This week is all about using conditional access for blocking downloads. I already did something similar before by using app enforced restrictions for Exchange Online and SharePoint Online. This time I’m going to take it one step further by looking at recently adjusted functionality for Conditional Access App Control. Conditional Access App Control enables administrators to control user sessions by redirecting the user through a reverse proxy instead of directly to the app. From then on, user requests and responses go through Cloud App Security rather than directly to the app. This creates an additional layer that can be used to filter actions. In this blog post I’ll start with a short introduction about Conditional Access App Control, followed by the configuration steps and the end-user experience.
Note: Cloud App Security can be licensed as part of EMS E5 or as a standalone service.
Introduction
Now let’s start with a short introduction about Conditional Access App Control. Conditional Access App Control uses a reverse proxy architecture and is directly integrated with conditional access. Conditional access enables administrators to route users to Cloud App Security, where data can be protected. That can be achieved by applying Conditional Access App Control session controls. That created route enables user app access and sessions to be monitored and controlled in real time, based on access and session policies in Cloud App Security. Those policies can also be used to further refine filters and set actions to be taken on a user. In other words, Conditional Access App Control enables administrators to control user sessions by redirecting the user through a reverse proxy instead of directly to the app.
Configuration
Let’s continue by having a look at the configuration options, by looking at a specific scenario. That scenario is blocking downloads on unmanaged devices, for any supported cloud app. The following seven steps walk through that scenario. After the creation of the conditional access policy, it can be assigned to a user group like any other conditional access policy.
| 1 | Open the Azure portal and navigate to Microsoft Intune > Conditional access > Policies or to Azure Active Directory > Conditional access > Policies to open the Conditional Access – Policies blade; |
| 2 | On the Conditional Access – Policies blade, click New policy to open the New blade; |
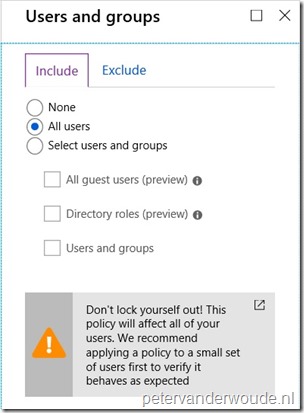
| 3a |
Explanation: This configuration will make sure that this conditional access policy is applicable to all users. |
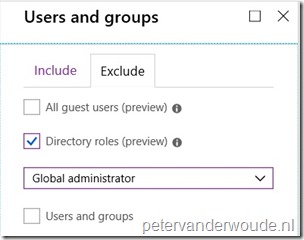
| 3b |
Explanation: This configuration will make sure that this conditional access policy will exclude global administrators. |
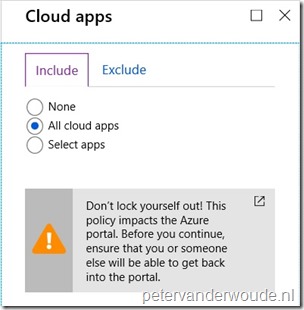
| 4 |
Explanation: This configuration will make sure that this conditional access policy is applicable to all connected cloud apps. |
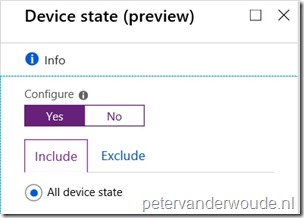
| 5a |
Explanation: This configuration will make sure that this conditional access policy is applicable to all device states. |
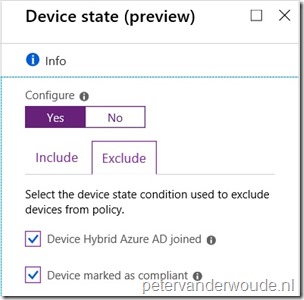
| 5b |
Explanation: This configuration will make sure that this conditional access policy will exclude managed and compliant devices. |
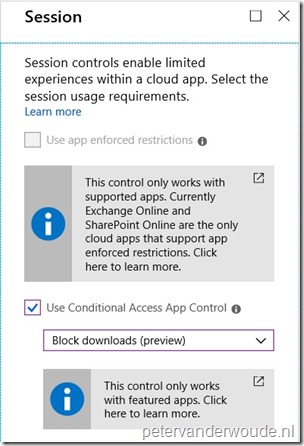
| 6 |
Explanation: This configuration will make sure that this conditional access policy will block downloads for the assigned users, from the assigned cloud apps, on unmanaged devices. The latest options within this configuration are the built-in options Monitor only and Block downloads, which are both still in preview and Use custom policy…. The latter option requires a custom policy within Cloud App Security. The other options two basically provide preconfigured options, of which Block downloads provides the behavior that I need for this scenario. |
| 7 | Open the New blade, select On with Enable policy and click Create; |
Note: Conditional Access App Control supports any SAML or Open ID Connect app that is configured with single sign-on in Azure AD, including these featured apps.
End-user experience
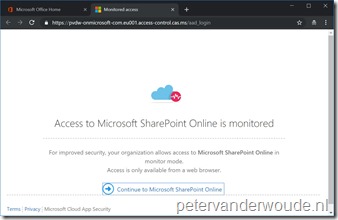
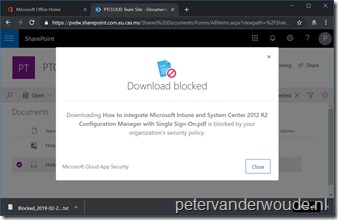
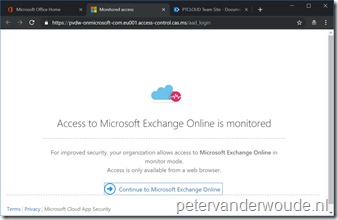
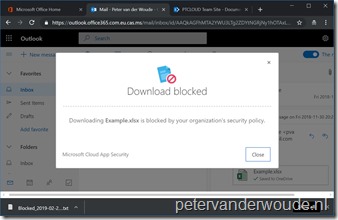
Now let’s end this blog post by having a look at the end-user experience. Below are example for the behavior with SharePoint Online and Exchange Online. I deliberately choose those apps, to show the difference in end-user experience compared to using app enforced restrictions (which I mentioned in the beginning of this post). The big difference is that app enforced restrictions are handled by the app, while this configuration is handled by Cloud App Security.
Below on the left is an example of the end-user accessing SharePoint Online on an unmanaged device. The end-user receives a clear message that the access is monitored. Below on the right is an example of the end-user trying to download a file from SharePoint Online, while being directed via Cloud App Security. The end-user receives a clear message that the download is blocked.
 |
 |
Below are similar examples for Exchange Online. On the left the message that the end-user receives when access Exchange Online on an unmanaged device and on the right the message that the end-user receives when trying to download an email attachment.
 |
 |
More information
For more information regarding Cloud App Security and conditional access, please refer to the following articles:
- Microsoft Cloud App Security overview: https://docs.microsoft.com/en-us/cloud-app-security/what-is-cloud-app-security
- Protect apps with Microsoft Cloud App Security Conditional Access App Control: https://docs.microsoft.com/en-gb/cloud-app-security/proxy-intro-aad
- Deploy Conditional Access App Control for Azure AD apps: https://docs.microsoft.com/en-gb/cloud-app-security/proxy-deployment-aad
Hi Peter,
Nice article!
Does every user need a EMS e5 license or separate Cloud App Security license or is one license enough to have the feature (like AAD p1) but the you are not compliant?
Do you perhaps know if we can block OneDrive sync without having to use the regkey on this article (https://docs.microsoft.com/en-us/onedrive/enable-conditional-access) ?
Hi RKast,
You need a license for every user that will use cloud app security. Use can also mean being redirected through cloud app security by conditional access.
Regards, Peter
Does MCAS solution outlined support a scenario where you want a certain subset of guest users to be able to download against a specific set of SPO Sites or MS Teams?
Hi Mike,
By using conditional access, the access check is done on a cloud app level and not on a site level.
Regards, Peter
Hi Peter
Is there functionality/options to prevent the user from opening the documents from online One Drive/SharePoint etc.. on the desktop application(s) for example a Word document in One drive and open in Word desktop, by selecting this option the user is able to then select save as and then save to local machine regardless which subsequently over-rides the download option as basically this is bypassing it?
Hi Dallan,
Are you looking for conditional acces functionality, or for WIP functionality?
Regards, Peter
Hi Peter
CA functionality as currently not leveraging WIP.
Thanks
Dallan
Hi Dallan,
CA alone won’t fix that complete scenario for you.
Regards, Peter
Great article Peter.
Personally don’t see the point of this functionality since i can use Sharepoint permissions and RMS to not allow people download documents from Sharepoint.
Did you have any luck with the new feature allowing non global admins to view Bitlocker Keys in Intune.
An article on that will be great :).
I tried my luck with Microsoft support but they blew me off since the feature is still in preview.
Thank you, Egert. It’s all about preference and use case.
Regarding your BitLocker question; I haven’t really looked into that, but I might. Having said that, no timetables and no guarantees 🙂
Regards, Peter
Hello Peter,
Thanks for the article, really helpful for a newbie like me.
I have a basic question. We currently have AAD P1 and I have followed all the steps, but still the test user is able to download attachments from Outlook. To implement the above setup do we need Microsoft Cloud App Security + EMS 3 licensing?
Any help is highly appreciated.
-Thanks
Haneesh
Hi Haneesh,
The licensing information regarding Cloud App Security can be found here: https://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2NXYO
Regards, Peter
In our environment when I apply to “All Users” it BLOCKS downloads on-prem coporate devices. This is not the behaviour I want. However when I select each user selectivielty one by one it gives the correct behvaiour does on BLOCK devices for on prem, any ideas how to fix this? or is this known issue?
Hi Qessar,
If the only adjusted parameter is the assigned group, the behavior doesn’t sound correct. In that case I would contact support.
Regards, Peter
Hi
I got a trial of M365 Business and i am trying to set this up however it just does not enable.
Do you know if Cloud app security comes part of this license and it is a requirement to use this CA session control?
Regards
Wasim
Hi Wasim,
You can find the licensing options for Cloud App Security here.
Regards, Peter
We had M365 Business., but we still had to purchase EMS5 to get access to Cloud App Security..
Hi Harini,
That makes sense.
Regards, Peter
This is great thanks!! Although I have worked out that you can still download a spreadsheet or word doc if you select “Open In Desktop App”, having said that it isn’t in my downloads folder. Does it just pull down a temp file for editing in the desktop app that isn’t available offline?
Hi Alex,
Are you saying that you could save the file locally after opening it in the desktop app?
Regards, Peter
Thanks for this articles, how about upload file?
that need for securing file specially source code so user can not upload these file.
You have some options for uploads. Have a look here for some more details: https://docs.microsoft.com/en-us/cloud-app-security/session-policy-aad
Regards, Peter
Hi, Thanks for the article. After applying conditional access to block download, I am unable to move files from OneDrive, is this expected ?
Hi Vasu,
Can you provide some more details about the scenario that you’re describing?
Regards, Peter