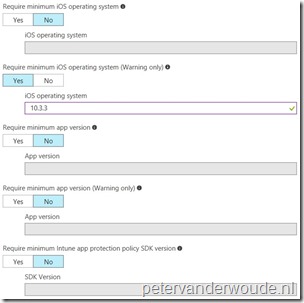
Now let’s have a look at configuring the available settings in an app protection policy. I’ll do that by going through the steps for creating an app protection policy for iOS that provides a warning message when the iOS platform is not at the specified minimum version. Configuring the remaining settings can be done by following similar steps, as shown in the screenshot in step 6. That screenshot shows all the new available settings. Also, keep in mind that it might require multiple app protection policies when targeting specific apps and versions.
| 1 | Open the Azure portal and navigate to Intune App Protection > App policy; |
| 2 | Select Add a policy to open the Add a policy blade; |
| 3 | On the Add a policy blade, provide a unique name for the app protection policy and select Apps to open the Apps blade; |
| 4 | On the Apps blade, select the required apps and click OK to return to the Add a policy blade; |
| 5 | Back on the Add a policy blade, select Settings to open the Settings blade; |
| 6 |
Note: When specifying a version number it’s required to specify at least a major and minor version. Only a major version is not sufficient. In my example I used 10.3.3 for easy testing, as the current iOS version is 10.3.2. |
| 7 | Back on the Add a policy blade, click Create; |
Note: When creating an app protection policy for Android devices, the option to configure a specific minimum Intune SDK version is available. However, it won’t be configurable.
End-user experience
Let’s end this post by looking at the end-user experience. Depending on the configuration, the end-user might be unable to access the targeted application if the minimum requirements through the app protection policy are not met at the three different levels mentioned above. Let’s start mildly. Below are examples of an iOS device trying to use the Outlook app to connect to Exchange Online. On the left is an example of a warning notification about the platform version and on the right is a warning notification about the app version. These notifications can be closed and the app can be used as normal.
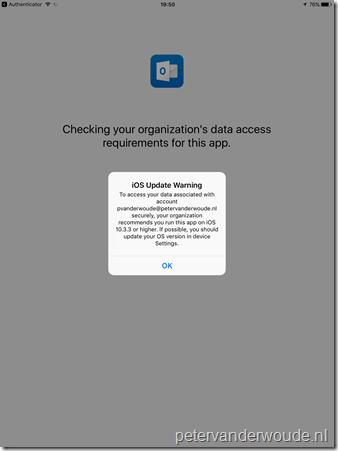 |
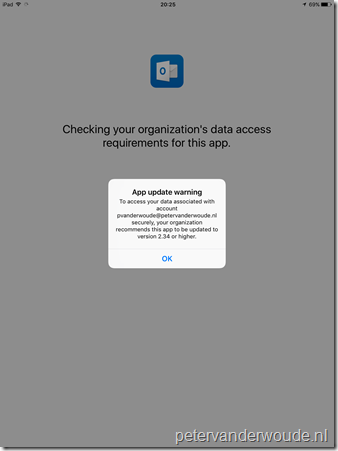 |
Now let’s take it one step further. Below are examples of an Android device trying to use the Outlook app to connect to Exchange Online. On the left is an example of a blocking notification about the platform version and on the right is an example of a blocking notification about the app version. At this moment, the end-user may either remove their account (for multi-identity applications), or go back to close the app and update the version of the app or platform.
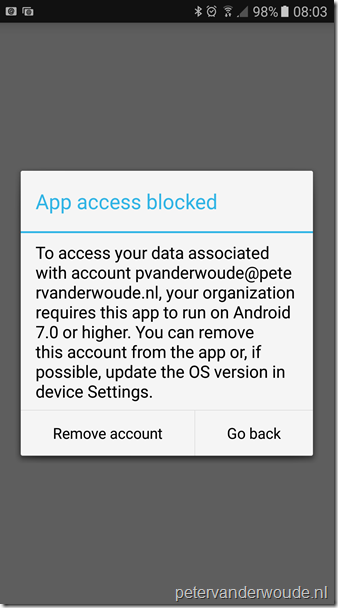 |
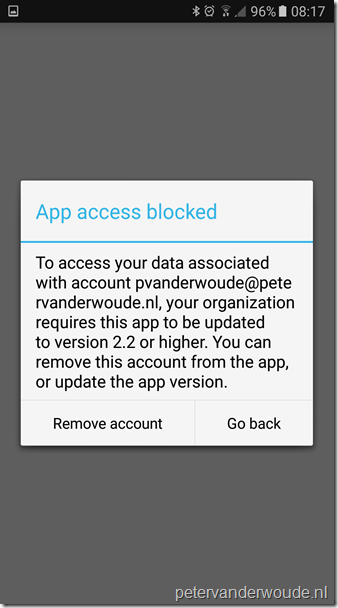 |
More information
For more information about the available app protection policies, please refer to:
- Android app protection policy settings: https://docs.microsoft.com/en-us/intune/app-protection-policy-settings-android
- iOS app protection policy settings: https://docs.microsoft.com/en-us/intune/app-protection-policy-settings-ios
Peter, are you assigning these policies to users or devices? Thanks 🙂
Hi Martin,
I’m assigning these policies to users (groups).
Regards, Peter
For required app version do you have to make a new policy for each app you want to specify a version?
Hi John.
You can have multiple apps in the policy, but I doubt that many apps have the same version number.
Regards, Peter