This week and next week I’ll be looking at integrating Microsoft Intune with Zimperium. Zimperium is one the available third-party Mobile Threat Defense connectors for Microsoft Intune. This enables organizations to add an additional layer of protection to their corporate resources. More specifically, prevent access from compromised mobile devices. In the first part of this week I’ll be providing a short introduction about the integration and I’ll show how to configure the integration. I’ll end this post with the configuration results.
Introduction
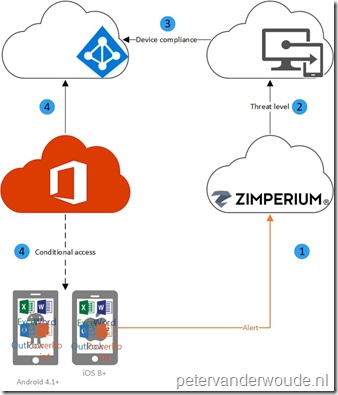
Let’s start with a little introduction. Organizations can control mobile device access to corporate resources by using conditional access based on a risk assessment conducted by Zimperium. For this, Zimperium must be integrated with Microsoft Intune. The risk is assessed based on telemetry collected from devices running the Zimperium app. This enables organizations to configure conditional access policies based on the Zimperium risk assessment. The conditional access policy requires compliant devices and the compliance policy requires a minimum Mobile Threat Defense level. That combination enables organizations to allow or block non-compliant devices to access corporate resources based on detected threats.
To visualize this a bit more, it could be summarized in the following flow.
Configuration
Now let’s have a look at the actual configuration of the integration between Zimperium and Microsoft Intune. The connector. Before starting with the configuration make sure that the following is available:
- Microsoft Intune subscription;
- Azure Active Directory administrative credentials;
- Zimperium zConsole administrative credentials.
Zimperium configuration
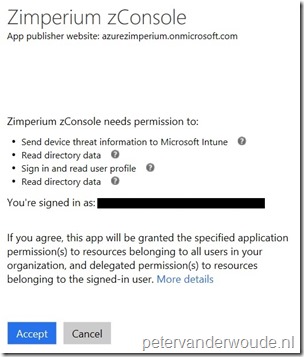
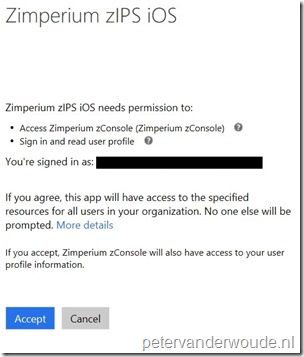
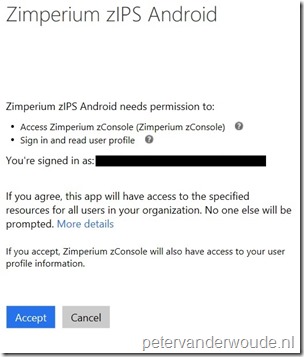
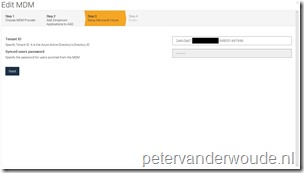
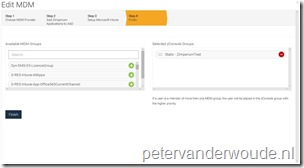
The actual configuration starts in the Zimperium zConsole and not in the Intune section of the Azure portal. The Intune section in the Azure portal will only refer to the Zimperium zConsole. The 6 steps below walk through the configuration in cloud version of Zimperium.
Note: The connector between Zimperium and Intune automatically synchronizes and the synchronization schedule can be customized. This synchronization can also be manually triggered (see the Results section).
Microsoft Intune configuration
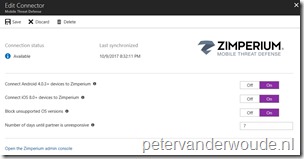
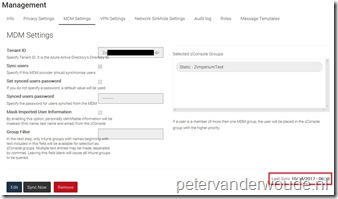
After performing the configuration in the Zimperium zConsole, the connector will be created in Microsoft Intune. This enables a few tuning options from Microsoft Intune perspective. The following 3 steps walk through the configuration options.
Results
When the configurations are completed, a successful configuration can be verified in the Zimperium zConsole (below on the right) and in the Azure portal (below on the left). Both will show the same synchronization time.
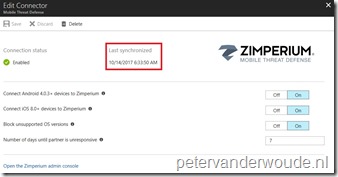 |
 |
More information
For more information about Mobile Treat Defense, Zimperium and Microsoft Intune, please refer to the following articles:
- Mobile Threat Defense integration with Intune: https://docs.microsoft.com/en-us/intune/mobile-threat-defense
- Zimperium Mobile Threat Defense connector with Intune: https://docs.microsoft.com/en-us/intune/zimperium-mobile-threat-defense-connector
- Integrate Zimperium with Intune: https://docs.microsoft.com/en-us/intune/zimperium-mtd-connector-integration