 This week another blog post about Windows 10 and OMA-DM. This week I’m going to have a look at managing Windows Update for Business on Windows 10. However, this time I’ll group the currently available policy settings per subject, to easily provide some more background information. Also, by now I assume that I don’t have to go through all the steps to create a Configuration Item or a Configuration Policy anymore.
This week another blog post about Windows 10 and OMA-DM. This week I’m going to have a look at managing Windows Update for Business on Windows 10. However, this time I’ll group the currently available policy settings per subject, to easily provide some more background information. Also, by now I assume that I don’t have to go through all the steps to create a Configuration Item or a Configuration Policy anymore.
To manage Windows Update for Business, IT organizations can use the Policy configuration service provider (CSP) and to report about Windows Update for Business IT organizations can mainly use the Update CSP. During this blog post I’ll provide more information about Windows Update for Business, the Policy CSP, the Update CSP and the available policy configurations. I’ll end this post with configuration examples for Microsoft Intune standalone and Microsoft Intune hybrid.
Introduction
Let’s start with a short introduction about Windows Update for Business. What is it and how is different from Windows Update and Windows Server Update Services (WSUS). Windows Update for Business enables IT organizations to keep the Windows 10 devices always up to date with the latest security updates and Windows features by directly connecting these devices to Windows Update. By only using policies, Windows Update for Business is an easily established and implemented system which enables IT organizations to exercise control on how their Windows 10 devices are updated.
IT organizations can specify which devices go first in an update wave, and which devices will come later, and can make the delivery of updates to branch offices and remote sites, with limited bandwidth, very efficient.
Windows Update for Business can even be used in combination with existing management tools, such as ConfigMgr. It basically allows IT organizations to manage how and when Windows 10 devices receive updates and upgrades and provides controls to help organizations validate update quality as well as time their update deployments.
Configuration
Now let’s have a look at the configuration options for Windows Update for Business via OMA-DM. I’ll have a look at how to defer updates and upgrades, how to pause updates and upgrades and how to optimize the deployment. However, it should be noted that at this moment not everything can be configured via OMA-DM, yet.
Policy CSP & Update CSP
Before really looking at the configuration scenarios, it’s good to have a quick look at the Policy CSP and the Update CSP. The Policy CSP enables IT organizations to configure company policies on Windows 10 devices. Those policies also include the configuration options for Windows Update for Business, The Update CSP enables IT organizations to get information about the update status of Windows 10 devices. Below is a quick overview of both CSPs.
| Policy CSP | Update CSP |
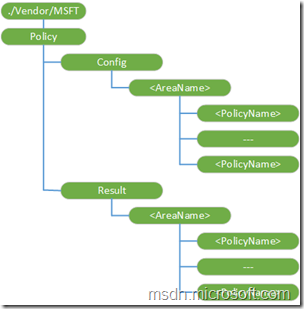 |
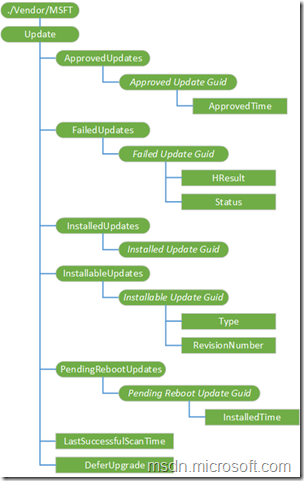 |
Defer upgrades
To use Windows Update for Business, Windows 10 devices must be configured to Current Branch for Business (CBB). This can be configured by using one of the following policies.
| Policy | Description |
Update/BranchReadinessLevel
|
New for Windows 10, version 1607. Allows the IT organization to set a device to the Current Branch or the Current Branch for Business servicing branch. |
Update/RequireDeferUpgrade
|
Allows the IT organization to set a device to the Current Branch or the Current Branch for Business servicing branch. |
Defer upgrade and update periods
Windows Update for Business provides IT organizations the ability to control when updates and upgrades are deployed to their Windows 10 devices. This can be achieved by specifying deferral windows from when the updates and upgrades are initially made available on Windows Update. There are restrictions as to how long IT organizations can delay updates and upgrades. The following table details the deferral periods and supported values.
| Policy | Description |
Update/DeferFeatureUpdatePeriodInDays
|
New for Windows 10, version 1607. Allows the IT organization to defer Feature Updates for up to 180 days. |
Update/DeferQualityUpdatePeriodInDays
|
New for Windows 10, version 1607. Allows the IT organization to defer Quality Updates for up to 30 days. |
Update/DeferUpdatePeriod
|
Allows the IT organization to delay updates for up to 4 weeks. |
Update/DeferUpgradePeriod
|
Allows the IT organization to delay upgrades for up to 8 months. |
Pause upgrades and updates
Windows Update for Business also provides IT organizations the ability to pause updates and upgrades on a per device basis. This pause functionality ensures that no updates or upgrades will be made available for the specified device. The device will remain in this state until the configured period has passed or when the device is specifically “unpaused”. At that point updates are auto-resumed. The following table details the pause options and the supported values.
| Policy | Description |
Update/PauseDeferrals
|
Allows the IT organization to pause updates and upgrades for up to 5 weeks. Paused deferrals will automatically be reset after 5 weeks, or when the value is set back to 0. |
Update/PauseFeatureUpdates
|
New in Windows 10, version 1607. Allows the IT organization to pause Feature Updates for up to 60 days. Paused Feature Updates will automatically be reset after 60 days, or when the value is set back to 0. |
Update/PauseQualityUpdates
|
New in Windows 10, version 1607. Allows IT Admins to pause Quality Updates. Paused Quality Updates will automatically be reset after 35 days, or when the value is set back to 0. |
Optimize delivery
By grouping machines into similar deferral periods, IT organizations can cluster devices into deployment or validation groups which can be used as a quality control measure as updates are deployed in Windows 10. With deferral windows and the ability to pause, IT organizations can effectively control and measure update deployments by rolling out to a small pool of devices first to verify quality, prior to a broader roll-out in the organization.
At this moment Windows 10 doesn’t provide configuration options via OMA-DM to specifically configure a device in a specific group. However, it’s still possible to configure a specific set of devices with a similar deferral period and to take advantage of the default configuration in Windows 10 to get updates from PCs on my local network,
Update approval
Windows Update for Business also provides IT organizations with the ability to restrict the updates that are installed on a device to only those on the update approval list. That list can be configured via the Update CSP and enables the IT organization to accept the End User License Agreement (EULA) on behalf of the end-user. This can be configured by using the following policy.
| Policy | Description |
Update/RequireUpdateApproval
|
Allows the IT organization to restrict the updates that are installed on a device to only those on an update approval list. It enables the IT organization to accept the EULA associated with the approved update on behalf of the end-user. |
Example configuration
Now let’s end this post slightly different as usual. This time not with the end-user experience, but with example configurations, as I didn’t provide any throughout this post. Also, the biggest end-user experience is already shown in the picture at the beginning of this post, which is showing a grayed-out Defer upgrades setting. Below is an example of the RequireDeferUpgrade setting in Microsoft Intune hybrid (Configuration Item) and Microsoft Intune standalone (Configuration Policy).
| Microsoft Intune hybrid | Microsoft Intune standalone |
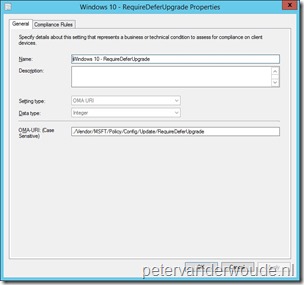 |
 |
More information
Fore more information about Windows Update for Business, the Update CSP and the Policy CSP, please refer to:
- Windows Update for Business: https://technet.microsoft.com/en-us/itpro/windows/plan/windows-update-for-business
- Setup and deployment: https://technet.microsoft.com/en-us/itpro/windows/plan/setup-and-deployment
- Integration with management solutions: https://technet.microsoft.com/en-us/itpro/windows/plan/integration-with-management-solutions-
- Policy CSP: https://msdn.microsoft.com/en-us/library/windows/hardware/dn904962%28v=vs.85%29.aspx
- Update CSP: https://msdn.microsoft.com/en-us/library/windows/hardware/dn904974(v=vs.85).aspx
But this does not work when using the Intune Agent, right?
This is specifically for devices managed via Windows 10 MDM.
Is there a mechanism to handle this same outcome but for Windows 10 devices managed by the Intune client (not MDM)?
If those devices are domain joined, you can use GPO’s.
I have In tune hybrid environment with 2000+ Windows 10 computers with OMA-DM.
We are noticing major issue after patch Tuesday since all computers are going together for patching together.
Can i use “Windows Update for Business” integrating with Configmgr to group the computers and set differeent time for patching each group ? or any other ways?
any method is there to avoid or control a particular patch getting installed on Intune managed Windows 10 computers with OMA-DM ?
There is no integration between ConfigMgr and WUfB. You can only manage some settings via Windows 10 MDM. Groups are currently not part of those manageable settings.
The “BranchReadinessLevel” REG_DWORD entries are 16 or 32 and not 0 or 1 as described in the article.
https://msdn.microsoft.com/en-us/library/windows/hardware/dn957432(v=vs.85).aspx#new_update_policies
Search for BranchReadinessLevel in my link above for confirmation.
Thank you, Ronan! That information has been recently updated and I’ll update my blog post accordingly. Thank you again.