This week back to the Windows platform. This week is again about managing local administrators on Windows 10 devices. Even in a modern world, there can still be a need for managing the local administrators on a Windows 10 devices and often that still requires more flexibility than provided with the default Azure AD functionality. I’ve also discussed managing local administrators already multiple times – either by using a Windows 10 MDM policy setting or by using proactive remediations – and this time it’s about a new method that became available in Windows 10, version 20H2 and later. That method is a new Windows 10 MDM policy setting. In this post, I’ll provide an introduction to that new policy setting and I’ll show how to use that new policy setting. I’ll end this post by having a look at the configuration result.
Introduction to the policy setting
Starting with Windows 10, version 20H2, a new policy setting is introduced that adds more options for managing the memberships of local groups. Those management options are the option to add, remove, or replace members of local groups on a managed device. That new policy setting is named LocalUsersAndGroups and is available within the Policy CSP. Before, the RestrictedGroups policy setting could be used for managing the membership of local groups. However, that policy setting only enables the option to replace members of local groups. This new policy setting provides more management options and is also the new recommended policy setting for managing the memberships of local groups. It provides a relatively easy method for adjusting members of local group without the need to overwrite all the existing members. That was often a reason to use custom scripting.
Important: The LocalUsersAndGroups policy setting and the RestrictedGroups policy setting should not be used together, as the behavior will be unpredictable. Both policy settings will be applied in no particular order.
The configuration node, of the LocalUsersAndGroups policy setting, in the Policy CSP is LocalUsersAndGroups/Configure and the configuration should contain a XML definition like the following.
<GroupConfiguration>
<accessgroup desc = "">
<group action = ""/>
<add member = ""/>
<remove member = ""/>
</accessgroup>
</GroupConfiguration> Within the example XML definition above, the different elements are used to specify the following information.
<accessgroup desc>– This element specifies the name or SID of the local group that should be configured<group action>– This element specifies the action that should be taken on the on the local group that should be configured. Those actions can be update (U) or restrict (R) and can be used to achieve the following:U– This action can be used to add or remove members of the local group that should be configured
R– This action can be used to replace current members of the local group that should be configured
<add member>– This element specifies the name or SID of the member that should be added to the local group<remove member>– This element specifies the name or SID of the member that should be removed from the local group. This element is not processed when the restrict action is used.
Tip: When specifying domain accounts or groups, use the fully qualified account or group name. When specifying Azure AD groups, use the group SID and when specifying Azure AD users, use AzureAD\{UPN}.
Configuration of the policy setting
The LocalUsersAndGroups policy setting can be configured by using a custom device configuration profile. That profile requires two important properties, the OMA-URI and the value. The OMA-URI is already known and the value requires an XML definition that might require some more explanation.
Construct the LocalUsersAndGroups XML
The best method to show the additional functionality of the LocalUsersAndGroups policy setting versus the RestrictedGroups policy settomg, is by using that policy setting for adding or removing members to a local group. In this post that policy setting is used for adding an Azure AD user and group to the local administrators group on a managed device. To achieve that, the different elements should be configured with the required values. Most of those values are pretty self explainable, with the explanation in the introduction, with the exception of the values of the Azure AD user and group. For those values the following information and format is required.
- Azure AD user – The Azure AD user is relatively simple, as that’s basically just adding a prefix to the UPN of the user account. For the example user that would be AzureAD\tvanderwoude@petervanderwoude.nl
- Azure AD group – The Azure AD group is a bit more challenging, as that requires the SID of the group. The SID of the group can be found by using Graph Explorer, querying the
/groupsendpoint, searching the response for the required group and looking at thesecurityIdentifierproperty. For the example group that would be S-1-12-1-934997727-1097630882-1590523563-2481977683
Together with the more self explainable elements, the values of the Azure AD user and group can be used to create the following XML definition. That content of that XML definition can be used as the value of the OMA-URI.
<GroupConfiguration>
<accessgroup desc = "Administrators">
<group action = "U"/>
<add member = "AzureAD\tvanderwoude@petervanderwoude.nl"/>
<add member = "S-1-12-1-934997727-1097630882-1590523563-2481977683"/>
</accessgroup>
</GroupConfiguration> Tip: If needed, it’s possible to use the SID (S-1-5-32-544) instead of the group name (Administrators).
Distribute the LocalUsersAndGroups XML
The best method for applying the configuration on Windows devices, is by using a custom device configuration profile. That profile can be used for configuring the OMA-URI with the constructed value. The following nine steps can be used for creating that profile and assigning it to the required users or devices.
- Open the Microsoft Endpoint Manager admin center portal navigate to Devices > Windows > Configuration profiles to open the Windows | Configuration profiles blade
- On the Windows | Configuration profiles blade, click Create profile to open the Create a profile page
- On the Create a profile page, provide the following information and click Create to open the Custom wizard
- Platform: Windows 10 and later
- Profile type: Custom
- On the Basics page, provide the following information and click Next
- Name: Provide a valid name for the custom device configuration profile
- Description: (Optional) Provide a valid description for the custom device configuration profile
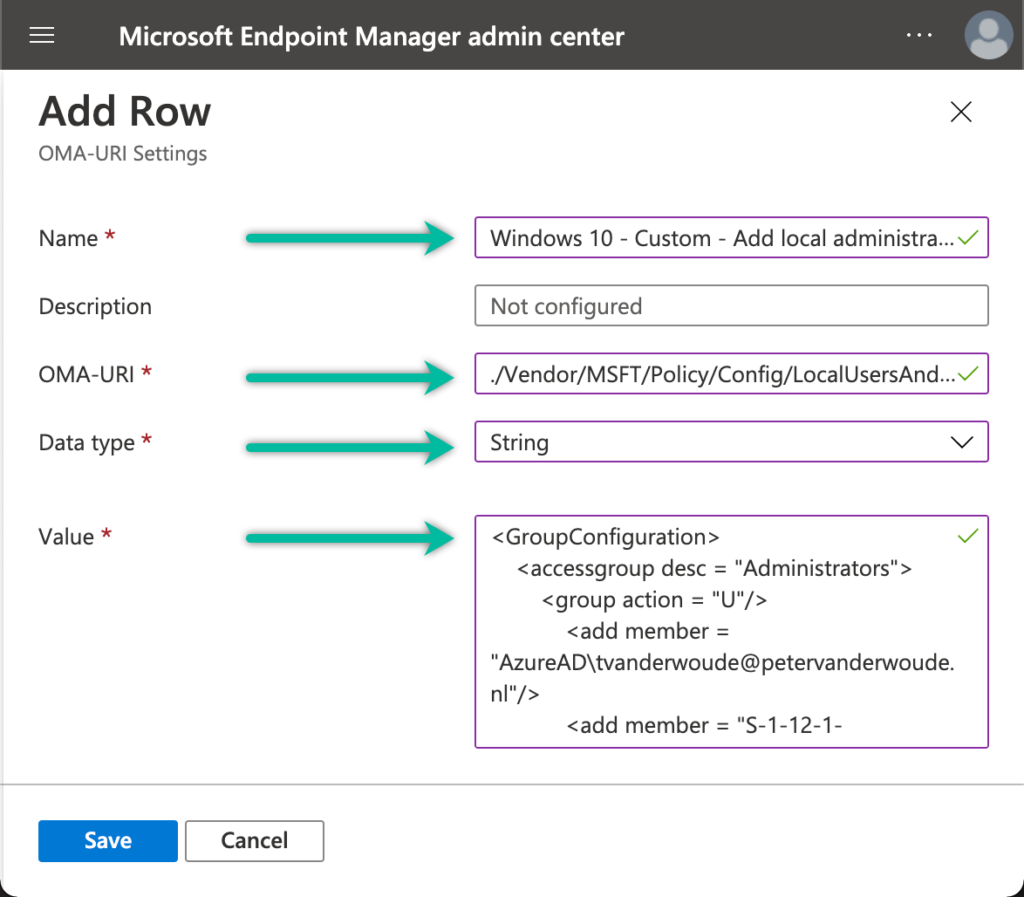
- On the Configuration settings page, click Add to open the Add Row page. On the Add Row page, provide the following information and click Add (and click Next back on the Configuration settings page)
- Name: Provide a valid name for the OMA-URI setting
- Description: (Optional) Provide a valid description for the OMA-URI setting
- OMA-URI: ./Vendor/MSFT/Policy/Config/LocalUsersAndGroups/Configure
- Data type: Select String
- Value: Provide the created XML definition
- On the Scope tags page, configure the required scope tags click Next
- On the Assignments page, configure the assignment to the required users and/or devices and click Next
- On the Applicability rules page, configure the applicability rules (think about the existence of this policy setting for only the Pro, Business, Enterprise and Education edition and the existence of this policy setting for only the 202H2 version and later) and click Next
- On the Review + create page, verify the configuration and click Create
Note: From an administrator perspective the status of the configuration in the Microsoft Endpoint Management admin center should eventually show as Succeeded for the managed devices.
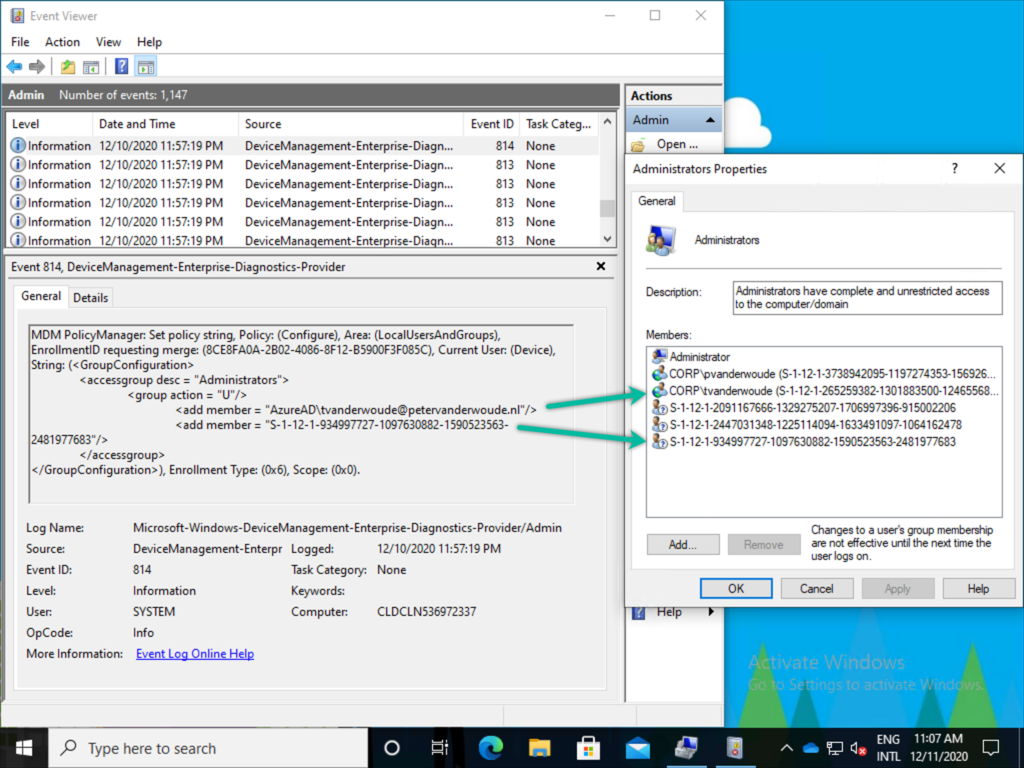
Configuration result
Once the custom device configuration profile has been applied, it’s time to have a look at the results of the configuration on a device with Windows 10, version 20H2 or later. The easiest method to view the results of the configuration, is by having a look in the Event Viewer together with a look at the members of the local administrators group. The Event Viewer will show the applied configuration and its results (as shown on the left in Figure 2). The members of the local administrators group will show the newly added members (as shown on the right in Figure 2).
Besides looking at the configuration result, it’s good to know that the custom device configuration device profile will be reapplied automatically, within 8 hours, when the configuration was changed by the user (behavior starting with Windows 10, version 1903).
Note: The other members of the local administrators group are the default administrator, the primary user and the SIDs that are representing the Global administrator role and the Device administrator role.
More information
For more information about managing local administrators on Windows devices, refer to the following docs.
Useful post, thank you.
If this only works for 20H2 devices, it could be a long time before that is the only version out there in some organisations. My preferred method currently is to use group policy preferences. This is very flexible and easy to use. Hopefully the method you outline here will be just as easy eventually.
Hi Gary,
This is indeed specific to Windows 10 version 20H2 and later. Also, keep in mind that this is also focussed on using MDM for managing the configuration. This is not applicable when you are still using GPO’s for configuring your devices.
Regards, Peter
So in my testing, I could not use the R method replace to dump out the built-in Administrator account (even though it is disabled on my workstations). Otherwise works fine for my uses!
Hi Andrew,
That is correct. You can’t remove the built-in Administrator account (see also the faq in the docs).
Regards, Peter
When using this on Windows 10 Business devices (20H2) the configuration is rejected by licensing. The eventlog shows this error:
MDM PolicyManager: Policy is rejected by licensing, Policy: (Configure), Area: (LocalUsersAndGroups), Result:(0x82B00006) Unknown Win32 Error code: 0x82b00006.
Both tried it with a user licensed with Microsoft 365 Business Premium and a user licensed with Enterprise Mobility + Security E3.
Any experience with that error? As far as I know this should work on Windows 10 Pro, Education, Enterprise and Business.
Sorry Martijn, but I haven’t had that combination yet. It sounds like a licensing challenge, but according to the docs it should be okay. The easiest would be to raise a ticket with Microsoft.
Regards, Peter
Ok, as David Masters quoted MS below, apparently it’s a bug in this particular Windows version. Will keep you informed.
Thank you Martijn!
Same problem as Martijn,
MDM PolicyManager: Policy is rejected by licensing, Policy: (Configure), Area: (LocalUsersAndGroups)
Strangely it works on one tenant with EMS E3 but not on a different tenant with M365 Business Premium.
Thank you for sharing Tjalling! That sounds like a licensing thing in that case, but to confirm please register a support case with Microsoft.
Regards, Peter
Hi thanks for this! For this administrator route I don’t seem to be able to bypass polices I set for users. I have put users in a security group which I have set policies to block certain things like personalisation but they also seem to be blocked for the admins using this custom policy. How would I create a admin account which I log into which doesn’t pick up any of the user polices I have added to others that use the device. Having a admin that bypasses these things is good for troubleshooting in my opinion and especially for those who work in schools. Currently our local admin or domain admin can log into devices without any policies with the current set up of AD on prem but would love if this can be done with AAD/intune too as we are looking to make the move to use intune. Im probably being a novice and this can be achieved quite easily I just dont know how. Any ideas?
Hi Aran,
If you’re assigning your policies to users, you can exclude a group with your admin(s).
Regards, Peter
I have the same issue has Martijn. I suspect it is related to the Windows 10 Business SKU as this works fine on 2 other machines with Windows 10 Pro. Even though, according to documentation Win10 Business is supported.
I’ve had the support ticket raised with Microsoft for this but they appear just as confused.
Thank you for sharing Sijia! I’m curious what the result of your ticket will be.
Regards, Peter
Hi Peter,
Quick question for you – I’m trying to decipher how (and if) I can translate this into the new Endpoint Manager Settings Catalogue.
Any ideas?
Regards, David
Hi David,
I haven’t seen this setting in the Settings Catalog yet. That can, however, change in the near future.
Regards, Peter
I also have the ‘Policy is rejected by licensing’ error.
It seems that the policy is applied when a 20H2 version is first configured. Changes afterwards to the policy are rejected with the licensing error.
Versions that are not 20H2 and are later updated to 20H2 when already enrolled in Intune (in my case 2004 to 20H2) never get this policy working.
It seems like a bug somewhere in Intune or Windows 10.
Thank you for the information Pieter! I hope you’ve already created a support case with Microsoft?
Regards, Peter
I think the information of Microsoft is wrong and you need Windows 10 Enterprise to apply this policy. I tried on a Windows 10 Pro 20H2 machine and the event logs said “Policy is rejected by licensing”.
Thank you for your input Teun.
I was able to recreate this in my environment for both Administrator and Hyper-V Administrator local groups. The policy is applying successfully (and I can see the Azure AD SIDs added once the policy applied- just like Peter’s screenshots). However, I am not seeing the permissions update. e.g. standard user is not elevated to admin even though its in the AAD group membership.
Has anyone else tested this recently? My PC is WinVer 20h2. I did see this working in 2004.
Hi Ryan,
Are you sure that we’re talking about the same? This functionality is introduced with 20H2.
Regards, Peter
Hi Peter, I did some more testing to confirm my use case. I referenced your previous article “Managing local administrators via Windows 10 MDM” and was able to effectively add AAD users to local admin group (prior to WinVer 20h2). I also used this approach for the HyperV administrators, which is another requirement for my environment (one AAD group needs HyperV access and NOT full administrator). My hope for 20h2 is to use group assignment for both of these Windows 10 device roles. I was able to get administrator group working, but I am not seeing permissions update for the user that I have assigned to the HyperV role. I will raise a MS premiere ticket for this.
Thank you for the explanation, Ryan. When you are using the group SID as a member and the permissions are not applying, then a support case is the best route for now. I’m curious about the response.
Regards, Peter
I’m having an issue with this CSP in my testing on 20H2 devices. I’ve created the policy to add a group to the Administrators and I see the policy applying and adding the AAD group SID. When I attempt to elevate with administrator privileges it won’t accept the account credentials for users in the AAD group. If I add individual user accounts(azuread\user), it works as expected. We really would like to get the AAD user groups working.
Has anyone been able to get this working in their environment?
Hi Jean,
I haven’t used it recently, but I’ve heard more reports about that behavior. When you are indeed using the group SID, you might want to create a support ticket.
Regards, Peter
Hi Peter,
I have logged a case with Microsoft 2-weeks ago and today have received the following message
I would like to inform you that this issue was reported to us few days back and we engaged the product team to look into it. After reviewing the details, this has been defined as OS bug and the ETA from the OSG bug owner is 90 days to fix. I would request you to wait for sometime and then try this policy on Windows 10 Business devices once this bug gets fixed from the Windows side.
I will continue to monitor and reply back as I hear something.
Regards
David
Thank you for the information David! That explains the different notifications in the comments here. Thank you!
Regards, Peter
What OMA-URI do i need to use?
./Vendor/MSFT/Policy/Config/LocalUsersAndGroups/Configure
or
./Device/Vendor/MSFT/Policy/Config/LocalUsersAndGroups/Configure
Now im using the first one but im receiving the following error message:
0x87d1fde8
Remediation failed
Hi Teun,
Both achieve the same. With a device wide policy /Device can be omitted.
Regards, Peter
Thank you for this method to modify groups.
In my case it idnt work.
Error message in event log is: Cannot be used on predefined groups.
Any idea?
And Kan
Hi And,
What are you trying to configure and which version and edition of Windows 10 are you using?
Regards, Peter
Hello Peter,
it is a Windows 10 Enterprise Evaluation 21H1, but same problem on 20H2.
I tried to replace all predefined entries in “Administrators” and add some “Remote desktop users”:
<GroupConfiguration>
<accessgroup desc = “Administratoren”>
<group action = “R”/>
<add member = “S-1-12-1-…” />
</accessgroup>
<accessgroup desc = “Remotedesktopbenutzer”>
<group action = “U”/>
<add member = “S-1-12-1-…/>
</accessgroup>
</GroupConfiguration>
It’s a german edition, that’s why I use “Administratoren” not “Administrators”
Thank you,
And Kan
Hi And,
Does that mean that you are trying to remove the built-in Administrator account from the group? If so, that’s not supported: https://docs.microsoft.com/en-us/windows/client-management/mdm/policy-csp-localusersandgroups?WT.mc_id=EM-MVP-5001447#faqs
Regards, Peter
Hi Peter,
Very useful post. Thank you.
I wonder how do we manage the password of the local user, can we reset the password and will it sync to all devices?
Thanks
Hi El,
This only helps with managing local administrators (or any other local group membership). Managing passwords, requires custom scripting.
Regards, Peter
Are there any updates regarding the 0x82b000060 Policy is rejected by licensing error ? I am running Windows 10 Business with 20H2 update.
Regards, Ognjen
Hi Ognjen,
Nothing more than what’s described by multiple others, which is that it will be fixed. If it’s not fixed yet, please create a support case with Microsoft.
Regards, Peter
Hey guys, any updates about the issue?
still waiting for the bug to be fixed.
is anyone able to add users?
No, we tried to permit Remote Desktop Users with an AAD-group. AAD-group SID is correctly member of the group and the policy is succeded in Endpoint Manager. But the users have to remote desktop access =( That’s also related to the bug, right?
correction: But the users have no remote desktop access
Hi,
We have AzureAD users added to the local admin group by default during the intune onboarding process – we now want to remove these using the above method. How can we specify the AzureAD account to be removed as it will be different on each device?
Hi Sarbjit,
When you do know the end situation, you don’t need to know the current situation and you can just “overwrite”.
Regards, Peter
Hi Peter,
I’m trying to roll this out in-house at the moment, replacing the older RestrictedGroups policy. Keep hitting an error when trying to deploy though:
“MDM ConfigurationManager: Command failure status. Configuration Source ID: (E90A892A-8B7B-4516-AA75-FC48610A74DB), Enrollment Name: (MDMDeviceWithAAD), Provider Name: (Policy), Command Type: (Add: from Replace or Add), CSP URI: (./Device/Vendor/MSFT/Policy/Config/LocalUsersAndGroups/Configure), Result: (Windows was unable to parse the requested XML data.).”
The XML appears fine to me though, and I’ve tried typing it all manually into the config window to make sure there wasn’t any issues with quotation marks and such – any ideas would be appreciated.
(Note SK-Admin-SK is what we rename the local admin account to)
Fixed it; I’d forgotten that device wide policies don’t need the ./Device at the start.
Really wish MS would apply some logic to such things and rationalise prefixing 🙂
Thank you for the update Rob!
Hi Rob,
You can now also use the UI to create the (most) required configurations. That prevents creating wrong XML-configuration. See for more information: https://www.petervanderwoude.nl/post/even-easier-managing-local-administrators/
Regards, Peter
Hi Peter,
does it work with HybridJoined devices too?
I get no error messages in evennt log, but users/groups not added to local group – no effect.
Hi AndKan,
Yes, you can also use this for hybrid Azure AD joined devices.
Regards, Peter
MDM PolicyManager: Set policy string, Policy: (Configure), Area: (LocalUsersAndGroups), EnrollmentID requesting set: (7F538369-5441-5B10-A41B-059FC86ECDE7), Current User: (Device), String: (), Enrollment Type: (0x0), Scope: (0x0), Result:(0x80070562) The specified account name is already a member of the group..
I’m seeing the above error for my environment. Any idea why this might be happening ? I’m trying to replace the older RestrictedGroups CSP used for performing these operations on local user accounts. (not AD joined or Azure AD joined).
Hi Windows User,
I would need some more information; what was the previous configuration and what is the new configuration that you’re applying?
Regards, Peter
Hi Peter,
I have similar issue as Jean described. The Azure AD group with its SID is deployed successfully to the machine.
At that moment all accounts within the group can do “run as administrator” action.
However, if I add new member to the group he never gets local admin rights(I was waiting around 24 hours).
And another question, does “Azure AD Joined Device Local Administrator” role need to be assigned to my group?
Or it can be simply Azure AD security group without that role.
Thanks
Hi Djordje,
You don’t need that role. That role is for device administrators that need local admin permissions on all devices.
Regards, Peter