This week a blog post about onboarding Windows 10 devices for Windows Defender Advanced Threat Protection (ATP). Windows Defender ATP is a relatively new service that will help enterprises to detect, investigate, and respond to advanced attacks on their networks. In this post I’ll show how to onboard Windows 10 devices, via Configuration Manager and Microsoft Intune, and I’ll show the end result in the Windows Defender Security Center and the Configuration Manager administration console.
Configuration
There are multiple methods available to onboard Windows 10 devices for Windows Defender ATP, Group Policy, Configuration Manager, mobile device management (including Microsoft Intune) and a local script. I’ll have a closer look at the configurations for onboarding Windows 10 devices via Configuration Manager and Microsoft Intune.
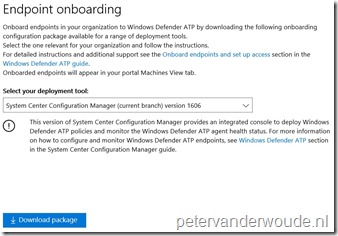
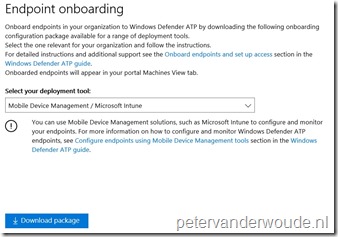
Create onboarding configuration file
Before starting with the configuration, it’s required to create an onboarding configuration file. The process for this is fairly simple and straightforward. Logon to the Windows Defender Security Center and select Endpoint Management. Now simply select the configuration method and download the required file, as shown below.
| System Center Configuration Manager | Mobile Device Management |
 |
 |
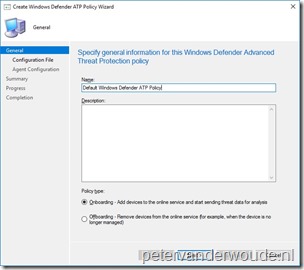
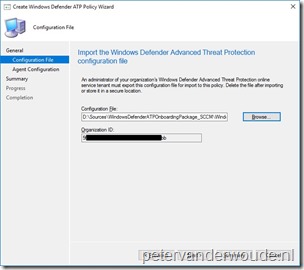
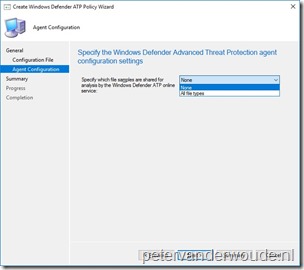
Configure endpoints using Configuration Manager
The first configuration method that I would like to show is using Configuration Manager, by creating and deploying a Windows Defender ATP Policy. By adding and deploying a client onboarding configuration file, via the Windows Defender ATP Policy, Configuration Manager can monitor the deployment status and the Windows Defender ATP agent health. Windows Defender ATP is only supported on Windows 10 devices, version 1607 and later, running the Configuration Manager client. On-premises mobile device management and Microsoft Intune hybrid MDM-managed computers are not supported. The following 7 steps show how to create the Windows Defender ATP Policy. After that, simply deploy the created policy.
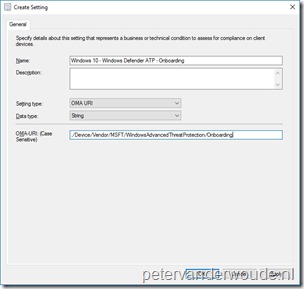
Configure endpoints using Microsoft Intune
The second configuration method that I would like to show is using Microsoft Intune hybrid and Microsoft Intune standalone, Windows Defender ATP supports Microsoft Intune by providing OMA-URI settings to create policies to manage endpoints. To achieve this the following OMA-URI configuration can be used:
- OMA-URI: ./Device/Vendor/MSFT/WindowsAdvancedThreatProtection/Onboarding
- Date type: String
- Value: [Content of the WindowsDefenderATP.onboarding file that is available in the downloaded WindowsDefenderATPOnboardingPackage.zip file]
Just to make sure that it’s absolutely clear, the value, of the OMA-URI configuration, is literally a copy-paste action of the content available in the WindowsDefenderATP.onboarding file. This information can be used in Microsoft Intune hybrid and Microsoft Intune standalone, by using the configuration guidelines shown below.
End result
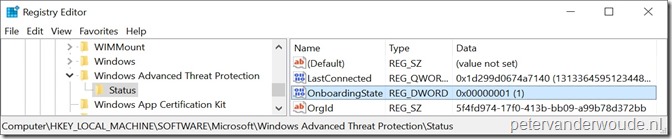
Let’s end this blog post by having a look at the end result. I’ll do that by providing a status view from the Windows Defender Security Center. Before doing that, it’s good to mention that a successful onboarding can be verified in the registry of the Windows 10 device, as shown below.
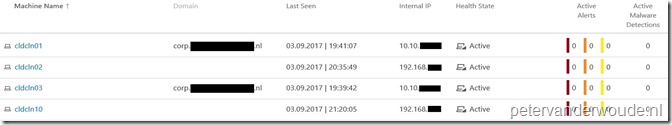
Once the onboarding is successful for the Windows 10 devices, the information about those devices will start flowing to the Windows Defender Security Center. The Machines section in the Windows Defender Security Center will provide an overview of those devices and their status, as shown below.
To see more information about the Windows 10 devices, click on a device and it will show a Machines view about the selected device. This view contains information about the logged on users, the reporting status, the alerts and the machine timeline. To get information in the Alerts section, I’ve simply created an EICAR test file, as shown below. This also enables me to select the alert and get more information about the alert, see the process tree and see the incident graph.
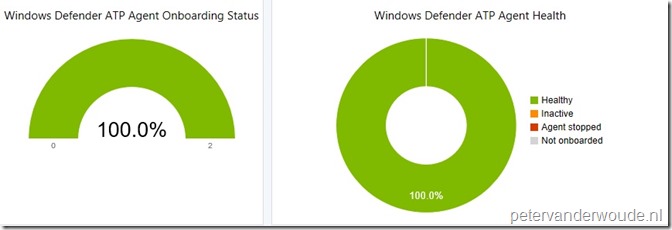
From a Configuration Manager perspective, I’ve saved the coolest information until the end. Windows 10 devices managed with the Configuration Manager client and successfully onboarded with the Windows Defender ATP Policy will also report information to Configuration Manager. This information can be viewed via additional columns in normal device views and collections. Even better, it will also show agent information in the Windows Defender ATP Status dashboard, as shown below.
Keep in mind that the Windows Defender ATP Status dashboard only shows information for Windows 10 devices managed with the Configuration Manager client and not for Windows 10 devices managed via MDM.
More information
For more information about Windows ATP and the onboarding, please refer to the following articles:
- Windows Defender Advanced Threat Protection: https://docs.microsoft.com/en-us/sccm/protect/deploy-use/windows-defender-advanced-threat-protection
- Configure endpoints using System Center Configuration Manager: https://technet.microsoft.com/itpro/windows/keep-secure/configure-endpoints-sccm-windows-defender-advanced-threat-protection
- Configure endpoints using Mobile Device Management tools: https://technet.microsoft.com/itpro/windows/keep-secure/configure-endpoints-mdm-windows-defender-advanced-threat-protection
- Troubleshoot Windows Defender Advanced Threat Protection onboarding issues: https://technet.microsoft.com/itpro/windows/keep-secure/troubleshoot-onboarding-windows-defender-advanced-threat-protection


Hi Peter,
We are using sccm 1702 and i am currently trialing ATP against win 10 pro 1703 devices.
The devices that are apart of a test collection where the ATP policy is being applied are not being shown within the ATP portal.
I followed the straightforward steps and i have validated that under “Configurations” in configuration manager properties on the workstation that the configuration policy is compliant although under status in registry the onboarding state is 0. I try to run the local ATP service and the error received is
Windows Defender Advanced Threat Protection service is not onboarded and no onboarding parameters were found.
Now i have gone through MS’s pre req and troubleshooting doc and i can verify that diag tracking is started. I have also enabled sample file submissions under windows defender also still no luck. Any ideas?
Hi Mark,
Are you using ConfigMgr hybrid or standalone and are you deploying a policies or a CI?
Peter