This week is also a relatively short blog post. However, this week is about a recently introduced feature in Microsoft Intune. That feature is the ability assign a scope tag to all devices in a specific security group. Like last week it’s a relatively simple feature, but also like last week that simple feature makes life a lot easier. A few months ago I did a post about adding scope tags to devices. In that time it was still a manual action per device, which could be automated via PowerShell. In this post I’ll show how that this configuration can now be achieved by using a security group and what the result of that configuration is.
Configuration
Now let’s start by having a look at the steps to configure the automatic assignment of scope tags to all devices in a specific security group. The following 5 simple steps walk through the configuration of that assignment.
| 1 | Open the Azure portal and navigate to Microsoft Intune > Roles > Scope (Tags) to open the Intune roles – Scope (Tags) blade; |
| 2 |
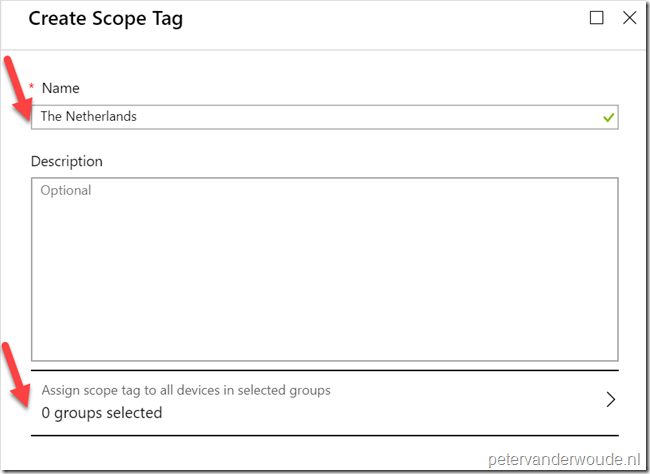
On the Intune roles – Scope (Tags) blade, select Create to open the Create Scope Tag blade; Note: When existing Scope tags are available, simply select the existing Scope tag to open the Edit <ScopeTagName> blade. The step next step will be pretty similar. |
| 3 | On the Create Scope Tag blade, provide a valid Name for the scope tag and select Assign scope tag to all devices in selected groups to open the Select groups blade; |
| — |  |
| 4 | On the Select groups blade, select the required security group and click Select to return to the Create Scope Tag blade; |
| — | 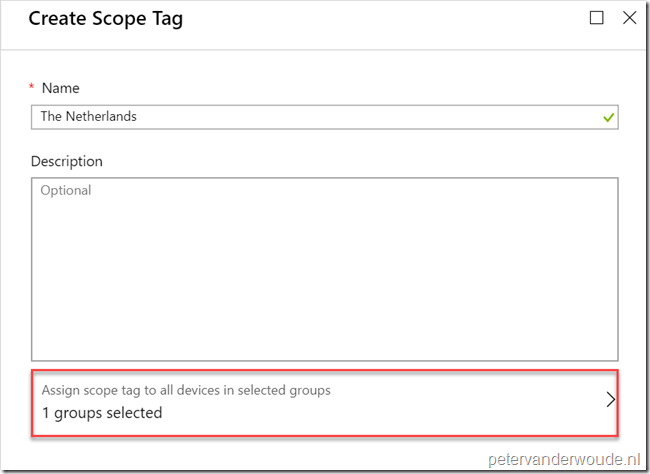 |
| 5 | Back on the Create Scope Tag blade, click Create to create the Scope tag; |
Result
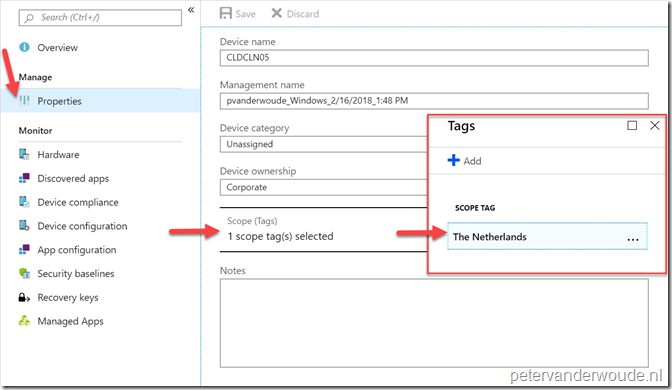
Let’s end this post by having a quick look at the result of the mentioned configuration. Let’s do that by having a look at the Properties of a device. Initially the scope tag configuration had to be done manually in the Properties of a device (or by using a script). Now the scope tag configuration will automatically be populated based on the devices in the selected security groups in the scope tag configuration (see below). When the device will be removed from the security group, the scope will also be automatically removed.
Note: At this moment the scope tags in the Properties of a device are not read-only. The administrator is still able to manually remove a scope tag. Even when that scope tag was added via a security group. It is strongly recommended not to do this, as, in my experience, it will break the automatic behavior for that scope tag. In the future this configuration will become read-only.
More information
For more information about using scope tags, refer to this article about using role-based access control (RBAC) and scope tags for distributed IT.
Then we just need a way to assign scope tags to all users devices, based on user groups 🙂
That would be nice.
Agree, Morten. We’re getting closer to what it should be like.
Regards, Peter
Does it supports dynamic device groups?
Hi Kazzan,
There is no specific mention in the docs that it’s not supported.
Regards, Peter
Any ETA for scope tagging of devices via their (dynamic) user groups? We would like to limit the view of managed devices to specific companies only (user attribute).
Hi JuFisherman,
I haven’t heard anything. You could look at creating your own logics and automation to create a custom solution.
Regards, Peter
Scope Tags applied correctly to Windows devices but only to 10 of 100 IOS devices, where can i reslove this so that all IOS devices are tagged correctly and not just some of them?
Hi Danilo,
When the configuration steps are the same, I would suggest to contact Microsoft.
Regards, Peter
This doesn’t seem to work with nested groups. The group I selected when creating the Scope Tag, contains 4 other groups yet none of the members of those groups are getting tagged with the Scope Tag.
Hi Steve,
I haven’t specifically had to deal with that, but I know that not everything in Azure plays nice with nested groups. Intune, however, should play nice with nested groups. To be sure you could check with Intune Support.
Regards, Peter