This week is all about a very often requested feature, which is the ability to hybrid Azure AD join a device when using Windows Autopilot. The combination of the latest updates to Microsoft Intune with Windows 10, version 1809, provides just that! The ability to hybrid Azure AD join a device when using Windows Autopilot! In other words, the device will join the on-premises Active Directory and register in Azure Active Directory. In this blog post I’ll start with a short introduction about the hybrid Azure AD join with Windows Autopilot, followed by the most important configurations. I’ll end this post by looking at the experience.
Introduction
Let’s start with a little introduction about the hybrid Azure AD join through Windows Autopilot. A short summary would be that Intune uses an on-premises connector to create an offline domain join (ODJ) blob for the device that will be provided to the device during enrollment. Now lets go through the high-level Autopilot flow for this scenario and see how that fits.
- The hardware ID of the device is registered with the Windows Autopilot service;
- The device is sent to the employee and the employee unboxes the device and turns it on;
- The device connects to the Windows Autopilot service;
- The Windows Autopilot service delivers the Autopilot profile to the device;
- The device performs a MDM-enrollment with Microsoft Intune;
- Microsoft Intune will use the on-premises connector to generate a machine object in Active Directory, which will generate an ODJ blob;
- The connector sends the ODJ blob to Microsoft Intune;
- Microsoft Intune sends the ODJ blob to the device;
- The MDM-enrollment is completed;
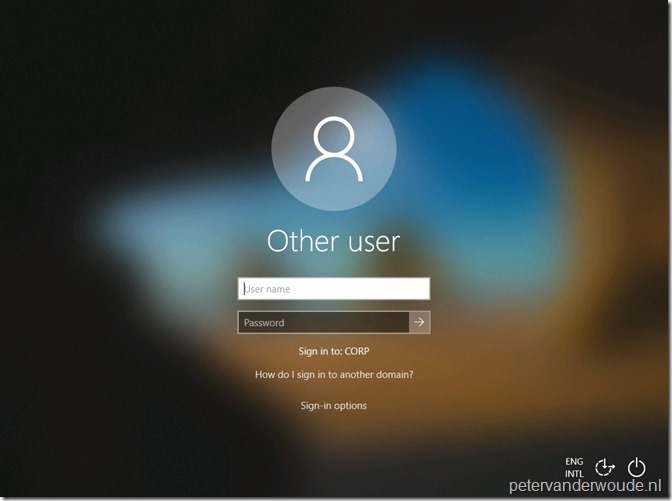
- The user logs on to the device to complete the domain join;
- The device receives any targeted group policies;
Configuration
Now let’s continue by looking at the configurations that are required to enable the hybrid Azure AD join scenario via Windows Autopilot. I’ll do that by going through the new Intune-related configurations. That means, I’ll show how to install the Intune connector, I’ll show how to configure the Autopilot deployment profile and I’ll show how to configure the domain join profile.
Requirements
Before looking at the configurations, let’s start with a few important requirements and limitations:
- The hybrid Azure AD join environment configurations must be in place;
- The device must run Windows 10, version 1809 or later;
- The device must have Internet access;
- The device must have direct access to Active Directory;
- Automatic enrollment must be configured (Azure AD > Mobility (MDM and MAM));
- The server hosting the Intune connector must have delegated permissions to create computer accounts in the specified OU;
- The server hosting the Intune connector must be Windows Server 2016, or later;
- The server hosting the Intune connector must have Internet connectivity;
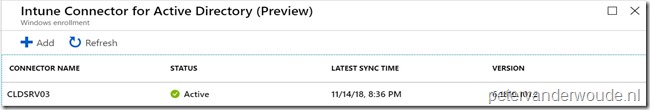
Intune connector
The first configuration that should be in place is the installation of the Intune connector. Multiple connectors can be installed to increase scale and availability (or even to support multiple Active Directory domains). The following nine steps walk through the steps to install the Intune connector.
| 1 | Open the Azure portal and navigate to Microsoft Intune > Device enrollment > Windows enrollment to open the Device enrollment – Windows enrollment blade; |
| 2 | On the Device enrollment – Windows enrollment blade, select Intune Connector for Active Directory (Preview) to open the Intune Connector for Active Directory (Preview) blade; |
| 3 | On the Intune Connector for Active Directory (Preview) blade, select Add connector to open the Add connector blade; |
| 4 | On the Add connector blade, click the Download the on-premises Intune Connector for Active Directory to download the connector for Active Directory (ODJConnectorBootstrapper.exe); |
| 5 | On the server that should be running the Intune connector for Active Directory, run ODJConnectorBootstrapper.exe; |
| 6 | On the Intune Connector for Active Directory Setup dialog box, select I agree to license terms and conditions and click Install; |
| 7 | On the Intune Connector for Active Directory Setup dialog box, after the installation completed, select Configure Now ; |
| 8 | On the Intune connector for Active Directory dialog box, select Sign In to sign in with a global administrator account to enroll the connector in the tenant and close the dialog box; |
| 9 | Back on the Intune Connector for Active Directory (Preview) blade, it should now show an entry for the added connector with the name of the server that is running the connector; |
| — |  |
Note: At this moment, make sure that a language pack is installed and configured as described in the Intune Connector (preview) language requirements.
Autopilot deployment profile
The second configuration that should be in place is the Windows Autopilot deployment profile. The following four steps walk through the steps to create the deployment profile. That deployment profile can be assigned to an Azure AD group that contains the required Autopilot devices.
| 1 | Open the Azure portal and navigate to Microsoft Intune > Device enrollment > Windows enrollment to open the Device enrollment – Windows enrollment blade; |
| 2 | On the Device enrollment – Windows enrollment blade, select Deployment Profiles in the Windows Autopilot Deployment Program section to open the Windows Autopilot deployment profiles blade; |
| 3 | On Windows Autopilot deployment profiles blade, select Create profile to open the Create profile blade; |
| 4a | 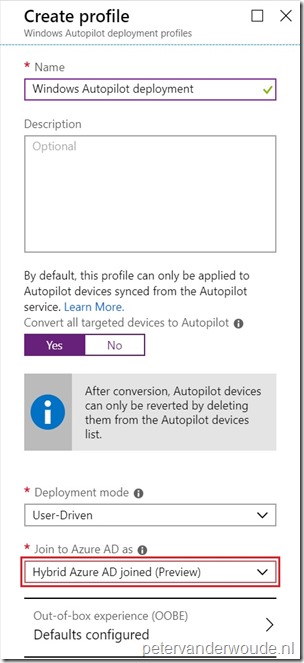 On the Create profile blade, provide the following information and click Create; On the Create profile blade, provide the following information and click Create;
Note: The hybrid Azure AD join is only available for user driven deployments. |
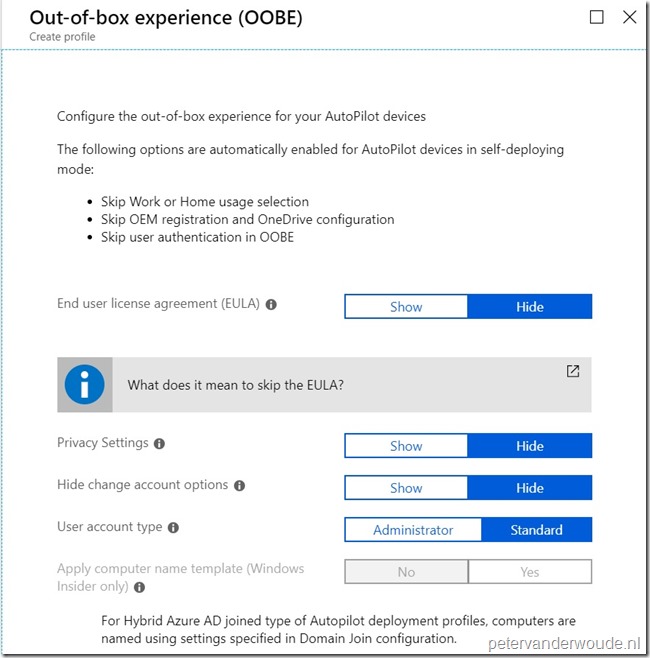
| 4b |
On the Out-of-box experience (OOBE) blade, provide the following information and click Save.
|
| — |  |
Domain Join profile
The third configuration that should be in place is the domain join profile. The following four steps walk through the steps to create the domain join profile. That domain join profile can be assigned to an Azure AD group that contains the required Autopilot devices.
| 1 | Open the Azure portal and navigate to Microsoft Intune > Device configuration > Profiles to open the Device configuration – Profiles blade; |
| 2 | On the Device configuration – Profiles blade, select Create profile to open the Create profile blade; |
| 3a | On the Create profile blade, provide the following information and click Create;
|
| 3b | On the Domain Join (Preview) blade, provide the following information and click OK;
|
| — | 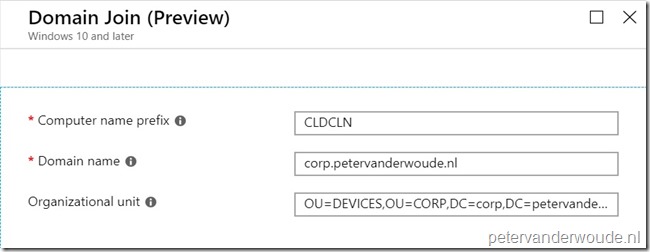 |
Note: When no OU is specified, the well known computer object container is used.
End-user experience
Let’s end this post by looking at the end-user experience. The beginning of the out-of-box-experience (OOBE) is similar to any other Windows Autopilot deployment. The difference is happening in the background, as explained during the introduction, and can be noticed during the Network configuration. The configuration will take longer than with a Azure AD join. Another thing that an administrator might notice is that the device will be available within Intune before it’s available within the Active Directory. That makes perfect sense as the domain join profile must come via Microsoft Intune.
Note: From an administrator perspective the Event Viewer, on the server running the connector, will show Event ID 30140 in the log ODJ Connector Service from the source ODJ Connector Service Source, with a successful creation of the computer object.
More information
For more information regarding Windows Autopilot and hybrid Azure AD join, please refer to the following articles:
- Deploy hybrid Azure AD joined devices using Intune and Windows Autopilot (Preview): https://docs.microsoft.com/en-us/intune/windows-autopilot-hybrid
- How to plan your hybrid Azure Active Directory join implementation: https://docs.microsoft.com/en-us/azure/active-directory/devices/hybrid-azuread-join-plan
Awesome blog!
You say;
The device must have direct access to Active Directory;
I presume this is needed after the enrollment so the user can login and it is not necessary for hybrid join?
Can a user log in with Azure credentials after the hybrid join?
Last, after the join the device is intune enrolled and domain joined? What will be leading in term of policies? Will gpo apply and/or intune policies?
Thank you, Paul!
Yes, during login the connection to the domain controller is required, but also before that already. For some more details, see also this post: https://blogs.technet.microsoft.com/mniehaus/2018/11/22/trying-out-windows-autopilot-user-driven-hybrid-azure-ad-join/
Hi
I am trying to setup the Intune connector and got successfully enrolled message.
But I am not seeing it in the Azure portal as well as getting the following error message in the event viewer:
Failed to get a value for Key: OdjServiceBaseUrl.The given key was not present in the dictionary.
Hi Ishwariya,
I haven’t seen that error yet, so I would advise to create a (free) support ticket.
Please do let us know the resolution.
Regards, Peter
had some interesting cases of the hybrid join working but ending up with 2 computer objects in Azure AD. Both with the same name but one Intune joined and one not. Do we know if there are specific client side logs that can see what is going on?
Hi Christian,
On the client it’s mainly the Event Viewer.
Regards, Peter
Great blog.
When assigning the Domain Join profile to the “All Autopilot Devices” Group and starting an autopilot deploy, the device shows up in AzureAD but this Domain Join Profile doesn’t apply.
The deployment status of the profile is “Not applicable”. Any ideas?
Hi Pieter,
The domain join profile is only applicable with an Autopilot deployment profile configured to do a hybrid Azure AD join.
Regards, Peter
Hi Peter,
I’m trying to do a Hybrid Domain Join (which works great)
But i created a second profile to apply, which changes the Computername to a more edible one (PC%rand:4%) Which also work.
However, it ONLY changes computername on the local PC and AD account DOESN’T update, which means that i cannot log on to the PC afterwards.
How can i make it change the AD Computer Name too?
Hi Thomas,
Do you mean that you’re not using the domain join profile to set the computername?
Regards, Peter
Yes i am, but that only lets me choose a prefix and the randomchars for the rest up to 15 chars.
I want a 4 letter prefix follow by a 4 digit number.
Hi Thomas,
I can’t find it being documented, but I would say that it’s the reason why it’s a separate policy at this moment.
Regards, Peter
Thomas/Peter,
I have the same issue. The computer rename option in Intune changes almost all names (local, Intune & AzureAD) but NOT on-prem AD, thus breaking on-prem access etc.
So close!
Thanks,
Dan
Sorry, I should clarify, my response is regarding this article in conjunction with https://www.petervanderwoude.nl/post/rename-a-device-via-windows-10-mdm/
Thank you, Dan!
Seeing the same thing.
A computer rename in Intune, dont replicate to onprem AD, thus it breaks the computer account in the onprem AD..
Had to make the domain join computer template look like this XXPC000000 then have 5 trailling random letters / numbers.
Its not super pretty but it does make the PC name more readable than 11 random characters.
Hi Kenneth,
Even though it’s not documented, it sounds like this CSP only works for Azure AD joined devices.
Regards, Peter
Hi Peter,
It was a wonderful post.
While performing Hybrid Azure AD join via Autopilot in hyper-v environment we are facing the issue (ERROR CODE : 80180005)
Hi Kruthika,
Did you verify the logs of the connector?
Regards, Peter
Great Post! Thank you!
Couple questions.
The Autopilot is marketed as the device can be shipped from Manufacturer to User ( Assuming they mean Remote User). For Hybrid Join, requirement is to have access to domain controller (be on the Corporate network, Direct connection to AD, etc., can’t be done over VPN), then how is the remote user gonna login from home when they get the laptop delivered from the manufacturer?
I tested in VM, and on a physical laptop, offcourse, I cant login for the first time as the user because its not connected to the network.
How is this autopilot useful in Hybrid environment then?
MS define Autopilot as one thing, offers one more thing, but defeats the original purpose of making it easier to provision the device straight from manufacturer to the user.
Hi Dipesh,
You could say that the deployment process is simplified and that the user will be faster up-and-running after a failure.
Regards, Peter
Hi Peter,
Great post, thanks!
What about the double objects in Azure AD. After we installed a device with AutoPilot two device objects appeared in Azure AD; a Azure AD Joined and Hybrid Azure AD Joined object.
Is this normal behaviour?
Regards, Angelo
Hi Angelo,
To my knowledge that’s currently expected behaviour. See also: https://social.technet.microsoft.com/Forums/en-US/64a2c8c7-5723-46fa-a63b-31a722710b42/hybrid-autopilot-double-aad-objects?forum=microsoftintuneprod
Regards, Peter
Good morning, sir,
Do you know if DirectAcces could work to allow users to log on to the computer for the first time?
Does Autopilot apply GPO during configuration?
Or do you have a solution so that users off the network can connect?
Thank you for your help.
Hi Guillaume,
VPN support is currently in development (see: https://docs.microsoft.com/en-us/mem/intune/fundamentals/in-development).
Regards, Peter
Hi Peter. I have installed the Intune Connector, but it won’t show up in Endpoint Manager. I tried to bypass proxy settings as described in this document: https://docs.microsoft.com/en-us/mem/intune/enrollment/autopilot-hybrid-connector-proxy
This is the error I receive in event viewer: https://docs.microsoft.com/en-us/troubleshoot/mem/intune/intune-connector-for-ad-not-appear
Do you have any idea what the issue can be?
Hi Simen,
That sounds like it’s still not going past the proxy. Do you see anything on the proxy?
Regards, Peter
Hi Peter
I’m in touch with MS Support for this issue but so far they are not able to answer me
Do you know, once we log into the connector for the first set up, what happens with the account used after ? The guy who enrolled the connector left the company, he did it with his own global admin account, i need to disable it now
I would like to reenroll the connector with a dedicated service account but even after uninstalling it the “sign in” is greyed like it keeps the credentials somewhere
So i have 3 questions :
Does the connector always rely on the account used for the setup to work ?
Can i disable this account without breaking the link ?
How can i logout this account from the onpremise server and use a new one ?
Thanks !
Alex
Hi Alex,
Sadly I can’t answer those question completely, as I have to rely on the docs for confirmation. And that’s nothing more than this: https://learn.microsoft.com/en-us/mem/autopilot/windows-autopilot-hybrid
Regards, Peter